Signed-off-by: Daniel Gray <dngray@privacyguides.org> Signed-off-by: Freddy <freddy@privacyguides.org>
6.9 KiB
| title | icon | description |
|---|---|---|
| Qubes Overview | simple/qubesos | Qubes is an operating system built around isolating apps within *qubes* (formerly "VMs") for heightened security. |
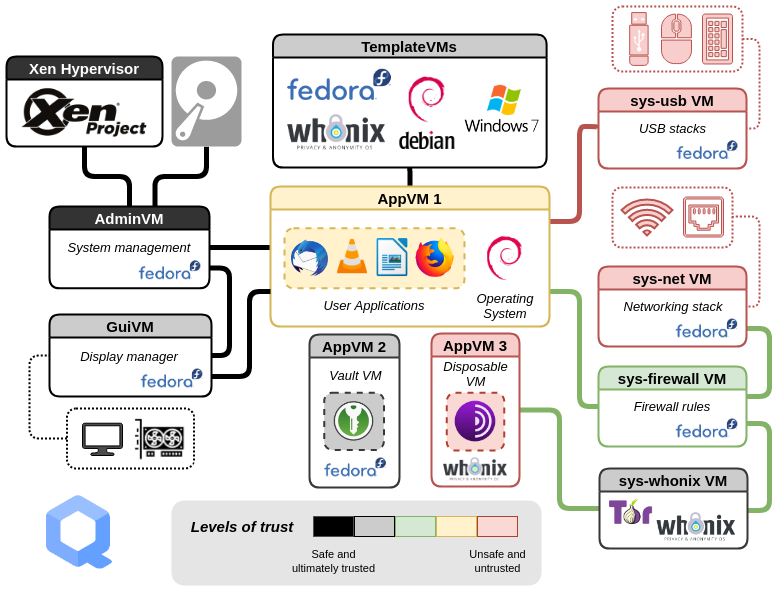
Qubes OS is an open-source operating system which uses the Xen hypervisor to provide strong security for desktop computing through isolated qubes, (which are Virtual Machines). You can assign each qube a level of trust based on its purpose. Qubes OS provides security by using isolation. It only permits actions on a per-case basis and therefore is the opposite of badness enumeration.
How does Qubes OS work?
Qubes uses compartmentalization to keep the system secure. Qubes are created from templates, the defaults being for Fedora, Debian and Whonix. Qubes OS also allows you to create once-use disposable qubes.
??? "The term qubes is gradually being updated to avoid referring to them as "virtual machines"."
Some of the information here and on the Qubes OS documentation may contain conflicting language as the "appVM" term is gradually being changed to "qube". Qubes are not entire virtual machines, but maintain similar functionalities to VMs.
Each qube has a colored border that can help you keep track of the domain in which it runs. You could, for example, use a specific color for your banking browser, while using a different color for a general untrusted browser.
Why Should I use Qubes?
Qubes OS is useful if your threat model requires strong security and isolation, such as if you think you'll be opening untrusted files from untrusted sources. A typical reason for using Qubes OS is to open documents from unknown sources, but the idea is that if a single qube is compromised it won't affect the rest of the system.
Qubes OS utilizes dom0 Xen VM for controlling other qubes on the host OS, all of which display individual application windows within dom0's desktop environment. There are many uses for this type of architecture. Here are some tasks you can perform. You can see just how much more secure these processes are made by incorporating multiple steps.
Copying and Pasting Text
You can copy and paste text using qvm-copy-to-vm or the below instructions:
- Press Ctrl+C to tell the qube you're in that you want to copy something.
- Press Ctrl+Shift+C to tell the qube to make this buffer available to the global clipboard.
- Press Ctrl+Shift+V in the destination qube to make the global clipboard available.
- Press Ctrl+V in the destination qube to paste the contents in the buffer.
File Exchange
To copy and paste files and directories (folders) from one qube to another, you can use the option Copy to Other AppVM... or Move to Other AppVM.... The difference is that the Move option will delete the original file. Either option will protect your clipboard from being leaked to any other qubes. This is more secure than air-gapped file transfer. An air-gapped computer will still be forced to parse partitions or file systems. That is not required with the inter-qube copy system.
??? "Qubes do not have their own filesystems."
You can [copy and move files](https://www.qubes-os.org/doc/how-to-copy-and-move-files/) between *qubes*. When doing so the changes aren't immediately made and can be easily undone in case of an accident. When you run a *qube*, it does not have a persistent filesystem. You can create and delete files, but these changes are ephemeral.
Inter-VM Interactions
The qrexec framework is a core part of Qubes which allows communication between domains. It is built on top of the Xen library vchan, which facilitates isolation through policies.
Connecting to Tor via a VPN
We recommend connecting to the Tor network via a VPN provider, and luckily Qubes makes this easy to do with a combination of ProxyVMs and Whonix.
After creating a new ProxyVM which connects to the VPN of your choice, you can chain your Whonix qubes to that ProxyVM before they connect to the Tor network, by setting the NetVM of your Whonix Gateway (sys-whonix) to the newly-created ProxyVM.
Your qubes should be configured in a manner similar to this:
| Qube name | Qube description | NetVM |
|---|---|---|
| sys-net | Your default network qube (pre-installed) | n/a |
| sys-firewall | Your default firewall qube (pre-installed) | sys-net |
| ==sys-proxyvm== | The VPN ProxyVM you created | sys-firewall |
| sys-whonix | Your Whonix Gateway VM | ==sys-proxyvm== |
| anon-whonix | Your Whonix Workstation VM | sys-whonix |
Additional Resources
For additional information we encourage you to consult the extensive Qubes OS documentation pages located on the Qubes OS Website. Offline copies can be downloaded from the Qubes OS documentation repository.
- Arguably the world's most secure operating system (Open Technology Fund)
- Software compartmentalization vs. physical separation (J. Rutkowska)
- Partitioning my digital life into security domains (J. Rutkowska)
- Related Articles (Qubes OS)