54 KiB
| published |
|---|
| false |
Explainer
Self Sovereign Identity
- What is Self Sovereign Identity 2021-10-13 Florian Strauf
The important thing in SSI is that instead of a stamp on the plastic card, the credential is signed cryptographically by the issuer, enabling anyone to verify who issued the credentials. This makes verification much easier than in the physical world.
- #SSI gives its owner control over some aspects of identity, but not all 2021-12-14 Jolocom
Connections, relationships, and third-party issued credentials are not entirely self-sovereign, nor should they be. #JolocomAdvent #AdventCalendar
- What are Verifiable Credentials? Why do they matter? 2022-01-10 Fluree
Authority Does Not Require Centralized Power
As mentioned in my previous article, the trouble with centralization is that data is stored in a database. Once breached, a database can yield a treasure chest of information to be sold on the dark web.
- What Are Verifiable Credentials? And How Can They Build Digital Trust? 2022-02-01 Salesforce
Verifiable credentials and verifiable credential management technology offer a direct and secure channel between an organization and its stakeholders. Learn how they bring control over digital identity and build trust with organizations – from health credentials to college degrees.
- The Decentralized Identity Schelling Point 2023-03-01 Sarah Baldeo
Back to the Schelling Point - communication requires a common language and understanding. As governments, banks, hospitals, etc. navigate how best to homogenize authenticating user identities in multiple contexts, solutions will depend on user adoption. Maximizing adoption requires avoiding a Schelling point by creating a shared, accessible, and evolving Decentralized Identity Lexicon.
- [Video] Self-Sovereign Identity (SSI) Explained 2021-09-13 Animo
In this video, we explain how third parties get to see a lot of personal information about you that they don't really need. Whether it is your local supermarket or your new job, you're often sharing a lot of data when all they really need is a very simple yes or no answer
- Decentralizing Identity - Taking Back Control 2021-10-13 Madigan Solutions
In a nutshell, Self-Sovereign Identity allows individuals to manage their own identities by moving physical credentials to digital devices. An individual will receive a credential from an issuer which will be stored in their digital wallet.
- 17 Things You Should Know About Self Sovereign Identity 2021-10-29 Colin Iles
lessons I took away from asking tech identity experts Andrew Baker (Head of EC2 Engineering at AWS), our mystery guest and Marius Mare, to why we need self-sovereign identity and why it has such profound implications.
- [Video] Is Self Sovereign Identity Going Exponential - With Andrew Baker and A Suprise Guest 2021-10-27 Colin Iles
despite the technological revolution we are living through, identity management is still as objectionable as ever, which is allowing criminals and companies (particularly the social media giants) to know more about you than can ever be justifiable.
In this discussion I ask Andrew Baker, AWS's Head of EC2 Engineering and a surprise guest, to share their views on whether Self Sovereign Identity management could be the solution and how likely it is
- Self-Sovereign Identity: a Primer 2021-08-03 Hartmut Obendorf
Digital trust is often centralised, with select, well-known entities providing an anchor of trust that is propagated to everyone else; you are using this mechanism as you read this paragraph, having accessed a https: URL to find this article on your trusted platform, Medium.
- Why self-sovereign identity matters 2020-04-29 GlobalID
your digital identity represents you as a unique real-life person in a secure digital format. In fact, we likely have many different virtual identities across a spectrum of platforms and services.
- Distributed, Decentralized, Self-Sovereign Identity 2021-04-22 Condatis
With DID already being implemented, this new and exciting technology is due to shake up the digital identity space. We expect decentralized identity to continue making headway, with more and more sectors and businesses adopting the technology.
- Introduction to Self-Sovereign Identity 2021-03-28 Jakubkoci
In this article, I will do my best to explain self-sovereign identity from the end-user perspective, without any technicalities.
- Kaliya Young on Identikit with Michelle Dennedy 2021-08-25 IdentityWoman
our latest series examining the evolution of digital identity, and how self-sovereign identity, specifically, can advance a consent-based economy.
