Awesome WAF Evasion 
A curated list of awesome WAF evasion stuff. 🔥
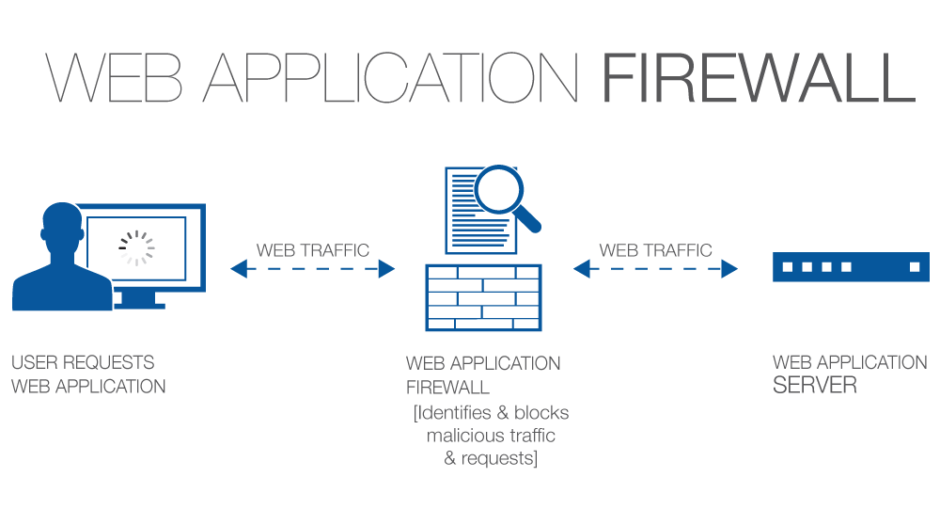
A Concise Definition: A web application firewall is a form of firewall with a set of configured rules that controls input, output, and/or access from, to, or by an application or service. It operates by monitoring and potentially blocking the input, output, or system service calls that do not meet the configured policy of the firewall. (Source Wikipedia)
Feel free to contribute.
Contents:
- Awesome WAFs List
- Awesome Testing Methodology
- Awesome WAF Detection
- Awesome WAF Rule Testing
- Awesome Evasion Techniques
- Awesome Tools
- Awesome Blogs & Writeups
- Awesome Presentations & Papers
Awesome WAFs List
Testing Methodology
Alright, now lets see the approach of testing WAFs. Wait, before that we need to know how they work right? Here you go.
How WAFs Work:
- Using a set of rules to distinguish between normal requests and malicious requests.
- Sometimes they use a learning mode to add rules automatically through learning about user behaviour.
Operation Modes:
- Negative Model (Blacklist based) -
One that defines what is not allowed. Eg. Block all
<script>*</script>inputs. - Positive Model (Whitelist based) - One that defines what is allowed and rejects everything else.
- Mixed/Hybrid Model (Inclusive model) - One that uses a mixed concept of blacklisting and whitelisting stuff.
Where To Look:
- Always look out for common ports that expose that a WAF
80,443,8000,8008,8080,8088.
Tip: You can use automate this easily by commandline using a screenshot taker like WebScreenShot.
- Some WAFs set their own cookies in requests (eg. Citrix Netscaler, Yunsuo WAF).
- Some associate themselves with separate headers (eg. Anquanbao WAF, Amazon AWS WAF).
- Some often alter headers and jumble characters to confuse attacker (eg. Citrix Netscaler, Big IP WAF).
- Some WAFs expose themselves in the response content (eg. DotDefender, Armor, truShield Sitelock).
- Other WAFs reply with unusual response codes upon malicious requests (eg. WebKnight).
Detection Techniques:
- Make a normal GET request from a browser, intercept and test response headers (specifically cookies).
- Make a request from command line (eg. cURL), and test response content and headers (no user-agent included).
