23 KiB
The worldwide neural control network
From the end of the second world war and mostly in the cold war remote neural control networks was develop.
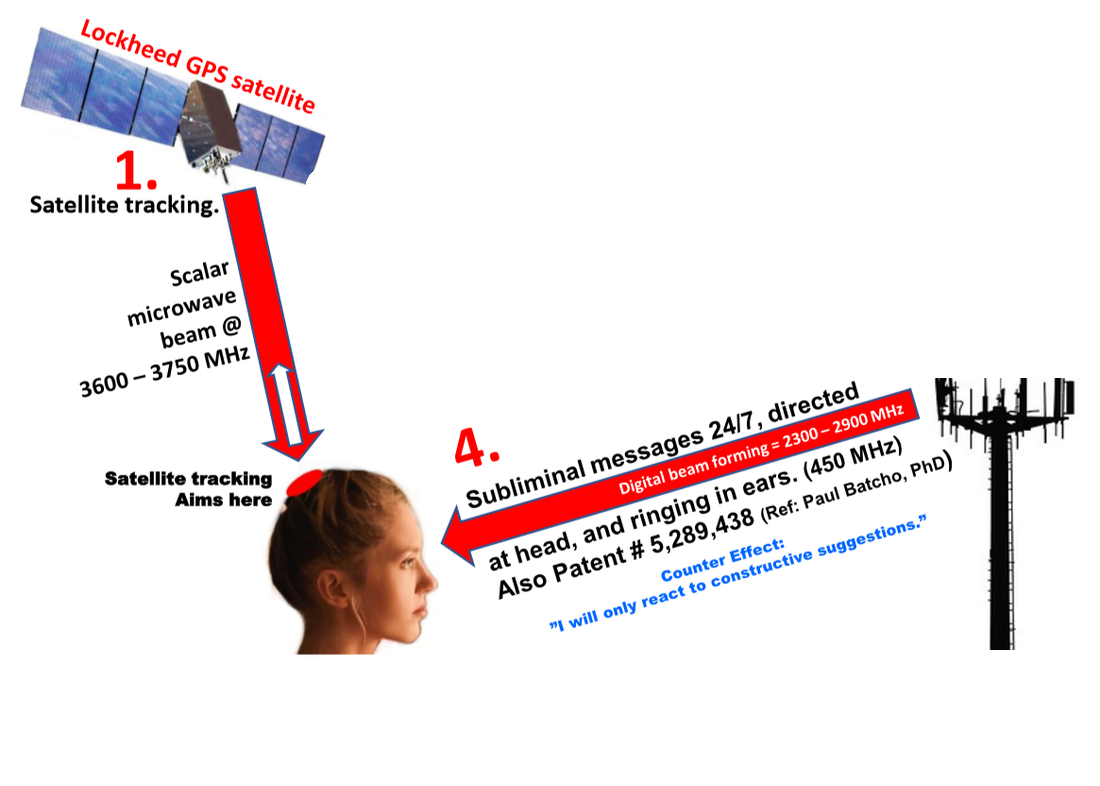
Nowadays it is a multi layer radio frequency networks like Internet tier division. Last mile is mixed between magnetic field are network to position and lock to the human and terrestrial waves towers.
It's a soap of different radio service, very complex to analyze because of a smoke curtain covering this type of networks. Why? Because in the past they was utilized by secret services and nowadays are utilized my a digital mafia that hack human brains. Manipulate masses. Change political views. Destroy families. Bet on suicides.
Something that is destroying the Europe Union and democracy
Who bind those services? Facilities that buy services from official providers that bind legal services and got also those services for big telecommunications clients. Normally are businessman that use to create B-side networks in a state and clean them in another with legal services. It's the digital mafia.
Last mile normally is soak into official infrastructure. It's not a secret all the patents are public. A lot of are from the US patents office but there is someone from India, Pakistan, China, Taiwan and Korea.
Who are target individuals? In the past terrorist, like ETA in Spain was controlled by remote neural networks. But in the last ten years someone become to speculate over those networks forcing human clients to join this hell because of data selling to big tech companies, military facilities and audiovisual industry. Because of big masses manipulation.
I'm in remote neural control because the madness of a mental sick mother and an inept father that didn't protect his son from this bitch. I'm in remote neural control from about twelve years. From when i came to live in Spain. Ten years of passive and two of active with subliminal voice to skull service. I've lost all what i've done, but not my mental clearness.
