mirror of
https://github.com/pe3zx/my-infosec-awesome.git
synced 2024-06-30 07:31:20 +00:00
707 lines
63 KiB
Markdown
707 lines
63 KiB
Markdown
## Articles
|
||
|
||
### Cryptography
|
||
|
||
- [A Readable Specification of TLS 1.3](https://davidwong.fr/tls13/)
|
||
- [Encrypting for Apple's Secure Enclave](https://darthnull.org/security/2018/05/31/secure-enclave-ecies/)
|
||
- [hannob/tls-what-can-go-wrong - TLS - what can go wrong?](https://github.com/hannob/tls-what-can-go-wrong)
|
||
|
||
### Digital Forensics and Incident Response
|
||
|
||
- [A Newbie’s Guide to ESXi and VM Log Files](https://www.altaro.com/vmware/introduction-esxi-vm-log-files/)
|
||
- [certsocietegenerale/IRM - Incident Response Methodologies](https://github.com/certsocietegenerale/IRM)
|
||
- [Cloud Forensics: Analyzing MEGASync](http://cyberforensicator.com/2018/04/15/cloud-forensics-analyzing-megasync/)
|
||
- [Cloud Forensics: Google Drive](http://cyberforensicator.com/2018/10/19/cloud-forensics-google-drive/)
|
||
- [Cloud Forensics: pCloud Drive](http://cyberforensicator.com/2018/05/05/cloud-forensics-pcloud-drive/)
|
||
- [Finding TikTok messages in iOS](https://abrignoni.blogspot.com/2018/11/finding-tiktok-messages-in-ios.html)
|
||
- [Forensic Analysis Of The μTorrent Peer-to-Peer Client In Windows](https://articles.forensicfocus.com/2018/11/02/forensic-analysis-of-the-%CE%BCtorrent-peer-to-peer-client-in-windows/)
|
||
- ["Gone In 10 Seconds" Snapchat Forensics](http://www.carpeindicium.com/blog/gone_10-seconds/)
|
||
- [How to Perform Hadoop Forensics](https://www.peerlyst.com/posts/how-to-perform-hadoop-forensics-chiheb-chebbi)
|
||
- [Tool Analysis Result Sheet](https://jpcertcc.github.io/ToolAnalysisResultSheet/)
|
||
|
||
#### Digital Forensics and Incident Response: Platform: Android
|
||
|
||
- [The Forensics of Cortana on Android](http://delyjester.blogspot.com/2018/08/the-forensics-of-cortana-on-android.html)
|
||
|
||
#### Digital Forensics and Incident Response: Platform: Unix/Linux
|
||
|
||
- [Bruteforcing Linux Full Disk Encryption (LUKS) with hashcat - The Forensic way!](https://blog.pnb.io/2018/02/bruteforcing-linux-full-disk-encryption.html)
|
||
- [Can an SSH session be taken from memory?](https://security.stackexchange.com/questions/148082/can-an-ssh-session-be-taken-from-memory)
|
||
- [Forensic Relevance of Vim Artifacts](https://tm4n6.com/2017/11/15/forensic-relevance-of-vim-artifacts/)
|
||
- [INTRO TO LINUX FORENSICS](https://countuponsecurity.com/2017/04/12/intro-to-linux-forensics/)
|
||
- [Linux Memory Forensics: Dissecting the User Space Process Heap](https://articles.forensicfocus.com/2017/10/16/linux-memory-forensics-dissecting-the-user-space-process-heap/)
|
||
- [KIT-CERT Checklist for Linux Forensics](https://git.scc.kit.edu/KIT-CERT/Linux-Forensics-Checklist/blob/master/Linux-Forensics-Checklist.md)
|
||
|
||
#### Digital Forensics and Incident Response: Platform: IoT
|
||
|
||
- [Internet Of Things Mobility Forensics](https://articles.forensicfocus.com/2017/05/17/internet-of-things-mobility-forensics/)
|
||
|
||
#### Digital Forensics and Incident Response: Platform: MacOS/iOS
|
||
|
||
- [A Few Interesting iOS Forensic Artefacts](https://salt4n6.com/2018/05/15/a-few-interesting-ios-forensic-artefacts/)
|
||
- [Apple File System Reference](https://developer.apple.com/support/apple-file-system/Apple-File-System-Reference.pdf)
|
||
- [Apple Probably Knows What You Did Last Summer](https://blog.elcomsoft.com/2018/06/apple-probably-knows-what-you-did-last-summer/)
|
||
- [Detection of Backdating the System Clock in macOS](http://cyberforensicator.com/2018/01/21/detection-of-backdating-the-system-clock-in-macos/)
|
||
- [Finding Slack app messages in iOS](https://abrignoni.blogspot.com/2018/10/finding-slack-app-messages-in-ios.html)
|
||
- [Getting saucy with APFS](https://www.dropbox.com/s/bfjgiakkwt1bhm1/GettingSaucyWithAPFS.zip?dl=0)
|
||
- [How to Acquire an iOS 11 Device Without the PIN/Passcode](https://www.magnetforensics.com/blog/how-to-acquire-an-ios-11-device-without-the-pinpasscode/)
|
||
- [I Know What You Did Last Month: A New Artifact of Execution on macOS 10.13](https://www.crowdstrike.com/blog/i-know-what-you-did-last-month-a-new-artifact-of-execution-on-macos-10-13/)
|
||
- [Inside iCloud Drive: Downloading](https://eclecticlight.co/2018/04/04/inside-icloud-drive-downloading/)
|
||
- [Inside iCloud Drive: Pushed updates, that syncing feeling](https://eclecticlight.co/2018/04/02/inside-icloud-drive-pushed-updates-that-syncing-feeling/)
|
||
- [Inside iCloud Drive: uploading a file](https://eclecticlight.co/2018/03/30/inside-icloud-drive-uploading-a-file/)
|
||
- [iOS 11: HEVC and HEIF (heic) files](https://www.cclgroupltd.com/ios-11-hevc-heif-heic-files/)
|
||
- [Knowledge is Power! Using the macOS/iOS knowledgeC.db Database to Determine Precise User and Application Usage](https://www.mac4n6.com/blog/2018/8/5/knowledge-is-power-using-the-knowledgecdb-database-on-macos-and-ios-to-determine-precise-user-and-application-usage)
|
||
- [mac4n6 - Presentations](https://www.mac4n6.com/resources)
|
||
- [macOS Unified log: 1 why, what and how](https://eclecticlight.co/2018/03/19/macos-unified-log-1-why-what-and-how/)
|
||
- [macOS Unified log: 2 content and extraction](https://eclecticlight.co/2018/03/20/macos-unified-log-2-content-and-extraction/)
|
||
- [macOS Unified log: 3 finding your way](https://eclecticlight.co/2018/03/21/macos-unified-log-3-finding-your-way/)
|
||
- [Monkey takes a .heic](http://cheeky4n6monkey.blogspot.com/2017/10/monkey-takes-heic.html)
|
||
- [Mounting an APFS image in Linux](http://az4n6.blogspot.com/2018/01/mounting-apfs-image-in-linux.html)
|
||
- [pstirparo/mac4n6 - Collection of forensics artifacs location for Mac OS X and iOS](https://github.com/pstirparo/mac4n6)
|
||
- [Reading Notes database on macOS](https://www.swiftforensics.com/2018/02/reading-notes-database-on-macos.html)
|
||
- [Staring into the Spotlight](https://blog.doyensec.com/2017/11/15/osx-spotlight.html)
|
||
- [The Hitchhiker’s Guide to macOS USB Forensics](http://cyberforensicator.com/2017/11/06/the-hitchhikers-guide-to-macos-usb-forensics/)
|
||
- [There’s Gold In Them There Blobs!](https://www.ciofecaforensics.com/2017/10/13/theres-gold-in-them-there-blobs/)
|
||
|
||
#### Digital Forensics and Incident Response: Platform: Windows
|
||
|
||
- [(Am)cache still rules everything around me (part 2 of 1)](https://binaryforay.blogspot.com/2017/10/amcache-still-rules-everything-around.html)
|
||
- [Amcache and Shimcache in forensic analysis](https://andreafortuna.org/amcache-and-shimcache-in-forensic-analysis-8e55aa675d2f)
|
||
- [Carving EVTX](https://rawsec.lu/blog/posts/2017/Jun/23/carving-evtx/)
|
||
- [Certificate Chain Cloning and Cloned Root Trust Attacks](https://posts.specterops.io/code-signing-certificate-cloning-attacks-and-defenses-6f98657fc6ec)
|
||
- [Detailed properties in the Office 365 audit log](https://docs.microsoft.com/en-us/office365/securitycompliance/detailed-properties-in-the-office-365-audit-log)
|
||
- [Detection and recovery of NSA’s covered up tracks](https://blog.fox-it.com/2017/12/08/detection-and-recovery-of-nsas-covered-up-tracks/)
|
||
- [Detecting DDE in MS Office documents with YARA rules](https://blog.nviso.be/2017/10/11/detecting-dde-in-ms-office-documents/)
|
||
- [Extracting Activity History from PowerShell Process Dumps](http://www.leeholmes.com/blog/2019/01/04/extracting-activity-history-from-powershell-process-dumps/)
|
||
- [Forensic Analysis of Systems that have Windows Subsystem for Linux Installed](http://blog.1234n6.com/2017/10/forensic-analysis-of-systems-with.html)
|
||
- [Getting to the Bottom of CVE-2018-0825 Heap Overflow Buffer](https://www.ixiacom.com/company/blog/getting-bottom-cve-2018-0825-heap-overflow-buffer)
|
||
- [How to Crack Passwords for Password Protected MS Office Documents](https://www.blackhillsinfosec.com/crack-passwords-password-protected-ms-office-documents/)
|
||
- [HUNTING EVENT LOGGING COVERUP](http://malwarenailed.blogspot.com/2017/10/update-to-hunting-mimikatz-using-sysmon.html)
|
||
- [In-depth forensic analysis of Windows registry files](https://www.slideshare.net/MaximSuhanov/indepth-forensic-analysis-of-windows-registry-files)