- Decentralized Identity Trilemma
There seems to exist a trilemma in decentralized identity analogous to @Zooko's triangle. None of the existing solutions are at the same time: 1) privacy-preserving, 2) Sybil-resistant 3) self-sovereign -[T]
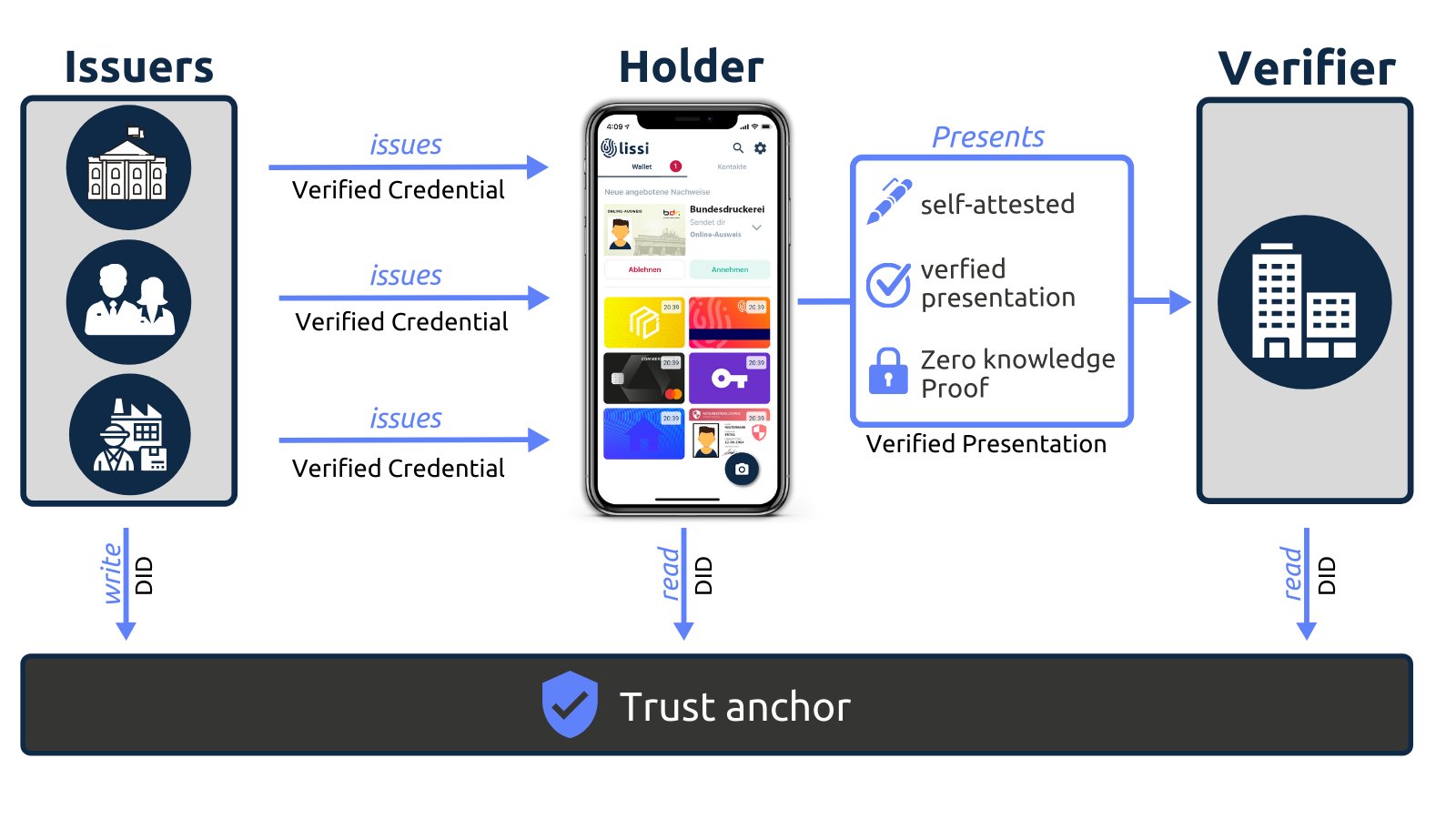
- When a user holds his:her own credentials locally on the phone, it creates a three-sided market 2020-12-04 Lissi ID
which puts the holder of the credential in the position of a carrier between issuer and verifiers.
- The Mental Models of Identity Enabled by SSI 2020-12-03 Adrian Doerk The Models: Space Time • Presentation • Attribute • Relationship • Capability
- Why is SSI becoming a necessity and what potential it holds? 2020-11-12 ACEBlock
- Natural persons and legal entities interact in the digital world with the same freedom and capacities as in the offline world (e. g. signing, authorizing documents, validating signatures, communicating privately etc.)
- Data is stored privately on a user device and not replicated numerous times across the digital world.
In other words, when a user “shares” data, it shares only the access to his/her data. And, as easy as one can do that, they can also revoke it (unless they are legally bound to share it for a certain period).
- The Implications of Bring Your Own Identity Identity Defined Security Alliance 2020-12-03
My short stint as “Mark Jannell" taught me a lot of about trust and ease of use in a bring your own identity model. Trust, as always in security, is essential to this new class of relationships and must be established and then protected from abuse. Ease of use, it turns out, is a key factor in protecting that trust and promoting the adoption of good identity patterns. I’m sure that I could have learned these lessons in some other way, but I’ll never forget my half year answering to a pseudonym.
- Evolution of Self-Sovereign Identity (SSI) 2021-11-16 LionsGate
The public keys of the user and the third-party organization for verifying the digital signature are recorded in a distributed ledger, and the user of the identity information verifies the provided information using them. In this way, users can control their own identity information without relying on a specific central administrator.
- Self-Sovereign Identity Crisis 2021-11-23 Lionsgate
Through deceptive marketing practices the first-movers in the Digital ID market have done-away with the sovereignty. As a result a burgeoning new industry is experiencing a Self-Sovereign Identity Crisis.
