mirror of
https://github.com/edgelesssys/constellation.git
synced 2025-04-11 18:39:44 -04:00
deploy cilium via helmchart (#321)
This commit is contained in:
parent
2c7129987a
commit
9478303f80
4
.github/workflows/test-shellcheck.yml
vendored
4
.github/workflows/test-shellcheck.yml
vendored
@ -18,7 +18,7 @@ jobs:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@2541b1294d2704b0964813337f33b291d3f8596b
|
||||
- name: Run ShellCheck
|
||||
uses: ludeeus/action-shellcheck@94e0aab03ca135d11a35e5bfc14e6746dc56e7e9
|
||||
uses: ludeeus/action-shellcheck@203a3fd018dfe73f8ae7e3aa8da2c149a5f41c33
|
||||
with:
|
||||
severity: error
|
||||
ignore_names: merge_config.sh
|
||||
ignore_paths: charts/cilium
|
||||
|
||||
@ -21,8 +21,7 @@ and this project adheres to [Semantic Versioning](https://semver.org/spec/v2.0.0
|
||||
### Added
|
||||
|
||||
- Kubernetes operator for Constellation nodes with ability to update node images.
|
||||
|
||||
<!-- For new features. -->
|
||||
- cilium strict pod2pod encryption.
|
||||
### Changed
|
||||
<!-- For changes in existing functionality. -->
|
||||
### Deprecated
|
||||
|
||||
@ -206,10 +206,11 @@ func (c *Client) RetrieveSubnetworkAliasCIDR(ctx context.Context, project, zone,
|
||||
if err != nil {
|
||||
return "", fmt.Errorf("retrieving subnetwork alias CIDR failed: %w", err)
|
||||
}
|
||||
if subnetwork == nil || subnetwork.IpCidrRange == nil || *subnetwork.IpCidrRange == "" {
|
||||
if subnetwork == nil || len(subnetwork.SecondaryIpRanges) == 0 || (subnetwork.SecondaryIpRanges[0]).IpCidrRange == nil {
|
||||
return "", fmt.Errorf("retrieving subnetwork alias CIDR returned invalid results")
|
||||
}
|
||||
return *subnetwork.IpCidrRange, nil
|
||||
|
||||
return *(subnetwork.SecondaryIpRanges[0]).IpCidrRange, nil
|
||||
}
|
||||
|
||||
// RetrieveLoadBalancerIP returns the IP address of the load balancer specified by project, zone and loadBalancerName.
|
||||
|
||||
@ -701,7 +701,11 @@ func TestRetrieveSubnetworkAliasCIDR(t *testing.T) {
|
||||
},
|
||||
stubSubnetworksClient: stubSubnetworksClient{
|
||||
GetSubnetwork: &computepb.Subnetwork{
|
||||
IpCidrRange: &aliasCIDR,
|
||||
SecondaryIpRanges: []*computepb.SubnetworkSecondaryRange{
|
||||
{
|
||||
IpCidrRange: proto.String(aliasCIDR),
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
wantAliasCIDR: aliasCIDR,
|
||||
|
||||
@ -14,7 +14,7 @@ import (
|
||||
type clusterFake struct{}
|
||||
|
||||
// InitCluster fakes bootstrapping a new cluster with the current node being the master, returning the arguments required to join the cluster.
|
||||
func (c *clusterFake) InitCluster(context.Context, []string, string, string, []byte, resources.KMSConfig, map[string]string, *logger.Logger,
|
||||
func (c *clusterFake) InitCluster(context.Context, []string, string, string, []byte, resources.KMSConfig, map[string]string, []byte, *logger.Logger,
|
||||
) ([]byte, error) {
|
||||
return []byte{}, nil
|
||||
}
|
||||
|
||||
@ -35,6 +35,7 @@ type InitRequest struct {
|
||||
KubernetesVersion string `protobuf:"bytes,8,opt,name=kubernetes_version,json=kubernetesVersion,proto3" json:"kubernetes_version,omitempty"`
|
||||
SshUserKeys []*SSHUserKey `protobuf:"bytes,9,rep,name=ssh_user_keys,json=sshUserKeys,proto3" json:"ssh_user_keys,omitempty"`
|
||||
Salt []byte `protobuf:"bytes,10,opt,name=salt,proto3" json:"salt,omitempty"`
|
||||
HelmDeployments []byte `protobuf:"bytes,11,opt,name=helm_deployments,json=helmDeployments,proto3" json:"helm_deployments,omitempty"`
|
||||
}
|
||||
|
||||
func (x *InitRequest) Reset() {
|
||||
@ -139,6 +140,13 @@ func (x *InitRequest) GetSalt() []byte {
|
||||
return nil
|
||||
}
|
||||
|
||||
func (x *InitRequest) GetHelmDeployments() []byte {
|
||||
if x != nil {
|
||||
return x.HelmDeployments
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
type InitResponse struct {
|
||||
state protoimpl.MessageState
|
||||
sizeCache protoimpl.SizeCache
|
||||
@ -261,7 +269,7 @@ var File_init_proto protoreflect.FileDescriptor
|
||||
|
||||
var file_init_proto_rawDesc = []byte{
|
||||
0x0a, 0x0a, 0x69, 0x6e, 0x69, 0x74, 0x2e, 0x70, 0x72, 0x6f, 0x74, 0x6f, 0x12, 0x04, 0x69, 0x6e,
|
||||
0x69, 0x74, 0x22, 0xb5, 0x03, 0x0a, 0x0b, 0x49, 0x6e, 0x69, 0x74, 0x52, 0x65, 0x71, 0x75, 0x65,
|
||||
0x69, 0x74, 0x22, 0xe0, 0x03, 0x0a, 0x0b, 0x49, 0x6e, 0x69, 0x74, 0x52, 0x65, 0x71, 0x75, 0x65,
|
||||
0x73, 0x74, 0x12, 0x36, 0x0a, 0x17, 0x61, 0x75, 0x74, 0x6f, 0x73, 0x63, 0x61, 0x6c, 0x69, 0x6e,
|
||||
0x67, 0x5f, 0x6e, 0x6f, 0x64, 0x65, 0x5f, 0x67, 0x72, 0x6f, 0x75, 0x70, 0x73, 0x18, 0x01, 0x20,
|
||||
0x03, 0x28, 0x09, 0x52, 0x15, 0x61, 0x75, 0x74, 0x6f, 0x73, 0x63, 0x61, 0x6c, 0x69, 0x6e, 0x67,
|
||||
@ -288,26 +296,29 @@ var file_init_proto_rawDesc = []byte{
|
||||
0x73, 0x18, 0x09, 0x20, 0x03, 0x28, 0x0b, 0x32, 0x10, 0x2e, 0x69, 0x6e, 0x69, 0x74, 0x2e, 0x53,
|
||||
0x53, 0x48, 0x55, 0x73, 0x65, 0x72, 0x4b, 0x65, 0x79, 0x52, 0x0b, 0x73, 0x73, 0x68, 0x55, 0x73,
|
||||
0x65, 0x72, 0x4b, 0x65, 0x79, 0x73, 0x12, 0x12, 0x0a, 0x04, 0x73, 0x61, 0x6c, 0x74, 0x18, 0x0a,
|
||||
0x20, 0x01, 0x28, 0x0c, 0x52, 0x04, 0x73, 0x61, 0x6c, 0x74, 0x22, 0x68, 0x0a, 0x0c, 0x49, 0x6e,
|
||||
0x69, 0x74, 0x52, 0x65, 0x73, 0x70, 0x6f, 0x6e, 0x73, 0x65, 0x12, 0x1e, 0x0a, 0x0a, 0x6b, 0x75,
|
||||
0x62, 0x65, 0x63, 0x6f, 0x6e, 0x66, 0x69, 0x67, 0x18, 0x01, 0x20, 0x01, 0x28, 0x0c, 0x52, 0x0a,
|
||||
0x6b, 0x75, 0x62, 0x65, 0x63, 0x6f, 0x6e, 0x66, 0x69, 0x67, 0x12, 0x19, 0x0a, 0x08, 0x6f, 0x77,
|
||||
0x6e, 0x65, 0x72, 0x5f, 0x69, 0x64, 0x18, 0x02, 0x20, 0x01, 0x28, 0x0c, 0x52, 0x07, 0x6f, 0x77,
|
||||
0x6e, 0x65, 0x72, 0x49, 0x64, 0x12, 0x1d, 0x0a, 0x0a, 0x63, 0x6c, 0x75, 0x73, 0x74, 0x65, 0x72,
|
||||
0x5f, 0x69, 0x64, 0x18, 0x03, 0x20, 0x01, 0x28, 0x0c, 0x52, 0x09, 0x63, 0x6c, 0x75, 0x73, 0x74,
|
||||
0x65, 0x72, 0x49, 0x64, 0x22, 0x47, 0x0a, 0x0a, 0x53, 0x53, 0x48, 0x55, 0x73, 0x65, 0x72, 0x4b,
|
||||
0x65, 0x79, 0x12, 0x1a, 0x0a, 0x08, 0x75, 0x73, 0x65, 0x72, 0x6e, 0x61, 0x6d, 0x65, 0x18, 0x01,
|
||||
0x20, 0x01, 0x28, 0x09, 0x52, 0x08, 0x75, 0x73, 0x65, 0x72, 0x6e, 0x61, 0x6d, 0x65, 0x12, 0x1d,
|
||||
0x0a, 0x0a, 0x70, 0x75, 0x62, 0x6c, 0x69, 0x63, 0x5f, 0x6b, 0x65, 0x79, 0x18, 0x02, 0x20, 0x01,
|
||||
0x28, 0x09, 0x52, 0x09, 0x70, 0x75, 0x62, 0x6c, 0x69, 0x63, 0x4b, 0x65, 0x79, 0x32, 0x34, 0x0a,
|
||||
0x03, 0x41, 0x50, 0x49, 0x12, 0x2d, 0x0a, 0x04, 0x49, 0x6e, 0x69, 0x74, 0x12, 0x11, 0x2e, 0x69,
|
||||
0x6e, 0x69, 0x74, 0x2e, 0x49, 0x6e, 0x69, 0x74, 0x52, 0x65, 0x71, 0x75, 0x65, 0x73, 0x74, 0x1a,
|
||||
0x12, 0x2e, 0x69, 0x6e, 0x69, 0x74, 0x2e, 0x49, 0x6e, 0x69, 0x74, 0x52, 0x65, 0x73, 0x70, 0x6f,
|
||||
0x6e, 0x73, 0x65, 0x42, 0x3d, 0x5a, 0x3b, 0x67, 0x69, 0x74, 0x68, 0x75, 0x62, 0x2e, 0x63, 0x6f,
|
||||
0x6d, 0x2f, 0x65, 0x64, 0x67, 0x65, 0x6c, 0x65, 0x73, 0x73, 0x73, 0x79, 0x73, 0x2f, 0x63, 0x6f,
|
||||
0x6e, 0x73, 0x74, 0x65, 0x6c, 0x6c, 0x61, 0x74, 0x69, 0x6f, 0x6e, 0x2f, 0x62, 0x6f, 0x6f, 0x74,
|
||||
0x73, 0x74, 0x72, 0x61, 0x70, 0x70, 0x65, 0x72, 0x2f, 0x69, 0x6e, 0x69, 0x74, 0x70, 0x72, 0x6f,
|
||||
0x74, 0x6f, 0x62, 0x06, 0x70, 0x72, 0x6f, 0x74, 0x6f, 0x33,
|
||||
0x20, 0x01, 0x28, 0x0c, 0x52, 0x04, 0x73, 0x61, 0x6c, 0x74, 0x12, 0x29, 0x0a, 0x10, 0x68, 0x65,
|
||||
0x6c, 0x6d, 0x5f, 0x64, 0x65, 0x70, 0x6c, 0x6f, 0x79, 0x6d, 0x65, 0x6e, 0x74, 0x73, 0x18, 0x0b,
|
||||
0x20, 0x01, 0x28, 0x0c, 0x52, 0x0f, 0x68, 0x65, 0x6c, 0x6d, 0x44, 0x65, 0x70, 0x6c, 0x6f, 0x79,
|
||||
0x6d, 0x65, 0x6e, 0x74, 0x73, 0x22, 0x68, 0x0a, 0x0c, 0x49, 0x6e, 0x69, 0x74, 0x52, 0x65, 0x73,
|
||||
0x70, 0x6f, 0x6e, 0x73, 0x65, 0x12, 0x1e, 0x0a, 0x0a, 0x6b, 0x75, 0x62, 0x65, 0x63, 0x6f, 0x6e,
|
||||
0x66, 0x69, 0x67, 0x18, 0x01, 0x20, 0x01, 0x28, 0x0c, 0x52, 0x0a, 0x6b, 0x75, 0x62, 0x65, 0x63,
|
||||
0x6f, 0x6e, 0x66, 0x69, 0x67, 0x12, 0x19, 0x0a, 0x08, 0x6f, 0x77, 0x6e, 0x65, 0x72, 0x5f, 0x69,
|
||||
0x64, 0x18, 0x02, 0x20, 0x01, 0x28, 0x0c, 0x52, 0x07, 0x6f, 0x77, 0x6e, 0x65, 0x72, 0x49, 0x64,
|
||||
0x12, 0x1d, 0x0a, 0x0a, 0x63, 0x6c, 0x75, 0x73, 0x74, 0x65, 0x72, 0x5f, 0x69, 0x64, 0x18, 0x03,
|
||||
0x20, 0x01, 0x28, 0x0c, 0x52, 0x09, 0x63, 0x6c, 0x75, 0x73, 0x74, 0x65, 0x72, 0x49, 0x64, 0x22,
|
||||
0x47, 0x0a, 0x0a, 0x53, 0x53, 0x48, 0x55, 0x73, 0x65, 0x72, 0x4b, 0x65, 0x79, 0x12, 0x1a, 0x0a,
|
||||
0x08, 0x75, 0x73, 0x65, 0x72, 0x6e, 0x61, 0x6d, 0x65, 0x18, 0x01, 0x20, 0x01, 0x28, 0x09, 0x52,
|
||||
0x08, 0x75, 0x73, 0x65, 0x72, 0x6e, 0x61, 0x6d, 0x65, 0x12, 0x1d, 0x0a, 0x0a, 0x70, 0x75, 0x62,
|
||||
0x6c, 0x69, 0x63, 0x5f, 0x6b, 0x65, 0x79, 0x18, 0x02, 0x20, 0x01, 0x28, 0x09, 0x52, 0x09, 0x70,
|
||||
0x75, 0x62, 0x6c, 0x69, 0x63, 0x4b, 0x65, 0x79, 0x32, 0x34, 0x0a, 0x03, 0x41, 0x50, 0x49, 0x12,
|
||||
0x2d, 0x0a, 0x04, 0x49, 0x6e, 0x69, 0x74, 0x12, 0x11, 0x2e, 0x69, 0x6e, 0x69, 0x74, 0x2e, 0x49,
|
||||
0x6e, 0x69, 0x74, 0x52, 0x65, 0x71, 0x75, 0x65, 0x73, 0x74, 0x1a, 0x12, 0x2e, 0x69, 0x6e, 0x69,
|
||||
0x74, 0x2e, 0x49, 0x6e, 0x69, 0x74, 0x52, 0x65, 0x73, 0x70, 0x6f, 0x6e, 0x73, 0x65, 0x42, 0x3d,
|
||||
0x5a, 0x3b, 0x67, 0x69, 0x74, 0x68, 0x75, 0x62, 0x2e, 0x63, 0x6f, 0x6d, 0x2f, 0x65, 0x64, 0x67,
|
||||
0x65, 0x6c, 0x65, 0x73, 0x73, 0x73, 0x79, 0x73, 0x2f, 0x63, 0x6f, 0x6e, 0x73, 0x74, 0x65, 0x6c,
|
||||
0x6c, 0x61, 0x74, 0x69, 0x6f, 0x6e, 0x2f, 0x62, 0x6f, 0x6f, 0x74, 0x73, 0x74, 0x72, 0x61, 0x70,
|
||||
0x70, 0x65, 0x72, 0x2f, 0x69, 0x6e, 0x69, 0x74, 0x70, 0x72, 0x6f, 0x74, 0x6f, 0x62, 0x06, 0x70,
|
||||
0x72, 0x6f, 0x74, 0x6f, 0x33,
|
||||
}
|
||||
|
||||
var (
|
||||
|
||||
@ -19,6 +19,7 @@ message InitRequest {
|
||||
string kubernetes_version = 8;
|
||||
repeated SSHUserKey ssh_user_keys = 9;
|
||||
bytes salt = 10;
|
||||
bytes helm_deployments = 11;
|
||||
}
|
||||
|
||||
message InitResponse {
|
||||
|
||||
@ -124,6 +124,7 @@ func (s *Server) Init(ctx context.Context, req *initproto.InitRequest) (*initpro
|
||||
UseExistingKEK: req.UseExistingKek,
|
||||
},
|
||||
sshProtoKeysToMap(req.SshUserKeys),
|
||||
req.HelmDeployments,
|
||||
s.log,
|
||||
)
|
||||
if err != nil {
|
||||
@ -198,6 +199,7 @@ type ClusterInitializer interface {
|
||||
measurementSalt []byte,
|
||||
kmsConfig resources.KMSConfig,
|
||||
sshUserKeys map[string]string,
|
||||
helmDeployments []byte,
|
||||
log *logger.Logger,
|
||||
) ([]byte, error)
|
||||
}
|
||||
|
||||
@ -282,7 +282,7 @@ type stubClusterInitializer struct {
|
||||
initClusterErr error
|
||||
}
|
||||
|
||||
func (i *stubClusterInitializer) InitCluster(context.Context, []string, string, string, []byte, resources.KMSConfig, map[string]string, *logger.Logger,
|
||||
func (i *stubClusterInitializer) InitCluster(context.Context, []string, string, string, []byte, resources.KMSConfig, map[string]string, []byte, *logger.Logger,
|
||||
) ([]byte, error) {
|
||||
return i.initClusterKubeconfig, i.initClusterErr
|
||||
}
|
||||
|
||||
@ -4,6 +4,7 @@ import (
|
||||
"context"
|
||||
"crypto/rand"
|
||||
"crypto/x509"
|
||||
"encoding/json"
|
||||
"encoding/pem"
|
||||
"errors"
|
||||
"fmt"
|
||||
@ -13,13 +14,16 @@ import (
|
||||
"os"
|
||||
"os/exec"
|
||||
"path/filepath"
|
||||
"regexp"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
"github.com/edgelesssys/constellation/bootstrapper/internal/kubelet"
|
||||
"github.com/edgelesssys/constellation/bootstrapper/internal/kubernetes/k8sapi/resources"
|
||||
"github.com/edgelesssys/constellation/internal/constants"
|
||||
kubeconstants "k8s.io/kubernetes/cmd/kubeadm/app/constants"
|
||||
|
||||
"github.com/edgelesssys/constellation/internal/crypto"
|
||||
"github.com/edgelesssys/constellation/internal/deploy/helm"
|
||||
"github.com/edgelesssys/constellation/internal/file"
|
||||
"github.com/edgelesssys/constellation/internal/logger"
|
||||
"github.com/edgelesssys/constellation/internal/versions"
|
||||
@ -27,8 +31,9 @@ import (
|
||||
"github.com/spf13/afero"
|
||||
"go.uber.org/zap"
|
||||
"golang.org/x/text/transform"
|
||||
"helm.sh/helm/v3/pkg/action"
|
||||
"helm.sh/helm/v3/pkg/cli"
|
||||
corev1 "k8s.io/api/core/v1"
|
||||
"k8s.io/kubernetes/cmd/kubeadm/app/constants"
|
||||
)
|
||||
|
||||
const (
|
||||
@ -40,8 +45,6 @@ const (
|
||||
crdTimeout = 15 * time.Second
|
||||
)
|
||||
|
||||
var providerIDRegex = regexp.MustCompile(`^azure:///subscriptions/([^/]+)/resourceGroups/([^/]+)/providers/Microsoft.Compute/virtualMachineScaleSets/([^/]+)/virtualMachines/([^/]+)$`)
|
||||
|
||||
// Client provides the functions to talk to the k8s API.
