mirror of
https://github.com/Decentralized-ID/decentralized-id.github.io.git
synced 2024-10-01 01:05:54 -04:00
145 lines
24 KiB
Markdown
145 lines
24 KiB
Markdown
---
|
||
title : "Self Sovereign Identity (SSI)"
|
||
excerpt: >
|
||
In a nutshell, Self-Sovereign Identity allows individuals to manage their own identities by moving physical credentials to digital devices. An individual will receive a credential from an issuer which will be stored in their digital wallet.
|
||
description : "Self-sovereign identity is the marriage of real identity with the digital world that will ultimately make people’s lives better."
|
||
image : "/images/sovereign-identity.webp"
|
||
permalink: /self-sovereign-identity/
|
||
canonical_url: 'https://decentralized-id.com/self-sovereign-identity/'
|
||
redirect_from:
|
||
- /literature/self-sovereign-identity/
|
||
- /self-sovereign-identity
|
||
- /self-sovereign-identity/
|
||
categories: ["About"]
|
||
tags: ["Self Sovereign Identity","Laws of Identity","RWoT","IIW","Learning Machine","Sovrin Foundation","Evernym"]
|
||
last_modified_at: 2023-06-22
|
||
---
|
||
|
||
## About Self Sovereign Identity
|
||
* [The Off Chain Internet: Decentralized Identity & Verifiable Credentials - Evin McMullen](https://www.youtube.com/watch?v=EZ_Bb6j87mg) 2022-02-19 ETH Denver
|
||
*FANTASTIC NEW TALK!!!!*
|
||
> i'm excited to share with you a little bit more about the web 3 beyond the chain. Public ledgers are where we hang out most of the time, but the best of web 3 is yet to be because it hasn't yet been built and embraced fully by all of us.
|
||
* [Decentralized identity: The Direct Presentation model](https://techcommunity.microsoft.com/t5/identity-standards-blog/decentralized-identity-the-direct-presentation-model/ba-p/3071981) 2022-02-02 Microsoft
|
||
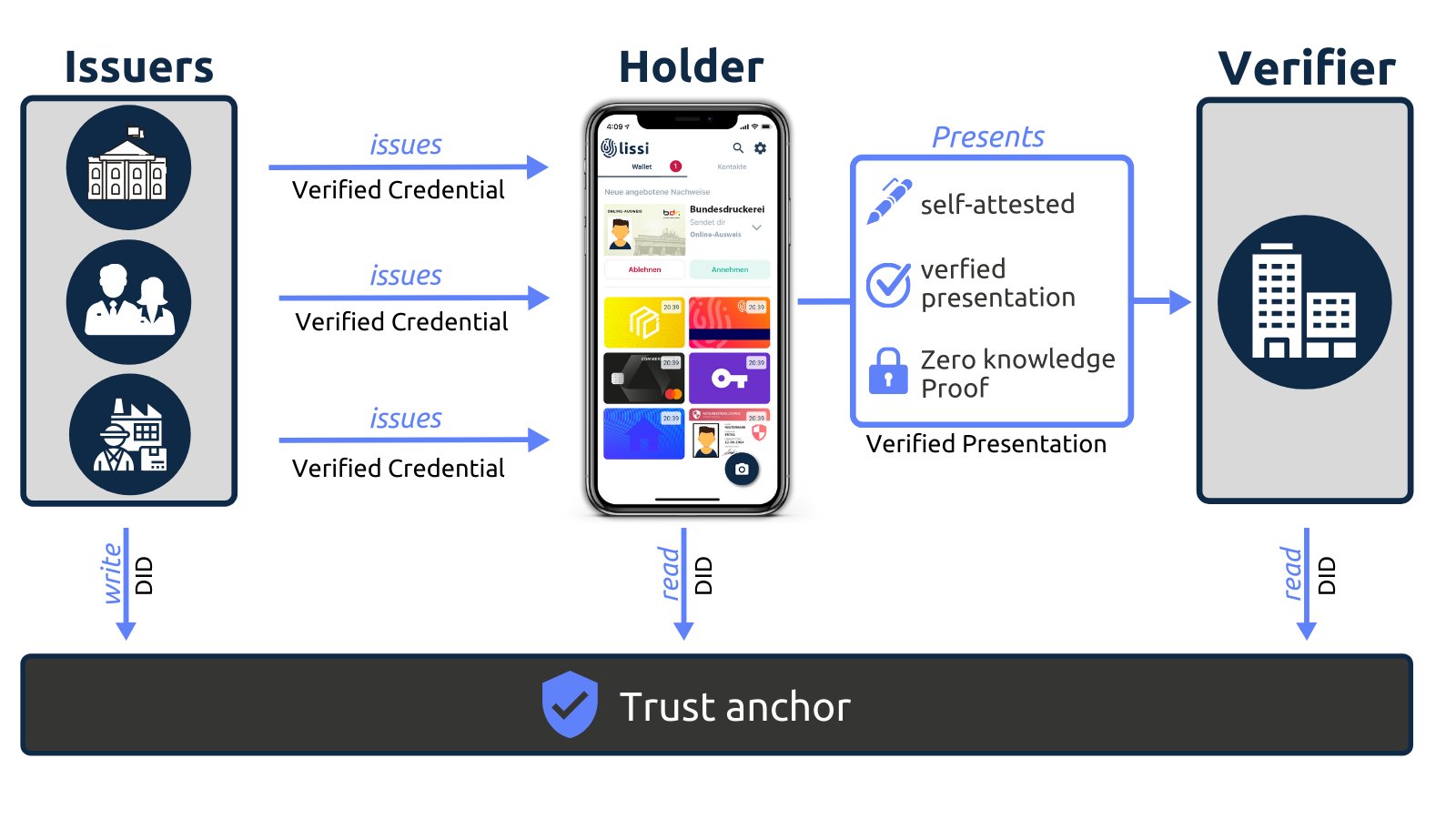
> The technical name for the model at work here is called the Direct Presentation model. A credential is issued, and then held for a long period of time with intermittent voluntary presentations to many different verifiers. To put that back into our example, my auto club issues me a card, which I hold in my wallet for years (maybe decades!), and I might choose to show that card to a garage when I need a tow, or possibly to a store to get a discount.