- Trusted Third Parties vs Self-Sovereign Identity 2021-12-30 Affinidi
All of us have multiple identities at any point. We are sons, daughters, brothers, sisters, parents, partners, friends, colleagues, and more to different people.
- A Future Built on Decentralized Identity 2021-12-22 Bloom
Decentralized identity is an emerging concept becoming more popular for online consumers by eliminating the need to pass personal identifiable information (PII) to an ever-increasing number of companies. However, in practice, decentralized identity has only existed for a handful of years, and its potential is still being discovered. So how did we get here?
- SSI Essentials: Everything you need to know about Decentralized Identity 2021-11-29 Gataca
Solving the identity paradox: the tradeoff between privacy, security, & user experience
- What is Self Sovereign Identity 2021-10-13 Florian Strauf
the digital representation of the identification process we know from the physical world. Things like showing our driver’s license to prove we are allowed to drive, or sending a bank statement to a real estate agent to prove our income and account balance.
- Self Sovereign Identity Explainer 2021-12-17 DIDAS Swiss (PDF
The Self Sovereign Identity Explainer (in German) is the basis for the future discussions and in-depth learning. It briefly introduces the development history of digital identity and roughly describes the different phases of identity in the Internet age.
- What Is Self-Sovereign Identity? 2020-04-28 Trinsic
Self-sovereign identity is the marriage of real identity with the digital world that will ultimately make people’s lives better.² It’s still in its infancy, and there is a long road ahead to truly make digital identity as legitimate and nuanced as a real-world identity.
- Explaining SSI to C-suite executives, and anyone else for that matter – John Phillips 2020-02-18 SSIMeetup
John Phillips from 460degrees in Australia has been exploring with his team for more than two years for a way to describe Self-Sovereign Identity (SSI) that was easy to understand. We think he has found a good method to make SSI easy to understand for any C-suite executive and business people that goes beyond the technology.
- Self-Sovereign Identity: The Ultimate Beginners Guide! 2021-02-23 101 Blockchains
Apart from addressing the pitfalls in conventional identity management systems, SSI allows better functionalities for all users. With a wide range of benefits and the self-sovereign identity blockchain applications, it is important to take a step towards adopting SSI solutions.
- [Video] Understanding the SSI Identity Model with Verifiable Credentials 2021-11-13 Manning
Drummond Reed, an expert in Internet identity, security, privacy, and trust frameworks, explains the basic building blocks of SSI and how this new identity model fundamentally works.
- The 5P’s of a Self-Sovereign Identity 2019-06-05 Dr Mark van Rijmenam
A self-sovereign identity can be defined by the 5P’s as it is personal (it is about you), portable (meaning you can take your identity and data from one platform to another), private (you control your identity and data), persistent (it does not change without your consent) and protected (they cannot steal your identity).
- Digital identities – steps on the path to an ID ecosystem 2021-03-18 Bankenverband
This article is very very good in articulating the big picture of how SSI systems relative to older system and emerging fragmetned systems.
An answer to these challenges is an ecosystem in which digital identity data can be exchanged in a way that is secure, reliable, scalable and convenient. This will have a positive impact on the economic future of Germany and Europe while at the same time enhancing the private sphere of the individual.
- Selective Disclosure: Share Just What You Want 2021-08-02 Affinidi
In the context of SSI, selective disclosure is best implemented through verifiable credentials where the user has separate credentials for each piece of information such as his/her date of birth, full name, vaccination details, address, passport number, etc.
- A beginner’s guide to self-sovereign identity (SSI) 2021-06-02 Domilabs
An issuer makes claims or assertions about a user. These claims are bundled together into verifiable credentials and given to the user, who stores them in their digital wallet. From there, they can decide which verifiers they want to present these credentials to.
- Self-Sovereign ID (SSI), The Unhackable Digital ID: What It Is and How It Works 2021-04 MemberPass
- The Siloed Model: The organization owns the member information, not the member.
- The Federated Model: The identity providers (IDP) owns the member data, not the member.
- The Best Model: SSI • The members own their own data!
- [Video] Karyl Fowler (Transmute) and Juan Caballero (DIF) present Intro to SSI at #IIW31 2020-10 Keryl Fowler, Juan Caballero Slides
Karyl and Juan revisited their slide deck from #IIW30 to give an overview of decentralized identity first as a "philosophy" at the confluence of ideological currents (Juan), and then as a set of specific emerging technologies which unlocks new mental models and business models that are still coming into focus sector by sector (Karyl). There follows a brief overview of educational resources, including some products of DIF's recent educational "content sprint," and a wide-ranging Q&A including podcast recommendations and how to navigate open standards for the first time. The slides are here, in downloadable and hyperlinked PDF form:
- [Video] Defining Self-Sovereign Identity with Kaliya Young 2021-06-02 Coding Over Cocktails
In this short preview, "Identity Woman" and digital identity advocate Kaliya Young tackles the issues around self-sovereign identity and how individuals are the rightful points of federation in sharing and controlling their online information.