|
||||
type Client interface {
|
||||
Apply(resources resources.Marshaler, forceConflicts bool) error
|
||||
@ -182,6 +185,33 @@ func (k *KubernetesUtil) InitCluster(
|
||||
return nil
|
||||
}
|
||||
|
||||
func (k *KubernetesUtil) SetupHelmDeployments(ctx context.Context, kubectl Client, helmDeployments []byte, in SetupPodNetworkInput, log *logger.Logger) error {
|
||||
var helmDeploy helm.Deployments
|
||||
if err := json.Unmarshal(helmDeployments, &helmDeploy); err != nil {
|
||||
return fmt.Errorf("unmarshalling helm deployments: %w", err)
|
||||
}
|
||||
settings := cli.New()
|
||||
settings.KubeConfig = kubeConfig
|
||||
|
||||
actionConfig := new(action.Configuration)
|
||||
if err := actionConfig.Init(settings.RESTClientGetter(), constants.HelmNamespace,
|
||||
"secret", log.Infof); err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
helmClient := action.NewInstall(actionConfig)
|
||||
helmClient.Namespace = constants.HelmNamespace
|
||||
helmClient.ReleaseName = "cilium"
|
||||
helmClient.Wait = true
|
||||
helmClient.Timeout = 30 * time.Second
|
||||
|
||||
if err := k.deployCilium(ctx, in, helmClient, helmDeploy.Cilium, kubectl); err != nil {
|
||||
return fmt.Errorf("deploying cilium: %w", err)
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
type SetupPodNetworkInput struct {
|
||||
CloudProvider string
|
||||
NodeName string
|
||||
@ -190,40 +220,29 @@ type SetupPodNetworkInput struct {
|
||||
ProviderID string
|
||||
}
|
||||
|
||||
// SetupPodNetwork sets up the cilium pod network.
|
||||
func (k *KubernetesUtil) SetupPodNetwork(ctx context.Context, in SetupPodNetworkInput, client Client) error {
|
||||
// deployCilium sets up the cilium pod network.
|
||||
func (k *KubernetesUtil) deployCilium(ctx context.Context, in SetupPodNetworkInput, helmClient *action.Install, ciliumDeployment helm.Deployment, kubectl Client) error {
|
||||
switch in.CloudProvider {
|
||||
case "gcp":
|
||||
return k.setupGCPPodNetwork(ctx, in.NodeName, in.FirstNodePodCIDR, in.SubnetworkPodCIDR, client)
|
||||
return k.deployCiliumGCP(ctx, helmClient, kubectl, ciliumDeployment, in.NodeName, in.FirstNodePodCIDR, in.SubnetworkPodCIDR)
|
||||
case "azure":
|
||||
return k.setupAzurePodNetwork(ctx, in.ProviderID, in.SubnetworkPodCIDR)
|
||||
return k.deployCiliumAzure(ctx, helmClient, ciliumDeployment)
|
||||
case "qemu":
|
||||
return k.setupQemuPodNetwork(ctx, in.SubnetworkPodCIDR)
|
||||
return k.deployCiliumQEMU(ctx, helmClient, ciliumDeployment, in.SubnetworkPodCIDR)
|
||||
default:
|
||||
return fmt.Errorf("unsupported cloud provider %q", in.CloudProvider)
|
||||
}
|
||||
}
|
||||
|
||||
func (k *KubernetesUtil) setupAzurePodNetwork(ctx context.Context, providerID, subnetworkPodCIDR string) error {
|
||||
matches := providerIDRegex.FindStringSubmatch(providerID)
|
||||
if len(matches) != 5 {
|
||||
return fmt.Errorf("error splitting providerID %q", providerID)
|
||||
}
|
||||
|
||||
ciliumInstall := exec.CommandContext(ctx, "cilium", "install", "--azure-resource-group", matches[2], "--ipam", "azure",
|
||||
"--helm-set",
|
||||
"tunnel=disabled,enableIPv4Masquerade=true,azure.enabled=true,debug.enabled=true,ipv4NativeRoutingCIDR="+subnetworkPodCIDR+
|
||||
",endpointRoutes.enabled=true,encryption.enabled=true,encryption.type=wireguard,l7Proxy=false,egressMasqueradeInterfaces=eth0")
|
||||
ciliumInstall.Env = append(os.Environ(), "KUBECONFIG="+kubeConfig)
|
||||
out, err := ciliumInstall.CombinedOutput()
|
||||
func (k *KubernetesUtil) deployCiliumAzure(ctx context.Context, helmClient *action.Install, ciliumDeployment helm.Deployment) error {
|
||||
_, err := helmClient.RunWithContext(ctx, ciliumDeployment.Chart, ciliumDeployment.Values)
|
||||
if err != nil {
|
||||
err = errors.New(string(out))
|
||||
return err
|
||||
return fmt.Errorf("installing cilium: %w", err)
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func (k *KubernetesUtil) setupGCPPodNetwork(ctx context.Context, nodeName, nodePodCIDR, subnetworkPodCIDR string, kubectl Client) error {
|
||||
func (k *KubernetesUtil) deployCiliumGCP(ctx context.Context, helmClient *action.Install, kubectl Client, ciliumDeployment helm.Deployment, nodeName, nodePodCIDR, subnetworkPodCIDR string) error {
|
||||
out, err := exec.CommandContext(ctx, kubectlPath, "--kubeconfig", kubeConfig, "patch", "node", nodeName, "-p", "{\"spec\":{\"podCIDR\": \""+nodePodCIDR+"\"}}").CombinedOutput()
|
||||
if err != nil {
|
||||
err = errors.New(string(out))
|
||||
@ -248,13 +267,13 @@ func (k *KubernetesUtil) setupGCPPodNetwork(ctx context.Context, nodeName, nodeP
|
||||
return err
|
||||
}
|
||||
|
||||
ciliumInstall := exec.CommandContext(ctx, "cilium", "install", "--ipam", "kubernetes", "--ipv4-native-routing-cidr", subnetworkPodCIDR,
|
||||
"--helm-set", "endpointRoutes.enabled=true,tunnel=disabled,encryption.enabled=true,encryption.type=wireguard,l7Proxy=false")
|
||||
ciliumInstall.Env = append(os.Environ(), "KUBECONFIG="+kubeConfig)
|
||||
out, err = ciliumInstall.CombinedOutput()
|
||||
// configure pod network CIDR
|
||||
ciliumDeployment.Values["ipv4NativeRoutingCIDR"] = subnetworkPodCIDR
|
||||
ciliumDeployment.Values["strictModeCIDR"] = subnetworkPodCIDR
|
||||
|
||||
_, err = helmClient.RunWithContext(ctx, ciliumDeployment.Chart, ciliumDeployment.Values)
|
||||
if err != nil {
|
||||
err = errors.New(string(out))
|
||||
return err
|
||||
return fmt.Errorf("installing cilium: %w", err)
|
||||
}
|
||||
|
||||
return nil
|
||||
@ -264,14 +283,15 @@ func (k *KubernetesUtil) setupGCPPodNetwork(ctx context.Context, nodeName, nodeP
|
||||
// the cilium daemonset, it only restarts the local cilium pod.
|
||||
func (k *KubernetesUtil) FixCilium(nodeNameK8s string, log *logger.Logger) {
|
||||
// wait for cilium pod to be healthy
|
||||
client := http.Client{}
|
||||
for {
|
||||
time.Sleep(5 * time.Second)
|
||||
req, err := http.NewRequestWithContext(context.Background(), http.MethodGet, "http://127.0.0.1:9876/healthz", nil)
|
||||
req, err := http.NewRequestWithContext(context.Background(), http.MethodGet, "http://127.0.0.1:9879/healthz", http.NoBody)
|
||||
if err != nil {
|
||||
log.With(zap.Error(err)).Errorf("Unable to create request")
|
||||
continue
|
||||
}
|
||||
resp, err := http.DefaultClient.Do(req)
|
||||
resp, err := client.Do(req)
|
||||
if err != nil {
|
||||
log.With(zap.Error(err)).Warnf("Waiting for local cilium daemonset pod not healthy")
|
||||
continue
|
||||
@ -303,13 +323,19 @@ func (k *KubernetesUtil) FixCilium(nodeNameK8s string, log *logger.Logger) {
|
||||
}
|
||||
}
|
||||
|
||||
func (k *KubernetesUtil) setupQemuPodNetwork(ctx context.Context, subnetworkPodCIDR string) error {
|
||||
ciliumInstall := exec.CommandContext(ctx, "cilium", "install", "--encryption", "wireguard", "--helm-set", "ipam.operator.clusterPoolIPv4PodCIDRList="+subnetworkPodCIDR+",endpointRoutes.enabled=true")
|
||||
ciliumInstall.Env = append(os.Environ(), "KUBECONFIG="+kubeConfig)
|
||||
out, err := ciliumInstall.CombinedOutput()
|
||||
func (k *KubernetesUtil) deployCiliumQEMU(ctx context.Context, helmClient *action.Install, ciliumDeployment helm.Deployment, subnetworkPodCIDR string) error {
|
||||
// configure pod network CIDR
|
||||
ciliumDeployment.Values["ipam"] = map[string]interface{}{
|
||||
"operator": map[string]interface{}{
|
||||
"clusterPoolIPv4PodCIDRList": []interface{}{
|
||||
subnetworkPodCIDR,
|
||||
},
|
||||
},
|
||||
}
|
||||
|
||||
_, err := helmClient.RunWithContext(ctx, ciliumDeployment.Chart, ciliumDeployment.Values)
|
||||
if err != nil {
|
||||
err = errors.New(string(out))
|
||||
return err
|
||||
return fmt.Errorf("installing cilium: %w", err)
|
||||
}
|
||||
return nil
|
||||
}
|
||||
@ -453,9 +479,9 @@ func (k *KubernetesUtil) createSignedKubeletCert(nodeName string, ips []net.IP)
|
||||
}
|
||||
|
||||
parentCertRaw, err := k.file.Read(filepath.Join(
|
||||
constants.KubernetesDir,
|
||||
constants.DefaultCertificateDir,
|
||||
constants.CACertName,
|
||||
kubeconstants.KubernetesDir,
|
||||
kubeconstants.DefaultCertificateDir,
|
||||
kubeconstants.CACertName,
|
||||
))
|
||||
if err != nil {
|
||||
return err
|
||||
@ -467,9 +493,9 @@ func (k *KubernetesUtil) createSignedKubeletCert(nodeName string, ips []net.IP)
|
||||
}
|
||||
|
||||
parentKeyRaw, err := k.file.Read(filepath.Join(
|
||||
constants.KubernetesDir,
|
||||
constants.DefaultCertificateDir,
|
||||
constants.CAKeyName,
|
||||
kubeconstants.KubernetesDir,
|
||||
kubeconstants.DefaultCertificateDir,
|
||||
kubeconstants.CAKeyName,
|
||||
))
|
||||
if err != nil {
|
||||
return err
|
||||
|
||||
@ -14,7 +14,7 @@ type clusterUtil interface {
|
||||
InstallComponents(ctx context.Context, version versions.ValidK8sVersion) error
|
||||
InitCluster(ctx context.Context, initConfig []byte, nodeName string, ips []net.IP, log *logger.Logger) error
|
||||
JoinCluster(ctx context.Context, joinConfig []byte, log *logger.Logger) error
|
||||
SetupPodNetwork(context.Context, k8sapi.SetupPodNetworkInput, k8sapi.Client) error
|
||||
SetupHelmDeployments(ctx context.Context, client k8sapi.Client, helmDeployments []byte, in k8sapi.SetupPodNetworkInput, log *logger.Logger) error
|
||||
SetupAccessManager(kubectl k8sapi.Client, sshUsers resources.Marshaler) error
|
||||
SetupAutoscaling(kubectl k8sapi.Client, clusterAutoscalerConfiguration resources.Marshaler, secrets resources.Marshaler) error
|
||||
SetupJoinService(kubectl k8sapi.Client, joinServiceConfiguration resources.Marshaler) error
|
||||
|
||||
@ -71,7 +71,7 @@ func New(cloudProvider string, clusterUtil clusterUtil, configProvider configura
|
||||
// InitCluster initializes a new Kubernetes cluster and applies pod network provider.