|
||
* [Video] [Exploring the Decentralized Web, Episode 4: Digital Identity](https://www.youtube.com/watch?v=jm8y56KMkIw) 2022-01-05 Filecoin Foundation
|
||
> Episode 4 explores the relationship between authentication and authorization, the rise of single sign-on platforms, and the advantages of and use cases for self-sovereign identity. Guests include Brian Behlendorf, Rainey Reitman, Danny O'Brien, Sarah Friend, Wendy Hanamura, Andrew Hill, and Brad Kam.
|
||
* [#SSI gives its owner control over some aspects of identity, but not all](https://twitter.com/GETJolocom/status/1470791578780413953) 2021-12-14 Jolocom
|
||
> Connections, relationships, and third-party issued credentials are not entirely self-sovereign, nor should they be. #JolocomAdvent #AdventCalendar
|
||
* [A Future Built on Decentralized Identity](https://bloom.co/blog/a-future-built-on-decentralized-identity/) 2021-12-22 Bloom
|
||
> Decentralized identity is an emerging concept becoming more popular for online consumers by eliminating the need to pass personal identifiable information (PII) to an ever-increasing number of companies. However, in practice, decentralized identity has only existed for a handful of years, and its potential is still being discovered. So how did we get here?
|
||
* [SSI Essentials: Everything you need to know about Decentralized Identity](https://gataca.io/blog/ssi-essentials-everything-you-need-to-know-about-decentralized-identity/) 2021-11-29 Gataca
|
||
> Solving the identity paradox: the tradeoff between privacy, security, & user experience
|
||
* [Self-Sovereign Identity Crisis](https://lionsgate.io/self-sovereign-identity-crisis/) 2021-11-23 Lionsgate
|
||
> Through deceptive marketing practices the first-movers in the Digital ID market have done-away with the sovereignty. As a result a burgeoning new industry is experiencing a Self-Sovereign Identity Crisis.