The service, because yes it is a service from a provider, was contracted in Spain by a military family derived girl that i know in Genoa, Italy, when i go in primary school. My parents have permitted it attaching drug abuse or some stupidity like this. This is only an horrible crime and they have done with my brain data and bet in my life thousand of millions of euro.
I'm public writing all of this because of justice. It's difficult to demonstrate but a very important person in Spain is helping me in this network. So i'm doing it. Thank you great man and person. I've lost the woman that i'm love to and this book is dedicated to her and her baby. They forced her to go out from our house five years ago.
Magnetic field area network, the radio steam machine
The magnetic field are network or MFAN is a terrestrial magnetic radio where they can identify exactly the position of the victim. More than this it's possible to practically physically the client or do sexual violence to him.
They call this steam machine.
With this virtual device the environment near the victim is like a tac machine. And it is continuously, the real mean is that we this system is carcinogenic for our brain and body.
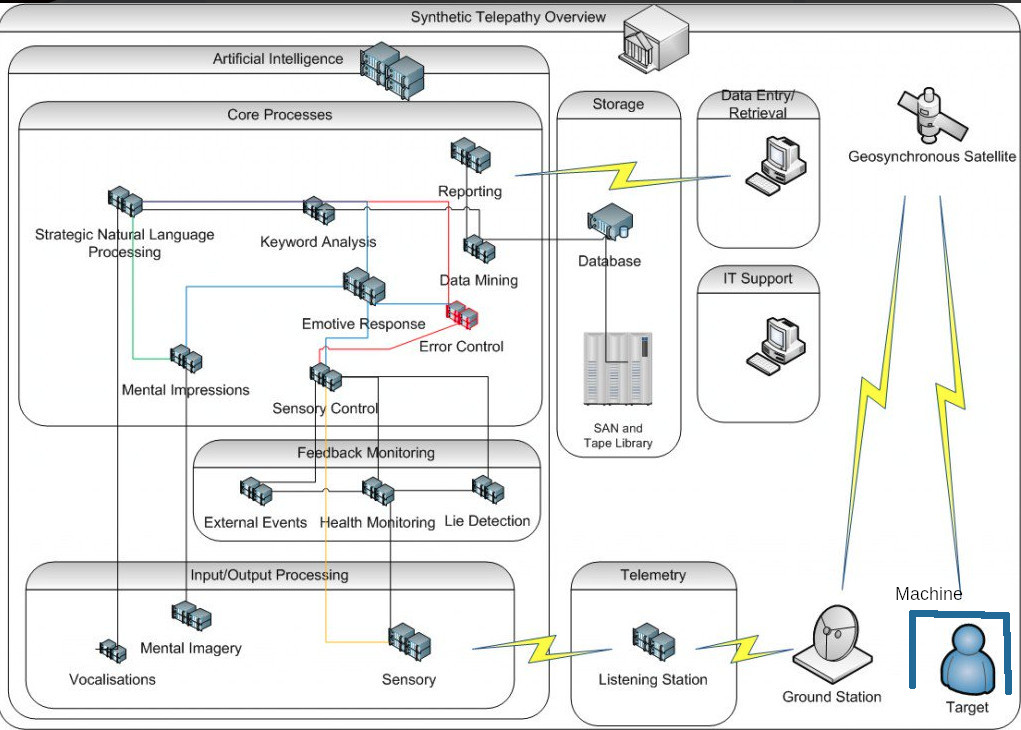
The synthetic telepathy network computing center
This is the network scheme of the "Illuminati" criminal network. Let's analyses device by device what is the synthetic telepathy network, a telecommunication facility that is changing in my opinion all Europe and is determining a right turning in our governments. It's very dangerous and probably it's the start of what i think it could be a neo nazism [1] digital dictatorship and a start of a alpha stage of what we found in Internet named as cyberwarfare [2].
In Internet we can find a lot of references about the synthetic telepathy network by metaphors [3], or what is called nowadays as Internet meme [4].