|
||||
func (k *KubeWrapper) InitCluster(
|
||||
ctx context.Context, autoscalingNodeGroups []string, cloudServiceAccountURI, versionString string,
|
||||
measurementSalt []byte, kmsConfig resources.KMSConfig, sshUsers map[string]string, log *logger.Logger,
|
||||
measurementSalt []byte, kmsConfig resources.KMSConfig, sshUsers map[string]string, helmDeployments []byte, log *logger.Logger,
|
||||
) ([]byte, error) {
|
||||
k8sVersion, err := versions.NewValidK8sVersion(versionString)
|
||||
if err != nil {
|
||||
@ -170,9 +170,8 @@ func (k *KubeWrapper) InitCluster(
|
||||
NodeName: nodeName,
|
||||
FirstNodePodCIDR: nodePodCIDR,
|
||||
SubnetworkPodCIDR: subnetworkPodCIDR,
|
||||
ProviderID: providerID,
|
||||
}
|
||||
if err = k.clusterUtil.SetupPodNetwork(ctx, setupPodNetworkInput, k.client); err != nil {
|
||||
if err = k.clusterUtil.SetupHelmDeployments(ctx, k.client, helmDeployments, setupPodNetworkInput, log); err != nil {
|
||||
return nil, fmt.Errorf("setting up pod network: %w", err)
|
||||
}
|
||||
|
||||
|
||||
@ -170,8 +170,8 @@ func TestInitCluster(t *testing.T) {
|
||||
wantErr: true,
|
||||
k8sVersion: versions.Latest,
|
||||
},
|
||||
"kubeadm init fails when setting up the pod network": {
|
||||
clusterUtil: stubClusterUtil{setupPodNetworkErr: someErr},
|
||||
"kubeadm init fails when deploying helm charts": {
|
||||
clusterUtil: stubClusterUtil{setupHelmDeploymentsErr: someErr},
|
||||
kubeconfigReader: &stubKubeconfigReader{
|
||||
Kubeconfig: []byte("someKubeconfig"),
|
||||
},
|
||||
@ -296,7 +296,7 @@ func TestInitCluster(t *testing.T) {
|
||||
kubeconfigReader: tc.kubeconfigReader,
|
||||
getIPAddr: func() (string, error) { return privateIP, nil },
|
||||
}
|
||||
_, err := kube.InitCluster(context.Background(), autoscalingNodeGroups, serviceAccountURI, string(tc.k8sVersion), nil, resources.KMSConfig{MasterSecret: masterSecret}, nil, logger.NewTest(t))
|
||||
_, err := kube.InitCluster(context.Background(), autoscalingNodeGroups, serviceAccountURI, string(tc.k8sVersion), nil, resources.KMSConfig{MasterSecret: masterSecret}, nil, nil, logger.NewTest(t))
|
||||
|
||||
if tc.wantErr {
|
||||
assert.Error(err)
|
||||
@ -504,7 +504,7 @@ func TestK8sCompliantHostname(t *testing.T) {
|
||||
type stubClusterUtil struct {
|
||||
installComponentsErr error
|
||||
initClusterErr error
|
||||
setupPodNetworkErr error
|
||||
setupHelmDeploymentsErr error
|
||||
setupAutoscalingError error
|
||||
setupJoinServiceError error
|
||||
setupCloudControllerManagerError error
|
||||
@ -533,8 +533,8 @@ func (s *stubClusterUtil) InitCluster(ctx context.Context, initConfig []byte, no
|
||||
return s.initClusterErr
|
||||
}
|
||||
|
||||
func (s *stubClusterUtil) SetupPodNetwork(context.Context, k8sapi.SetupPodNetworkInput, k8sapi.Client) error {
|
||||
return s.setupPodNetworkErr
|
||||
func (s *stubClusterUtil) SetupHelmDeployments(context.Context, k8sapi.Client, []byte, k8sapi.SetupPodNetworkInput, *logger.Logger) error {
|
||||
return s.setupHelmDeploymentsErr
|
||||
}
|
||||
|
||||
func (s *stubClusterUtil) SetupAutoscaling(kubectl k8sapi.Client, clusterAutoscalerConfiguration resources.Marshaler, secrets resources.Marshaler) error {
|
||||
|
||||
13
cli/internal/cmd/helmloader.go
Normal file
13
cli/internal/cmd/helmloader.go
Normal file
@ -0,0 +1,13 @@
|
||||
package cmd
|
||||
|
||||
type helmLoader interface {
|
||||
Load(csp string) ([]byte, error)
|
||||
}
|
||||
|
||||
type stubHelmLoader struct {
|
||||
loadErr error
|
||||
}
|
||||
|
||||
func (d *stubHelmLoader) Load(csp string) ([]byte, error) {
|
||||
return nil, d.loadErr
|
||||
}
|
||||
@ -16,6 +16,7 @@ import (
|
||||
"github.com/edgelesssys/constellation/cli/internal/azure"
|
||||
"github.com/edgelesssys/constellation/cli/internal/cloudcmd"
|
||||
"github.com/edgelesssys/constellation/cli/internal/gcp"
|
||||
"github.com/edgelesssys/constellation/cli/internal/helm"
|
||||
"github.com/edgelesssys/constellation/internal/cloud/cloudprovider"
|
||||
"github.com/edgelesssys/constellation/internal/cloud/cloudtypes"
|
||||
"github.com/edgelesssys/constellation/internal/config"
|
||||
@ -55,12 +56,13 @@ func runInitialize(cmd *cobra.Command, args []string) error {
|
||||
newDialer := func(validator *cloudcmd.Validator) *dialer.Dialer {
|
||||
return dialer.New(nil, validator.V(), &net.Dialer{})
|
||||
}
|
||||
return initialize(cmd, newDialer, serviceAccountCreator, fileHandler)
|
||||
helmLoader := &helm.ChartLoader{}
|
||||
return initialize(cmd, newDialer, serviceAccountCreator, fileHandler, helmLoader)
|
||||
}
|
||||
|
||||
// initialize initializes a Constellation.
|
||||
func initialize(cmd *cobra.Command, newDialer func(*cloudcmd.Validator) *dialer.Dialer,
|
||||
serviceAccCreator serviceAccountCreator, fileHandler file.Handler,
|
||||
func initialize(cmd *cobra.Command, newDialer func(validator *cloudcmd.Validator) *dialer.Dialer,
|
||||
serviceAccCreator serviceAccountCreator, fileHandler file.Handler, helmLoader helmLoader,
|
||||
) error {
|
||||
flags, err := evalFlagArgs(cmd, fileHandler)
|
||||
if err != nil {
|
||||
@ -115,6 +117,12 @@ func initialize(cmd *cobra.Command, newDialer func(*cloudcmd.Validator) *dialer.
|
||||
autoscalingNodeGroups = append(autoscalingNodeGroups, workers.GroupID)
|
||||
}
|
||||
|
||||
cmd.Println("Loading Helm charts ...")
|
||||
helmDeployments, err := helmLoader.Load(stat.CloudProvider)
|
||||
if err != nil {
|
||||
return fmt.Errorf("loading Helm charts: %w", err)
|
||||
}
|
||||
|
||||
req := &initproto.InitRequest{
|
||||
AutoscalingNodeGroups: autoscalingNodeGroups,
|
||||
MasterSecret: flags.masterSecret.Key,
|
||||
@ -126,6 +134,7 @@ func initialize(cmd *cobra.Command, newDialer func(*cloudcmd.Validator) *dialer.
|
||||
CloudServiceAccountUri: serviceAccount,
|
||||
KubernetesVersion: config.KubernetesVersion,
|
||||
SshUserKeys: ssh.ToProtoSlice(sshUsers),
|
||||
HelmDeployments: helmDeployments,
|
||||
}
|
||||
resp, err := initCall(cmd.Context(), newDialer(validator), stat.BootstrapperHost, req)
|
||||
if err != nil {
|
||||
|
||||
@ -85,6 +85,7 @@ func TestInitialize(t *testing.T) {
|
||||
testCases := map[string]struct {
|
||||
existingState state.ConstellationState
|
||||
serviceAccountCreator stubServiceAccountCreator
|
||||
helmLoader stubHelmLoader
|
||||
initServerAPI *stubInitServer
|
||||
setAutoscaleFlag bool
|
||||
wantErr bool
|
||||
@ -127,6 +128,12 @@ func TestInitialize(t *testing.T) {
|
||||
serviceAccountCreator: stubServiceAccountCreator{createErr: someErr},
|
||||
wantErr: true,
|
||||
},
|
||||
"fail to load helm charts": {
|
||||
existingState: testGcpState,
|
||||
helmLoader: stubHelmLoader{loadErr: someErr},
|
||||
initServerAPI: &stubInitServer{initResp: testInitResp},
|
||||
wantErr: true,
|
||||
},
|
||||
}
|
||||
|
||||
for name, tc := range testCases {
|
||||
@ -162,7 +169,7 @@ func TestInitialize(t *testing.T) {
|
||||
defer cancel()
|
||||
cmd.SetContext(ctx)
|
||||
|
||||
err := initialize(cmd, newDialer, &tc.serviceAccountCreator, fileHandler)
|
||||
err := initialize(cmd, newDialer, &tc.serviceAccountCreator, fileHandler, &tc.helmLoader)
|
||||
|
||||
if tc.wantErr {
|
||||
assert.Error(err)
|
||||
@ -441,7 +448,7 @@ func TestAttestation(t *testing.T) {
|
||||
defer cancel()
|
||||
cmd.SetContext(ctx)
|
||||
|
||||
err := initialize(cmd, newDialer, &stubServiceAccountCreator{}, fileHandler)
|
||||
err := initialize(cmd, newDialer, &stubServiceAccountCreator{}, fileHandler, &stubHelmLoader{})
|
||||
assert.Error(err)
|
||||
// make sure the error is actually a TLS handshake error
|
||||
assert.Contains(err.Error(), "transport: authentication handshake failed")
|
||||
|
||||
23
cli/internal/helm/charts/cilium/.helmignore
Normal file
23
cli/internal/helm/charts/cilium/.helmignore
Normal file
@ -0,0 +1,23 @@
|
||||
# Patterns to ignore when building packages.
|
||||
# This supports shell glob matching, relative path matching, and
|
||||
# negation (prefixed with !). Only one pattern per line.
|
||||
.DS_Store
|
||||
# Common VCS dirs
|
||||
.git/
|
||||
.gitignore
|
||||
.bzr/
|
||||
.bzrignore
|
||||
.hg/
|
||||
.hgignore
|
||||
.svn/
|
||||
# Common backup files
|
||||
*.swp
|
||||
*.bak
|
||||
*.tmp
|
||||
*.orig
|
||||
*~
|
||||
# Various IDEs
|
||||
.project
|
||||
.idea/
|
||||
*.tmproj
|
||||
.vscode/
|
||||
127
cli/internal/helm/charts/cilium/Chart.yaml
Normal file
127
cli/internal/helm/charts/cilium/Chart.yaml
Normal file
@ -0,0 +1,127 @@
|
||||
apiVersion: v2
|
||||
name: cilium
|
||||
displayName: Cilium
|
||||
home: https://cilium.io/
|
||||
version: 1.12.0
|
||||
appVersion: 1.12.0
|
||||
kubeVersion: ">= 1.16.0-0"
|
||||
icon: https://cdn.jsdelivr.net/gh/cilium/cilium@v1.12/Documentation/images/logo-solo.svg
|
||||
description: eBPF-based Networking, Security, and Observability
|
||||
keywords:
|
||||
- BPF
|
||||
- eBPF
|
||||
- Kubernetes
|
||||
- Networking
|
||||
- Security
|
||||
- Observability
|
||||
- Troubleshooting
|
||||
sources:
|
||||
- https://github.com/cilium/cilium
|
||||
links:
|
||||
- name: eBPF.io
|
||||
url: https://ebpf.io/
|
||||
annotations:
|
||||
artifacthub.io/crds: |
|
||||
- kind: CiliumNetworkPolicy
|
||||
version: v2
|
||||
name: ciliumnetworkpolicies.cilium.io
|
||||
displayName: Cilium Network Policy
|
||||
description: |
|
||||
Cilium Network Policies provide additional functionality beyond what
|
||||
is provided by standard Kubernetes NetworkPolicy such as the ability
|
||||
to allow traffic based on FQDNs, or to filter at Layer 7.
|
||||
- kind: CiliumClusterwideNetworkPolicy
|
||||
version: v2
|
||||
name: ciliumclusterwidenetworkpolicies.cilium.io
|
||||
displayName: Cilium Clusterwide Network Policy
|
||||
description: |
|
||||
Cilium Clusterwide Network Policies support configuring network traffic
|
||||
policiies across the entire cluster, including applying node firewalls.
|
||||
- kind: CiliumExternalWorkload
|
||||
version: v2
|
||||
name: ciliumexternalworkloads.cilium.io
|
||||
displayName: Cilium External Workload
|
||||
description: |
|
||||
Cilium External Workload supports configuring the ability for external
|
||||
non-Kubernetes workloads to join the cluster.
|
||||
- kind: CiliumLocalRedirectPolicy
|
||||
version: v2
|
||||
name: ciliumlocalredirectpolicies.cilium.io
|
||||
displayName: Cilium Local Redirect Policy
|
||||
description: |
|
||||
Cilium Local Redirect Policy allows local redirects to be configured
|
||||
within a node to support use cases like Node-Local DNS or KIAM.
|
||||
- kind: CiliumNode
|
||||
version: v2
|
||||
name: ciliumnodes.cilium.io
|
||||
displayName: Cilium Node
|
||||
description: |
|
||||
Cilium Node represents a node managed by Cilium. It contains a
|
||||
specification to control various node specific configuration aspects
|
||||
and a status section to represent the status of the node.
|
||||
- kind: CiliumIdentity
|
||||
version: v2
|
||||
name: ciliumidentities.cilium.io
|
||||
displayName: Cilium Identity
|
||||
description: |
|
||||
Cilium Identity allows introspection into security identities that
|
||||
Cilium allocates which identify sets of labels that are assigned to
|
||||
individual endpoints in the cluster.
|
||||
- kind: CiliumEndpoint
|
||||
version: v2
|
||||
name: ciliumendpoints.cilium.io
|
||||
displayName: Cilium Endpoint
|
||||
description: |
|
||||
Cilium Endpoint represents the status of individual pods or nodes in
|
||||
the cluster which are managed by Cilium, including enforcement status,
|
||||
IP addressing and whether the networking is succesfully operational.
|
||||
- kind: CiliumEndpointSlice
|
||||
version: v2alpha1
|
||||
name: ciliumendpointslices.cilium.io
|
||||
displayName: Cilium Endpoint Slice
|
||||
description: |
|
||||
Cilium Endpoint Slice represents the status of groups of pods or nodes
|
||||
in the cluster which are managed by Cilium, including enforcement status,
|
||||
IP addressing and whether the networking is succesfully operational.
|
||||
- kind: CiliumEgressNATPolicy
|
||||
version: v2alpha1
|
||||
name: ciliumegressnatpolicies.cilium.io
|
||||
displayName: Cilium Egress NAT Policy
|
||||
description: |
|
||||
Cilium Egress NAT Policy provides control over the way that traffic
|
||||
leaves the cluster and which source addresses to use for that traffic.
|
||||
- kind: CiliumEgressGatewayPolicy
|
||||
version: v2
|
||||
name: ciliumegressgatewaypolicies.cilium.io
|
||||
displayName: Cilium Egress Gateway Policy
|
||||
description: |
|
||||
Cilium Egress Gateway Policy provides control over the way that traffic
|
||||
leaves the cluster and which source addresses to use for that traffic.
|
||||
- kind: CiliumClusterwideEnvoyConfig
|
||||
version: v2
|
||||
name: ciliumclusterwideenvoyconfigs.cilium.io
|
||||
displayName: Cilium Clusterwide Envoy Config
|
||||
description: |
|
||||
Cilium Clusterwide Envoy Config specifies Envoy resources and K8s service mappings
|
||||
to be provisioned into Cilium host proxy instances in cluster context.
|
||||
- kind: CiliumEnvoyConfig
|
||||
version: v2
|
||||
name: ciliumenvoyconfigs.cilium.io
|
||||
displayName: Cilium Envoy Config
|
||||
description: |
|
||||
Cilium Envoy Config specifies Envoy resources and K8s service mappings
|
||||
to be provisioned into Cilium host proxy instances in namespace context.
|
||||
- kind: CiliumBGPPeeringPolicy
|
||||
version: v2alpha1
|
||||
name: ciliumbgppeeringpolicies.cilium.io
|
||||
displayName: Cilium BGP Peering Policy
|
||||
description: |
|
||||
Cilium BGP Peering Policy instructs Cilium to create specific BGP peering
|
||||
configurations.
|
||||
- kind: CiliumBGPLoadBalancerIPPool
|
||||
version: v2alpha1
|
||||
name: ciliumbgploadbalancerippools.cilium.io
|
||||
displayName: Cilium BGP Load Balancer IP Pool
|
||||
description: |
|
||||
Defining a Cilium BGP Load Balancer IP Pool instructs Cilium to assign and
|
||||
advertise LoadBalancer Services to BGP peers defined by Cilium BGP Peering Policies.
|
||||
202
cli/internal/helm/charts/cilium/LICENSE
Normal file
202
cli/internal/helm/charts/cilium/LICENSE
Normal file
@ -0,0 +1,202 @@
|
||||
Apache License
|
||||
Version 2.0, January 2004
|
||||
http://www.apache.org/licenses/
|
||||
|
||||
TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION
|
||||
|
||||
1. Definitions.
|
||||
|
||||
"License" shall mean the terms and conditions for use, reproduction,
|
||||
and distribution as defined by Sections 1 through 9 of this document.
|
||||
|
||||
"Licensor" shall mean the copyright owner or entity authorized by
|
||||
the copyright owner that is granting the License.