|
||
- [Logging Keystrokes with Event Tracing for Windows (ETW)](https://www.cyberpointllc.com/srt/posts/srt-logging-keystrokes-with-event-tracing-for-windows-etw.html)
|
||
- [Looking at APT28 latest Talos Security write up and how YOU could catch this type of behavior](https://hackerhurricane.blogspot.com/2017/10/looking-at-apt28-latest-talos-security.html)
|
||
- [MAC(b) times in Windows forensic analysis](https://andreafortuna.org/mac-b-times-in-windows-forensics-analysis-c821d801a810)
|
||
- [Malicious PowerShell in the Registry: Persistence](http://az4n6.blogspot.com/2018/06/malicious-powershell-in-registry.html)
|
||
- [Memory Acquisition and Virtual Secure Mode](https://df-stream.com/2017/08/memory-acquisition-and-virtual-secure/)
|
||
- [pwndizzle/CodeExecutionOnWindows - A list of ways to execute code on Windows using legitimate Windows tools](https://github.com/pwndizzle/CodeExecutionOnWindows)
|
||
- [RecentApps Registry Key](https://df-stream.com/2017/10/recentapps/)
|
||
- [RegRipper & keys parsed by plugins](http://hexacorn.com/tools/3r.html)
|
||
- [Tales of a Threat Hunter - Detecting Mimikatz & other Suspicious LSASS Access](https://www.eideon.com/2017-09-09-THL01-Mimikatz/)
|
||
- [Volume Shadow Copies in forensic analysis](https://andreafortuna.org/volume-shadow-copies-in-forensics-analysis-7708adefe61c)
|
||
- [Use Windows Event Forwarding to help with intrusion detection](https://docs.microsoft.com/en-us/windows/threat-protection/use-windows-event-forwarding-to-assist-in-instrusion-detection)
|
||
- [Windows, Now with built in anti forensics!](http://www.hecfblog.com/2017/04/windows-now-built-in-anti-forensics.html)
|
||
- [Windows Credentials: Attack + Mitigation + Defense](https://www.first.org/resources/papers/conf2017/Windows-Credentials-Attacks-and-Mitigation-Techniques.pdf)
|
||
- [Windows Drive Acquisition](https://articles.forensicfocus.com/2017/10/19/windows-drive-acquisition/)
|
||
- [Windows event logs in forensic analysis](https://andreafortuna.org/windows-event-logs-in-forensic-analysis-d80e2a134fdd)
|
||
- [Windows Privileged Access Reference](https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securing-privileged-access-reference-material#ATLT_BM)
|
||
- [Windows registry in forensic analysis](https://andreafortuna.org/windows-registry-in-forensic-analysis-7bf060d2da)
|
||
- [Windows Security Identifiers (SIDs)](https://andreafortuna.org/windows-security-identifiers-sids-2196a5be2f4d)
|
||
- [Windows Subsystem for Linux and Forensic Analysi](http://blog.1234n6.com/2017/10/windows-subsystem-for-linux-and.html)
|
||
- [Windows Event Forwarding for Network Defense](https://medium.com/@palantir/windows-event-forwarding-for-network-defense-cb208d5ff86f)
|
||
- [Word Forensic Analysis And Compound File Binary Format](https://articles.forensicfocus.com/2018/09/18/word-forensic-analysis-and-compound-file-binary-format/)
|
||
|
||
### Exploitation
|
||
|
||
- [Guest Diary (Etay Nir) Kernel Hooking Basics](https://isc.sans.edu/forums/diary/Guest+Diary+Etay+Nir+Kernel+Hooking+Basics/23155/)
|
||
- [MorteNoir1/virtualbox_e1000_0day](https://github.com/MorteNoir1/virtualbox_e1000_0day)
|
||
|
||
#### Exploitation: Hardware-related Attacks
|
||
|
||
- [Attacking a co-hosted VM: A hacker, a hammer and two memory modules](https://thisissecurity.stormshield.com/2017/10/19/attacking-co-hosted-vm-hacker-hammer-two-memory-modules/)
|
||
|
||
#### Exploitation: Platform: Android
|
||
|
||
- [Android Bluetooth Vulnerabilities in the March 2018 Security Bulletin](https://blog.quarkslab.com/android-bluetooth-vulnerabilities-in-the-march-2018-security-bulletin.html)
|
||
- [CVE-2017-13253: Buffer overflow in multiple Android DRM services](https://blog.zimperium.com/cve-2017-13253-buffer-overflow-multiple-android-drm-services/)
|
||
- [Writing the worlds worst Android fuzzer, and then improving it](https://gamozolabs.github.io/fuzzing/2018/10/18/terrible_android_fuzzer.html)
|
||
|
||
#### Exploitation: Platform: Linux
|
||
|
||
- [64-bit Linux Return-Oriented Programming](https://crypto.stanford.edu/~blynn/rop/)
|
||
- [Adapting the POC for CVE-2017-1000112 to Other Kernels](http://ricklarabee.blogspot.ch/2017/12/adapting-poc-for-cve-2017-1000112-to.html)
|
||
- [Blocking double-free in Linux kernel](http://blog.ptsecurity.com/2017/08/linux-block-double-free.html)
|
||
- [Binary Exploitation ELI5– Part 1](https://hackernoon.com/binary-exploitation-eli5-part-1-9bc23855a3d8)
|
||
- [Binary Exploitation ELI5 — Part 2](https://medium.com/@danielabloom/binary-exploitation-eli5-part-2-8fd71bf214b9)
|
||
- [Binary Exploitation ELI5 — Part 3](https://medium.com/@danielabloom/binary-exploitation-eli5-part-3-d1872eef71b3)
|
||
- [CVE-2016-2384: exploiting a double-free in the usb-midi linux kernel driver](https://xairy.github.io/blog/2016/cve-2016-2384)
|
||
- [CVE-2017-2636: exploit the race condition in the n_hdlc Linux kernel driver bypassing SMEP](https://a13xp0p0v.github.io/2017/03/24/CVE-2017-2636.html)
|
||
- [CVE-2017-11176: A step-by-step Linux Kernel exploitation (part 1/4)](https://blog.lexfo.fr/cve-2017-11176-linux-kernel-exploitation-part1.html)
|
||
- [CVE-2017-11176: A step-by-step Linux Kernel exploitation (part 2/4)](https://blog.lexfo.fr/cve-2017-11176-linux-kernel-exploitation-part2.html)
|
||
- [CVE-2017-11176: A step-by-step Linux Kernel exploitation (part 3/4)](https://blog.lexfo.fr/cve-2017-11176-linux-kernel-exploitation-part3.html)
|
||
- [CVE-2017-11176: A step-by-step Linux Kernel exploitation (part 4/4)](https://blog.lexfo.fr/cve-2017-11176-linux-kernel-exploitation-part4.html)
|
||
- [Dirty COW and why lying is bad even if you are the Linux kernel](https://chao-tic.github.io/blog/2017/05/24/dirty-cow)
|
||
- [Enumeration for Linux Privilege Escalation](https://0x00sec.org/t/enumeration-for-linux-privilege-escalation/1959)
|
||
- [Escaping Docker container using waitid() – CVE-2017-5123](https://www.twistlock.com/2017/12/27/escaping-docker-container-using-waitid-cve-2017-5123/)
|
||
- [Exploiting the Linux kernel via packet sockets](https://googleprojectzero.blogspot.com/2017/05/exploiting-linux-kernel-via-packet.html)
|
||
- [Kernel Exploitation | Dereferencing a NULL pointer!](https://0x00sec.org/t/kernel-exploitation-dereferencing-a-null-pointer/3850)
|
||
- [Linux (x86) Exploit Development Series](https://sploitfun.wordpress.com/2015/06/26/linux-x86-exploit-development-tutorial-series/)
|
||
- [Linux Heap Exploitation Intro Series: The magicians cape – 1 Byte Overflow](https://sensepost.com/blog/2017/linux-heap-exploitation-intro-series-the-magicians-cape-1-byte-overflow/)
|
||
- [Linux Heap Exploitation Intro Series: Set you free() – part 1](https://sensepost.com/blog/2018/linux-heap-exploitation-intro-series-set-you-free-part-1/)
|
||
- [Linux Heap Exploitation Intro Series: Used and Abused – Use After Free](https://sensepost.com/blog/2017/linux-heap-exploitation-intro-series-used-and-abused-use-after-free/)
|
||
- [Linux Kernel ROP - Ropping your way to # (Part 1)](<https://www.trustwave.com/Resources/SpiderLabs-Blog/Linux-Kernel-ROP---Ropping-your-way-to---(Part-1)/>)
|
||
- [Linux Kernel ROP - Ropping your way to # (Part 2)](<https://www.trustwave.com/Resources/SpiderLabs-Blog/Linux-Kernel-ROP---Ropping-your-way-to---(Part-2)/>)
|
||
- [Linux Kernel Vulnerability Can Lead to Privilege Escalation: Analyzing CVE-2017-1000112](https://securingtomorrow.mcafee.com/mcafee-labs/linux-kernel-vulnerability-can-lead-to-privilege-escalation-analyzing-cve-2017-1000112/#sf118405156)
|
||
- [Linux System Call Table](http://thevivekpandey.github.io/posts/2017-09-25-linux-system-calls.html)
|
||
- [MMap Vulnerabilities – Linux Kernel](https://research.checkpoint.com/mmap-vulnerabilities-linux-kernel/)
|
||
- [r0hi7/BinExp - Linux Binary Exploitation](https://github.com/r0hi7/BinExp)
|
||
- [Reversing DirtyC0W](http://blog.tetrane.com/2017/09/dirtyc0w-1.html)
|
||
- [The Definitive Guide to Linux System Calls](https://blog.packagecloud.io/eng/2016/04/05/the-definitive-guide-to-linux-system-calls/)
|
||
- [xairy/linux-kernel-exploitation](https://github.com/xairy/linux-kernel-exploitation)
|
||
|
||