- If there is a login page somewhere, try some common (easily detectable) payloads like
' or 1 = 1 --. - If there is some search box or input field somewhere, try detecting payloads like
<script>alert()</script>. - Make GET requests with outdated protocols like
HTTP/0.9(HTTP/0.9does not support POST type queries). - Drop Action Technique - Send a raw crafted FIN/RST packet to server and identify response.
Tip: This method could be easily achieved with HPing3 or Scapy.
- Side Channel Attacks - Examine the timing behaviour of the request and response content.
WAF Detection
Wanna detect WAFs? Lets see how.
Note
: This section contains manual WAF detection techniques. You might want to switch over to next section.
WAF Rule Testing
Lets head over to testing WAF rules.
WAF Evasion Techniques
Lets look at some methods of bypassing and evading WAFs.
Awesome Tools
WAF Fingerprinting:
1. Fingerprinting with NMap: Source: https://
- Normal WAF Fingerprinting
nmap --script=http-waf-fingerprint <target>
- Intensive WAF Fingerprinting
nmap --script=http-waf-fingerprint –script-args http-waf-fingerprint.intensive=1 <target>
- Generic Detection
nmap --script=http-waf-detect <target>
2. Fingerprinting with WafW00f:
wafw00f <target>
WAF Testing:
WAF Evading:
1. Evading WAFs with SQLMap Tamper Scripts:
- General Tamper Testing
tamper=apostrophemask,apostrophenullencode,base64encode,between,chardoubleencode,charencode,charunicodeencode,equaltolike,greatest,ifnull2ifisnull,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,space2comment,space2plus,space2randomblank,unionalltounion,unmagicquotes
- MSSQL Tamper Testing
tamper=between,charencode,charunicodeencode,equaltolike,greatest,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,sp_password,space2comment,space2dash,space2mssqlblank,space2mysqldash,space2plus,space2randomblank,unionalltounion,unmagicquotes
- MySQL Tamper Testing
tamper=between,bluecoat,charencode,charunicodeencode,concat2concatws,equaltolike,greatest,halfversionedmorekeywords,ifnull2ifisnull,modsecurityversioned,modsecurityzeroversioned,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,space2comment,space2hash,space2morehash,space2mysqldash,space2plus,space2randomblank,unionalltounion,unmagicquotes,versionedkeywords,versionedmorekeywords,xforwardedfor
- Generic Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=apostrophemask,apostrophenullencode,appendnullbyte,base64encode,between,bluecoat,chardoubleencode,charencode,charunicodeencode,concat2concatws,equaltolike,greatest,halfversionedmorekeywords,ifnull2ifisnull,modsecurityversioned,modsecurityzeroversioned,multiplespaces,nonrecursivereplacement,percentage,randomcase,randomcomments,securesphere,space2comment,space2dash,space2hash,space2morehash,space2mssqlblank,space2mssqlhash,space2mysqlblank,space2mysqldash,space2plus,space2randomblank,sp_password,unionalltounion,unmagicquotes,versionedkeywords,versionedmorekeywords
2. Evading WAFs with WhatWaf:
whatwaf -u <target> --ra --throttle 2
Presentations & Research Papers
Presentations:
- WAF Profiling & Evasion Techniques - A WAF testing and evasion guide from OWASP.
- Protocol Level WAF Evasion Techniques - A presentation at about efficiently evading WAFs at protocol level from BlackHat US 12.
- Analysing Attacking Detection Logic Mechanisms - A presentation about WAF logic applied to detecting attacks from BlackHat US 16.
- WAF Bypasses and PHP Exploits - A presentation about evading WAFs and developing related PHP exploits.
- Playing Around with WAFs - A small presentation about WAF profiling and playing around with them from Defcon 16.
Research Papers:
- WASC WAF Evaluation Criteria - A guide for WAF Evaluation from Web Application Security Consortium
- Protocol Level WAF Evasion - A protocol level WAF evasion techniques and analysis by Qualys.
- WAF Evasion Testing - A WAF evasion testing guide from SANS.
- Bypassing all WAF XSS Filters - A paper about bypassing all XSS filter rules and evading WAFs for XSS.