|
||||
|
||||
"Legal Entity" shall mean the union of the acting entity and all
|
||||
other entities that control, are controlled by, or are under common
|
||||
control with that entity. For the purposes of this definition,
|
||||
"control" means (i) the power, direct or indirect, to cause the
|
||||
direction or management of such entity, whether by contract or
|
||||
otherwise, or (ii) ownership of fifty percent (50%) or more of the
|
||||
outstanding shares, or (iii) beneficial ownership of such entity.
|
||||
|
||||
"You" (or "Your") shall mean an individual or Legal Entity
|
||||
exercising permissions granted by this License.
|
||||
|
||||
"Source" form shall mean the preferred form for making modifications,
|
||||
including but not limited to software source code, documentation
|
||||
source, and configuration files.
|
||||
|
||||
"Object" form shall mean any form resulting from mechanical
|
||||
transformation or translation of a Source form, including but
|
||||
not limited to compiled object code, generated documentation,
|
||||
and conversions to other media types.
|
||||
|
||||
"Work" shall mean the work of authorship, whether in Source or
|
||||
Object form, made available under the License, as indicated by a
|
||||
copyright notice that is included in or attached to the work
|
||||
(an example is provided in the Appendix below).
|
||||
|
||||
"Derivative Works" shall mean any work, whether in Source or Object
|
||||
form, that is based on (or derived from) the Work and for which the
|
||||
editorial revisions, annotations, elaborations, or other modifications
|
||||
represent, as a whole, an original work of authorship. For the purposes
|
||||
of this License, Derivative Works shall not include works that remain
|
||||
separable from, or merely link (or bind by name) to the interfaces of,
|
||||
the Work and Derivative Works thereof.
|
||||
|
||||
"Contribution" shall mean any work of authorship, including
|
||||
the original version of the Work and any modifications or additions
|
||||
to that Work or Derivative Works thereof, that is intentionally
|
||||
submitted to Licensor for inclusion in the Work by the copyright owner
|
||||
or by an individual or Legal Entity authorized to submit on behalf of
|
||||
the copyright owner. For the purposes of this definition, "submitted"
|
||||
means any form of electronic, verbal, or written communication sent
|
||||
to the Licensor or its representatives, including but not limited to
|
||||
communication on electronic mailing lists, source code control systems,
|
||||
and issue tracking systems that are managed by, or on behalf of, the
|
||||
Licensor for the purpose of discussing and improving the Work, but
|
||||
excluding communication that is conspicuously marked or otherwise
|
||||
designated in writing by the copyright owner as "Not a Contribution."
|
||||
|
||||
"Contributor" shall mean Licensor and any individual or Legal Entity
|
||||
on behalf of whom a Contribution has been received by Licensor and
|
||||
subsequently incorporated within the Work.
|
||||
|
||||
2. Grant of Copyright License. Subject to the terms and conditions of
|
||||
this License, each Contributor hereby grants to You a perpetual,
|
||||
worldwide, non-exclusive, no-charge, royalty-free, irrevocable
|
||||
copyright license to reproduce, prepare Derivative Works of,
|
||||
publicly display, publicly perform, sublicense, and distribute the
|
||||
Work and such Derivative Works in Source or Object form.
|
||||
|
||||
3. Grant of Patent License. Subject to the terms and conditions of
|
||||
this License, each Contributor hereby grants to You a perpetual,
|
||||
worldwide, non-exclusive, no-charge, royalty-free, irrevocable
|
||||
(except as stated in this section) patent license to make, have made,
|
||||
use, offer to sell, sell, import, and otherwise transfer the Work,
|
||||
where such license applies only to those patent claims licensable
|
||||
by such Contributor that are necessarily infringed by their
|
||||
Contribution(s) alone or by combination of their Contribution(s)
|
||||
with the Work to which such Contribution(s) was submitted. If You
|
||||
institute patent litigation against any entity (including a
|
||||
cross-claim or counterclaim in a lawsuit) alleging that the Work
|
||||
or a Contribution incorporated within the Work constitutes direct
|
||||
or contributory patent infringement, then any patent licenses
|
||||
granted to You under this License for that Work shall terminate
|
||||
as of the date such litigation is filed.
|
||||
|
||||
4. Redistribution. You may reproduce and distribute copies of the
|
||||
Work or Derivative Works thereof in any medium, with or without
|
||||
modifications, and in Source or Object form, provided that You
|
||||
meet the following conditions:
|
||||
|
||||
(a) You must give any other recipients of the Work or
|
||||
Derivative Works a copy of this License; and
|
||||
|
||||
(b) You must cause any modified files to carry prominent notices
|
||||
stating that You changed the files; and
|
||||
|
||||
(c) You must retain, in the Source form of any Derivative Works
|
||||
that You distribute, all copyright, patent, trademark, and
|
||||
attribution notices from the Source form of the Work,
|
||||
excluding those notices that do not pertain to any part of
|
||||
the Derivative Works; and
|
||||
|
||||
(d) If the Work includes a "NOTICE" text file as part of its
|
||||
distribution, then any Derivative Works that You distribute must
|
||||
include a readable copy of the attribution notices contained
|
||||
within such NOTICE file, excluding those notices that do not
|
||||
pertain to any part of the Derivative Works, in at least one
|
||||
of the following places: within a NOTICE text file distributed
|
||||
as part of the Derivative Works; within the Source form or
|
||||
documentation, if provided along with the Derivative Works; or,
|
||||
within a display generated by the Derivative Works, if and
|
||||
wherever such third-party notices normally appear. The contents
|
||||
of the NOTICE file are for informational purposes only and
|
||||
do not modify the License. You may add Your own attribution
|
||||
notices within Derivative Works that You distribute, alongside
|
||||
or as an addendum to the NOTICE text from the Work, provided
|
||||
that such additional attribution notices cannot be construed
|
||||
as modifying the License.
|
||||
|
||||
You may add Your own copyright statement to Your modifications and
|
||||
may provide additional or different license terms and conditions
|
||||
for use, reproduction, or distribution of Your modifications, or
|
||||
for any such Derivative Works as a whole, provided Your use,
|
||||
reproduction, and distribution of the Work otherwise complies with
|
||||
the conditions stated in this License.
|
||||
|
||||
5. Submission of Contributions. Unless You explicitly state otherwise,
|
||||
any Contribution intentionally submitted for inclusion in the Work
|
||||
by You to the Licensor shall be under the terms and conditions of
|
||||
this License, without any additional terms or conditions.
|
||||
Notwithstanding the above, nothing herein shall supersede or modify
|
||||
the terms of any separate license agreement you may have executed
|
||||
with Licensor regarding such Contributions.
|
||||
|
||||
6. Trademarks. This License does not grant permission to use the trade
|
||||
names, trademarks, service marks, or product names of the Licensor,
|
||||
except as required for reasonable and customary use in describing the
|
||||
origin of the Work and reproducing the content of the NOTICE file.
|
||||
|
||||
7. Disclaimer of Warranty. Unless required by applicable law or
|
||||
agreed to in writing, Licensor provides the Work (and each
|
||||
Contributor provides its Contributions) on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or
|
||||
implied, including, without limitation, any warranties or conditions
|
||||
of TITLE, NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A
|
||||
PARTICULAR PURPOSE. You are solely responsible for determining the
|
||||
appropriateness of using or redistributing the Work and assume any
|
||||
risks associated with Your exercise of permissions under this License.
|
||||
|
||||
8. Limitation of Liability. In no event and under no legal theory,
|
||||
whether in tort (including negligence), contract, or otherwise,
|
||||
unless required by applicable law (such as deliberate and grossly
|
||||
negligent acts) or agreed to in writing, shall any Contributor be
|
||||
liable to You for damages, including any direct, indirect, special,
|
||||
incidental, or consequential damages of any character arising as a
|
||||
result of this License or out of the use or inability to use the
|
||||
Work (including but not limited to damages for loss of goodwill,
|
||||
work stoppage, computer failure or malfunction, or any and all
|
||||
other commercial damages or losses), even if such Contributor
|
||||
has been advised of the possibility of such damages.
|
||||
|
||||
9. Accepting Warranty or Additional Liability. While redistributing
|
||||
the Work or Derivative Works thereof, You may choose to offer,
|
||||
and charge a fee for, acceptance of support, warranty, indemnity,
|
||||
or other liability obligations and/or rights consistent with this
|
||||
License. However, in accepting such obligations, You may act only
|
||||
on Your own behalf and on Your sole responsibility, not on behalf
|
||||
of any other Contributor, and only if You agree to indemnify,
|
||||
defend, and hold each Contributor harmless for any liability
|
||||
incurred by, or claims asserted against, such Contributor by reason
|
||||
of your accepting any such warranty or additional liability.
|
||||
|
||||
END OF TERMS AND CONDITIONS
|
||||
|
||||
APPENDIX: How to apply the Apache License to your work.
|
||||
|
||||
To apply the Apache License to your work, attach the following
|
||||
boilerplate notice, with the fields enclosed by brackets "{}"
|
||||
replaced with your own identifying information. (Don't include
|
||||
the brackets!) The text should be enclosed in the appropriate
|
||||
comment syntax for the file format. We also recommend that a
|
||||
file or class name and description of purpose be included on the
|
||||
same "printed page" as the copyright notice for easier
|
||||
identification within third-party archives.
|
||||
|
||||
Copyright {yyyy} Authors of Cilium
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
You may obtain a copy of the License at
|
||||
|
||||
http://www.apache.org/licenses/LICENSE-2.0
|
||||
|
||||
Unless required by applicable law or agreed to in writing, software
|
||||
distributed under the License is distributed on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
See the License for the specific language governing permissions and
|
||||
limitations under the License.
|
||||
|
||||
474
cli/internal/helm/charts/cilium/README.md
Normal file
474
cli/internal/helm/charts/cilium/README.md
Normal file
@ -0,0 +1,474 @@
|
||||
# cilium
|
||||
|
||||
 
|
||||
|
||||
Cilium is open source software for providing and transparently securing
|
||||
network connectivity and loadbalancing between application workloads such as
|
||||
application containers or processes. Cilium operates at Layer 3/4 to provide
|
||||
traditional networking and security services as well as Layer 7 to protect and
|
||||
secure use of modern application protocols such as HTTP, gRPC and Kafka.
|
||||
|
||||
A new Linux kernel technology called eBPF is at the foundation of Cilium.
|
||||
It supports dynamic insertion of eBPF bytecode into the Linux kernel at various
|
||||
integration points such as: network IO, application sockets, and tracepoints
|
||||
to implement security, networking and visibility logic. eBPF is highly
|
||||
efficient and flexible.
|
||||
|
||||
|
||||
|
||||
## Prerequisites
|
||||
|
||||
* Kubernetes: `>= 1.16.0-0`
|
||||
* Helm: `>= 3.0`
|
||||
|
||||
## Getting Started
|
||||
|
||||
Try Cilium on any Kubernetes distribution in under 15 minutes:
|
||||
|
||||
| Minikube | Self-Managed K8s | Amazon EKS | Google GKE | Microsoft AKS |
|
||||
|:-:|:-:|:-:|:-:|:-:|
|
||||
| [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) |
|
||||
|
||||
Or, for a quick install with the default configuration:
|
||||
|
||||
```
|
||||
$ helm repo add cilium https://helm.cilium.io/
|
||||
$ helm install cilium cilium/cilium --namespace=kube-system
|
||||
```
|
||||
|
||||
After Cilium is installed, you can explore the features that Cilium has to
|
||||
offer from the [Getting Started Guides page](https://docs.cilium.io/en/latest/gettingstarted/).
|
||||
|
||||
## Source Code
|
||||
|
||||
* <https://github.com/cilium/cilium>
|
||||
|
||||
## Getting Help
|
||||
|
||||
The best way to get help if you get stuck is to ask a question on the
|
||||
[Cilium Slack channel](https://cilium.herokuapp.com/). With Cilium
|
||||
contributors across the globe, there is almost always someone available to help.