#### Exploitation: Platform: MacOS/iOS
|
||
|
||
- [A Methodical Approach to Browser Exploitation](https://blog.ret2.io/2018/06/05/pwn2own-2018-exploit-development/)
|
||
- [An introduction to exploiting userspace race conditions on iOS](https://bazad.github.io/2018/11/introduction-userspace-race-conditions-ios/)
|
||
- [Analysis: Inspecting Mach Messages in macOS Kernel-Mode Part I: Sniffing the sent Mach messages](https://www.fortinet.com/blog/threat-research/inspecting-mach-messages-in-macos-kernel-mode--part-i--sniffing-.html)
|
||
- [Analysis: Inspecting Mach Messages in macOS Kernel-Mode Part II: Sniffing the received Mach messages](https://www.fortinet.com/blog/threat-research/inspect-mach-messages-in-macos-kernel-mode--part-ii--sniffing-th.html)
|
||
- [Covering Ian Beer's exploit techniques for getvolattrlist bug (iOS 11-11.3.1)](https://4ldebaran.blogspot.com/2018/07/covering-ian-beers-exploit-techniques.html)
|
||
- [Cracking the Walls of the Safari Sandbox - Fuzzing the macOS WindowServer for Exploitable Vulnerabilities](http://blog.ret2.io/2018/07/25/pwn2own-2018-safari-sandbox/)
|
||
- [Heapple Pie - The macOS/iOS default heap](https://www.synacktiv.com/ressources/Sthack_2018_Heapple_Pie.pdf)
|
||
- [Kernel RCE caused by buffer overflow in Apple's ICMP packet-handling code (CVE-2018-4407)](https://lgtm.com/blog/apple_xnu_icmp_error_CVE-2018-4407)
|
||
- [LightSpeed, a race for an iOS/MacOS sandbox escape](https://www.synacktiv.com/posts/exploit/lightspeed-a-race-for-an-iosmacos-sandbox-escape.html)
|
||
- [The HIDeous parts of IOKit](https://s.siguza.net/dl/pdf/2018-Zer0Con.pdf)
|
||
- [Timeless Debugging of Complex Software: Root Cause Analysis of a Non-Deterministic JavaScriptCore Bug](http://blog.ret2.io/2018/06/19/pwn2own-2018-root-cause-analysis/)
|
||
- [Weaponization of a JavaScriptCore Vulnerability -Illustrating the Progression of Advanced Exploit Primitives In Practice](https://blog.ret2.io/2018/07/11/pwn2own-2018-jsc-exploit/)
|
||
|
||
#### Exploitation: Platform: Windows
|
||
|
||
- [0patching the "Immortal" CVE-2017-7269](https://0patch.blogspot.com/2017/03/0patching-immortal-cve-2017-7269.html)
|
||
- [15 Ways to Bypass the PowerShell Execution Policy](https://blog.netspi.com/15-ways-to-bypass-the-powershell-execution-policy/)
|
||
- [A Bug Has No Name: Multiple Heap Buffer Overflows In the Windows DNS Client](https://www.bishopfox.com/blog/2017/10/a-bug-has-no-name-multiple-heap-buffer-overflows-in-the-windows-dns-client/)
|
||
- [A Deep Analysis of the Microsoft Outlook Vulnerability CVE-2018-8587](https://www.fortinet.com/blog/threat-research/a-deep-analysis-of-the-microsoft-outlook-vulnerability-.html)
|
||
- [A deeper look at ms11-058](https://blog.skullsecurity.org/2011/a-deeper-look-at-ms11-058)
|
||
- [Abusing A Writable Windows Service](https://blog.didierstevens.com/2017/09/05/abusing-a-writable-windows-service/)
|
||
- [Abusing Delay Load DLLs for Remote Code Injection](http://hatriot.github.io/blog/2017/09/19/abusing-delay-load-dll/)
|
||
- [Abusing GDI objects: Bitmap object’s size in the kernel pool](http://theevilbit.blogspot.com/2017/10/abusing-gdi-objects-bitmap-objects-size.html)
|
||
- [An Analysis of Microsoft Edge Chakra JavascriptArray TypeId Handling Memory Corruption (CVE-2018-8467)](https://www.fortinet.com/blog/threat-research/an-analysis-of-microsoft-edge-chakra-javascriptarray-typeid-hand.html)
|
||
- [An Analysis of the Use-After-Free Bug in the Microsoft Edge Chakra Engine (CVE-2018-0946)](https://www.fortinet.com/blog/threat-research/an-analysis-of-the-use-after-free-bug-in-microsoft-edge-chakra-engine.html)
|
||
- [An Inside Look at CVE-2017-0199 – HTA and Scriptlet File Handler Vulnerability](https://blog.fortinet.com/2017/06/05/an-inside-look-at-cve-2017-0199-hta-and-scriptlet-file-handler-vulnerability)
|
||
- [ANALYSIS OF A WIN32K NULL POINTER DEREFERENCE BY MATCHING THE MAY PATCH](https://xiaodaozhi.com/exploit/156.html)
|
||
- [Analysis of CVE-2017-11882 Exploit in the Wild](https://researchcenter.paloaltonetworks.com/2017/12/unit42-analysis-of-cve-2017-11882-exploit-in-the-wild/)
|
||
- [aPAColypse now: Exploiting Windows 10 in a Local Network with WPAD/PAC and JScript](https://googleprojectzero.blogspot.com/2017/12/apacolypse-now-exploiting-windows-10-in_18.html)
|
||
- [Arbitrary Code Guard vs. Kernel Code Injections](https://www.countercraft.eu/blog/post/arbitrary-vs-kernel/)
|
||
- [Breaking backwards compatibility: a 5 year old bug deep within Windows](http://www.triplefault.io/2017/07/breaking-backwards-compatibility-5-year.html)
|
||
- [Breaking out of Restricted Windows Environment](https://weirdgirlweb.wordpress.com/2017/06/14/first-blog-post/)
|
||
- [Bypassing Microsoft's Patch for CVE-2017-0199](http://justhaifei1.blogspot.com.br/2017/07/bypassing-microsofts-cve-2017-0199-patch.html)
|
||
- [C# Inject a Dll into a Process (w/ CreateRemoteThread)](http://www.codingvision.net/miscellaneous/c-inject-a-dll-into-a-process-w-createremotethread)
|
||
- [CVE-2018-8453 Win32k Elevation of Privilege Vulnerability Targeting the Middle East](https://ti.360.net/blog/articles/cve-2018-8453-win32k-elevation-of-privilege-vulnerability-targeting-the-middle-east-en/)
|
||
- [CVE-2018-8460: EXPOSING A DOUBLE FREE IN INTERNET EXPLORER FOR CODE EXECUTION](https://www.thezdi.com/blog/2018/10/18/cve-2018-8460-exposing-a-double-free-in-internet-explorer-for-code-execution)
|
||
- [DEFEATING DEVICE GUARD: A LOOK INTO CVE-2017-0007](https://enigma0x3.net/2017/04/03/defeating-device-guard-a-look-into-cve-2017-0007/)
|
||
- [Delving deep into VBScript - Analysis of CVE-2018-8174 exploitation](https://securelist.com/delving-deep-into-vbscript-analysis-of-cve-2018-8174-exploitation/86333/)
|
||
- [Detecting and mitigating elevation-of-privilege exploit for CVE-2017-0005](https://blogs.technet.microsoft.com/mmpc/2017/03/27/detecting-and-mitigating-elevation-of-privilege-exploit-for-cve-2017-0005/)
|
||
- [Digging Into a Windows Kernel Privilege Escalation Vulnerability: CVE-2016-7255](https://securingtomorrow.mcafee.com/mcafee-labs/digging-windows-kernel-privilege-escalation-vulnerability-cve-2016-7255/)
|
||
- [Disarming EMET 5.52: Controlling it all with a single write action](https://blog.ropchain.com/2017/04/03/disarming-emet-5-52/)
|
||
- [Enumerating process, thread, and image load notification callback routines in Windows](http://www.triplefault.io/2017/09/enumerating-process-thread-and-image.html)
|
||
- [EternalBlue – Everything there is to know](https://research.checkpoint.com/eternalblue-everything-know/)
|
||
- [Exploiting a Windows 10 PagedPool off-by-one overflow (WCTF 2018)](https://j00ru.vexillium.org/2018/07/exploiting-a-windows-10-pagedpool-off-by-one/)
|
||
- [Exploit Kit Rendezvous and CVE-2017-0022](https://0patch.blogspot.com/2017/09/exploit-kit-rendezvous-and-cve-2017-0022.html)
|
||
- [Exploiting MS16-145: MS Edge TypedArray.sort Use-After-Free (CVE-2016-7288)](https://blog.quarkslab.com/exploiting-ms16-145-ms-edge-typedarraysort-use-after-free-cve-2016-7288.html)
|
||
- [Exploiting MS16-098 RGNOBJ Integer Overflow on Windows 8.1 x64 bit by abusing GDI objects](https://sensepost.com/blog/2017/exploiting-ms16-098-rgnobj-integer-overflow-on-windows-8.1-x64-bit-by-abusing-gdi-objects/)
|
||
- [Exploring Windows virtual memory management](http://www.triplefault.io/2017/08/exploring-windows-virtual-memory.html)
|
||
- [EXPLOITING WINDOWS’ IP ID RANDOMIZATION BUG TO LEAK KERNEL DATA AND MORE (CVE-2018-8493)](https://menschers.com/2018/10/30/what-is-cve-2018-8493/)
|
||
- [From Out Of Memory to Remote Code Execution](https://speakerdeck.com/yukichen/from-out-of-memory-to-remote-code-execution)
|
||
- [Getting Code Execution on Windows by Abusing Default Kernel Debugging Setting](https://tyranidslair.blogspot.com/2017/03/getting-code-execution-on-windows-by.html)
|
||
- [Hardening Windows 10 with zero-day exploit mitigations](https://blogs.technet.microsoft.com/mmpc/2017/01/13/hardening-windows-10-with-zero-day-exploit-mitigations/)
|
||
- [Introduction to IA-32e hardware paging](http://www.triplefault.io/2017/07/introduction-to-ia-32e-hardware-paging.html)
|
||