- 19 FAQs on Verifiable Credentials and Self-Sovereign Identity 2021-05-31 Affinidi
This article has some FAQs on the basics of Verifiable Credentials (VCs) and Self-Sovereign Identity (SSI).
- Self-Sovereign Identity: What You Can/Can’t Do With SSI? 2021-06-24 Affinidi
it gives complete control and ownership of data to the individual entities as they can decide what data to share and with whom.
Beyond this encompassing vision, let’s drill down into the specifics to understand what you can and can’t do with SSI.
- The Basic Building Blocks of SSI 2020-07-29 Drummond Reed, Alex Preukschat Manning
In many cases these core concepts have been established for decades. What’s new is how they’re put together to create a new model for digital identity management. The purpose of this article is to quickly familiarize you with these seven basic building blocks from a conceptual and technical point-of-view.
- Verifiable credentials (aka digital credentials)
- Issuers, holders, and verifiers
- Digital wallets
- Digital agents and hubs
- Decentralized identifiers (DIDs)
- Blockchains
- Governance frameworks (aka trust frameworks)
- How to decentralize identity and empower individuals 2021-07-26 GlobalID
If the internet decentralized information and crypto decentralized money and payments, then verifiable credentials will decentralize identity. In this episode, we chat with Dev Bharel, the software architect leading the charge around verifiable credentials at GlobaliD.
- Self-Sovereign Identity: What’s the Big Deal? 2021-07-06 Affinidi, Hackernoon
Do you know where your digital credentials like your full name, date of birth, phone number, government ID, and other Personally Identifiable Information (PII) are stored online, and how they are used?
- Bright Story: Self Sovereign Identity 2019-05-05 Brightlands (EN)
the benefits (The good) of SSI are illustrated with a range of examples, comparing SSI-based business transactions to their current non-SSI-based equivalents and thus more cumbersome.
In addition, examples are given of the disadvantages (The bad); how SSI technology can be misused by unscrupulous organizations and how a combination of technology, knowledge and legislation could mitigate this risk.
Finally, we give examples of the harmful side (The ugly); how SSI technology can be used by criminals and what countermeasures are possible.
- How Verifiable Creds, Decentralized Identifiers and Blockchain Work Together for a Safer Internet 2021-08-22 Fluree, Hackernoon
Verifiable credentials, DIDs, and blockchain are evidence of what's to come: Web3, a more secure, widespread, machine-to-machine internet.
- Beyond basics: Expert Q&A about SSI with Dr. Milly Perry and Martin Schäffner 2021-06-01
In May, Dr. Milly Perry, blockchain expert and former research director at the Open University of Israel, had invited Martin Schäffner, the initiator of the SSI Working Group at the European Blockchain Association, to speak at a webinar of the Israeli Chamber of Information Technology (You can find the recording here). [...] Here is their exchange about Verifiable Credentials, biometrics, pitfalls and barriers, NFTs, the role of governments and the thing that could make SSI obsolete.
- Self-Sovereign Identity Allows YOU to Control Your Personal Data 2022-12-13 Imageware
SSI supports credential leveling, including:
- Authentication Assurance Levels (AAL) 1, 2 & 3
- Biometrics to protect your data
- Affirmation/Metadata SSI credentials can be used:
- In person or online
- For government, financial, or high trust applications (document verification markets)
- For asset ownership, decentralized finance (DeFi), and crypto markets
Security
- Getting Data Security Right Alan Michel
data security is about system-wide design, where many different elements need to fit together to create a working whole.
- ID Verification Threats On the Horizon 2022-03-31 Liminal Podcasts
Cognito's CEO Alain Meier joins the State of Identity host Cameron D’Ambrosi to dive into why industries beyond financial services are now in the market for identity verification. They also unpack the impact of synthetic identity fraud across verticals, and how platforms find the balance when building their onboarding processes.
- How Decentralized Identifiers Will Shape the Future of Identity 2020-11-09 HackerNoon
Hackers value personal information the most. 96% of hacking groups’ primary motive is intelligence gathering. Researchers at privacy website PrivacyAffairs.com found that you can obtain a person's full identity for the low price of $1,275.
- Security, Silos, and Sovereignty 2021-03-12 Daniel Hardman
Why portable security is the sleeper — but killer — feature for SSI
what’s cool about DIDs (besides their self-service creation) is that their metadata is cryptographically verifiable. That means that anyone in the world can tell whether the metadata is legit, in the blink of an eye, just by asking software to check some math. And it also means that you can build a transport-independent, tamper-proof, encrypted communication channel with whoever controls a DID.
- Impact of Self-Sovereign Identity on Cybersecurity 2022-04 Security Boulevard
How does this change the world of cybersecurity protection? Typically, bad actors approach cybersecurity attacks by developing solutions that exploit the attack vectors of their target victims.