|
||
* [Video] [Understanding the SSI Identity Model with Verifiable Credentials](https://www.youtube.com/watch?v=TRuz39SEX7E) 2021-11-13 Manning
|
||
> Drummond Reed, an expert in Internet identity, security, privacy, and trust frameworks, explains the basic building blocks of SSI and how this new identity model fundamentally works.
|
||
* [What is Self Sovereign Identity](https://medium.com/coinmonks/what-is-self-sovereign-identity-a8087b2bf0ea) 2021-10-13 Florian Strauf
|
||
> the digital representation of the identification process we know from the physical world. Things like showing our driver’s license to prove we are allowed to drive, or sending a bank statement to a real estate agent to prove our income and account balance.
|
||
* [Video] [Is Self Sovereign Identity Going Exponential - With Andrew Baker and A Suprise Guest](https://www.youtube.com/watch?v=caZnuTBJ_TM) 2021-10-27 Colin Iles
|
||
> despite the technological revolution we are living through, identity management is still as objectionable as ever, which is allowing criminals and companies (particularly the social media giants) to know more about you than can ever be justifiable.
|
||
>
|
||
> In this discussion I ask Andrew Baker, AWS's Head of EC2 Engineering and a surprise guest, to share their views on whether Self Sovereign Identity management could be the solution and how likely it is
|
||
* [Decentralizing Identity - Taking Back Control](https://www.madigansolutions.com/blog/decentralizing-identity-taking-back-control/) 2021-10-13 Madigan Solutions
|
||
> In a nutshell, Self-Sovereign Identity allows individuals to manage their own identities by moving physical credentials to digital devices. An individual will receive a credential from an issuer which will be stored in their digital wallet.
|
||
* [What is Self Sovereign Identity](https://medium.com/coinmonks/what-is-self-sovereign-identity-a8087b2bf0ea) 2021-10-13 Florian Strauf
|
||
> The important thing in SSI is that instead of a stamp on the plastic card, the credential is signed cryptographically by the issuer, enabling anyone to verify who issued the credentials. This makes verification much easier than in the physical world.
|
||
* [Video] [Self-Sovereign Identity (SSI) Explained](https://www.youtube.com/watch?v=kJAapPG_jBY) 2021-09-13 Animo
|
||
> In this video, we explain how third parties get to see a lot of personal information about you that they don't really need. Whether it is your local supermarket or your new job, you're often sharing a lot of data when all they really need is a very simple yes or no answer
|
||
* [Self-Sovereign Identity: a Primer](https://medium.com/@hartmut.obendorf/self-sovereign-identity-a-primer-ee3d7066348a) 2021-08-03 Hartmut Obendorf
|
||
> Digital trust is often centralised, with select, well-known entities providing an anchor of trust that is propagated to everyone else; you are using this mechanism as you read this paragraph, having accessed a https: URL to find this article on your trusted platform, Medium.
|
||
* [Self-Sovereign Identity: What’s the Big Deal?](https://hackernoon.com/self-sovereign-identity-whats-the-big-deal-6i1a37z3) 2021-07-06 Affinidi, Hackernoon
|
||
> Do you know where your digital credentials like your full name, date of birth, phone number, government ID, and other Personally Identifiable Information (PII) are stored online, and how they are used?
|
||
* [A beginner’s guide to self-sovereign identity (SSI)](https://domilabs.io/beginners-guide-ssi/) 2021-06-02 Domilabs
|
||
> An issuer makes claims or assertions about a user. These claims are bundled together into verifiable credentials and given to the user, who stores them in their digital wallet. From there, they can decide which verifiers they want to present these credentials to.