- [Introduction to Windows shellcode development – Part 1](https://securitycafe.ro/2015/10/30/introduction-to-windows-shellcode-development-part1/)
|
||
- [Introduction to Windows shellcode development – Part 2](https://securitycafe.ro/2015/12/14/introduction-to-windows-shellcode-development-part-2/)
|
||
- [Introduction to Windows shellcode development – Part 3](https://securitycafe.ro/2016/02/15/introduction-to-windows-shellcode-development-part-3/)
|
||
- [Kernel Debugging 101 – Part1](https://vvalien1.wordpress.com/2016/12/26/kernel-debugging-101/)
|
||
- [Kernel Debugging 101 – Part2](https://vvalien1.wordpress.com/2017/01/01/kernel-debugging-101-part2/)
|
||
- [Kernel Debugging 101 – Part3](https://vvalien1.wordpress.com/2017/01/01/kernel-debugging-101-part3/)
|
||
- [Kernel Exploitation Case Study - "Wild" Pool Overflow on Win10 x64 RS2 (CVE-2016-3309 Reloaded)](https://siberas.de/blog/2017/10/05/exploitation_case_study_wild_pool_overflow_CVE-2016-3309_reloaded.html)
|
||
- [Kernel Exploit Demo - Windows 10 privesc via WARBIRD](https://blog.xpnsec.com/windows-warbird-privesc/)
|
||
- [Kernel Pool Overflow Exploitation In Real World – Windows 7](http://trackwatch.com/kernel-pool-overflow-exploitation-in-real-world-windows-7/)
|
||
- [Kernel Pool Overflow Exploitation In Real World – Windows 10](http://trackwatch.com/kernel-pool-overflow-exploitation-in-real-world-windows-10/)
|
||
- [Many Formulas, One Calc – Exploiting a New Office Equation Vulnerability](https://research.checkpoint.com/another-office-equation-rce-vulnerability/)
|
||
- [Marshalling to SYSTEM - An analysis of CVE-2018-0824](https://codewhitesec.blogspot.com/2018/06/cve-2018-0624.html)
|
||
- [Microsoft Kills Potential Remote Code Execution Vulnerability in Office (CVE-2017-8630)](https://securingtomorrow.mcafee.com/mcafee-labs/microsoft-kills-potential-remote-code-execution-vulnerability-in-office-cve-2017-8630/)
|
||
- [MS17-010: EternalBlue’s Large Non-Paged Pool Overflow in SRV Driver](http://blog.trendmicro.com/trendlabs-security-intelligence/ms17-010-eternalblue/)
|
||
- [MS OFFICE EXPLOIT ANALYSIS – CVE-2015-1641](http://www.sekoia.fr/blog/ms-office-exploit-analysis-cve-2015-1641/)
|
||
- [ON THE ROAD OF HIDING… PEB, PE FORMAT HANDLING AND DLL LOADING HOMEMADE APIS – PART 1](https://gbmaster.wordpress.com/2012/02/26/on-the-road-of-hiding-peb-pe-format-handling-and-dll-loading-homemade-apis-part-1/)
|
||
- [ON THE ROAD OF HIDING… PEB, PE FORMAT HANDLING AND DLL LOADING HOMEMADE APIS – PART 2](https://gbmaster.wordpress.com/2012/03/02/on-the-road-of-hiding-peb-pe-format-handling-and-dll-loading-homemade-apis-part-2/)
|
||
- [ON THE ROAD OF HIDING… PEB, PE FORMAT HANDLING AND DLL LOADING HOMEMADE APIS – PART 3](https://gbmaster.wordpress.com/2012/04/02/on-the-road-of-hiding-peb-pe-format-handling-and-dll-loading-homemade-apis-part-3/)
|
||
- [ON THE ROAD OF HIDING… PEB, PE FORMAT HANDLING AND DLL LOADING HOMEMADE APIS – LAST PART](https://gbmaster.wordpress.com/2012/04/17/on-the-road-of-hiding-peb-pe-format-handling-and-dll-loading-homemade-apis-last-part/)
|
||
- [Puppet Strings - Dirty Secret for Windows Ring 0 Code Execution](https://zerosum0x0.blogspot.com/2017/07/puppet-strings-dirty-secret-for-free.html?m=1)
|
||
- [Reading Your Way Around UAC (Part 1)](https://tyranidslair.blogspot.com/2017/05/reading-your-way-around-uac-part-1.html)
|
||
- [Reading Your Way Around UAC (Part 2)](https://tyranidslair.blogspot.com/2017/05/reading-your-way-around-uac-part-2.html)
|
||
- [Reading Your Way Around UAC (Part 3)](https://tyranidslair.blogspot.com/2017/05/reading-your-way-around-uac-part-3.html)
|
||
- [Reflective DLL Injection](https://0x00sec.org/t/reflective-dll-injection/3080)
|
||
- [Rotten Potato – Privilege Escalation from Service Accounts to SYSTEM](https://foxglovesecurity.com/2016/09/26/rotten-potato-privilege-escalation-from-service-accounts-to-system/)
|
||
- [sam-b/windows_kernel_resources](https://github.com/sam-b/windows_kernel_resources)
|
||
- [Sharks in the Pool :: Mixed Object Exploitation in the Windows Kernel Pool](http://srcincite.io/blog/2017/09/06/sharks-in-the-pool-mixed-object-exploitation-in-the-windows-kernel-pool.html)
|
||
- [Starting with Windows Kernel Exploitation – part 1 – setting up the lab](https://hshrzd.wordpress.com/2017/05/28/starting-with-windows-kernel-exploitation-part-1-setting-up-the-lab/)
|
||
- [Starting with Windows Kernel Exploitation – part 2 – getting familiar with HackSys Extreme Vulnerable Driver](https://hshrzd.wordpress.com/2017/06/05/starting-with-windows-kernel-exploitation-part-2/)
|
||
- [Starting with Windows Kernel Exploitation – part 3 – stealing the Access Token](https://hshrzd.wordpress.com/2017/06/22/starting-with-windows-kernel-exploitation-part-3-stealing-the-access-token/)
|
||
- [Tales from the MSRC: from pixels to POC](https://blogs.technet.microsoft.com/srd/2017/06/20/tales-from-the-msrc-from-pixels-to-poc/)
|
||
- [The Art of Becoming TrustedInstaller](https://tyranidslair.blogspot.co.id/2017/08/the-art-of-becoming-trustedinstaller.html)
|
||
- [The lonely potato](https://decoder.cloud/2017/12/23/the-lonely-potato/)
|
||
- [The Unpatched LSASS Remote Denial of Service (MS16-137)](https://www.coresecurity.com/blog/unpatched-lsass-remote-denial-service-ms16-137)
|
||
- [Using Binary Diffing to Discover Windows Kernel Memory Disclosure Bugs](http://googleprojectzero.blogspot.com/2017/10/using-binary-diffing-to-discover.html)
|
||
- [Windows 10 Creators Update 32-bit execution of ring-0 code from NULL page via NtQuerySystemInformation (class 185, Warbird functionality)](https://bugs.chromium.org/p/project-zero/issues/detail?id=1391)
|
||
- [Windows Exploit Development (primer) : Debugging Threads and Analyzing Memory](http://blog.k3170makan.com/2018/05/windows-exploit-development-primer.html)
|
||
- [Windows Exploit Development (primer II) : Corrupting Structured Exception Handling and Controlling Memory Pointers](http://blog.k3170makan.com/2018/05/windows-exploit-development-primer-ii.html)
|
||
- [Windows Exploitation and AntiExploitation Evolution](https://forums.juniper.net/t5/Security/Windows-Exploitation-and-AntiExploitation-Evolution/ba-p/329283)
|
||
- [Windows Exploitation Tricks: Arbitrary Directory Creation to Arbitrary File Read](https://googleprojectzero.blogspot.com/2017/08/windows-exploitation-tricks-arbitrary.html)
|
||
- [Windows kernel pool spraying fun - Part 1 - Determine kernel object size](http://theevilbit.blogspot.com/2017/09/pool-spraying-fun-part-1.html)
|
||
- [Windows kernel pool spraying fun - Part 2 - More objects](http://theevilbit.blogspot.com/2017/09/windows-kernel-pool-spraying-fun-part-2.html)
|
||
- [Windows kernel pool spraying fun - Part 3 - Let's make holes](http://theevilbit.blogspot.com/2017/09/windows-kernel-pool-spraying-fun-part-3.html)
|
||
- [Windows kernel pool spraying fun - Part 4 - object & pool headers, kex & putting it all together](http://theevilbit.blogspot.com/2017/09/windows-kernel-pool-spraying-fun-part-4.html)
|
||
- [Windows Kernel Exploitation Part 1](http://resources.infosecinstitute.com/windows-kernel-exploitation-part-1/)
|
||
- [Windows Kernel Exploitation Part 2](http://resources.infosecinstitute.com/kernel-exploitation-part-2/)
|
||
- [Windows Kernel Exploitation Part 3](http://resources.infosecinstitute.com/kernel-exploitation-part-3/)
|
||
- [Windows Kernel Exploitation Tutorial Part 1: Setting up the Environment](https://rootkits.xyz/blog/2017/06/kernel-setting-up/)
|
||
- [Windows Kernel Exploitation Tutorial Part 2: Stack Overflow](https://rootkits.xyz/blog/2017/08/kernel-stack-overflow/)
|
||
- [Windows Kernel Exploitation Tutorial Part 3: Arbitrary Memory Overwrite (Write-What-Where)](https://rootkits.xyz/blog/2017/09/kernel-write-what-where/)
|
||
- [Windows Kernel Exploitation Tutorial Part 4: Pool Feng-Shui –> Pool Overflow](https://rootkits.xyz/blog/2017/11/kernel-pool-overflow/)
|
||
- [Windows Kernel Exploitation Tutorial Part 5: NULL Pointer Dereference](https://rootkits.xyz/blog/2018/01/kernel-null-pointer-dereference/)
|
||
- [Windows Kernel Exploitation Tutorial Part 6: Uninitialized Stack Variable](https://rootkits.xyz/blog/2018/01/kernel-uninitialized-stack-variable/)
|
||