There are 4 attack vector categories to self-sovereign identity that map directly to each element: Issuer, Holder, Trust Registry and Verifier.
Cryptography
- The Use of Self-Sovereign Identity With Zero-Knowledge Proof (ZKP) Data Driven Investor
- Part 5: How Zero-Knowledge Proofs (ZKPs) Enable Smarter Customer Insights, With Less Liability
Put simply, most organizations are unthinkingly collecting more data from customers, without understanding the true impact: the real costs to themselves, and to customers.
- Privacy-Preserving Authentication, Another Reason to Care about Zero-Knowledge Proofs —slideshare 2017-08-14 Clare Nelson
In the near future, privacy-preserving authentication methods will flood the market, and they will be based on Zero-Knowledge Proofs. IBM and Microsoft invested in these solutions many years ago.
- How to Explain Public-Key Cryptography and Digital Signatures to Anyone
Here’s an easy-to-understand analogy to help your non-technical friends and customers understand public keys and private keys, and how they relate to cryptography and digital signatures.
- Zero Knowledge Proofs 2021-11 Phil Windley
This problem was first explored by MIT researchers Shafi Goldwasser, Silvio Micali and Charles Rackoff in the 1980s as a way of combatting information leakage. The goal is to reduce the amount of extra information the verifier, Victor, can learn about the prover, Peggy.
Development
- Comparing X.509 Certificates with SSI Windley
X.509 certificates have been around for 40 years and have proven to be a trustworthy means of exchanging data. So, what are the differences between X.509 ceritificates and SSI? And what are the advantages of each?
- [resources] Getting Started with Self Sovereign Identity SSI 2021-03-29
The blog is my getting started with Self Sovereign identity. I plan to explore developing solutions using Self Sovereign Identities, the different services and evaluate some of the user cases in the next couple of blogs.
- Bootstrapping a VDR-based Fully Decentralized Object (FDO)/Credential Platform: VON Example 2021-07-26 Hyperonomy
What are the common/known strategies for bootstrapping a VDR-based decentralized credential/object platform? …asked naively on purpose. Strategies for placing the first/initial DIDs in the VDR? …presumably purposed to be the initial Issuer(s) of verifiable
- Challenges to Self-Sovereign Identity 2021-10-11 Damien Bod
The article goes through some of the challenges we face when using or implementing identity, authentication and authorization solutions using self sovereign identity. I based my findings after implementing and testing solutions and wallets with the following SSI solution providers: Trinsic MATTR.global Evernym Azure Active Directory Verifiable Credentials Different Wallets like Lissi SSI
Germany
- Decentralization is the Future of Digitization Jolocom
Digital identity data is introduced as having a positive impact on Germany’s future as well as Europe’s. Following, benefits of a decentralized identity based on a fully open infrastructure are given.
Markets
- What Will We Learn from the Market Failure of Digital Identity? Identiverse
We have a widely accepted Standard Model of Identity, or architecture, in which Subjects, Identity Providers and Relying Parties (aka Holders, Issuers and Verifiers) hold, present, exchange, use and/or consume digital identities.
Education
- Advocating for learner-centric badge systems We Are Open Coop
how do we advocate for learner-centric badge systems? This is the piece that we’ve been thinking about the past couple of weeks.
Architecture
- Crafting a “no-bs” SSI platform Aditya Santhanarn
Let’s look at a few pointers that I believe make it hard for the web3 protocols to work for businesses and users in general
Atla PRISM
- [Video] Self-Sovereign Identity (SSI) & Atala PRISM with Allison Fromm Cardano Catalyst Women
- [0:02:58] What is Identity?
- [0:04:14] Problems with Digital Identity
- [0:08:38] Solution: Self-Sovereign Identity (SSI)
- [0:15:55] Getting Started with SSI: A Catalyst Proposal
- [0:20:11] Conclusion
- [0:22:20] Core team
- [0:24:05] Questions
Reputation
- [Video] SSI & Proof of Reputation Catalyst Swarm
Join Frank Albanese (Snapbrillia), Lance Byrd (RootsID), Nick Mason (ProofSpace), Niels Kijf (Design Academy), Patrick Suzzi (F8 OSDE), Juan Sierra (HERG), Zoéys Welt, Brian Harper, Ashton Engberg, Ninh Tran (Snapbrillia) and many others as the community discusses the different what is SSI & Proof of Reputation and why it matters.
Big Picture
- Unwrapping the Decentralised Identity Landscape Affinidi
- Crossfunctionality Centre
I have developed a pet peeve for "technosolutionism": the notion that a sufficiently innovative technology can solve a social problem, or a business problem, without complex and nuanced changes to social and business practice.