|
||||
|
||||
## Values
|
||||
|
||||
| Key | Type | Default | Description |
|
||||
|-----|------|---------|-------------|
|
||||
| affinity | object | `{"podAntiAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"k8s-app":"cilium"}},"topologyKey":"kubernetes.io/hostname"}]}}` | Affinity for cilium-agent. |
|
||||
| agent | bool | `true` | Install the cilium agent resources. |
|
||||
| agentNotReadyTaintKey | string | `"node.cilium.io/agent-not-ready"` | Configure the key of the taint indicating that Cilium is not ready on the node. When set to a value starting with `ignore-taint.cluster-autoscaler.kubernetes.io/`, the Cluster Autoscaler will ignore the taint on its decisions, allowing the cluster to scale up. |
|
||||
| aksbyocni.enabled | bool | `false` | Enable AKS BYOCNI integration. Note that this is incompatible with AKS clusters not created in BYOCNI mode: use Azure integration (`azure.enabled`) instead. |
|
||||
| alibabacloud.enabled | bool | `false` | Enable AlibabaCloud ENI integration |
|
||||
| annotateK8sNode | bool | `false` | Annotate k8s node upon initialization with Cilium's metadata. |
|
||||
| autoDirectNodeRoutes | bool | `false` | Enable installation of PodCIDR routes between worker nodes if worker nodes share a common L2 network segment. |
|
||||
| azure.enabled | bool | `false` | Enable Azure integration. Note that this is incompatible with AKS clusters created in BYOCNI mode: use AKS BYOCNI integration (`aksbyocni.enabled`) instead. |
|
||||
| bandwidthManager | object | `{"bbr":false,"enabled":false}` | Enable bandwidth manager to optimize TCP and UDP workloads and allow for rate-limiting traffic from individual Pods with EDT (Earliest Departure Time) through the "kubernetes.io/egress-bandwidth" Pod annotation. |
|
||||
| bandwidthManager.bbr | bool | `false` | Activate BBR TCP congestion control for Pods |
|
||||
| bandwidthManager.enabled | bool | `false` | Enable bandwidth manager infrastructure (also prerequirement for BBR) |
|
||||
| bgp | object | `{"announce":{"loadbalancerIP":false,"podCIDR":false},"enabled":false}` | Configure BGP |
|
||||
| bgp.announce.loadbalancerIP | bool | `false` | Enable allocation and announcement of service LoadBalancer IPs |
|
||||
| bgp.announce.podCIDR | bool | `false` | Enable announcement of node pod CIDR |
|
||||
| bgp.enabled | bool | `false` | Enable BGP support inside Cilium; embeds a new ConfigMap for BGP inside cilium-agent and cilium-operator |
|
||||
| bgpControlPlane | object | `{"enabled":false}` | This feature set enables virtual BGP routers to be created via CiliumBGPPeeringPolicy CRDs. |
|
||||
| bgpControlPlane.enabled | bool | `false` | Enables the BGP control plane. |
|
||||
| bpf.clockProbe | bool | `false` | Enable BPF clock source probing for more efficient tick retrieval. |
|
||||
| bpf.lbExternalClusterIP | bool | `false` | Allow cluster external access to ClusterIP services. |
|
||||
| bpf.lbMapMax | int | `65536` | Configure the maximum number of service entries in the load balancer maps. |
|
||||
| bpf.monitorAggregation | string | `"medium"` | Configure the level of aggregation for monitor notifications. Valid options are none, low, medium, maximum. |
|
||||
| bpf.monitorFlags | string | `"all"` | Configure which TCP flags trigger notifications when seen for the first time in a connection. |
|
||||
| bpf.monitorInterval | string | `"5s"` | Configure the typical time between monitor notifications for active connections. |
|
||||
| bpf.policyMapMax | int | `16384` | Configure the maximum number of entries in endpoint policy map (per endpoint). |
|
||||
| bpf.preallocateMaps | bool | `false` | Enables pre-allocation of eBPF map values. This increases memory usage but can reduce latency. |
|
||||
| bpf.root | string | `"/sys/fs/bpf"` | Configure the mount point for the BPF filesystem |
|
||||
| certgen | object | `{"image":{"override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/certgen","tag":"v0.1.8@sha256:4a456552a5f192992a6edcec2febb1c54870d665173a33dc7d876129b199ddbd"},"podLabels":{},"tolerations":[],"ttlSecondsAfterFinished":1800}` | Configure certificate generation for Hubble integration. If hubble.tls.auto.method=cronJob, these values are used for the Kubernetes CronJob which will be scheduled regularly to (re)generate any certificates not provided manually. |
|
||||
| certgen.podLabels | object | `{}` | Labels to be added to hubble-certgen pods |
|
||||
| certgen.tolerations | list | `[]` | Node tolerations for pod assignment on nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| certgen.ttlSecondsAfterFinished | int | `1800` | Seconds after which the completed job pod will be deleted |
|
||||
| cgroup | object | `{"autoMount":{"enabled":true},"hostRoot":"/run/cilium/cgroupv2"}` | Configure cgroup related configuration |
|
||||
| cgroup.autoMount.enabled | bool | `true` | Enable auto mount of cgroup2 filesystem. When `autoMount` is enabled, cgroup2 filesystem is mounted at `cgroup.hostRoot` path on the underlying host and inside the cilium agent pod. If users disable `autoMount`, it's expected that users have mounted cgroup2 filesystem at the specified `cgroup.hostRoot` volume, and then the volume will be mounted inside the cilium agent pod at the same path. |
|
||||
| cgroup.hostRoot | string | `"/run/cilium/cgroupv2"` | Configure cgroup root where cgroup2 filesystem is mounted on the host (see also: `cgroup.autoMount`) |
|
||||
| cleanBpfState | bool | `false` | Clean all eBPF datapath state from the initContainer of the cilium-agent DaemonSet. WARNING: Use with care! |
|
||||
| cleanState | bool | `false` | Clean all local Cilium state from the initContainer of the cilium-agent DaemonSet. Implies cleanBpfState: true. WARNING: Use with care! |
|
||||
| cluster.id | int | `0` | (int) Unique ID of the cluster. Must be unique across all connected clusters and in the range of 1 to 255. Only required for Cluster Mesh, may be 0 if Cluster Mesh is not used. |
|
||||
| cluster.name | string | `"default"` | Name of the cluster. Only required for Cluster Mesh. |
|
||||
| clustermesh.apiserver.affinity | object | `{"podAntiAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"k8s-app":"clustermesh-apiserver"}},"topologyKey":"kubernetes.io/hostname"}]}}` | Affinity for clustermesh.apiserver |
|
||||
| clustermesh.apiserver.etcd.image | object | `{"override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/coreos/etcd","tag":"v3.5.4@sha256:795d8660c48c439a7c3764c2330ed9222ab5db5bb524d8d0607cac76f7ba82a3"}` | Clustermesh API server etcd image. |
|
||||
| clustermesh.apiserver.extraEnv | list | `[]` | Additional clustermesh-apiserver environment variables. |
|
||||
| clustermesh.apiserver.image | object | `{"digest":"sha256:3f5a6298bd70a2b555c88e291eec1583a6478c3e2272e3fc721aa03b3300d299","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/clustermesh-apiserver","tag":"v1.12.0","useDigest":true}` | Clustermesh API server image. |
|
||||
| clustermesh.apiserver.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for pod assignment ref: https://kubernetes.io/docs/user-guide/node-selection/ |
|
||||
| clustermesh.apiserver.podAnnotations | object | `{}` | Annotations to be added to clustermesh-apiserver pods |
|
||||
| clustermesh.apiserver.podDisruptionBudget.enabled | bool | `false` | enable PodDisruptionBudget ref: https://kubernetes.io/docs/concepts/workloads/pods/disruptions/ |
|
||||
| clustermesh.apiserver.podDisruptionBudget.maxUnavailable | int | `1` | Maximum number/percentage of pods that may be made unavailable |
|
||||
| clustermesh.apiserver.podDisruptionBudget.minAvailable | string | `nil` | Minimum number/percentage of pods that should remain scheduled. When it's set, maxUnavailable must be disabled by `maxUnavailable: null` |
|
||||
| clustermesh.apiserver.podLabels | object | `{}` | Labels to be added to clustermesh-apiserver pods |
|
||||
| clustermesh.apiserver.priorityClassName | string | `""` | The priority class to use for clustermesh-apiserver |
|
||||
| clustermesh.apiserver.replicas | int | `1` | Number of replicas run for the clustermesh-apiserver deployment. |
|
||||
| clustermesh.apiserver.resources | object | `{}` | Resource requests and limits for the clustermesh-apiserver |
|
||||
| clustermesh.apiserver.service.annotations | object | `{}` | Annotations for the clustermesh-apiserver For GKE LoadBalancer, use annotation cloud.google.com/load-balancer-type: "Internal" For EKS LoadBalancer, use annotation service.beta.kubernetes.io/aws-load-balancer-internal: 0.0.0.0/0 |
|
||||
| clustermesh.apiserver.service.nodePort | int | `32379` | Optional port to use as the node port for apiserver access. |
|
||||
| clustermesh.apiserver.service.type | string | `"NodePort"` | The type of service used for apiserver access. |
|
||||
| clustermesh.apiserver.tls.admin | object | `{"cert":"","key":""}` | base64 encoded PEM values for the clustermesh-apiserver admin certificate and private key. Used if 'auto' is not enabled. |
|
||||
| clustermesh.apiserver.tls.auto | object | `{"certManagerIssuerRef":{},"certValidityDuration":1095,"enabled":true,"method":"helm"}` | Configure automatic TLS certificates generation. A Kubernetes CronJob is used the generate any certificates not provided by the user at installation time. |
|
||||
| clustermesh.apiserver.tls.auto.certManagerIssuerRef | object | `{}` | certmanager issuer used when clustermesh.apiserver.tls.auto.method=certmanager. If not specified, a CA issuer will be created. |
|
||||
| clustermesh.apiserver.tls.auto.certValidityDuration | int | `1095` | Generated certificates validity duration in days. |
|
||||
| clustermesh.apiserver.tls.auto.enabled | bool | `true` | When set to true, automatically generate a CA and certificates to enable mTLS between clustermesh-apiserver and external workload instances. If set to false, the certs to be provided by setting appropriate values below. |
|
||||
| clustermesh.apiserver.tls.ca | object | `{"cert":"","key":""}` | base64 encoded PEM values for the ExternalWorkload CA certificate and private key. |
|
||||
| clustermesh.apiserver.tls.ca.cert | string | `""` | Optional CA cert. If it is provided, it will be used by the 'cronJob' method to generate all other certificates. Otherwise, an ephemeral CA is generated. |
|
||||
| clustermesh.apiserver.tls.ca.key | string | `""` | Optional CA private key. If it is provided, it will be used by the 'cronJob' method to generate all other certificates. Otherwise, an ephemeral CA is generated. |
|
||||
| clustermesh.apiserver.tls.client | object | `{"cert":"","key":""}` | base64 encoded PEM values for the clustermesh-apiserver client certificate and private key. Used if 'auto' is not enabled. |
|
||||
| clustermesh.apiserver.tls.remote | object | `{"cert":"","key":""}` | base64 encoded PEM values for the clustermesh-apiserver remote cluster certificate and private key. Used if 'auto' is not enabled. |
|
||||
| clustermesh.apiserver.tls.server | object | `{"cert":"","extraDnsNames":[],"extraIpAddresses":[],"key":""}` | base64 encoded PEM values for the clustermesh-apiserver server certificate and private key. Used if 'auto' is not enabled. |
|
||||
| clustermesh.apiserver.tls.server.extraDnsNames | list | `[]` | Extra DNS names added to certificate when it's auto generated |
|
||||
| clustermesh.apiserver.tls.server.extraIpAddresses | list | `[]` | Extra IP addresses added to certificate when it's auto generated |
|
||||
| clustermesh.apiserver.tolerations | list | `[]` | Node tolerations for pod assignment on nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| clustermesh.apiserver.updateStrategy | object | `{"rollingUpdate":{"maxUnavailable":1},"type":"RollingUpdate"}` | clustermesh-apiserver update strategy |
|
||||
| clustermesh.config | object | `{"clusters":[],"domain":"mesh.cilium.io","enabled":false}` | Clustermesh explicit configuration. |
|
||||
| clustermesh.config.clusters | list | `[]` | List of clusters to be peered in the mesh. |
|
||||
| clustermesh.config.domain | string | `"mesh.cilium.io"` | Default dns domain for the Clustermesh API servers This is used in the case cluster addresses are not provided and IPs are used. |
|
||||
| clustermesh.config.enabled | bool | `false` | Enable the Clustermesh explicit configuration. |
|
||||
| clustermesh.useAPIServer | bool | `false` | Deploy clustermesh-apiserver for clustermesh |
|
||||
| cni.binPath | string | `"/opt/cni/bin"` | Configure the path to the CNI binary directory on the host. |
|
||||
| cni.chainingMode | string | `"none"` | Configure chaining on top of other CNI plugins. Possible values: - none - aws-cni - flannel - generic-veth - portmap |
|
||||
| cni.confFileMountPath | string | `"/tmp/cni-configuration"` | Configure the path to where to mount the ConfigMap inside the agent pod. |
|
||||
| cni.confPath | string | `"/etc/cni/net.d"` | Configure the path to the CNI configuration directory on the host. |
|
||||
| cni.configMapKey | string | `"cni-config"` | Configure the key in the CNI ConfigMap to read the contents of the CNI configuration from. |
|
||||
| cni.customConf | bool | `false` | Skip writing of the CNI configuration. This can be used if writing of the CNI configuration is performed by external automation. |
|
||||
| cni.exclusive | bool | `true` | Make Cilium take ownership over the `/etc/cni/net.d` directory on the node, renaming all non-Cilium CNI configurations to `*.cilium_bak`. This ensures no Pods can be scheduled using other CNI plugins during Cilium agent downtime. |
|
||||
| cni.hostConfDirMountPath | string | `"/host/etc/cni/net.d"` | Configure the path to where the CNI configuration directory is mounted inside the agent pod. |
|
||||
| cni.install | bool | `true` | Install the CNI configuration and binary files into the filesystem. |
|
||||
| cni.logFile | string | `"/var/run/cilium/cilium-cni.log"` | Configure the log file for CNI logging with retention policy of 7 days. Disable CNI file logging by setting this field to empty explicitly. |
|
||||
| containerRuntime | object | `{"integration":"none"}` | Configure container runtime specific integration. |
|
||||
| containerRuntime.integration | string | `"none"` | Enables specific integrations for container runtimes. Supported values: - containerd - crio - docker - none - auto (automatically detect the container runtime) |
|
||||
| customCalls | object | `{"enabled":false}` | Tail call hooks for custom eBPF programs. |
|
||||
| customCalls.enabled | bool | `false` | Enable tail call hooks for custom eBPF programs. |
|
||||
| daemon.runPath | string | `"/var/run/cilium"` | Configure where Cilium runtime state should be stored. |
|
||||
| datapathMode | string | `"veth"` | Configure which datapath mode should be used for configuring container connectivity. Valid options are "veth" or "ipvlan". Deprecated, to be removed in v1.12. |
|
||||
| debug.enabled | bool | `false` | Enable debug logging |
|
||||
| disableEndpointCRD | string | `"false"` | Disable the usage of CiliumEndpoint CRD. |
|
||||
| dnsPolicy | string | `""` | DNS policy for Cilium agent pods. Ref: https://kubernetes.io/docs/concepts/services-networking/dns-pod-service/#pod-s-dns-policy |
|
||||
| dnsProxy.dnsRejectResponseCode | string | `"refused"` | DNS response code for rejecting DNS requests, available options are '[nameError refused]'. |
|
||||
| dnsProxy.enableDnsCompression | bool | `true` | Allow the DNS proxy to compress responses to endpoints that are larger than 512 Bytes or the EDNS0 option, if present. |
|
||||
| dnsProxy.endpointMaxIpPerHostname | int | `50` | Maximum number of IPs to maintain per FQDN name for each endpoint. |
|
||||
| dnsProxy.idleConnectionGracePeriod | string | `"0s"` | Time during which idle but previously active connections with expired DNS lookups are still considered alive. |
|
||||
| dnsProxy.maxDeferredConnectionDeletes | int | `10000` | Maximum number of IPs to retain for expired DNS lookups with still-active connections. |
|
||||
| dnsProxy.minTtl | int | `3600` | The minimum time, in seconds, to use DNS data for toFQDNs policies. |
|
||||
| dnsProxy.preCache | string | `""` | DNS cache data at this path is preloaded on agent startup. |
|
||||
| dnsProxy.proxyPort | int | `0` | Global port on which the in-agent DNS proxy should listen. Default 0 is a OS-assigned port. |
|
||||
| dnsProxy.proxyResponseMaxDelay | string | `"100ms"` | The maximum time the DNS proxy holds an allowed DNS response before sending it along. Responses are sent as soon as the datapath is updated with the new IP information. |
|
||||
| egressGateway | object | `{"enabled":false,"installRoutes":false}` | Enables egress gateway to redirect and SNAT the traffic that leaves the cluster. |
|
||||
| egressGateway.installRoutes | bool | `false` | Install egress gateway IP rules and routes in order to properly steer egress gateway traffic to the correct ENI interface |
|
||||
| enableCiliumEndpointSlice | bool | `false` | Enable CiliumEndpointSlice feature. |
|
||||
| enableCnpStatusUpdates | bool | `false` | Whether to enable CNP status updates. |
|
||||