- [Windows Kernel Exploitation Tutorial Part 7: Uninitialized Heap Variable](https://rootkits.xyz/blog/2018/03/kernel-uninitialized-heap-variable/)
|
||
- [Windows Kernel Exploitation Tutorial Part 8: Use After Free](https://rootkits.xyz/blog/2018/04/kernel-use-after-free/)
|
||
- [Windows Kernel Exploitation – Arbitrary Overwrite](https://osandamalith.com/2017/06/14/windows-kernel-exploitation-arbitrary-overwrite/)
|
||
- [Windows Kernel Exploitation : This Time Font hunt you down in 4 bytes](https://www.slideshare.net/PeterHlavaty/windows-kernel-exploitation-this-time-font-hunt-you-down-in-4-bytes)
|
||
- [Windows Operating System Archaeology](https://www.slideshare.net/enigma0x3/windows-operating-system-archaeology)
|
||
- [Zero Day Zen Garden: Windows Exploit Development - Part 0 [Dev Setup & Advice]](http://www.shogunlab.com/blog/2017/08/11/zdzg-windows-exploit-0.html)
|
||
- [Zero Day Zen Garden: Windows Exploit Development - Part 1 [Stack Buffer Overflow Intro]](http://www.shogunlab.com/blog/2017/08/19/zdzg-windows-exploit-1.html)
|
||
- [Zero Day Zen Garden: Windows Exploit Development - Part 2 [JMP to Locate Shellcode]](http://www.shogunlab.com/blog/2017/08/26/zdzg-windows-exploit-2.html)
|
||
- [Zero Day Zen Garden: Windows Exploit Development - Part 3 [Egghunter to Locate Shellcode]](http://www.shogunlab.com/blog/2017/09/02/zdzg-windows-exploit-3.html)
|
||
|
||
#### Exploitation: Technique: Bypassing ASLR
|
||
|
||
_Any related techniques for ASLR bypassing_
|
||
|
||
- [Bypass ASLR with partial EIP overwrite](http://ly0n.me/2015/07/30/bypass-aslr-with-partial-eip-overwrite/)
|
||
- [Bypassing ASLR – Part I](https://sploitfun.wordpress.com/2015/05/08/bypassing-aslr-part-i/)
|
||
- [Bypassing ASLR – Part II](https://sploitfun.wordpress.com/2015/05/08/bypassing-aslr-part-ii/)
|
||
- [Bypassing ASLR – Part III](https://sploitfun.wordpress.com/2015/05/08/bypassing-aslr-part-iii/)
|
||
- [Bypass ASLR+NX Part 1](http://intx0x80.blogspot.com/2018/04/bypass-aslrnx-part-1.html)
|
||
- [Bypass ASLR+NX Part 2](https://intx0x80.blogspot.com/2018/04/bypass-aslrnx-part-2.html)
|
||
- [Exploit Mitigation Techniques - Address Space Layout Randomization (ASLR)](https://0x00sec.org/t/exploit-mitigation-techniques-address-space-layout-randomization-aslr/5452/1)
|
||
- [New bypass and protection techniques for ASLR on Linux](http://blog.ptsecurity.com/2018/02/new-bypass-and-protection-techniques.html)
|
||
|
||
#### Exploitation: Technique: Format Strings
|
||
|
||
- [Format String Exploitation Primer](https://borgandrew.blogspot.com/2017/01/h1-margin-bottom-0.html)
|
||
- [X86 EXPLOITATION 101: “FORMAT STRINGS” – I’LL TELL YA WHAT TO SAY](https://gbmaster.wordpress.com/2015/12/08/x86-exploitation-101-format-strings-ill-tell-ya-what-to-say/)
|
||
|
||
#### Exploitation: Technique: Heap Exploitation
|
||
|
||
- [Heap Exploitation](https://www.gitbook.com/book/dhavalkapil/heap-exploitation/details)
|
||
- [Heap Exploitation ~ Fastbin Attack](https://0x00sec.org/t/heap-exploitation-fastbin-attack/3627)
|
||
- [Heap Exploitation ~ Abusing Use-After-Free](https://0x00sec.org/t/heap-exploitation-abusing-use-after-free/3580)
|
||
- [Heap overflow using unlink](https://sploitfun.wordpress.com/2015/02/26/heap-overflow-using-unlink/)
|
||
- [Heap overflow using Malloc Maleficarum](https://sploitfun.wordpress.com/2015/03/04/heap-overflow-using-malloc-maleficarum/)
|
||
- [Heap Safari - Thread Local Caching](https://0x00sec.org/t/heap-safari-thread-local-caching/5054)
|
||
- [shellphishi/how2heap](https://github.com/shellphish/how2heap)
|
||
- [X86 EXPLOITATION 101: HEAP OVERFLOWS… UNLINK ME, WOULD YOU PLEASE?](https://gbmaster.wordpress.com/2014/08/11/x86-exploitation-101-heap-overflows-unlink-me-would-you-please/)
|
||
- [X86 EXPLOITATION 101: THIS IS THE FIRST WITCHY HOUSE](https://gbmaster.wordpress.com/2014/08/24/x86-exploitation-101-this-is-the-first-witchy-house/)
|
||
- [X86 EXPLOITATION 101: “HOUSE OF MIND” – UNDEAD AND LOVING IT…](https://gbmaster.wordpress.com/2015/06/15/x86-exploitation-101-house-of-mind-undead-and-loving-it/)
|
||
- [X86 EXPLOITATION 101: “HOUSE OF FORCE” – JEDI OVERFLOW](https://gbmaster.wordpress.com/2015/06/28/x86-exploitation-101-house-of-force-jedi-overflow/)
|
||
- [X86 EXPLOITATION 101: “HOUSE OF LORE” – PEOPLE AND TRADITIONS](https://gbmaster.wordpress.com/2015/07/16/x86-exploitation-101-house-of-lore-people-and-traditions/)
|
||
- [Understanding the Heap & Exploiting Heap Overflows](http://www.mathyvanhoef.com/2013/02/understanding-heap-exploiting-heap.html)
|
||
|
||
#### Exploitation: Technique: Integer Overflow
|
||
|
||
- [Integer Overflow](https://sploitfun.wordpress.com/2015/06/23/integer-overflow/)
|
||
- [X86 EXPLOITATION 101: “INTEGER OVERFLOW” – ADDING ONE MORE… AAAAAAAAAAAND IT’S GONE](https://gbmaster.wordpress.com/2015/08/13/x86-exploitation-101-integer-overflow-adding-one-more-aaaaaaaaaaand-its-gone/)
|
||
|
||
#### Exploitation: Technique: Return Oriented Programming
|
||
|
||
- [A ROP Primer solution 64-bit style](https://blog.techorganic.com/2015/10/09/a-rop-primer-solution-64-bit-style/)
|
||
- [Blind Return Oriented Programming 102](https://oddcoder.com/BROP-102/)
|
||
- [Interactive Beginner's Guide to ROP](https://bordplate.no/blog/en/post/interactive-rop-tutorial/)
|
||
- [Intro to ROP: ROP Emporium — Split](https://medium.com/@iseethieves/intro-to-rop-rop-emporium-split-9b2ec6d4db08)
|
||
- [Introduction to Return Oriented Programming (ROP)](https://ketansingh.net/Introduction-to-Return-Oriented-Programming-ROP/index.html)
|
||
- [Return-Oriented Programming (ROP) 101](https://www.tripwire.com/state-of-security/off-topic/vert-vuln-school-return-oriented-programming-rop-101/)
|
||
- [ROP Emporium](https://ropemporium.com/)
|
||
- [ROP Primer](https://speakerdeck.com/barrebas/rop-primer)
|
||
- [ropchain](http://www.kvakil.me/posts/ropchain/)
|
||
- [Sigreturn Oriented Programming](https://0x00sec.org/t/srop-signals-you-say/2890)
|
||
|
||
#### Exploitation: Technique: return-to-libc
|
||
|
||
_return-to-libc techniques_
|
||
|
||
- [Bypassing NX bit using return-to-libc](https://sploitfun.wordpress.com/2015/05/08/bypassing-nx-bit-using-return-to-libc/)
|
||
- [Bypassing NX bit using chained return-to-libc](https://sploitfun.wordpress.com/2015/05/08/bypassing-nx-bit-using-chained-return-to-libc/)
|
||
|
||
#### Exploitation: Technique: Shellcoding
|
||
|
||
- [A Primer to Windows x64 shellcoding](https://blahcat.github.io/2017/08/14/a-primer-to-windows-x64-shellcoding/)
|
||
- [Shellcoding for Linux and Windows Tutorial](http://www.vividmachines.com/shellcode/shellcode.html)
|
||
- [SLAE: Bind TCP Shell – Assignment 1](http://0xdeadcode.se/archives/637)
|
||
- [SLAE: Reverse TCP Shell – Assignment 2](http://0xdeadcode.se/archives/689)
|
||
- [SLAE: Egg Hunter – Assignment 3](http://0xdeadcode.se/archives/707)
|
||
|
||
#### Exploitation: Technique: Stack Exploitation
|
||
|
||
- [Buffer Overflow Explotation](https://0x00sec.org/t/buffer-overflow-explotation/3846/1)
|
||
- [Classic Stack Based Buffer Overflow](https://sploitfun.wordpress.com/2015/05/08/classic-stack-based-buffer-overflow/)
|
||
- [Exploiting 1-byte buffer overflows](https://www.welivesecurity.com/2016/05/10/exploiting-1-byte-buffer-overflows/)
|
||
- [PLAYING WITH CANARIES](https://www.elttam.com.au/blog/playing-with-canaries/)
|
||
- [Simple buffer overflow on a modern system](http://liveoverflow.com/blog/stack0_buffer_overflow_on_ubuntu.html)
|
||
- [Stack Based Buffer Overflows on x64 (Windows)](Stack Based Buffer Overflows on x64 (Windows))
|
||
- [Stack Clashing for Fun and Profit](http://nullprogram.com/blog/2017/06/21/)
|
||
- [When is something overflowing](https://www.slideshare.net/PeterHlavaty/overflow-48573748)
|
||
- [X86 EXPLOITATION 101: WHEN THE STACK GETS OVER ITS HEAD](https://gbmaster.wordpress.com/2014/06/18/x86-exploitation-101-when-the-stack-gets-over-its-head/)
|
||
- [X86 EXPLOITATION 101: BORN IN A SHELL](https://gbmaster.wordpress.com/2014/07/01/x86-exploitation-101-born-in-a-shell/)
|
||
- [X86 EXPLOITATION 101: “HOUSE OF SPIRIT” – FRIENDLY STACK OVERFLOW](https://gbmaster.wordpress.com/2015/07/21/x86-exploitation-101-house-of-spirit-friendly-stack-overflow/)
|
||