Blockchain
GDPR
- Can Self-Sovereign Identity (SSI) fit within the GDPR? : a Conceptual Data Protection Analysis (Part II)
- Can Self-Sovereign Identity (SSI) fit within the GDPR?: a Conceptual Data Protection Analysis (Part I)
Government
Trending
-
New Encyclopedia entry Self-Sovereign Identity (SSI) Encyclopedia.pub
-
[Whitepaper] Self-Sovereign Identity Foundations, Applications, and Potentials of Portable Digital Identities 2021-09 Fraunhofer Institute for Applied Information Technology FIT
This paper analyses the SSI paradigm's conceptual characteristics and technical aspects and presents three use cases as examples. It becomes clear that SSI offers advantages in individual control, data security, and full portability of identities between different services. For example, forgeryand tamper-proof digital versions of important personal documents such as ID cards, passports, birth certificates or medical confirmations can be created. However, the use cases are not limited to personal SSI but can also be, for example, digital identities of organizations and physical objects in the context of IoT solutions. This is particularly important in connection with the comprehensive digitization of companies.
-
What is the Trust Triangle? Affinidi
The relationship between the issuers, holders, and verifiers is called the trust triangle simply because you need an element of trust among these entities for them to work together.
-
[WhitePaper] Self Sovereign Identity Phil Windley, Blockchain Research Institute
the relationship view of identity, the nature of authentic digital relationships, the trust bases of identity systems, and the architecture of the identity metasystem, including decentralized identifier communication and the self-sovereign Internet. He then explores how to operationalize digital relationships and the potential of generative identities (e.g., verifiable credentials) and credential exchange. He concludes with a deep dive into self-sovereign identities in production: the UK National Health Service staff passport, Bonifii’s MemberPass for credit unions, the International Air Transport Association Travel Pass, and others.
-
The Era of Self-Sovereign Identity ChakRay
Similar actions conducted in person do not represent the same amount of risk. For example, if someone asks you to verify your identity, we show our ID or driver’s license, and when you pay at the store, you provide your bank card. In this way, the control and the ownership of the data stays with you.
-
Blockchain Self-Sovereign Identity: True Control Of Your Identity Komodo Platform
The adoption of verifiable credentials is another fundamental part of the SSI concept. Verifiable credentials use a digital signature for identity claims by combining public-key hashing cryptography and privacy-protection techniques to convert credentials like ID cards to digital versions.
-
[Video] Exploring the Decentralized Web, Episode 4: Digital Identity Filecoin Foundation
Episode 4 explores the relationship between authentication and authorization, the rise of single sign-on platforms, and the advantages of and use cases for self-sovereign identity. Guests include Brian Behlendorf, Rainey Reitman, Danny O'Brien, Sarah Friend, Wendy Hanamura, Andrew Hill, and Brad Kam.
Presentation: https://bit.ly/3OmuIRx
Podcast: Digital Identity and Self Sovereignty Kaliya Young & Lucy Yang -Future of You
- The tools Kaliya and Lucy are developing to enable self-sovereign identities
- Whether anonymity or pseudonymity is feasible while maintaining accountability
- Wallet Wars: how might wallets evolve and consolidate across the public and private sector
-
myths and facts. Is Self-Sovereign Identity Dangerous? Jolocom (in german)
we examine more closely whether self-sovereign identity can increase or reduce risks for data misuse in certain cases.
-
Digital Identity Conspiracies ContinuumLoop
The only ones who will benefit from your digital ID are the Issuer (who gave you the credential), holder (you) and verifier (who you’re sharing it with).
-
What is Self-Sovereign Identity? Tangle Labs
-
SteveWilson Considering SSI critics
I reckon most cases of over-identification stem either from bad habits (e.g. RPs gathering circumstantial AuthN signals) or from Surveillance Capitalism. Either way, better deals for users will come from better design, not by weaponising Digital Identity (SSI, DIDs).
-
Understanding Verifiable Credentials Credivera
The value of verifiable credentials and the critical role they will play to our future digital identities is undeniable. As we enter a new era of online representation, trust in the internet will need to be vigorously robust.
-
Never mind who I am, ask me about my credentials John Phillips
Many (most) identity systems make a fundamental assumption that is built into their very architecture. This assumption creates three significant problems: privacy erosion; toxic data stores; and poor security.
-
Digital Identity Convenience Christine Martin, Continuum Loop
You will take back control of your identity and hold it. Not Facebook, not Google, and you will decide what credentials to share on a need-to-know basis. We don’t have to be scared of the shift; we have to ensure the architecture is built ethically for all
-
Understanding Verifiable Credentials by Credivera
The value of verifiable credentials and the critical role they will play to our future digital identities is undeniable. As we enter a new era of online representation, trust in the internet will need to be vigorously robust.
-
Rewiring the Internet with Self-Sovereign Identities.
In “Self-Sovereign Identity,” Johannes Sedlmeir makes a clear distinction between two concepts too often mixed: “identity” and “identifiers”. What we are experiencing in today’s Web are some external organizations identifying us as citizens, community members, customers, etc. But this isn’t our “identity.” Those are identifiers.