|
||
* [Distributed, Decentralized, Self-Sovereign Identity](https://condatis.com/news/blog/did-decentralized-ssi/) 2021-04-22 Condatis
|
||
> With DID already being implemented, this new and exciting technology is due to shake up the digital identity space. We expect decentralized identity to continue making headway, with more and more sectors and businesses adopting the technology.
|
||
* [Video] [Karyl Fowler (Transmute) and Juan Caballero (DIF) present Intro to SSI at #IIW31](https://www.youtube.com/watch?v=DaM0UtQTLCs) 2020-10 Keryl Fowler, Juan Caballero [Slides](https://drive.google.com/file/d/1_9jCcxgcCrL4Dfjvr4z7XSIwxfadjveR/view?usp=sharingQ)
|
||
> Karyl and Juan revisited their slide deck from #IIW30 to give an overview of decentralized identity first as a "philosophy" at the confluence of ideological currents (Juan), and then as a set of specific emerging technologies which unlocks new mental models and business models that are still coming into focus sector by sector (Karyl). There follows a brief overview of educational resources, including some products of DIF's recent educational "content sprint," and a wide-ranging Q&A including podcast recommendations and how to navigate open standards for the first time. The slides are here, in downloadable and hyperlinked PDF form:
|
||
* [What Is Self-Sovereign Identity?](https://trinsic.id/what-is-self-sovereign-identity/) 2020-04-28 Trinsic
|
||
> Self-sovereign identity is the marriage of real identity with the digital world that will ultimately make people’s lives better.² It’s still in its infancy, and there is a long road ahead to truly make digital identity as legitimate and nuanced as a real-world identity.
|
||
* [Explaining SSI to C-suite executives, and anyone else for that matter – John Phillips](https://ssimeetup.org/explaining-ssi-c-suite-executives-anyone-else-john-phillips-webinar-48/) 2020-02-18 SSIMeetup
|
||
> John Phillips from 460degrees in Australia has been exploring with his team for more than two years for a way to describe Self-Sovereign Identity (SSI) that was easy to understand. We think he has found a good method to make SSI easy to understand for any C-suite executive and business people that goes beyond the technology.
|
||
* [How Verifiable Creds, Decentralized Identifiers and Blockchain Work Together for a Safer Internet](https://hackernoon.com/how-verifiable-creds-decentralized-identifiers-and-blockchain-work-together-for-a-safer-internet-k2u37bk) 2021-08-22 Fluree, Hackernoon
|
||
> Verifiable credentials, DIDs, and blockchain are evidence of what's to come: Web3, a more secure, widespread, machine-to-machine internet.
|
||
* [Introduction to Decentralized Identity](https://wiki.iota.org/identity.rs/decentralized_identity) IOTA Wiki
|
||
> Decentralized Identity or Self-Sovereign Identity (SSI) defines a new method for identity management and authentication. It removes the centralized aspects and puts the Identity subject in full control over its own identity. Decentralized Identity provides a solution for the increasing amount of database breaches, the lack of trust in any digital setting, and the increasingly difficult to comply with privacy legislation, such as GDPR.
|
||
* [Self-Sovereign Identity — wiki.p2pfoundation](https://wiki.p2pfoundation.net/Self-Sovereign_Identity) 2019-11-13 P2P Foundation
|
||
> The beauty of sovereignty isn't complete and total control, but rather balance of power that leads to negotiations about the nature of the relationships between various entities in the system."
|
||
|
||
* [Self-Sovereign Identity](https://thelivinglib.org/self-sovereign-identity/) 2019-06-17 Living Library
|
||
> Identification document (ID) is a crucial part of every individual’s life, in that it is often a prerequisite for accessing a variety of services — ranging from creating a bank account to enrolling children in school to buying alcoholic beverages to signing up for an email account to voting in an election — and also a proof of simply being.