- [Your First Buffer Overflow](https://medium.com/@mackwage/your-first-buffer-overflow-89141a9a2941)
|
||
|
||
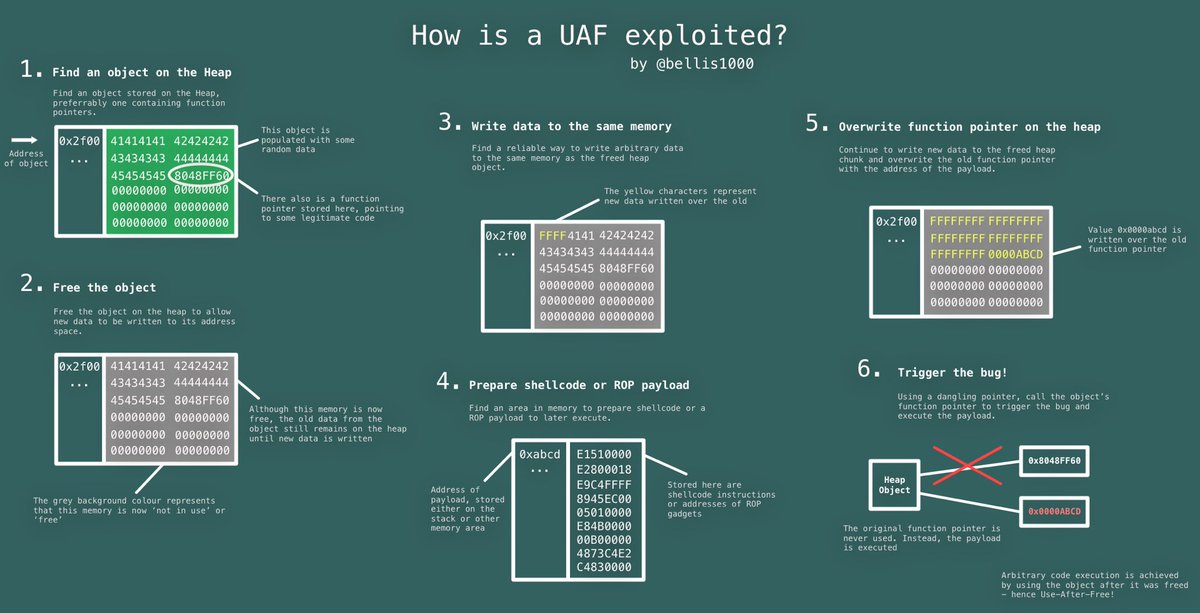
#### Exploitation: Technique Use-After-Free
|
||
|
||
|
||
|
||
- [Use-After-Free](https://sploitfun.wordpress.com/2015/06/16/use-after-free/)
|
||
|
||
#### Exploitation: Vulnerability: Speculative Side-Channel Attacks
|
||
|
||
- [A Deep Dive Analysis of Microsoft’s Kernel Virtual Address Shadow Feature](https://www.fortinet.com/blog/threat-research/a-deep-dive-analysis-of-microsoft-s-kernel-virtual-address-shadow-feature.html)
|
||
- [An accessible overview of Meltdown and Spectre, Part 1](https://blog.trailofbits.com/2018/01/30/an-accessible-overview-of-meltdown-and-spectre-part-1/)
|
||
- [An accessible overview of Meltdown and Spectre, Part 2](https://blog.trailofbits.com/2018/03/22/an-accessible-overview-of-meltdown-and-spectre-part-2/)
|
||
- [Explainer on #Spectre & #Meltdown](https://twitter.com/gsuberland/status/948907452786933762)
|
||
- [KVA Shadow: Mitigating Meltdown on Windows](https://blogs.technet.microsoft.com/srd/2018/03/23/kva-shadow-mitigating-meltdown-on-windows/)
|
||
- [Post-Spectre Threat Model Re-Think](https://chromium.googlesource.com/chromium/src/+/master/docs/security/side-channel-threat-model.md)
|
||
- [Reading privileged memory with a side-channel](https://googleprojectzero.blogspot.com/2018/01/reading-privileged-memory-with-side.html)
|
||
- [Total Meltdown?](https://blog.frizk.net/2018/03/total-meltdown.html)
|
||
|
||
### Hardening
|
||
|
||
- [nsacyber/Hardware-and-Firmware-Security-Guidance - Guidance for the Spectre, Meltdown, Speculative Store Bypass, Rogue System Register Read, Lazy FP State Restore, Bounds Check Bypass Store, TLBleed, and L1TF/Foreshadow vulnerabilities as well as general hardware and firmware security guidance. #nsacyber](https://github.com/nsacyber/Hardware-and-Firmware-Security-Guidance)
|
||
|
||
### Malware Analysis
|
||
|
||
|
||
|
||
- [A zebra in sheep’s clothing: How a Microsoft icon-display bug in Windows allows attackers to masquerade PE files with special icons](https://www.cybereason.com/labs-a-zebra-in-sheeps-clothing-how-a-microsoft-icon-display-bug-in-windows-allows-attackers-to-masquerade-pe-files-with-special-icons/)
|
||
- [Add-In Opportunities for Office Persistence](https://labs.mwrinfosecurity.com/blog/add-in-opportunities-for-office-persistence/)
|
||
- [Anti-debugging Techniques Cheat Sheet](http://antukh.com/blog/2015/01/19/malware-techniques-cheat-sheet/)
|
||
- [APT Groups and Operations](https://airtable.com/shr3Po3DsZUQZY4we/tbljpA5wI1IaLI4Gv/viwGFVFtuu0l88e7u)
|
||
- [baderj/domain_generation_algorithms - Some results of my DGA reversing efforts](https://github.com/baderj/domain_generation_algorithms)
|
||
- [Borrowing Microsoft Code Signing Certificate](https://blog.conscioushacker.io/index.php/2017/09/27/borrowing-microsoft-code-signing-certificates/)
|
||
- [Detecting Architecture in Windows](https://osandamalith.com/2017/09/24/detecting-architecture-in-windows/)
|
||
- [DOSfuscation: Exploring the Depths Cmd.exe Obfuscation and Detection Techniques](https://www.fireeye.com/content/dam/fireeye-www/blog/pdfs/dosfuscation-report.pdf)
|
||
- [Fast Flux networks: What are they and how do they work?](https://www.welivesecurity.com/2017/01/12/fast-flux-networks-work/)
|
||
- [FIN7 Group Uses JavaScript and Stealer DLL Variant in New Attacks](http://blog.talosintelligence.com/2017/09/fin7-stealer.html#more)
|
||
- [HIDING YOUR PROCESS FROM SYSINTERNALS](https://riscybusiness.wordpress.com/2017/10/07/hiding-your-process-from-sysinternals/)
|
||
- [High-reputation Redirectors and Domain Fronting](https://blog.cobaltstrike.com/2017/02/06/high-reputation-redirectors-and-domain-fronting/)
|
||
- [How to become the best Malware Analyst E-V-E-R](http://www.hexacorn.com/blog/2018/04/14/how-to-become-the-best-malware-analyst-e-v-e-r/)
|
||
- [Hunting For In-Memory .NET Attacks](https://www.endgame.com/blog/technical-blog/hunting-memory-net-attacks)
|
||
- [Hunting Malware with Memory Analysis](https://technical.nttsecurity.com/post/102egyy/hunting-malware-with-memory-analysis)
|
||
- [If memory doesn’t serve me right…](http://www.hexacorn.com/blog/2017/07/10/if-memory-doesnt-serve-me-right/)
|
||
- [MAEC - Malware Attribute Enumeration and Characterization | MAEC Project Documentation](https://maecproject.github.io)
|
||
- [MikroTik Cryptojacking Campaigns](https://docs.google.com/spreadsheets/d/1RdT_r4fi4wPx5rY306FftVKaXiAZeQeb5fx78DmbVx0/edit#gid=0)
|
||
- [PE File Infection Part I](https://0x00sec.org/t/pe-file-infection/401)
|
||
- [PE File Infection Part II](https://0x00sec.org/t/pe-file-infection-part-ii/4135)
|
||
- [So You Want To Be A Malware Analyst](https://blog.malwarebytes.com/security-world/2012/09/so-you-want-to-be-a-malware-analyst/)
|
||
- [Running programs via Proxy & jumping on a EDR-bypass trampoline](http://www.hexacorn.com/blog/2017/05/01/running-programs-via-proxy-jumping-on-a-edr-bypass-trampoline/)
|
||
- [Running programs via Proxy & jumping on a EDR-bypass trampoline, Part 2](http://www.hexacorn.com/blog/2017/10/04/running-programs-via-proxy-jumping-on-a-edr-bypass-trampoline-part-2/)
|
||
- [Running programs via Proxy & jumping on a EDR-bypass trampoline, Part 3](http://www.hexacorn.com/blog/2017/10/22/running-programs-via-proxy-jumping-on-a-edr-bypass-trampoline-part-3/)
|
||
- [Running programs via Proxy & jumping on a EDR-bypass trampoline, Part 4](http://www.hexacorn.com/blog/2017/10/29/running-programs-via-proxy-jumping-on-a-edr-bypass-trampoline-part-4/)
|
||
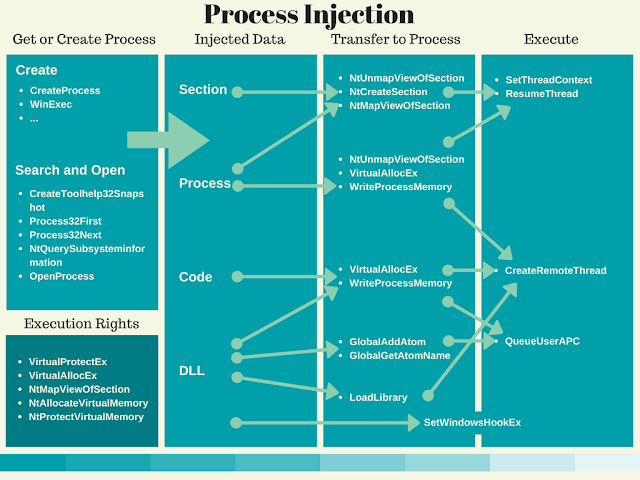
- [Ten Process Injection Techniques: A Technical Survey Of Common And Trending Process Injection Techniques](https://www.endgame.com/blog/technical-blog/ten-process-injection-techniques-technical-survey-common-and-trending-process)
|
||
- [The Archaeologologogology #3 – Downloading stuff with cmdln32](http://www.hexacorn.com/blog/2017/04/30/the-archaeologologogology-3-downloading-stuff-with-cmdln32/)
|
||
- [ThreatHuntingProject/ThreatHunting](https://github.com/ThreatHuntingProject/ThreatHunting)
|
||
- [Tips for Reverse-Engineering Malicious Code](https://zeltser.com/reverse-engineering-malicious-code-tips/)
|
||
- [Understanding Process Hollowing](https://andreafortuna.org/understanding-process-hollowing-b94ce77c3276)
|
||
- [Use of DNS Tunneling for C&C Communications](https://securelist.com/use-of-dns-tunneling-for-cc-communications/78203/)
|
||
- [Attacks on point-of-sales systems](https://www.symantec.com/content/dam/symantec/docs/white-papers/attacks-on-point-of-sale-systems-en.pdf)
|
||
- [Another Brick in the FrameworkPoS](https://www.trustwave.com/Resources/SpiderLabs-Blog/Another-Brick-in-the-FrameworkPoS/)
|
||
- [Backoff: New Point of Sale Malware](https://www.us-cert.gov/sites/default/files/publications/BackoffPointOfSaleMalware_0.pdf)
|
||
- [Bingo, Amigo! Jackpotting: ATM malware from Latin America to the World](https://securelist.com/atm-malware-from-latin-america-to-the-world/83836/)
|
||
- [Buy Candy, Lose Your Credit Card - Investigating PoS RAM Scraping Malware](https://www.rsaconference.com/writable/presentations/file_upload/hta-w01-buy-candy_-lose-your-credit-card-investigating-pos-ram-scraping-malware.pdf)
|
||
- [Follow The Money: Dissecting the Operations of the Cyber Crime Group FIN6](https://www2.fireeye.com/rs/848-DID-242/images/rpt-fin6.pdf)
|
||
- [New FrameworkPOS variant exfiltrates data via DNS requests](https://www.gdatasoftware.com/blog/2014/10/23942-new-frameworkpos-variant-exfiltrates-data-via-dns-requests)
|
||
- [PoS RAM Scraper Malware - Past, Present, and Future](https://www.wired.com/wp-content/uploads/2014/09/wp-pos-ram-scraper-malware.pdf)
|
||
- [RawPOS Technical Brief](http://sjc1-te-ftp.trendmicro.com/images/tex/pdf/RawPOS%20Technical%20Brief.pdf)
|
||
|
||
### Mobile Security
|
||
|
||
- [Four Ways to Bypass iOS SSL Verification and Certificate Pinning](https://blog.netspi.com/four-ways-to-bypass-ios-ssl-verification-and-certificate-pinning/)
|
||
- [Mobile Application Hacking Diary Ep.1](https://www.exploit-db.com/papers/26620/)
|
||
- [Mobile Application Hacking Diary Ep.2](https://www.exploit-db.com/papers/44145/)