| enableCriticalPriorityClass | bool | `true` | Explicitly enable or disable priority class. .Capabilities.KubeVersion is unsettable in `helm template` calls, it depends on k8s libraries version that Helm was compiled against. This option allows to explicitly disable setting the priority class, which is useful for rendering charts for gke clusters in advance. |
|
||||
| enableIPv4Masquerade | bool | `true` | Enables masquerading of IPv4 traffic leaving the node from endpoints. |
|
||||
| enableIPv6Masquerade | bool | `true` | Enables masquerading of IPv6 traffic leaving the node from endpoints. |
|
||||
| enableK8sEventHandover | bool | `false` | Configures the use of the KVStore to optimize Kubernetes event handling by mirroring it into the KVstore for reduced overhead in large clusters. |
|
||||
| enableK8sTerminatingEndpoint | bool | `true` | Configure whether to enable auto detect of terminating state for endpoints in order to support graceful termination. |
|
||||
| enableRuntimeDeviceDetection | bool | `false` | Enables experimental support for the detection of new and removed datapath devices. When devices change the eBPF datapath is reloaded and services updated. If "devices" is set then only those devices, or devices matching a wildcard will be considered. |
|
||||
| enableXTSocketFallback | bool | `true` | Enables the fallback compatibility solution for when the xt_socket kernel module is missing and it is needed for the datapath L7 redirection to work properly. See documentation for details on when this can be disabled: https://docs.cilium.io/en/stable/operations/system_requirements/#linux-kernel. |
|
||||
| encryption.enabled | bool | `false` | Enable transparent network encryption. |
|
||||
| encryption.interface | string | `""` | Deprecated in favor of encryption.ipsec.interface. The interface to use for encrypted traffic. This option is only effective when encryption.type is set to ipsec. |
|
||||
| encryption.ipsec.interface | string | `""` | The interface to use for encrypted traffic. |
|
||||
| encryption.ipsec.keyFile | string | `""` | Name of the key file inside the Kubernetes secret configured via secretName. |
|
||||
| encryption.ipsec.mountPath | string | `""` | Path to mount the secret inside the Cilium pod. |
|
||||
| encryption.ipsec.secretName | string | `""` | Name of the Kubernetes secret containing the encryption keys. |
|
||||
| encryption.keyFile | string | `"keys"` | Deprecated in favor of encryption.ipsec.keyFile. Name of the key file inside the Kubernetes secret configured via secretName. This option is only effective when encryption.type is set to ipsec. |
|
||||
| encryption.mountPath | string | `"/etc/ipsec"` | Deprecated in favor of encryption.ipsec.mountPath. Path to mount the secret inside the Cilium pod. This option is only effective when encryption.type is set to ipsec. |
|
||||
| encryption.nodeEncryption | bool | `false` | Enable encryption for pure node to node traffic. This option is only effective when encryption.type is set to ipsec. |
|
||||
| encryption.secretName | string | `"cilium-ipsec-keys"` | Deprecated in favor of encryption.ipsec.secretName. Name of the Kubernetes secret containing the encryption keys. This option is only effective when encryption.type is set to ipsec. |
|
||||
| encryption.type | string | `"ipsec"` | Encryption method. Can be either ipsec or wireguard. |
|
||||
| encryption.wireguard.userspaceFallback | bool | `false` | Enables the fallback to the user-space implementation. |
|
||||
| endpointHealthChecking.enabled | bool | `true` | Enable connectivity health checking between virtual endpoints. |
|
||||
| endpointRoutes.enabled | bool | `false` | Enable use of per endpoint routes instead of routing via the cilium_host interface. |
|
||||
| endpointStatus | object | `{"enabled":false,"status":""}` | Enable endpoint status. Status can be: policy, health, controllers, logs and / or state. For 2 or more options use a comma. |
|
||||
| eni.awsEnablePrefixDelegation | bool | `false` | Enable ENI prefix delegation |
|
||||
| eni.awsReleaseExcessIPs | bool | `false` | Release IPs not used from the ENI |
|
||||
| eni.ec2APIEndpoint | string | `""` | EC2 API endpoint to use |
|
||||
| eni.enabled | bool | `false` | Enable Elastic Network Interface (ENI) integration. |
|
||||
| eni.eniTags | object | `{}` | Tags to apply to the newly created ENIs |
|
||||
| eni.iamRole | string | `""` | If using IAM role for Service Accounts will not try to inject identity values from cilium-aws kubernetes secret. Adds annotation to service account if managed by Helm. See https://github.com/aws/amazon-eks-pod-identity-webhook |
|
||||
| eni.instanceTagsFilter | string | `""` | Filter via AWS EC2 Instance tags (k=v) which will dictate which AWS EC2 Instances are going to be used to create new ENIs |
|
||||
| eni.subnetIDsFilter | string | `""` | Filter via subnet IDs which will dictate which subnets are going to be used to create new ENIs Important note: This requires that each instance has an ENI with a matching subnet attached when Cilium is deployed. If you only want to control subnets for ENIs attached by Cilium, use the CNI configuration file settings (cni.customConf) instead. |
|
||||
| eni.subnetTagsFilter | string | `""` | Filter via tags (k=v) which will dictate which subnets are going to be used to create new ENIs Important note: This requires that each instance has an ENI with a matching subnet attached when Cilium is deployed. If you only want to control subnets for ENIs attached by Cilium, use the CNI configuration file settings (cni.customConf) instead. |
|
||||
| eni.updateEC2AdapterLimitViaAPI | bool | `false` | Update ENI Adapter limits from the EC2 API |
|
||||
| etcd.clusterDomain | string | `"cluster.local"` | Cluster domain for cilium-etcd-operator. |
|
||||
| etcd.enabled | bool | `false` | Enable etcd mode for the agent. |
|
||||
| etcd.endpoints | list | `["https://CHANGE-ME:2379"]` | List of etcd endpoints (not needed when using managed=true). |
|
||||
| etcd.extraArgs | list | `[]` | Additional cilium-etcd-operator container arguments. |
|
||||
| etcd.image | object | `{"override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium-etcd-operator","tag":"v2.0.7@sha256:04b8327f7f992693c2cb483b999041ed8f92efc8e14f2a5f3ab95574a65ea2dc"}` | cilium-etcd-operator image. |
|
||||
| etcd.k8sService | bool | `false` | If etcd is behind a k8s service set this option to true so that Cilium does the service translation automatically without requiring a DNS to be running. |
|
||||
| etcd.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for cilium-etcd-operator pod assignment ref: https://kubernetes.io/docs/user-guide/node-selection/ |
|
||||
| etcd.podAnnotations | object | `{}` | Annotations to be added to cilium-etcd-operator pods |
|
||||
| etcd.podDisruptionBudget.enabled | bool | `false` | enable PodDisruptionBudget ref: https://kubernetes.io/docs/concepts/workloads/pods/disruptions/ |
|
||||
| etcd.podDisruptionBudget.maxUnavailable | int | `1` | Maximum number/percentage of pods that may be made unavailable |
|
||||
| etcd.podDisruptionBudget.minAvailable | string | `nil` | Minimum number/percentage of pods that should remain scheduled. When it's set, maxUnavailable must be disabled by `maxUnavailable: null` |
|
||||
| etcd.podLabels | object | `{}` | Labels to be added to cilium-etcd-operator pods |
|
||||
| etcd.priorityClassName | string | `""` | The priority class to use for cilium-etcd-operator |
|
||||
| etcd.resources | object | `{}` | cilium-etcd-operator resource limits & requests ref: https://kubernetes.io/docs/user-guide/compute-resources/ |
|
||||
| etcd.securityContext | object | `{}` | Security context to be added to cilium-etcd-operator pods |
|
||||
| etcd.ssl | bool | `false` | Enable use of TLS/SSL for connectivity to etcd. (auto-enabled if managed=true) |
|
||||
| etcd.tolerations | list | `[{"operator":"Exists"}]` | Node tolerations for cilium-etcd-operator scheduling to nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| etcd.updateStrategy | object | `{"rollingUpdate":{"maxSurge":1,"maxUnavailable":1},"type":"RollingUpdate"}` | cilium-etcd-operator update strategy |
|
||||
| externalIPs.enabled | bool | `false` | Enable ExternalIPs service support. |
|
||||
| externalWorkloads | object | `{"enabled":false}` | Configure external workloads support |
|
||||
| externalWorkloads.enabled | bool | `false` | Enable support for external workloads, such as VMs (false by default). |
|
||||
| extraArgs | list | `[]` | Additional agent container arguments. |
|
||||
| extraConfig | object | `{}` | extraConfig allows you to specify additional configuration parameters to be included in the cilium-config configmap. |
|
||||
| extraEnv | list | `[]` | Additional agent container environment variables. |
|
||||
| extraHostPathMounts | list | `[]` | Additional agent hostPath mounts. |
|
||||
| extraVolumeMounts | list | `[]` | Additional agent volumeMounts. |
|
||||
| extraVolumes | list | `[]` | Additional agent volumes. |
|
||||
| gke.enabled | bool | `false` | Enable Google Kubernetes Engine integration |
|
||||
| healthChecking | bool | `true` | Enable connectivity health checking. |
|
||||
| healthPort | int | `9879` | TCP port for the agent health API. This is not the port for cilium-health. |
|
||||
| hostFirewall | object | `{"enabled":false}` | Configure the host firewall. |
|
||||
| hostFirewall.enabled | bool | `false` | Enables the enforcement of host policies in the eBPF datapath. |
|
||||
| hostPort.enabled | bool | `false` | Enable hostPort service support. |
|
||||
| hubble.enabled | bool | `true` | Enable Hubble (true by default). |
|
||||
| hubble.listenAddress | string | `":4244"` | An additional address for Hubble to listen to. Set this field ":4244" if you are enabling Hubble Relay, as it assumes that Hubble is listening on port 4244. |
|
||||
| hubble.metrics | object | `{"enabled":null,"port":9965,"serviceAnnotations":{},"serviceMonitor":{"annotations":{},"enabled":false,"labels":{}}}` | Hubble metrics configuration. See https://docs.cilium.io/en/stable/operations/metrics/#hubble-metrics for more comprehensive documentation about Hubble metrics. |
|
||||
| hubble.metrics.enabled | string | `nil` | Configures the list of metrics to collect. If empty or null, metrics are disabled. Example: enabled: - dns:query;ignoreAAAA - drop - tcp - flow - icmp - http You can specify the list of metrics from the helm CLI: --set metrics.enabled="{dns:query;ignoreAAAA,drop,tcp,flow,icmp,http}" |
|
||||
| hubble.metrics.port | int | `9965` | Configure the port the hubble metric server listens on. |
|
||||
| hubble.metrics.serviceAnnotations | object | `{}` | Annotations to be added to hubble-metrics service. |
|
||||
| hubble.metrics.serviceMonitor.annotations | object | `{}` | Annotations to add to ServiceMonitor hubble |
|
||||
| hubble.metrics.serviceMonitor.enabled | bool | `false` | Create ServiceMonitor resources for Prometheus Operator. This requires the prometheus CRDs to be available. ref: https://github.com/prometheus-operator/prometheus-operator/blob/master/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml) |
|
||||
| hubble.metrics.serviceMonitor.labels | object | `{}` | Labels to add to ServiceMonitor hubble |
|
||||
| hubble.peerService.clusterDomain | string | `"cluster.local"` | The cluster domain to use to query the Hubble Peer service. It should be the local cluster. |
|
||||
| hubble.peerService.enabled | bool | `true` | Enable a K8s Service for the Peer service, so that it can be accessed by a non-local client |
|
||||
| hubble.peerService.targetPort | int | `4244` | Target Port for the Peer service. |
|
||||
| hubble.relay.affinity | object | `{"podAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"k8s-app":"cilium"}},"topologyKey":"kubernetes.io/hostname"}]}}` | Affinity for hubble-replay |
|
||||
| hubble.relay.dialTimeout | string | `nil` | Dial timeout to connect to the local hubble instance to receive peer information (e.g. "30s"). |
|
||||
| hubble.relay.enabled | bool | `false` | Enable Hubble Relay (requires hubble.enabled=true) |
|
||||
| hubble.relay.extraEnv | list | `[]` | Additional hubble-relay environment variables. |
|
||||
| hubble.relay.image | object | `{"digest":"sha256:ca8033ea8a3112d838f958862fa76c8d895e3c8d0f5590de849b91745af5ac4d","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-relay","tag":"v1.12.0","useDigest":true}` | Hubble-relay container image. |
|
||||
| hubble.relay.listenHost | string | `""` | Host to listen to. Specify an empty string to bind to all the interfaces. |
|
||||
| hubble.relay.listenPort | string | `"4245"` | Port to listen to. |
|
||||
| hubble.relay.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for pod assignment ref: https://kubernetes.io/docs/user-guide/node-selection/ |
|
||||
| hubble.relay.podAnnotations | object | `{}` | Annotations to be added to hubble-relay pods |
|
||||
| hubble.relay.podDisruptionBudget.enabled | bool | `false` | enable PodDisruptionBudget ref: https://kubernetes.io/docs/concepts/workloads/pods/disruptions/ |
|
||||
| hubble.relay.podDisruptionBudget.maxUnavailable | int | `1` | Maximum number/percentage of pods that may be made unavailable |
|
||||
| hubble.relay.podDisruptionBudget.minAvailable | string | `nil` | Minimum number/percentage of pods that should remain scheduled. When it's set, maxUnavailable must be disabled by `maxUnavailable: null` |
|
||||
| hubble.relay.podLabels | object | `{}` | Labels to be added to hubble-relay pods |
|
||||
| hubble.relay.priorityClassName | string | `""` | The priority class to use for hubble-relay |
|
||||
| hubble.relay.prometheus | object | `{"enabled":false,"port":9966,"serviceMonitor":{"annotations":{},"enabled":false,"interval":"10s","labels":{}}}` | Enable prometheus metrics for hubble-relay on the configured port at /metrics |
|
||||
| hubble.relay.prometheus.serviceMonitor.annotations | object | `{}` | Annotations to add to ServiceMonitor hubble-relay |
|
||||
| hubble.relay.prometheus.serviceMonitor.enabled | bool | `false` | Enable service monitors. This requires the prometheus CRDs to be available (see https://github.com/prometheus-operator/prometheus-operator/blob/master/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml) |
|
||||
| hubble.relay.prometheus.serviceMonitor.interval | string | `"10s"` | Interval for scrape metrics. |
|
||||
| hubble.relay.prometheus.serviceMonitor.labels | object | `{}` | Labels to add to ServiceMonitor hubble-relay |
|
||||
| hubble.relay.replicas | int | `1` | Number of replicas run for the hubble-relay deployment. |
|
||||
| hubble.relay.resources | object | `{}` | Specifies the resources for the hubble-relay pods |
|
||||
| hubble.relay.retryTimeout | string | `nil` | Backoff duration to retry connecting to the local hubble instance in case of failure (e.g. "30s"). |
|
||||
| hubble.relay.rollOutPods | bool | `false` | Roll out Hubble Relay pods automatically when configmap is updated. |
|
||||
| hubble.relay.securityContext | object | `{}` | hubble-relay security context |
|
||||
| hubble.relay.service | object | `{"nodePort":31234,"type":"ClusterIP"}` | hubble-relay service configuration. |
|
||||
| hubble.relay.service.nodePort | int | `31234` | - The port to use when the service type is set to NodePort. |
|
||||
| hubble.relay.service.type | string | `"ClusterIP"` | - The type of service used for Hubble Relay access, either ClusterIP or NodePort. |
|
||||
| hubble.relay.sortBufferDrainTimeout | string | `nil` | When the per-request flows sort buffer is not full, a flow is drained every time this timeout is reached (only affects requests in follow-mode) (e.g. "1s"). |
|
||||
| hubble.relay.sortBufferLenMax | string | `nil` | Max number of flows that can be buffered for sorting before being sent to the client (per request) (e.g. 100). |
|
||||
| hubble.relay.terminationGracePeriodSeconds | int | `1` | Configure termination grace period for hubble relay Deployment. |
|
||||
| hubble.relay.tls | object | `{"client":{"cert":"","key":""},"server":{"cert":"","enabled":false,"extraDnsNames":[],"extraIpAddresses":[],"key":""}}` | TLS configuration for Hubble Relay |
|
||||
| hubble.relay.tls.client | object | `{"cert":"","key":""}` | base64 encoded PEM values for the hubble-relay client certificate and private key This keypair is presented to Hubble server instances for mTLS authentication and is required when hubble.tls.enabled is true. These values need to be set manually if hubble.tls.auto.enabled is false. |
|
||||
| hubble.relay.tls.server | object | `{"cert":"","enabled":false,"extraDnsNames":[],"extraIpAddresses":[],"key":""}` | base64 encoded PEM values for the hubble-relay server certificate and private key |
|
||||
| hubble.relay.tls.server.extraDnsNames | list | `[]` | extra DNS names added to certificate when its auto gen |
|
||||
| hubble.relay.tls.server.extraIpAddresses | list | `[]` | extra IP addresses added to certificate when its auto gen |
|
||||
| hubble.relay.tolerations | list | `[]` | Node tolerations for pod assignment on nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| hubble.relay.updateStrategy | object | `{"rollingUpdate":{"maxUnavailable":1},"type":"RollingUpdate"}` | hubble-relay update strategy |