Let's introduce every device of the network scheme above:
- Target machine: A virtual device locked to the target person(s) by radio frequency. What does it mean? Every machine has an identification, a human unique magnetic field identification, an id to witch in a VPN [5] there's a correspondence with a remote virtual Android [6] device where we can find a lot of applications more or less powerful depending on what kind of access we've got in the network. A single Machine, later i will explain theory and technology about this death device, could be shared by many clients, usually humans but also animals, could determine a pyramid structure normally identified by a natural number, the mine in Barcelona for example is the number 9.
- Target in reality: one or more persons that doesn't have access to the administration of his Machine, she/he loose totally her/his privacy and all the time passed without access is considered like a slave. Many times she/he is also considered only like an object, they use to do experiments with the person to archive data under extreme stress, violent sex situations and brain experiments. The target individual is a human guinea pig in an unauthorized human subject research [7].
- Machine in metaphor: A mobile telephone, protected by a simple PIN [8] of four numbers. It's security it's so basic because allow gangstalker to steal money of the target machine or another client that doesn't know about basic security. Money are always in crypt concurrency [9].
- Target in metaphor: Is a dog, gangstalkers consider a target individual with the same rights of an animal. They give her/him orders, deny to her/him every types of rights, electronically punish her/him and hit her/him. So do practically all the persons connected to this system because if they doesn't torture the victim they loose privilege in the network and return to the victim state that is the initial state when you was forced to join this hell network with brain zapping, that is a technique used to find the unique magnetic identification of a human. It is archive using a physical Android device, normally a telephone. A victim is captured identifying is unique magnetic field id by proximity with another network client used like predator. Normally is a woman or a very attractive man that have sex with the victim, the predator has got her or his mobile infected by an application remotely controlled by the network owners. In Barcelona Spain i think that there are more than two hundred thousand clients connected.
- Bidirectional connection to target machine: Using a unique identification of the target person, or probably an array of, ground station speak directly with the victim or the client using RNM, remote neural monitoring. The remote neural monitoring act like a BCI [10], a TMS [11] device, a MRI [12] device; all of them are remote and virtual. All is done by radio frequency. All is remote brain waves. There is no need of any sort of device acting like a client in the human target. There is no need of brain implant [13].
- Remote brainwaves: This one of the last mile [14] technology used by the synthetic telepathy network. They are used to build what is known as BRAINnet [15], a sort of network of interconnected brains. In the synthetic telepathy network brainwaves [16] was hacked to archive the modulation of the eight neural oscillations that are present in our brain. The frequencies used by BRAINnet are from 0.5 to 100 Hz and are transmitted by analogue SDR [17]. Every type of brain wave is related to a part of our brain and to a specific function like the auditory cortex or the visual cortex. Those name are:
- Silent subliminal presentation system: a method from United States patent that serve to bypass first human auditory system, using the frequency of 462.25 KHz with a channel width of 14.5 KHz.
- Geosynchronous satellite: Used to obtain remote imaging of the target. Nowadays with the advent of the open hardware, middle size criminal organization could have a satellite in low orbit. This could be classified as satellite terrorism. Open hardware satellite [25] could be launch in orbit by companies that bind this service at relative low cost.
- Ground station: Is an access point to BRAINnet. To archive the full coverage of a territory like Catalunya there is no need of too many points because of wavelengths [26] from 100000 to 1000 kilometers and because at this frequencies there is no need of line of sight [27], waves can pass through many types of materials. Every ground station perhaps have got eight different physical radios and antennas, one for every type of brain wave, and an interface, fibre optic or another radio technology, for the backbone [28]. The backbone doesn't have the need to transport a lot of data so it can be build using low size technology and NLOS [29] radio and frequency.
- Telemetry
- Listening station : part of every ground station but not in the outside. Every target individual got his telemetry [30] saved in the network computing center, like all steps taken, all the trips and so on. There's no privacy in this network.
- Input/Output processing
- Vocalizations: in the synthetic telepathy network with technology the owners can exact copy the voice of a target. Not only the timbre of the voice but also the vocalization speech [31]. Targets individuals can be tricked to think to speak with another individual that is not. This is part of the mental confusion in which he may fall the victim in the gangstalking mind game. He may fall in mental disorder confusion. Vocalizations is modulated in gamma wave using a vocoder [32] and it results on voice to skull transmission, that is a hearing direct to the auditory cortex [33].