|
||
* [video] [What is self-sovereign identity?](https://www.youtube.com/watch?v=rygsE1JC-8Q) 2019-05-31 Evernym
|
||
> - A brief history and overview of self-sovereign identity / decentralized identity
|
||
> - The top consumer-focused and business-focused benefits of SSI
|
||
> - Real-world examples of SSI in action
|
||
> - How organizations can the journey to a decentralized future
|
||
* [Self-sovereign identity: 3 key questions](https://www.csoonline.com/article/3366261/self-sovereign-identity-3-key-questions.html) 2019-03-19 CSO Online
|
||
> SSI is on the extreme end of the digital identity spectrum. Its focus is putting control back in the hands of you, the user. But SSI is not the only way to skin a cat.
|
||
* [Self-Sovereign Identity: Shifting the Locus of Control](https://medium.com/@trbouma/self-sovereign-identity-shifting-the-locus-of-control-10da1c8757ad) 2019-03-02 Tim Bouma
|
||
> Simply put, the old (centralized and federated models) the locus of control was between the other parties that could make decisions about me, whether I was in the picture or not. In the new model (self-sovereign identity), the user is put into the centre of his/her own locus of control. See above.
|
||
* [The Three Models of Digital Identity Relationships — How self-sovereign identity (SSI) is different, and why it’s better](https://medium.com/evernym/the-three-models-of-digital-identity-relationships-ca0727cb5186) 2018-08-24 Timothy Ruff, Evernym
|
||
> SSI is powerful yet elegant, bold yet familiar, and through it we can finally break free from the paradox of having to sacrifice security for user experience (or vice versa): we can have both, and at levels vastly improved over the status quo. Wonderfully, SSI also has life-altering potential for at-risk populations around the globe.
|
||
* [Inevitable Rise of Self-Sovereign Identity](https://sovrin.org/wp-content/uploads/2018/03/The-Inevitable-Rise-of-Self-Sovereign-Identity.pdf) 2018-03-28
|
||
> The evolution of internet identity is the result of trying to satisfy three basic requirements:
|
||
> 1. Security - the identity information must be protected from unintentional disclosure;
|
||
> 2. Control - the identity owner must be in control of who can see and access their data and for what purposes;
|
||
> 3. Portability - the user must be able to use their identity data wherever they want and not be tied into a single provide
|
||
* [Self Sovereign Identity](https://identitywoman.net/self-sovereign-identity/) 2018-01-23 Kaliya 'Identity Woman' Young
|
||
> The Social Human Fabric: This is critical to why we actually are having these breakthroughs woven together to create the open standards for self-sovereign identity to become real. A dedicated group of individuals that have been actively meeting face to face twice a year for over 12 years at the Internet Identity Workshop, and other industry events like the RSA Conference, Cloud Identity Summit and the new kid on the collaboration block Rebooting the Web of Trust.
|
||
|
||
## Aspects of SSI
|
||
|
||
* [GlobaliD 101: Device-based identity](https://medium.com/global-id/globalid-101-device-based-identity-c6096a5b0890) 2022-10-05 GlobalID
|
||
> That way, your sensitive personal data is stored locally on your own device rather than hosted on some company’s server that becomes a target for hackers.
|
||
* [GlobaliD 101: Bring Your Own Identity](https://medium.com/global-id/globalid-101-bring-your-own-identity-5b9927008190) 2022-08-30 GlobalID
|
||
> There is a real opportunity to combine technology that is being developed with the concept of BYO Identity that will create a new identity framework where you own and control your data.