|
||||
| hubble.socketPath | string | `"/var/run/cilium/hubble.sock"` | Unix domain socket path to listen to when Hubble is enabled. |
|
||||
| hubble.tls | object | `{"auto":{"certManagerIssuerRef":{},"certValidityDuration":1095,"enabled":true,"method":"helm","schedule":"0 0 1 */4 *"},"ca":{"cert":"","key":""},"enabled":true,"server":{"cert":"","extraDnsNames":[],"extraIpAddresses":[],"key":""}}` | TLS configuration for Hubble |
|
||||
| hubble.tls.auto | object | `{"certManagerIssuerRef":{},"certValidityDuration":1095,"enabled":true,"method":"helm","schedule":"0 0 1 */4 *"}` | Configure automatic TLS certificates generation. |
|
||||
| hubble.tls.auto.certManagerIssuerRef | object | `{}` | certmanager issuer used when hubble.tls.auto.method=certmanager. If not specified, a CA issuer will be created. |
|
||||
| hubble.tls.auto.certValidityDuration | int | `1095` | Generated certificates validity duration in days. |
|
||||
| hubble.tls.auto.enabled | bool | `true` | Auto-generate certificates. When set to true, automatically generate a CA and certificates to enable mTLS between Hubble server and Hubble Relay instances. If set to false, the certs for Hubble server need to be provided by setting appropriate values below. |
|
||||
| hubble.tls.auto.method | string | `"helm"` | Set the method to auto-generate certificates. Supported values: - helm: This method uses Helm to generate all certificates. - cronJob: This method uses a Kubernetes CronJob the generate any certificates not provided by the user at installation time. - certmanager: This method use cert-manager to generate & rotate certificates. |
|
||||
| hubble.tls.auto.schedule | string | `"0 0 1 */4 *"` | Schedule for certificates regeneration (regardless of their expiration date). Only used if method is "cronJob". If nil, then no recurring job will be created. Instead, only the one-shot job is deployed to generate the certificates at installation time. Defaults to midnight of the first day of every fourth month. For syntax, see https://kubernetes.io/docs/tasks/job/automated-tasks-with-cron-jobs/#schedule |
|
||||
| hubble.tls.ca | object | `{"cert":"","key":""}` | Deprecated in favor of tls.ca. To be removed in 1.13. base64 encoded PEM values for the Hubble CA certificate and private key. |
|
||||
| hubble.tls.ca.cert | string | `""` | Deprecated in favor of tls.ca.cert. To be removed in 1.13. |
|
||||
| hubble.tls.ca.key | string | `""` | Deprecated in favor of tls.ca.key. To be removed in 1.13. The CA private key (optional). If it is provided, then it will be used by hubble.tls.auto.method=cronJob to generate all other certificates. Otherwise, a ephemeral CA is generated if hubble.tls.auto.enabled=true. |
|
||||
| hubble.tls.enabled | bool | `true` | Enable mutual TLS for listenAddress. Setting this value to false is highly discouraged as the Hubble API provides access to potentially sensitive network flow metadata and is exposed on the host network. |
|
||||
| hubble.tls.server | object | `{"cert":"","extraDnsNames":[],"extraIpAddresses":[],"key":""}` | base64 encoded PEM values for the Hubble server certificate and private key |
|
||||
| hubble.tls.server.extraDnsNames | list | `[]` | Extra DNS names added to certificate when it's auto generated |
|
||||
| hubble.tls.server.extraIpAddresses | list | `[]` | Extra IP addresses added to certificate when it's auto generated |
|
||||
| hubble.ui.affinity | object | `{}` | Affinity for hubble-ui |
|
||||
| hubble.ui.backend.extraEnv | list | `[]` | Additional hubble-ui backend environment variables. |
|
||||
| hubble.ui.backend.image | object | `{"override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-ui-backend","tag":"v0.9.0@sha256:000df6b76719f607a9edefb9af94dfd1811a6f1b6a8a9c537cba90bf12df474b"}` | Hubble-ui backend image. |
|
||||
| hubble.ui.backend.resources | object | `{}` | Resource requests and limits for the 'backend' container of the 'hubble-ui' deployment. |
|
||||
| hubble.ui.enabled | bool | `false` | Whether to enable the Hubble UI. |
|
||||
| hubble.ui.frontend.extraEnv | list | `[]` | Additional hubble-ui frontend environment variables. |
|
||||
| hubble.ui.frontend.image | object | `{"override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-ui","tag":"v0.9.0@sha256:0ef04e9a29212925da6bdfd0ba5b581765e41a01f1cc30563cef9b30b457fea0"}` | Hubble-ui frontend image. |
|
||||
| hubble.ui.frontend.resources | object | `{}` | Resource requests and limits for the 'frontend' container of the 'hubble-ui' deployment. |
|
||||
| hubble.ui.ingress | object | `{"annotations":{},"className":"","enabled":false,"hosts":["chart-example.local"],"tls":[]}` | hubble-ui ingress configuration. |
|
||||
| hubble.ui.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for pod assignment ref: https://kubernetes.io/docs/user-guide/node-selection/ |
|
||||
| hubble.ui.podAnnotations | object | `{}` | Annotations to be added to hubble-ui pods |
|
||||
| hubble.ui.podDisruptionBudget.enabled | bool | `false` | enable PodDisruptionBudget ref: https://kubernetes.io/docs/concepts/workloads/pods/disruptions/ |
|
||||
| hubble.ui.podDisruptionBudget.maxUnavailable | int | `1` | Maximum number/percentage of pods that may be made unavailable |
|
||||
| hubble.ui.podDisruptionBudget.minAvailable | string | `nil` | Minimum number/percentage of pods that should remain scheduled. When it's set, maxUnavailable must be disabled by `maxUnavailable: null` |
|
||||
| hubble.ui.podLabels | object | `{}` | Labels to be added to hubble-ui pods |
|
||||
| hubble.ui.priorityClassName | string | `""` | The priority class to use for hubble-ui |
|
||||
| hubble.ui.replicas | int | `1` | The number of replicas of Hubble UI to deploy. |
|
||||
| hubble.ui.rollOutPods | bool | `false` | Roll out Hubble-ui pods automatically when configmap is updated. |
|
||||
| hubble.ui.securityContext | object | `{"enabled":true,"fsGroup":1001,"runAsGroup":1001,"runAsUser":1001}` | Security context to be added to Hubble UI pods |
|
||||
| hubble.ui.securityContext.enabled | bool | `true` | Deprecated in favor of hubble.ui.securityContext. Whether to set the security context on the Hubble UI pods. |
|
||||
| hubble.ui.service | object | `{"nodePort":31235,"type":"ClusterIP"}` | hubble-ui service configuration. |
|
||||
| hubble.ui.service.nodePort | int | `31235` | - The port to use when the service type is set to NodePort. |
|
||||
| hubble.ui.service.type | string | `"ClusterIP"` | - The type of service used for Hubble UI access, either ClusterIP or NodePort. |
|
||||
| hubble.ui.standalone.enabled | bool | `false` | When true, it will allow installing the Hubble UI only, without checking dependencies. It is useful if a cluster already has cilium and Hubble relay installed and you just want Hubble UI to be deployed. When installed via helm, installing UI should be done via `helm upgrade` and when installed via the cilium cli, then `cilium hubble enable --ui` |
|
||||
| hubble.ui.standalone.tls.certsVolume | object | `{}` | When deploying Hubble UI in standalone, with tls enabled for Hubble relay, it is required to provide a volume for mounting the client certificates. |
|
||||
| hubble.ui.tls.client | object | `{"cert":"","key":""}` | base64 encoded PEM values used to connect to hubble-relay This keypair is presented to Hubble Relay instances for mTLS authentication and is required when hubble.relay.tls.server.enabled is true. These values need to be set manually if hubble.tls.auto.enabled is false. |
|
||||
| hubble.ui.tolerations | list | `[]` | Node tolerations for pod assignment on nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| hubble.ui.updateStrategy | object | `{"rollingUpdate":{"maxUnavailable":1},"type":"RollingUpdate"}` | hubble-ui update strategy. |
|
||||
| identityAllocationMode | string | `"crd"` | Method to use for identity allocation (`crd` or `kvstore`). |
|
||||
| image | object | `{"digest":"sha256:079baa4fa1b9fe638f96084f4e0297c84dd4fb215d29d2321dcbe54273f63ade","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium","tag":"v1.12.0","useDigest":true}` | Agent container image. |
|
||||
| imagePullSecrets | string | `nil` | Configure image pull secrets for pulling container images |
|
||||
| ingressController.enabled | bool | `false` | Enable cilium ingress controller This will automatically set enable-envoy-config as well. |
|
||||
| ingressController.enforceHttps | bool | `true` | Enforce https for host having matching TLS host in Ingress. Incoming traffic to http listener will return 308 http error code with respective location in header. |
|
||||
| ingressController.secretsNamespace | object | `{"create":true,"name":"cilium-secrets","sync":true}` | SecretsNamespace is the namespace in which envoy SDS will retrieve TLS secrets from. |
|
||||
| ingressController.secretsNamespace.create | bool | `true` | Create secrets namespace for Ingress. |
|
||||
| ingressController.secretsNamespace.name | string | `"cilium-secrets"` | Name of Ingress secret namespace. |
|
||||
| ingressController.secretsNamespace.sync | bool | `true` | Enable secret sync, which will make sure all TLS secrets used by Ingress are synced to secretsNamespace.name. If disabled, TLS secrets must be maintained externally. |
|
||||
| installIptablesRules | bool | `true` | Configure whether to install iptables rules to allow for TPROXY (L7 proxy injection), iptables-based masquerading and compatibility with kube-proxy. |
|
||||
| installNoConntrackIptablesRules | bool | `false` | Install Iptables rules to skip netfilter connection tracking on all pod traffic. This option is only effective when Cilium is running in direct routing and full KPR mode. Moreover, this option cannot be enabled when Cilium is running in a managed Kubernetes environment or in a chained CNI setup. |
|
||||
| ipMasqAgent | object | `{"enabled":false}` | Configure the eBPF-based ip-masq-agent |
|
||||
| ipam.mode | string | `"cluster-pool"` | Configure IP Address Management mode. ref: https://docs.cilium.io/en/stable/concepts/networking/ipam/ |
|
||||
| ipam.operator.clusterPoolIPv4MaskSize | int | `24` | IPv4 CIDR mask size to delegate to individual nodes for IPAM. |
|
||||
| ipam.operator.clusterPoolIPv4PodCIDR | string | `"10.0.0.0/8"` | Deprecated in favor of ipam.operator.clusterPoolIPv4PodCIDRList. IPv4 CIDR range to delegate to individual nodes for IPAM. |
|
||||
| ipam.operator.clusterPoolIPv4PodCIDRList | list | `[]` | IPv4 CIDR list range to delegate to individual nodes for IPAM. |
|
||||
| ipam.operator.clusterPoolIPv6MaskSize | int | `120` | IPv6 CIDR mask size to delegate to individual nodes for IPAM. |
|
||||
| ipam.operator.clusterPoolIPv6PodCIDR | string | `"fd00::/104"` | Deprecated in favor of ipam.operator.clusterPoolIPv6PodCIDRList. IPv6 CIDR range to delegate to individual nodes for IPAM. |
|
||||
| ipam.operator.clusterPoolIPv6PodCIDRList | list | `[]` | IPv6 CIDR list range to delegate to individual nodes for IPAM. |
|
||||
| ipv4.enabled | bool | `true` | Enable IPv4 support. |
|
||||
| ipv6.enabled | bool | `false` | Enable IPv6 support. |
|
||||
| ipvlan.enabled | bool | `false` | Enable the IPVLAN datapath (deprecated) |
|
||||
| k8s | object | `{}` | Configure Kubernetes specific configuration |
|
||||
| keepDeprecatedLabels | bool | `false` | Keep the deprecated selector labels when deploying Cilium DaemonSet. |
|
||||
| keepDeprecatedProbes | bool | `false` | Keep the deprecated probes when deploying Cilium DaemonSet |
|
||||
| kubeProxyReplacementHealthzBindAddr | string | `""` | healthz server bind address for the kube-proxy replacement. To enable set the value to '0.0.0.0:10256' for all ipv4 addresses and this '[::]:10256' for all ipv6 addresses. By default it is disabled. |
|
||||
| l2NeighDiscovery.enabled | bool | `true` | Enable L2 neighbor discovery in the agent |
|
||||
| l2NeighDiscovery.refreshPeriod | string | `"30s"` | Override the agent's default neighbor resolution refresh period. |
|
||||
| l7Proxy | bool | `true` | Enable Layer 7 network policy. |
|
||||
| livenessProbe.failureThreshold | int | `10` | failure threshold of liveness probe |
|
||||
| livenessProbe.periodSeconds | int | `30` | interval between checks of the liveness probe |
|
||||
| localRedirectPolicy | bool | `false` | Enable Local Redirect Policy. |
|
||||
| logSystemLoad | bool | `false` | Enables periodic logging of system load |
|
||||
| maglev | object | `{}` | Configure maglev consistent hashing |
|
||||
| monitor | object | `{"enabled":false}` | cilium-monitor sidecar. |
|
||||
| monitor.enabled | bool | `false` | Enable the cilium-monitor sidecar. |
|
||||
| name | string | `"cilium"` | Agent container name. |
|
||||
| nodePort | object | `{"autoProtectPortRange":true,"bindProtection":true,"enableHealthCheck":true,"enabled":false}` | Configure N-S k8s service loadbalancing |
|
||||
| nodePort.autoProtectPortRange | bool | `true` | Append NodePort range to ip_local_reserved_ports if clash with ephemeral ports is detected. |
|
||||
| nodePort.bindProtection | bool | `true` | Set to true to prevent applications binding to service ports. |
|
||||
| nodePort.enableHealthCheck | bool | `true` | Enable healthcheck nodePort server for NodePort services |
|
||||
| nodePort.enabled | bool | `false` | Enable the Cilium NodePort service implementation. |
|
||||
| nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node selector for cilium-agent. |
|
||||
| nodeinit.affinity | object | `{}` | Affinity for cilium-nodeinit |
|
||||
| nodeinit.bootstrapFile | string | `"/tmp/cilium-bootstrap.d/cilium-bootstrap-time"` | bootstrapFile is the location of the file where the bootstrap timestamp is written by the node-init DaemonSet |
|
||||
| nodeinit.enabled | bool | `false` | Enable the node initialization DaemonSet |
|
||||
| nodeinit.extraEnv | list | `[]` | Additional nodeinit environment variables. |
|
||||
| nodeinit.image | object | `{"override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/startup-script","tag":"d69851597ea019af980891a4628fb36b7880ec26"}` | node-init image. |
|
||||
| nodeinit.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for nodeinit pod assignment ref: https://kubernetes.io/docs/user-guide/node-selection/ |
|
||||
| nodeinit.podAnnotations | object | `{}` | Annotations to be added to node-init pods. |
|
||||
| nodeinit.podLabels | object | `{}` | Labels to be added to node-init pods. |
|
||||
| nodeinit.priorityClassName | string | `""` | The priority class to use for the nodeinit pod. |
|
||||
| nodeinit.resources | object | `{"requests":{"cpu":"100m","memory":"100Mi"}}` | nodeinit resource limits & requests ref: https://kubernetes.io/docs/user-guide/compute-resources/ |
|
||||
| nodeinit.securityContext | object | `{"capabilities":{"add":["SYS_MODULE","NET_ADMIN","SYS_ADMIN","SYS_CHROOT","SYS_PTRACE"]},"privileged":false,"seLinuxOptions":{"level":"s0","type":"spc_t"}}` | Security context to be added to nodeinit pods. |
|
||||
| nodeinit.tolerations | list | `[{"operator":"Exists"}]` | Node tolerations for nodeinit scheduling to nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| nodeinit.updateStrategy | object | `{"type":"RollingUpdate"}` | node-init update strategy |
|
||||
| operator.affinity | object | `{"podAntiAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"io.cilium/app":"operator"}},"topologyKey":"kubernetes.io/hostname"}]}}` | Affinity for cilium-operator |
|
||||
| operator.dnsPolicy | string | `""` | DNS policy for Cilium operator pods. Ref: https://kubernetes.io/docs/concepts/services-networking/dns-pod-service/#pod-s-dns-policy |
|
||||
| operator.enabled | bool | `true` | Enable the cilium-operator component (required). |
|
||||
| operator.endpointGCInterval | string | `"5m0s"` | Interval for endpoint garbage collection. |
|
||||
| operator.extraArgs | list | `[]` | Additional cilium-operator container arguments. |
|
||||
| operator.extraEnv | list | `[]` | Additional cilium-operator environment variables. |
|
||||
| operator.extraHostPathMounts | list | `[]` | Additional cilium-operator hostPath mounts. |
|
||||
| operator.extraVolumeMounts | list | `[]` | Additional cilium-operator volumeMounts. |
|
||||
| operator.extraVolumes | list | `[]` | Additional cilium-operator volumes. |
|
||||
| operator.identityGCInterval | string | `"15m0s"` | Interval for identity garbage collection. |
|
||||
| operator.identityHeartbeatTimeout | string | `"30m0s"` | Timeout for identity heartbeats. |
|
||||
| operator.image | object | `{"alibabacloudDigest":"sha256:93dddf88e92119a141a913b44ab9cb909f19b9a7bf01e30b98c1e8afeec51cd5","awsDigest":"sha256:cb73df18b03b4fc914c80045d0ddb6c9256972449382e3c4b294fd9c371ace22","azureDigest":"sha256:98ffa2c8ebff33d4e91762fb57d4c36f152bb044c4e2141e15362cf95ecc24ba","genericDigest":"sha256:bb2a42eda766e5d4a87ee8a5433f089db81b72dd04acf6b59fcbb445a95f9410","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/operator","suffix":"","tag":"v1.12.0","useDigest":true}` | cilium-operator image. |
|
||||
| operator.nodeGCInterval | string | `"5m0s"` | Interval for cilium node garbage collection. |
|
||||