-
Digital Identities and Verifiable Credentials Johannes Sedlmeir • Reilly Smethurst • Alexander Rieger • Gilbert Fridgen Published October 2021
-
Myths about SSI Jolocom
The idea that as a user of SSI I have complete sovereignty over my digital identity is often misunderstood. At its core, SSI is about my digital identity being under my own control, so I can decide to whom I show my data, when, and for what.
-
What is Self-Sovereign Identity (SSI) with PeterMcCormack @justinrezvani (short clip)
-
Understanding Online Identity EducatedGuessWork (broad contextualization)
-
What are the main contributions of the Self-Sovereign Identity?
Identity represents a great asset. But we do not have control of this asset, as it is in the hands of organizations, governments, institutions, etc. These entities know everything about us from all this data.
-
[Video] The Future of Self-Sovereign Identity (SSI) Evernym
Drummond Reed and Alex Preukschat, co-authors of Manning Publication's new book 'Self-Sovereign Identity,' for a conversation on the book's development and recent release and what the future holds for SSI as a technology, architecture, and movement.
-
The Evolution of Digital Identity Tomas Hahn
How is it possible that the Internet has spread and developed to such an extent, while the unambiguous digital identification is not yet feasible?
-
Simple Definitions for Complex Terms in Decentralized Identity
-
What is Self-Sovereign Identity? TangleLabs
-
How Do Verifiable Credentials and Decentralized Identities Work?
Decentralized identity (DID) is a way for users to own their identity, using specific credentials to verify their identity to applications. These credentials, called Verifiable Credentials, enable you to do this. Verifiable Credentials are identity attestations that come from a trusted issuer, like proof of a workplace, student IDs, or official memberships.
-
SSI 101: Online identity and the history of identifiers Hypersign
This series is intended to be a basic, easy-to-understand introduction to SSI, but for a much deeper dive, check out Hypersign Labs — our technical blog. Here’s a good place to start on SSI:
-
Digital Identity: Past; Present; Future Hypersign
As a result of limited and known users there was no layer of identity and authentication in the design of internet framework. With the invention of the World Wide Web (WWW), the users made it a common platform for data sciences. Various sectors of society like health and finance have started using the internet for their services.
-
In-depth introduction to Self Sovereign Identity (SSI) Hypersign
-
What Is Self-Sovereign Identity? Trinsic
Eventually, SSI will give people a super simple way to do the following and more:
- Protect sensitive identity information like SSN and birthdates to reduce the likelihood and impact of identity theft
- Securely prove your identity or things about yourself in a way that institutions can trust
- Maintain privacy and reduce the ability for corporations or nefarious actors to track you without your consent
- Conveniently get access to services you need without usernames and passwords
-
The Self-Sovereign Identity (SSI) Basics Santanderigo
The very center of the digital identity is your documents: from your National ID or Passport to your degrees, mobile phone number, bank account number, or your medical records. Anything that is intrinsically bound to you is your data and therefore your identity. While talking about SSI these are called Verifiable Credentials (VC).
-
What is decentralized identity? In CSO
The DID model allows you to establish a relationship between your private key (your blockchain wallet) and your citizenship. The issuing authority signs off on the truth of your claim and, thereafter, third parties can check your public key to see that the holder of the private key is in fact a British citizen.
-
How Self-Sovereign Identity Works with Trinsic's Riley Hughes Georgian
- What is identity?
- The different ways Trinsic can be used by developers.
- Ways to disrupt or democratize the current model of identity.
- Decentralized identity and its many use cases.
- The continued need for anonymity in a digital identity world.
- How identity will evolve with web 3 and the metaverse.
-
Decentralization of Identity Exstalis
-
What is decentralized identity? CSO Online
-
The Journey of Decentralized Identity: Where It’s Been and Where It’s Going Trinsic
Our goal has been to completely abstract away the complexity of the ever-changing landscape so organizations can focus on the important stuff—what product to build, and how to take it to market. Teams shouldn’t have to “pick winners” and wager what to build on. Their products should be interoperable with multiple ecosystems. That’s what Trinsic is providing, out-of-the-box.
-
Self Sovereign Identity- Internet’s Missing Identity Layer 2022-02-02 Identrix
When the Internet was built, it was done so in a way that you would not know who you were connecting to. To get rid of this loophole, the TCP/IP protocol was introduced, which gives us the address of the computer we are connecting to, but nothing about the person, organisation or thing we are communicating with! We can see how that be potentially dangerous for any online user, making your devices highly susceptible not only to hacking but also to identity theft.
-
Can Decentralized Identity Give You Greater Control of Your Online Identity? 2022-07 Anonyome
-
Decentralized identifiers - Self-Sovereign Identity livebook Manning Manning
-
Worried About Digital Identity? - Continuum Loop Inc. Christine Martin
-
SSI (Self-Sovereign Identity): The Most Important Acronym You've Probably Never Heard Of A glimpse of VR & AR
-
For traditional identity models, the biggest misconception is “strong passwords” IDRamp
One way to avoid password-related problems is to use decentralized identity management. This method is relatively new, so the best way to gain knowledge about it – contact the experts. For this reason, we are speaking with Mike Vesey, CEO of IdRamp.