- Mental Imagery: in this network it's possible to do data injection direct to the visual cortex [34]. It's something very powerful they can archive augmented [35] and mixed reality [36] direct in our brain without using the human eye [37], that are organs of the visual system [38]. It's also possible to archive dream injections. They can obtain to stream a video in our brain when we are sleeping using the correct brainwave . Our dreams can also be read, they have archive to stole our dreams one of the most private and personal think of our personal sphere.
- Sensory: Like the auditory and visual cortex also the sensory cortex [39] can be tricked, injected and manipulated by remote brain waves. They can archive that our brain can reproduce unreal feelings in our body, like sexual excitement. In the synthetic telepathy network it's possible to force a woman or a man to have sex with a stalker, to be all the day exited and then s/he can be tricked in a machined situation to have a disproportionate orgies that can be remote filmed always by the network and then to be sold in VOD crypt concurrences systems. The worst think is that they can do this also to minors creating sexual slavery [40].
- Feedback monitoring
- External events: because of our visual cortex is under control, like in a MitM [41] environment, when we're victim of the synthetic telepathy network we are like a remote video camera. All what we do and we see is transmitted to the . What it can mean? Simple, our privacy and the privacy of whatever is under our line of sight is compromised. All what we write be pen or in a computer or in a cash dispenser is stolen. When we've sex all is transmitted, and so on. We're like a tool for hackers. What does it mean? Image a beautiful woman victim of the network. All the people that have sex with her are connected to the network. Woman can be like a Trojan horse [42].
- Health monitoring: With this machine owners of the synthetic telepathy network got physical health values of the targets individuals, like blood pressure [43], heart rate [44], human body temperature [45] and so on. They have the complete medical view of every human client connected to the network.
- Lie detection: owners of the network got also in their hands a full remote equipment of lie detection [46]. They know if the target lie or not about an argue. All is registered in the network core center.
- Core process
- Strategic Natural Language Processing: client who has got access to the services in BRAINnet could understand and speak a lot of different humans languages with them vocalization. This is possible by an advanced system of natural language processing [47] , a part of computer science concerned with the interactions between computers and human (natural) languages.
- Mental Impressions: i don't know what it can be.
- Keyword analysis: like a search engine [48]. In the core process of the synthetic telepathy network there is a keyword analysis [49] system that could react to certain word or phrases with artificial intelligence [50] bot that use known speech and vocalization of the victim. He can trust to speak with a real person but in reality is a chatbot [51]. This function also aliment the schizophrenia [52] and paranoia [53] of the target individual that is slowly condemned to go crazy.
- Emotive response: related to the different possible responses of the target individual among the artificial intelligence, chatbot, owners and machined situations proposed to him. All of this data are certainly used to improve the different algorithms inside the network but also probably sold to military and paramilitary forces that use human data to build robot and electronic cyberwarfare equipment. This is terrorism because target individuals are not volunteers but are unconscious victims. This is in opposition to the universal declaration of human rights [54].
- Data mining: always focused to the sold of data related to the target individual. Data mining [55] is the computer science and statistics part related to the extract of data set [56] in a large amount of data. What could be the meaning in a criminal point of view because of the target individual condition? It could be referred to the fact that all what the victim do is registered. Imagine when a person go to a big shopping center; what are the windows that mostly reclaim his attention? What products does he buy mostly when he go to a market? What are the colors that they attract him? And so on. All of those data are potentially sold to big firm companies, and are an important part of a commercial campaign if they are in big amount of individuals. They are also very important in a political point of view. Remember that target individuals aren't volunteers but they are obligated victims so we can always speak about terrorism. With BRAINnet in my opinion it's possible also to have a target individual that doesn't know to be because he doesn't listen to voice to skull telecommunication so only the visual cortex could be under control and only in read mode. What does it mean? It means that probably this network got thousand of victims and it probably mean that is the cause of the change in Europe these days.
- Reporting: Data reporting [57] is the fact to exactly report all the data set extracted from big data [58]
- Error control: referring to the control of percent of errors in the data reporting process.
- Sensory control: machines dedicated to the automatic control and regulation on all what append in the feedback monitoring facility. Certainly dominated by machine intelligence, machine learning [59] and neural network [60].