|
||
- [tanprathan/MobileApp-Pentest-Cheatsheet](https://github.com/tanprathan/MobileApp-Pentest-Cheatsheet)
|
||
|
||
### Post Exploitation
|
||
|
||
#### Post Exploitation Platform: Linux
|
||
|
||
- [Exfiltrating credentials via PAM backdoors & DNS requests](https://x-c3ll.github.io//posts/PAM-backdoor-DNS/)
|
||
|
||
#### Post Exploitation Platform: Windows
|
||
|
||
- [infosecn1nja/AD-Attack-Defense - Active Directory Security For Red & Blue Team](https://github.com/infosecn1nja/AD-Attack-Defense)
|
||
- **Nested commands technique**: chain multiple commands with `&`, `&&`, `||`
|
||
- **Abusing legitimate executables**: using legitimate executables to execute intended commands e.g.
|
||
- `Rundll32.exe`: `rundll32.exe shell32.dll,ShellExec_RunDLL notepad.exe`
|
||
- Program Compatibility Assistant (pcalua): `pcalua.exe -a calc.exe`
|
||
- `SyncAppvPublishingServer.vbs` or `SyncAppvPublishingServer.exe`: `SyncAppvPublishingServer.exe "n; Start-Process notepad.exe"`
|
||
- [Evading Microsoft’s AutoRuns](https://blog.conscioushacker.io/index.php/2017/10/25/evading-microsofts-autoruns/)
|
||
- **Extension search order hijacking**: Manipulate extension search order which `.COM` has been looked for first before `.EXE` by making the actual `.EXE` disappeared and place dummy `.COM` with the same name as `.EXE` on the same directory
|
||
- **PowerShell injection vulnerability**: Use `SyncAppvPublishingServer.exe` to execute powershell cmdlet e.g. `SyncAppvPublishingServer.exe ".; Start-Process calc.exe`
|
||
- [Golden Ticket](https://pentestlab.blog/2018/04/09/golden-ticket/)
|
||
- [paranoidninja/CarbonCopy](A tool which creates a spoofed certificate of any online website and signs an Executable for AV Evasion. Works for both Windows and Linux
|
||
)
|
||
- [Post Exploitation Using NetNTLM Downgrade Attacks](https://www.optiv.com/blog/post-exploitation-using-netntlm-downgrade-attacks)
|
||
- [Top Five Ways I Got Domain Admin on Your Internal Network before Lunch (2018 Edition)](https://medium.com/@adam.toscher/top-five-ways-i-got-domain-admin-on-your-internal-network-before-lunch-2018-edition-82259ab73aaa)
|
||
|
||
##### DCShadow & DCSync
|
||
|
||
- [ACTIVE DIRECTORY ATTACK - DCSHADOW](https://www.c0d3xpl0it.com/2018/06/ad-attacks-dcshadow.html)
|
||
- [DCShadow](https://pentestlab.blog/2018/04/16/dcshadow/)
|
||
- [DCShadow - Minimal permissions, Active Directory Deception, Shadowception and more](http://www.labofapenetrationtester.com/2018/04/dcshadow.html)
|
||
- [DCShadow: Attacking Active Directory with Rouge DCs](https://blog.stealthbits.com/dcshadow-attacking-active-directory-with-rogue-dcs/)
|
||
- [DCShadow explained: A technical deep dive into the latest AD attack technique](https://blog.alsid.eu/dcshadow-explained-4510f52fc19d?gi=fe7b55fa3114)
|
||
|
||
##### Hot Potato
|
||
|
||
- [Hot Potato – Windows Privilege Escalation](https://foxglovesecurity.com/2016/01/16/hot-potato/)
|
||
|
||
#### Post Exploitation Platform: Unix/Linux
|
||
|
||
- [GTFOBins - GTFOBins is a curated list of Unix binaries that can be exploited by an attacker to bypass local security restrictions.](https://gtfobins.github.io/)
|
||
|
||
### Privacy
|
||
|
||
- [Digital Privacy at the U.S. Border: Protecting the Data On Your Devices](https://www.eff.org/wp/digital-privacy-us-border-2017)
|
||
- [Protecting Your Source When Releasing Sensitive Documents](https://source.opennews.org/articles/how-protect-your-sources-when-releasing-sensitive-/)
|
||
- [Secure Journalism at Protests](https://medium.com/@mshelton/secure-journalism-at-protests-a435b2d6398b)
|
||
- [Security Education Companion](https://sec.eff.org/)
|
||
- [Surveillance Self-Defense Checklist](https://medium.com/theintercept/surveillance-self-defense-for-journalists-ce627e332db6)
|
||
- [The Field Guide to Security Training in the Newsroom](https://the-field-guide-to-security-training-in-the-newsroom.readthedocs.io/en/latest/)
|
||
- [The Wired Guide to Digital Security](https://www.wired.com/2017/12/digital-security-guide/)
|
||
|
||
### Reverse Engineering
|
||
|
||
- [A Gentle Primer on Reverse Engineering](https://emily.st/2015/01/27/reverse-engineering/)
|
||
- [A Guide to ARM64 / AArch64 Assembly on Linux with Shellcodes and Cryptography](https://modexp.wordpress.com/2018/10/30/arm64-assembly/)
|
||
- [ELF hacking with Rekall](http://blog.rekall-forensic.com/2018/01/elf-hacking-with-rekall.html)
|
||
- [FAQ: How to learn reverse-engineering?](http://gynvael.coldwind.pl/?id=664)
|
||
- [How to decompile any Python binary](https://countercept.com/our-thinking/how-to-decompile-any-python-binary/)
|
||
- [Reverse Engineering 101](https://osandamalith.com/2014/12/31/reverse-engineering-101/)
|
||
|
||
### Tutorials
|
||
|
||
<table>
|
||
<tr>
|
||
<td>American Fuzzy Lop</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://kciredor.com/fuzzing-adobe-reader-for-exploitable-vulns-fun-not-profit.html">Fuzzing Adobe Reader for exploitable vulns (fun != profit)</a></li>
|
||
<li><a href="https://animal0day.blogspot.co.uk/2017/05/fuzzing-apache-httpd-server-with.html">Fuzzing Apache httpd server with American Fuzzy Lop + persistent mode</a></li>
|
||
<li><a href="https://irssi.org/2017/05/12/fuzzing-irssi/">Fuzzing Irssi</a></li>
|
||
<li><a href="https://symeonp.github.io/2017/09/17/fuzzing-winafl.html">Fuzzing the MSXML6 library with WinAFL</a></li>
|
||
<li><a href="https://www.sec-consult.com/en/blog/2017/09/hack-the-hacker-fuzzing-mimikatz-on-windows-with-winafl-heatmaps-0day/index.html">HACK THE HACKER – FUZZING MIMIKATZ ON WINDOWS WITH WINAFL & HEATMAPS (0DAY)</a></li>
|
||
<li><a href="https://www.softscheck.com/en/identifying-security-vulnerabilities-with-cloud-fuzzing/">How we found a tcpdump vulnerability using cloud fuzzing</a></li>
|
||
<li><a href="https://tunnelshade.in/blog/2018/01/afl-internals-compile-time-instrumentation/">Internals of AFL fuzzer - Compile Time Instrumentation</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Amazon Web Services (AWS)</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://github.com/open-guides/og-aws">open-guides/og-aws</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Binary Ninja</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://blog.trailofbits.com/2016/06/03/2000-cuts-with-binary-ninja/">2000 cuts with Binary Ninja</a></li>
|
||
<li><a href="https://binary.ninja/2017/10/01/automated-opaque-predicate-removal.html">Automated Opaque Predicate Removal</a></li>
|
||
<li><a href="http://www.chokepoint.net/2017/10/pin-visual-coverage-tool-for-binary.html">Pin Visual Coverage Tool For Binary Ninja</a></li>
|
||
<li><a href="https://blog.ret2.io/2017/10/17/untangling-exotic-architectures-with-binary-ninja/">Untangling Exotic Architectures with Binary Ninja</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>BloodHound</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="http://threat.tevora.com/lay-of-the-land-with-bloodhound/">Lay of the Land with BloodHound</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Docker</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://hackernoon.com/making-right-things-using-docker-7296cf0f6c6e">Making right things using Docker</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Elasticsearch</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://www.elastic.co/blog/a-practical-introduction-to-elasticsearch">A Practical Introduction to Elasticsearch</a></li>
|
||
<li><a href="https://elastalert.readthedocs.io/en/latest/elastalert.html">ElastAlert</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Frida</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="http://www.fuzzysecurity.com/tutorials/29.html">Application Introspection & Hooking With Frida</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>IDA Pro</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://qmemcpy.github.io/post/ida-series-1-hex-rays">IDA series, part 1: the Hex-Rays decompiler</a></li>
|
||