|
||
> - [Part 1: What a smart and humanistic approach to digital identity would like](https://medium.com/global-id/globalid-101-how-digital-identity-should-work-fc53ede7b86f) 2022-07-05
|
||
> - [Part 2: The Trust Triangle — the system of issuers, holders, and verifiers that illustrates how identity works (and how it’s broken, today)](https://medium.com/global-id/globalid-101-what-is-the-trust-triangle-260e85e1c640) 2022-07-21
|
||
> - [Part 3: Why the ID Wallet is the first step toward achieving a new vision for digital identity](https://medium.com/global-id/globalid-101-id-wallets-68fa77e6d0d7) 2022-08-02
|
||
> - [Part 4: Why every company is an identity company](https://medium.com/global-id/globalid-101-every-company-is-an-identity-company-a851beed999d) 2022-08-16
|
||
* [Trusted Third Parties vs Self-Sovereign Identity](https://academy.affinidi.com/trusted-third-parties-vs-self-sovereign-identity-4e96de929b1b) 2021-12-30 Affinidi
|
||
> All of us have [multiple identities](https://academy.affinidi.com/what-links-identity-and-vcs-together-across-applications-9523af3884a9) at any point. We are sons, daughters, brothers, sisters, parents, partners, friends, colleagues, and more to different people.
|
||
* [Selective Disclosure: Share Just What You Want](https://academy.affinidi.com/selective-disclosure-share-what-you-want-8ae367655b7b) 2021-08-02 Affinidi
|
||
> In the context of SSI, selective disclosure is best implemented through [verifiable credentials](https://academy.affinidi.com/what-are-verifiable-credentials-79f1846a7b9) where the user has separate credentials for each piece of information such as his/her date of birth, full name, vaccination details, address, passport number, etc.
|
||
* [Self-Sovereign Identity: What You Can/Can’t Do With SSI?](https://academy.affinidi.com/self-sovereign-identity-what-you-can-cant-do-with-ssi-1284f7227b4e) 2021-06-24 Affinidi
|
||
> it gives complete control and ownership of data to the individual entities as they can decide what data to share and with whom.
|
||
>
|
||
> Beyond this encompassing vision, let’s drill down into the specifics to understand what you can and can’t do with SSI.
|
||
* [When a user holds his:her own credentials locally on the phone, it creates a three-sided market](https://twitter.com/lissi_id/status/1334834875896004608) 2020-12-04 Lissi ID
|
||
> which puts the holder of the credential in the position of a carrier between issuer and verifiers.
|
||
> 
|
||
* [The Implications of Bring Your Own Identity](https://www.idsalliance.org/blog/2020/12/03/the-implications-of-bring-your-own-identity/) Identity Defined Security Alliance 2020-12-03
|
||
> My short stint as “Mark Jannell" taught me a lot of about trust and ease of use in a bring your own identity model. Trust, as always in security, is essential to this new class of relationships and must be established and then protected from abuse. Ease of use, it turns out, is a key factor in protecting that trust and promoting the adoption of good identity patterns. I’m sure that I could have learned these lessons in some other way, but I’ll never forget my half year answering to a pseudonym.
|
||
* [What is the Trust Triangle?](https://academy.affinidi.com/what-is-the-trust-triangle-9a9caf36b321) 2021-08-23 Affinidi
|
||
> The relationship between the issuers, holders, and verifiers is called the trust triangle simply because you need an element of trust among these entities for them to work together.
|
||
|
||
## Security
|
||
* [What is decentralized identity?](https://www.csoonline.com/article/3665692/what-is-decentralized-identity.html) 2022-07-06 CSO Online
|
||
> The DID model allows you to establish a relationship between your private key (your blockchain wallet) and your citizenship. The issuing authority signs off on the truth of your claim and, thereafter, third parties can check your public key to see that the holder of the private key is in fact a British citizen.
|
||
* [Getting Data Security Right](https://medium.com/mydex/getting-data-security-right-36d291cac156) 2022-05-23 Alan Michel
|
||
> data security is about system-wide design, where many different elements need to fit together to create a working whole.
|
||
* [Impact of Self-Sovereign Identity on Cybersecurity](https://securityboulevard.com/2022/04/impact-of-self-sovereign-identity-on-cybersecurity-avast/) 2022-04 Security Boulevard
|
||
> How does this change the world of cybersecurity protection? Typically, bad actors approach cybersecurity attacks by developing solutions that exploit the attack vectors of their target victims.
|
||
>
|
||
> There are 4 attack vector categories to self-sovereign identity that map directly to each element: Issuer, Holder, Trust Registry and Verifier.