-
Introducing the Auth0 Research Program auth0
give direct input towards our product improvements and be the first choice for research recruiting opportunities.
-
Stoic Sovereign Identity (SSI) Simone Ravaioli
-
Digital Identity: Past; Present; Future Hypersign
-
In-depth introduction to Self Sovereign Identity (SSI) Hypersign
-
Future with Decentralized Identity SparkPlusTech
-
The changing landscape of digital identity by Tata Consultancy Services
-
Future with Decentralized Identity SparkPlusTech
-
The changing landscape of digital identity by Tata Consultancy Services
-
[Video] Identity Insights - Basics of Verifiable Credentials Indicio, Youtube
What are verifiable credentials? In this episode we are joined by Indicio software engineer Char Howland for an introduction to what this technology is and what it can do.
-
Decentralized identity: What it is, why it matters SC Magazine
-
Self-sovereign identity: an ecosystem of digital identities 2022 Ergon
Even though some questions are still unanswered, self-sovereign identities will unlock enormous economic value. If you want to get some initial experience with SSI you can try the available open-source technologies. A successful proof of concept will enable companies to see the possibilities of the new technology and harness this potential more effectively.
-
What is decentralized identity in blockchain? Cointelegraph
-
Are Self-Sovereign Identities on blockchain technology the future? 2022-09-01 Kook Content
-
Self-sovereign identity: an ecosystem of digital identities 2022 Ergon
-
The Top Five Misconceptions around Self-Sovereign Identity (SSI) Digital Stationary Consortium
We all have a cybersecurity problem, and SSI represents the most current thinking to address it. For that reason, we believe that SSI is not just another technology.
-
GlobaliD 101: Bring Your Own Identity GlobalID
There is a real opportunity to combine technology that is being developed with the concept of BYO Identity that will create a new identity framework where you own and control your data.
- Part 1: What a smart and humanistic approach to digital identity would like
- Part 2: The Trust Triangle — the system of issuers, holders, and verifiers that illustrates how identity works (and how it’s broken, today)
- Part 3: Why the ID Wallet is the first step toward achieving a new vision for digital identity
- Part 4: Why every company is an identity company
-
Centralized\Federated vs Self Sovereign dominiumssi
-
Self-sovereign identity: an ecosystem of digital identities Ergon
-
Many articles are being written about SSI, not all so excellent John Philip
Most are probably not "written" in the normally understood sense of the word (auto-scraping and ctrl-c and ctrl-v isn't writing). Many are probably not written by a person at all.
-
Centralized\Federated vs Self Sovereign dominiumssi
-
TOWARDS A USER-CENTRIC DIGITAL IDENTITY SYSTEM Irish Tech News
-
Debunking Common Misconceptions About Passwordless Authentication auth0
-
From DID to DeFi and EVM Metadium
-
A Beginners Guide to Decentralized Identifiers (DIDs) Veramo
-
10 Resources for beginners in Decentralized Identity (DID) Veramo
-
Self-Sovereign Identity: Taking Control Over Your Digital Identity Forbes 2022-09-26
The two main ingredients of SSI are verifiable credentials (VCs) and decentralized identifiers (DIDs).
-
Self-Sovereign Identity, Zero-Knowledge Proofs & the Future of Data Blockchain Australia
No other additional information is needed to complete this data exchange. So how do you know that the information being provided is authentic? The identity ‘proof’ uses a cryptographic hash function that confirms beyond any doubt that the identity claim is accurate.
-
The Importance of Self-Sovereign Identity Blockchain Solutions Zaisan
The public keys, as the name implies are there to view anytime and are used for exchanging information and can be revoked, however, the private key is for the account holder himself, be that an issuer, a verifier, or a subject. It is only through a private key that one can pass on his credentials using his DID to an issuer who then validates the credentials and sends them to the verifier using his DID.
-
WHAT’S DECENTRALIZED IDENTITY? 2022-10-06 NFTNewsToday
issuers or verifiers can only access the information shared by the DID holder. This information exchange can occur through various technologies, like NFC, QR, or Bluetooth. Zero-knowledge proofs are applied to restrict full information access. 2022-09-15
-
GlobaliD 101: Device-based identity
That way, your sensitive personal data is stored locally on your own device rather than hosted on some company’s server that becomes a target for hackers.
-
Decentralized Systems of Identity and Owning Your Own Data Coindesk
On this episode of “Money Reimagined,” hosts Michael Casey and Sheila Warren are together again but this time, at Converge22 by Circle. They discuss the challenges of identity and verification in the U.S. and in other countries with Daniel Buchner, head of decentralized identity at Block; and Chi Nnadi, the co-founder and CEO at Mara.
-
Introduction to Decentralized Identity IOTA Wiki