<li><a href="https://qmemcpy.github.io/post/ida-series-2-debugging-net">IDA series, part 2: debugging a .NET executable</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Masscan</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://danielmiessler.com/study/masscan/#gs.zhlnvjE">A Masscan Tutorial and Primer</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Mimikatz</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://adsecurity.org/?page_id=1821">Unofficial Guide to Mimikatz & Command Reference</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>MISP</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://github.com/remg427/misp42splunk/">remg427/misp42splunk</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>osquery</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://blog.trailofbits.com/2018/05/28/collect-ntfs-forensic-information-with-osquery/">Collect NTFS forensic information with osquery</a></li>
|
||
<li><a href="https://blog.trailofbits.com/2018/05/30/manage-your-fleets-firewalls-with-osquery/">Manage your fleet’s firewalls with osquery</a></li>
|
||
<li><a href="https://medium.com/@palantir/osquery-across-the-enterprise-3c3c9d13ec55">osquery Across the Enterprise</a></li>
|
||
<li><a href="https://blog.trailofbits.com/2017/10/10/tracking-a-stolen-code-signing-certificate-with-osquery/">Tracking a stolen code-signing certificate with osquery</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>PCILeech</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://sysdream.com/news/lab/2017-12-22-windows-dma-attacks-gaining-system-shells-using-a-generic-patch/">Windows DMA Attacks : Gaining SYSTEM shells using a generic patch</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>RunPE</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://www.adlice.com/runpe-hide-code-behind-legit-process/">RunPE: How to hide code behind a legit process</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Splunk</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://www.malwarearchaeology.com/s/Windows-Splunk-Logging-Cheat-Sheet-v20-spjb.pdf">The Windows Splunk Logging Cheat Sheet</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Sysmon</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="http://www.hexacorn.com/blog/2017/10/02/sysmon-doing-lines/">Sysmon doing lines</a></li>
|
||
<li><a href="https://github.com/MHaggis/sysmon-dfir">Mhaggis/sysmon-dfir</a></li>
|
||
<li><a href="http://syspanda.com/index.php/2017/02/28/deploying-sysmon-through-gpo/">Deploying Sysmon through Group Policy (GPO)</a></li>
|
||
<li><a href="http://syspanda.com/index.php/2017/03/03/sysmon-filtering-using-logstash/">Advanced Sysmon filtering using Logstash</a></li>
|
||
<li><a href="http://syspanda.com/index.php/2017/10/10/threat-hunting-sysmon-word-document-macro/">Threat Hunting with Sysmon: Word Document with Macro</a></li>
|
||
<li><a href="http://syspanda.com/index.php/2017/10/31/monitoring-monitor-sysmon-status/">Monitoring the monitor: Sysmon status</a></li>
|
||
<li><a href="https://github.com/olafhartong/sysmon-modular">olafhartong/sysmon-modular</a><li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Radare2</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://www.megabeets.net/a-journey-into-radare-2-part-1/">A journey into Radare 2 – Part 1: Simple crackme</a></li>
|
||
<li><a href="https://www.megabeets.net/a-journey-into-radare-2-part-2/">A journey into Radare 2 – Part 2: Exploitation</a></li>
|
||
<li><a href="https://www.megabeets.net/decrypting-dropshot-with-radare2-and-cutter-part-1/">Decrypting APT33’s Dropshot Malware with Radare2 and Cutter – Part 1</a></li>
|
||
<li><a href="https://www.megabeets.net/decrypting-dropshot-with-radare2-and-cutter-part-2/">Decrypting APT33’s Dropshot Malware with Radare2 and Cutter – Part 2</a></li>
|
||
<li><a href="https://leotindall.com/tutorial/an-intro-to-x86_64-reverse-engineering/">An Intro to x86_64 Reverse Engineering</a></li>
|
||
<li><a href="http://blog.superponible.com/2017/04/15/emulating-assembly-in-radare2/">Emulating Assembly in Radare2</a></li>
|
||
<li><a href="https://github.com/chrysh/ctf_writeups/tree/master/pwnable.kr">Pwnable.kr - Passcode</a></li>
|
||
<li><a href="https://radare2.securisec.com/">r2wiki</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>Volatility</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-1-image-identification-9343c077f8da">Volatility, my own cheatsheet (Part 1): Image Identification</a></li>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-2-processes-and-dlls-ba22050ba25a">Volatility, my own cheatsheet (Part 2): Processes and DLLs</a></li>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-3-process-memory-a0470f378ad2">Volatility, my own cheatsheet (Part 3): Process Memory</a></li>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-4-kernel-memory-and-objects-af9c022bf32c">Volatility, my own cheatsheet (Part 4): Kernel Memory and Objects</a></li>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-5-networking-ae92834e2214">Volatility, my own cheatsheet (Part 5): Networking</a></li>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-6-windows-registry-ddbea0e15ff5">Volatility, my own cheatsheet (Part 6): Windows Registry</a></li>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-7-analyze-and-convert-crash-dumps-and-hibernation-files-5d4b5b9c5194">Volatility, my own cheatsheet (Part 7): Analyze and convert crash dumps and hibernation files</a></li>
|
||
<li><a href="https://andreafortuna.org/volatility-my-own-cheatsheet-part-8-filesystem-5c1b710b091f">Volatility, my own cheatsheet (Part 8): Filesystem</a></li>
|
||
<li><a href="https://isc.sans.edu/forums/diary/Using+Yara+rules+with+Volatility/22950/">Using Yara rules with Volatility</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
<tr>
|
||
<td>WinDBG</td>
|
||
<td>
|
||
<ul>
|
||
<li><a href="https://vallejo.cc/2017/07/16/anti-antidebugging-windbg-scripts/">Anti-Antidebugging WinDbg Scripts</a></li>
|
||
<li><a href="https://github.com/bulentrahimkazanci/Windbg-Cheat-Sheet">bulentrahimkazanci/Windbg-Cheat-Sheet</a></li>
|
||
<li><a href="http://blog.talosintelligence.com/2017/08/windbg-and-javascript-analysis.html">WinDBG and JavaScript Analysis</a></li>
|
||
</ul>
|
||
</td>
|
||
</tr>
|
||
</table>
|
||
|
||
### Web Application Security
|
||
|
||
- [0xInfection/Awesome-WAF](https://github.com/0xInfection/Awesome-WAF)
|
||
- [BugBountyProtips ~ Collection](https://medium.com/@khaled.hassan/bugbountyprotip-collection-4a19e5b5b296)
|
||
- [Gaining access for HTTPS certificate by abusing RFC2142.](https://twitter.com/spazef0rze/status/942800411941048320)
|
||
- Using `admin@`, `administrator@`, `hostmaster@`, `postmaster@`, `webmaster@` for email address
|
||
- [List of bug bounty writeups](List of bug bounty writeups)
|
||
- [The 2018 Guide to Building Secure PHP Software](https://paragonie.com/blog/2017/12/2018-guide-building-secure-php-software)
|
||
|
||
#### Web Application Security: Technique: CORS
|
||
|
||
- [Exploiting CORS misconfigurations for Bitcoins and bounties](https://portswigger.net/blog/exploiting-cors-misconfigurations-for-bitcoins-and-bounties)
|
||
|
||
#### Web Application Security: Technique: Cross-site Request Forgery
|
||
|
||
- [What is CSRF , Preventions? And How to bypass the CSRF protection via XSS?](https://medium.com/@agrawalsmart7/what-is-csrf-how-to-bypass-the-csrf-protection-via-xss-55695f5789d7)
|
||
|
||
#### Web Application Security: Technique: Cross-site Scripting
|
||
|
||
- [BRUTE XSS - Master the art of Cross Site Scripting](https://brutelogic.com.br/blog/)
|
||
- [XSS Cheat Sheet](https://leanpub.com/xss)
|
||
|
||
#### Web Application Security: Technique: Serialization/Deserialization
|
||
|
||
- [Understanding Java deserialization](https://nytrosecurity.com/2018/05/30/understanding-java-deserialization/)
|
||
- [Why You Should Never Pass Untrusted Data to Unserialize When Writing PHP Code](https://www.netsparker.com/blog/web-security/untrusted-data-unserialize-php/)
|
||
|
||
#### Web Application Security: Technique: SQL Injection
|
||
|
||
- [MySQL UDF Exploitation](https://osandamalith.com/2018/02/11/mysql-udf-exploitation/)
|
||
- [NetSPI SQL Injection Wiki](https://sqlwiki.netspi.com/)
|
||
- [Your Pokemon Guide for Essential SQL Pen Test Commands](https://pen-testing.sans.org/blog/2017/12/09/your-pokemon-guide-for-essential-sql-pen-test-commands) |