|
||
* [ID Verification Threats On the Horizon](https://stateofidentity.libsyn.com/id-verification-threats-on-the-horizon) 2022-03-31 Liminal Podcasts
|
||
> Cognito's CEO Alain Meier joins the State of Identity host Cameron D’Ambrosi to dive into why industries beyond financial services are now in the market for identity verification. They also unpack the impact of synthetic identity fraud across verticals, and how platforms find the balance when building their onboarding processes.
|
||
* [Security, Silos, and Sovereignty](https://daniel-hardman.medium.com/security-silos-and-sovereignty-522e30bb8eb4) 2021-03-12 Daniel Hardman
|
||
> Why portable security is the sleeper — but killer — feature for SSI
|
||
>
|
||
> what’s cool about DIDs (besides their self-service creation) is that their metadata is cryptographically verifiable. That means that anyone in the world can tell whether the metadata is legit, in the blink of an eye, just by asking software to check some math. And it also means that you can build a transport-independent, tamper-proof, encrypted communication channel with whoever controls a DID.
|
||
* [How Decentralized Identifiers Will Shape the Future of Identity](https://hackernoon.com/how-decentralized-identifiers-will-shape-the-future-of-identity-iam3w9g) 2020-11-09 HackerNoon
|
||
> Hackers value personal information the most. 96% of hacking groups’ primary motive is intelligence gathering. Researchers at privacy website PrivacyAffairs.com found that you can obtain a person's full identity for the low price of $1,275.
|
||
|
||
## Literature
|
||
|
||
* [WhitePaper] [Self Sovereign Identity](https://www.blockchainresearchinstitute.org/project/self-sovereign-identity) 2022-05-10 Phil Windley, Blockchain Research Institute
|
||
> In this research, one of the leading experts and thought leaders in the digital identity space brings his latest thinking to enterprise innovators. He explains the value of the relationship view of identity, the nature of authentic digital relationships, the trust bases of identity systems, and the architecture of the identity metasystem, including decentralized identifier communication and the self-sovereign Internet. He then explores how to operationalize digital relationships and the potential of generative identities (e.g., verifiable credentials) and credential exchange. He concludes with a deep dive into self-sovereign identities in production: the UK National Health Service staff passport, Bonifii’s MemberPass for credit unions, the International Air Transport Association Travel Pass, and others. The project is a must-read for enterprise leaders looking to understand their opportunities in identity platforms and applications.
|
||
* [Whitepaper] [Self-Sovereign Identity Foundations, Applications, and Potentials of Portable Digital Identities](https://www.fim-rc.de/wp-content/uploads/2021/09/20210811-SSI-Whitepaper-English.pdf) 2021-09 Fraunhofer Institute for Applied Information Technology FIT
|
||
> This paper analyses the SSI paradigm's conceptual characteristics and technical aspects and presents three use cases as examples. It becomes clear that SSI offers advantages in individual control, data security, and full portability of identities between different services. For example, forgeryand tamper-proof digital versions of important personal documents such as ID cards, passports, birth certificates or medical confirmations can be created. However, the use cases are not limited to personal SSI but can also be, for example, digital identities of organizations and physical objects in the context of IoT solutions. This is particularly important in connection with the comprehensive digitization of companies.
|
||
* [Digital identities – steps on the path to an ID ecosystem](https://bankenverband.de/en/digitisation/digital-identities-steps-path-id-ecosystem/) 2021-03-18 Bankenverband
|
||
*This article is very very good in articulating the big picture of how SSI systems relative to older system and emerging fragmetned systems.*
|
||
> An answer to these challenges is an ecosystem in which digital identity data can be exchanged in a way that is secure, reliable, scalable and convenient. This will have a positive impact on the economic future of Germany and Europe while at the same time enhancing the private sphere of the individual.
|
||
|
||
[](https://www.researchgate.net/figure/Self-Sovereign-Identity-Locus-of-Control-Bouma-2019_fig1_340938808)
|