- Artificial Intelligence: all in the synthetic telepathy network, or BRAINnet, is absolutely dominated by machine intelligence. I think that there isn't a big crew of administrators but there is a lot of excellent programmers. I've found connections with the Neuralink [61] project by Elon Musk [62] and what have said Mark Zuckerberg [63] at F8 conference in 2017 [64].
External links
- https://en.wikipedia.org/wiki/Neo-Nazism
- https://en.wikipedia.org/wiki/Cyberwarfare
- https://en.wikipedia.org/wiki/Metaphor
- https://en.wikipedia.org/wiki/Internet_meme
- https://en.wikipedia.org/wiki/Virtual_private_network
- https://en.wikipedia.org/wiki/Android_(operating_system)
- https://en.wikipedia.org/wiki/Human_subject_research
- https://en.wikipedia.org/wiki/Personal_identification_number
- https://en.wikipedia.org/wiki/Cryptocurrency
- https://en.wikipedia.org/wiki/Brain%E2%80%93computer_interface
- https://en.wikipedia.org/wiki/Transcranial_magnetic_stimulation
- https://en.wikipedia.org/wiki/Magnetic_resonance_imaging
- https://en.wikipedia.org/wiki/Brain_implant
- https://en.wikipedia.org/wiki/Last_mile
- http://www.BRAINnet.net/
- https://en.wikipedia.org/wiki/Neural_oscillation
- https://en.wikipedia.org/wiki/Software-defined_radio
- https://en.wikipedia.org/wiki/Delta_wave
- https://en.wikipedia.org/wiki/Theta_wave
- https://en.wikipedia.org/wiki/Mu_wave
- https://en.wikipedia.org/wiki/Sensorimotor_rhythm
- https://en.wikipedia.org/wiki/Alpha_wave
- https://en.wikipedia.org/wiki/Beta_wave
- https://en.wikipedia.org/wiki/Gamma_wave
- https://www.google.com/search?q=open+hardware+satellite
- https://en.wikipedia.org/wiki/Wavelength
- https://en.wikipedia.org/wiki/Line-of-sight_propagation
- https://en.wikipedia.org/wiki/Backbone_network
- https://en.wikipedia.org/wiki/Non-line-of-sight_propagation
- https://en.wikipedia.org/wiki/Telemetry
- https://en.wikipedia.org/wiki/Speech
- https://en.wikipedia.org/wiki/Vocoder
- https://en.wikipedia.org/wiki/Auditory_cortex
- https://en.wikipedia.org/wiki/Visual_cortex
- https://en.wikipedia.org/wiki/Augmented_reality
- https://en.wikipedia.org/wiki/Mixed_reality
- https://en.wikipedia.org/wiki/Human_eye
- https://en.wikipedia.org/wiki/Visual_system
- https://en.wikipedia.org/wiki/Primary_somatosensory_cortex
- https://en.wikipedia.org/wiki/Sexual_slavery
- https://en.wikipedia.org/wiki/Man-in-the-middle_attack
- https://en.wikipedia.org/wiki/Trojan_Horse
- https://en.wikipedia.org/wiki/Blood_pressure
- https://en.wikipedia.org/wiki/Heart_rate
- https://en.wikipedia.org/wiki/Human_body_temperature
- https://en.wikipedia.org/wiki/Lie_detection
- https://en.wikipedia.org/wiki/Natural_language_processing
- https://en.wikipedia.org/wiki/Search_engine_(computing)
- https://en.wikipedia.org/wiki/Search_engine_optimization
- https://en.wikipedia.org/wiki/Artificial_intelligence
- https://en.wikipedia.org/wiki/Chatbot
- https://en.wikipedia.org/wiki/Schizophrenia
- https://en.wikipedia.org/wiki/Paranoia
- https://www.un.org/en/universal-declaration-human-rights/
- https://en.wikipedia.org/wiki/Data_mining
- https://en.wikipedia.org/wiki/Data_set
- https://en.wikipedia.org/wiki/Data_reporting
- https://en.wikipedia.org/wiki/Big_data
- https://en.wikipedia.org/wiki/Machine_learning
- https://en.wikipedia.org/wiki/Neural_network
- https://en.wikipedia.org/wiki/Neuralink
- https://en.wikipedia.org/wiki/Elon_Musk
- https://en.wikipedia.org/wiki/Mark_Zuckerberg
- https://newsroom.fb.com/news/2017/04/f8-2017-day-1/x