| operator.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for cilium-operator pod assignment ref: https://kubernetes.io/docs/user-guide/node-selection/ |
|
||||
| operator.podAnnotations | object | `{}` | Annotations to be added to cilium-operator pods |
|
||||
| operator.podDisruptionBudget.enabled | bool | `false` | enable PodDisruptionBudget ref: https://kubernetes.io/docs/concepts/workloads/pods/disruptions/ |
|
||||
| operator.podDisruptionBudget.maxUnavailable | int | `1` | Maximum number/percentage of pods that may be made unavailable |
|
||||
| operator.podDisruptionBudget.minAvailable | string | `nil` | Minimum number/percentage of pods that should remain scheduled. When it's set, maxUnavailable must be disabled by `maxUnavailable: null` |
|
||||
| operator.podLabels | object | `{}` | Labels to be added to cilium-operator pods |
|
||||
| operator.priorityClassName | string | `""` | The priority class to use for cilium-operator |
|
||||
| operator.prometheus | object | `{"enabled":false,"port":9963,"serviceMonitor":{"annotations":{},"enabled":false,"labels":{}}}` | Enable prometheus metrics for cilium-operator on the configured port at /metrics |
|
||||
| operator.prometheus.serviceMonitor.annotations | object | `{}` | Annotations to add to ServiceMonitor cilium-operator |
|
||||
| operator.prometheus.serviceMonitor.enabled | bool | `false` | Enable service monitors. This requires the prometheus CRDs to be available (see https://github.com/prometheus-operator/prometheus-operator/blob/master/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml) |
|
||||
| operator.prometheus.serviceMonitor.labels | object | `{}` | Labels to add to ServiceMonitor cilium-operator |
|
||||
| operator.removeNodeTaints | bool | `true` | Remove Cilium node taint from Kubernetes nodes that have a healthy Cilium pod running. |
|
||||
| operator.replicas | int | `2` | Number of replicas to run for the cilium-operator deployment |
|
||||
| operator.resources | object | `{}` | cilium-operator resource limits & requests ref: https://kubernetes.io/docs/user-guide/compute-resources/ |
|
||||
| operator.rollOutPods | bool | `false` | Roll out cilium-operator pods automatically when configmap is updated. |
|
||||
| operator.securityContext | object | `{}` | Security context to be added to cilium-operator pods |
|
||||
| operator.setNodeNetworkStatus | bool | `true` | Set Node condition NetworkUnavailable to 'false' with the reason 'CiliumIsUp' for nodes that have a healthy Cilium pod. |
|
||||
| operator.skipCRDCreation | bool | `false` | Skip CRDs creation for cilium-operator |
|
||||
| operator.tolerations | list | `[{"operator":"Exists"}]` | Node tolerations for cilium-operator scheduling to nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| operator.unmanagedPodWatcher.intervalSeconds | int | `15` | Interval, in seconds, to check if there are any pods that are not managed by Cilium. |
|
||||
| operator.unmanagedPodWatcher.restart | bool | `true` | Restart any pod that are not managed by Cilium. |
|
||||
| operator.updateStrategy | object | `{"rollingUpdate":{"maxSurge":1,"maxUnavailable":1},"type":"RollingUpdate"}` | cilium-operator update strategy |
|
||||
| podAnnotations | object | `{}` | Annotations to be added to agent pods |
|
||||
| podLabels | object | `{}` | Labels to be added to agent pods |
|
||||
| policyEnforcementMode | string | `"default"` | The agent can be put into one of the three policy enforcement modes: default, always and never. ref: https://docs.cilium.io/en/stable/policy/intro/#policy-enforcement-modes |
|
||||
| pprof.enabled | bool | `false` | Enable Go pprof debugging |
|
||||
| preflight.affinity | object | `{"podAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"k8s-app":"cilium"}},"topologyKey":"kubernetes.io/hostname"}]}}` | Affinity for cilium-preflight |
|
||||
| preflight.enabled | bool | `false` | Enable Cilium pre-flight resources (required for upgrade) |
|
||||
| preflight.extraEnv | list | `[]` | Additional preflight environment variables. |
|
||||
| preflight.image | object | `{"digest":"sha256:079baa4fa1b9fe638f96084f4e0297c84dd4fb215d29d2321dcbe54273f63ade","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium","tag":"v1.12.0","useDigest":true}` | Cilium pre-flight image. |
|
||||
| preflight.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for preflight pod assignment ref: https://kubernetes.io/docs/user-guide/node-selection/ |
|
||||
| preflight.podAnnotations | object | `{}` | Annotations to be added to preflight pods |
|
||||
| preflight.podDisruptionBudget.enabled | bool | `false` | enable PodDisruptionBudget ref: https://kubernetes.io/docs/concepts/workloads/pods/disruptions/ |
|
||||
| preflight.podDisruptionBudget.maxUnavailable | int | `1` | Maximum number/percentage of pods that may be made unavailable |
|
||||
| preflight.podDisruptionBudget.minAvailable | string | `nil` | Minimum number/percentage of pods that should remain scheduled. When it's set, maxUnavailable must be disabled by `maxUnavailable: null` |
|
||||
| preflight.podLabels | object | `{}` | Labels to be added to the preflight pod. |
|
||||
| preflight.priorityClassName | string | `""` | The priority class to use for the preflight pod. |
|
||||
| preflight.resources | object | `{}` | preflight resource limits & requests ref: https://kubernetes.io/docs/user-guide/compute-resources/ |
|
||||
| preflight.securityContext | object | `{}` | Security context to be added to preflight pods |
|
||||
| preflight.terminationGracePeriodSeconds | int | `1` | Configure termination grace period for preflight Deployment and DaemonSet. |
|
||||
| preflight.tofqdnsPreCache | string | `""` | Path to write the `--tofqdns-pre-cache` file to. |
|
||||
| preflight.tolerations | list | `[{"effect":"NoSchedule","key":"node.kubernetes.io/not-ready"},{"effect":"NoSchedule","key":"node-role.kubernetes.io/master"},{"effect":"NoSchedule","key":"node.cloudprovider.kubernetes.io/uninitialized","value":"true"},{"key":"CriticalAddonsOnly","operator":"Exists"}]` | Node tolerations for preflight scheduling to nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| preflight.updateStrategy | object | `{"type":"RollingUpdate"}` | preflight update strategy |
|
||||
| preflight.validateCNPs | bool | `true` | By default we should always validate the installed CNPs before upgrading Cilium. This will make sure the user will have the policies deployed in the cluster with the right schema. |
|
||||
| priorityClassName | string | `""` | The priority class to use for cilium-agent. |
|
||||
| prometheus | object | `{"enabled":false,"metrics":null,"port":9962,"serviceMonitor":{"annotations":{},"enabled":false,"labels":{}}}` | Configure prometheus metrics on the configured port at /metrics |
|
||||
| prometheus.metrics | string | `nil` | Metrics that should be enabled or disabled from the default metric list. (+metric_foo to enable metric_foo , -metric_bar to disable metric_bar). ref: https://docs.cilium.io/en/stable/operations/metrics/#exported-metrics |
|
||||
| prometheus.serviceMonitor.annotations | object | `{}` | Annotations to add to ServiceMonitor cilium-agent |
|
||||
| prometheus.serviceMonitor.enabled | bool | `false` | Enable service monitors. This requires the prometheus CRDs to be available (see https://github.com/prometheus-operator/prometheus-operator/blob/master/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml) |
|
||||
| prometheus.serviceMonitor.labels | object | `{}` | Labels to add to ServiceMonitor cilium-agent |
|
||||
| proxy | object | `{"prometheus":{"enabled":true,"port":"9964"},"sidecarImageRegex":"cilium/istio_proxy"}` | Configure Istio proxy options. |
|
||||
| proxy.sidecarImageRegex | string | `"cilium/istio_proxy"` | Regular expression matching compatible Istio sidecar istio-proxy container image names |
|
||||
| rbac.create | bool | `true` | Enable creation of Resource-Based Access Control configuration. |
|
||||
| readinessProbe.failureThreshold | int | `3` | failure threshold of readiness probe |
|
||||
| readinessProbe.periodSeconds | int | `30` | interval between checks of the readiness probe |
|
||||
| remoteNodeIdentity | bool | `true` | Enable use of the remote node identity. ref: https://docs.cilium.io/en/v1.7/install/upgrade/#configmap-remote-node-identity |
|
||||
| resourceQuotas | object | `{"cilium":{"hard":{"pods":"10k"}},"enabled":false,"operator":{"hard":{"pods":"15"}}}` | Enable resource quotas for priority classes used in the cluster. |
|
||||
| resources | object | `{}` | Agent resource limits & requests ref: https://kubernetes.io/docs/user-guide/compute-resources/ |
|
||||
| rollOutCiliumPods | bool | `false` | Roll out cilium agent pods automatically when configmap is updated. |
|
||||
| securityContext | object | `{"extraCapabilities":["DAC_OVERRIDE","FOWNER","SETGID","SETUID"],"privileged":false}` | Security context to be added to agent pods |
|
||||
| serviceAccounts | object | Component's fully qualified name. | Define serviceAccount names for components. |
|
||||
| serviceAccounts.clustermeshcertgen | object | `{"annotations":{},"create":true,"name":"clustermesh-apiserver-generate-certs"}` | Clustermeshcertgen is used if clustermesh.apiserver.tls.auto.method=cronJob |
|
||||
| serviceAccounts.hubblecertgen | object | `{"annotations":{},"create":true,"name":"hubble-generate-certs"}` | Hubblecertgen is used if hubble.tls.auto.method=cronJob |
|
||||
| sleepAfterInit | bool | `false` | Do not run Cilium agent when running with clean mode. Useful to completely uninstall Cilium as it will stop Cilium from starting and create artifacts in the node. |
|
||||
| socketLB | object | `{"enabled":false}` | Configure socket LB |
|
||||
| socketLB.enabled | bool | `false` | Enable socket LB |
|
||||
| sockops | object | `{"enabled":false}` | Configure BPF socket operations configuration |
|
||||
| startupProbe.failureThreshold | int | `105` | failure threshold of startup probe. 105 x 2s translates to the old behaviour of the readiness probe (120s delay + 30 x 3s) |
|
||||
| startupProbe.periodSeconds | int | `2` | interval between checks of the startup probe |
|
||||
| svcSourceRangeCheck | bool | `true` | Enable check of service source ranges (currently, only for LoadBalancer). |
|
||||
| synchronizeK8sNodes | bool | `true` | Synchronize Kubernetes nodes to kvstore and perform CNP GC. |
|
||||
| terminationGracePeriodSeconds | int | `1` | Configure termination grace period for cilium-agent DaemonSet. |
|
||||
| tls | object | `{"ca":{"cert":"","certValidityDuration":1095,"key":""},"secretsBackend":"local"}` | Configure TLS configuration in the agent. |
|
||||
| tls.ca | object | `{"cert":"","certValidityDuration":1095,"key":""}` | Base64 encoded PEM values for the CA certificate and private key. This can be used as common CA to generate certificates used by hubble and clustermesh components |
|
||||
| tls.ca.cert | string | `""` | Optional CA cert. If it is provided, it will be used by cilium to generate all other certificates. Otherwise, an ephemeral CA is generated. |
|
||||
| tls.ca.certValidityDuration | int | `1095` | Generated certificates validity duration in days. This will be used for auto generated CA. |
|
||||
| tls.ca.key | string | `""` | Optional CA private key. If it is provided, it will be used by cilium to generate all other certificates. Otherwise, an ephemeral CA is generated. |
|
||||
| tls.secretsBackend | string | `"local"` | This configures how the Cilium agent loads the secrets used TLS-aware CiliumNetworkPolicies (namely the secrets referenced by terminatingTLS and originatingTLS). Possible values: - local - k8s |
|
||||
| tolerations | list | `[{"operator":"Exists"}]` | Node tolerations for agent scheduling to nodes with taints ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ |
|
||||
| tunnel | string | `"vxlan"` | Configure the encapsulation configuration for communication between nodes. Possible values: - disabled - vxlan (default) - geneve |
|
||||
| updateStrategy | object | `{"rollingUpdate":{"maxUnavailable":2},"type":"RollingUpdate"}` | Cilium agent update strategy |
|
||||
| vtep.cidr | string | `""` | A space separated list of VTEP device CIDRs, for example "1.1.1.0/24 1.1.2.0/24" |
|
||||
| vtep.enabled | bool | `false` | Enables VXLAN Tunnel Endpoint (VTEP) Integration (beta) to allow Cilium-managed pods to talk to third party VTEP devices over Cilium tunnel. |
|
||||
| vtep.endpoint | string | `""` | A space separated list of VTEP device endpoint IPs, for example "1.1.1.1 1.1.2.1" |
|
||||
| vtep.mac | string | `""` | A space separated list of VTEP device MAC addresses (VTEP MAC), for example "x:x:x:x:x:x y:y:y:y:y:y:y" |
|
||||
| vtep.mask | string | `""` | VTEP CIDRs Mask that applies to all VTEP CIDRs, for example "255.255.255.0" |
|
||||
| waitForKubeProxy | bool | `false` | Wait for KUBE-PROXY-CANARY iptables rule to appear in "wait-for-kube-proxy" init container before launching cilium-agent. More context can be found in the commit message of below PR https://github.com/cilium/cilium/pull/20123 |
|
||||
| wellKnownIdentities.enabled | bool | `false` | Enable the use of well-known identities. |
|
||||
54
cli/internal/helm/charts/cilium/README.md.gotmpl
Normal file
54
cli/internal/helm/charts/cilium/README.md.gotmpl
Normal file
@ -0,0 +1,54 @@
|
||||
{{ template "chart.header" . }}
|
||||
|
||||
{{ template "chart.deprecationWarning" . }}
|
||||
|
||||
{{ template "chart.versionBadge" . }}{{ template "chart.typeBadge" . }}{{ template "chart.appVersionBadge" . }}
|
||||
|
||||
Cilium is open source software for providing and transparently securing
|
||||
network connectivity and loadbalancing between application workloads such as
|
||||
application containers or processes. Cilium operates at Layer 3/4 to provide
|
||||
traditional networking and security services as well as Layer 7 to protect and
|
||||
secure use of modern application protocols such as HTTP, gRPC and Kafka.
|
||||
|
||||
A new Linux kernel technology called eBPF is at the foundation of Cilium.
|
||||
It supports dynamic insertion of eBPF bytecode into the Linux kernel at various
|
||||
integration points such as: network IO, application sockets, and tracepoints
|
||||
to implement security, networking and visibility logic. eBPF is highly
|
||||
efficient and flexible.
|
||||
|
||||
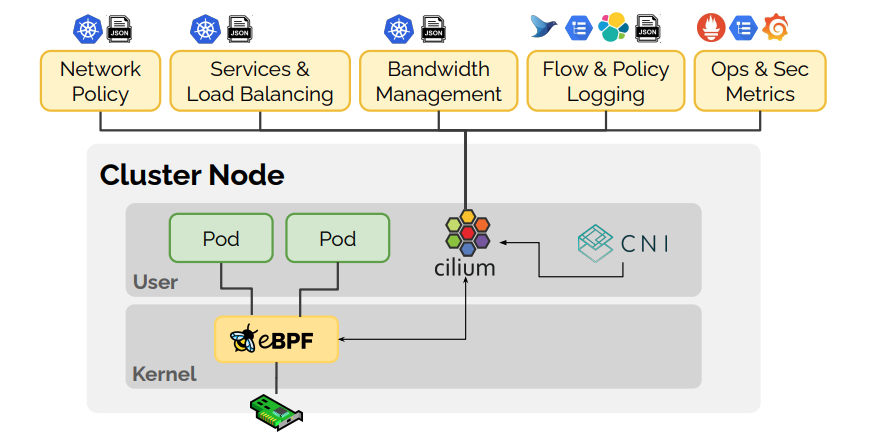
|
||||
|
||||
## Prerequisites
|
||||
|
||||
* Kubernetes: `{{ template "chart.kubeVersion" . }}`
|
||||
* Helm: `>= 3.0`
|
||||
|
||||
## Getting Started
|
||||
|
||||
Try Cilium on any Kubernetes distribution in under 15 minutes:
|
||||
|
||||
| Minikube | Self-Managed K8s | Amazon EKS | Google GKE | Microsoft AKS |
|
||||
|:-:|:-:|:-:|:-:|:-:|
|
||||
| [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) | [](https://docs.cilium.io/en/stable/gettingstarted/k8s-install-default/) |
|
||||
|
||||
Or, for a quick install with the default configuration:
|
||||
|
||||
```
|
||||
$ helm repo add cilium https://helm.cilium.io/
|
||||
$ helm install cilium cilium/cilium --namespace=kube-system
|
||||
```
|
||||
|
||||
After Cilium is installed, you can explore the features that Cilium has to
|
||||
offer from the [Getting Started Guides page](https://docs.cilium.io/en/latest/gettingstarted/).
|
||||
|
||||
{{ template "chart.maintainersSection" . }}
|
||||
|
||||
{{ template "chart.sourcesSection" . }}
|
||||
|
||||
## Getting Help
|
||||
|
||||
The best way to get help if you get stuck is to ask a question on the
|
||||
[Cilium Slack channel](https://cilium.herokuapp.com/). With Cilium
|
||||
contributors across the globe, there is almost always someone available to help.
|
||||
|
||||
{{ template "chart.valuesSection" . }}
|
||||
@ -0,0 +1,21 @@
|
||||
#!/bin/bash
|
||||
|
||||
set -o errexit
|
||||
set -o pipefail
|
||||
set -o nounset
|
||||
|
||||
# When running in AWS ENI mode, it's likely that 'aws-node' has
|
||||
# had a chance to install SNAT iptables rules. These can result
|
||||
# in dropped traffic, so we should attempt to remove them.
|
||||
# We do it using a 'postStart' hook since this may need to run
|
||||
# for nodes which might have already been init'ed but may still
|
||||
# have dangling rules. This is safe because there are no
|
||||
# dependencies on anything that is part of the startup script
|
||||
# itself, and can be safely run multiple times per node (e.g. in
|
||||
# case of a restart).
|
||||
if [[ "$(iptables-save | grep -c AWS-SNAT-CHAIN)" != "0" ]];
|
||||
then
|
||||
echo 'Deleting iptables rules created by the AWS CNI VPC plugin'
|
||||
iptables-save | grep -v AWS-SNAT-CHAIN | iptables-restore
|
||||
fi
|
||||
echo 'Done!'
|
||||
56
cli/internal/helm/charts/cilium/files/nodeinit/prestop.bash
Normal file
56
cli/internal/helm/charts/cilium/files/nodeinit/prestop.bash
Normal file
@ -0,0 +1,56 @@
|
||||
#!/bin/bash
|
||||
|
||||
set -o errexit
|
||||
set -o pipefail
|
||||
set -o nounset
|
||||
|
||||
if stat /tmp/node-deinit.cilium.io > /dev/null 2>&1; then
|
||||
exit 0
|
||||
fi
|
||||
|
||||
echo "Waiting on pods to stop..."
|
||||
if [ ! -f /etc/crictl.yaml ] || grep -q 'docker' /etc/crictl.yaml; then
|
||||
# Works for COS, ubuntu
|
||||
while docker ps | grep -v "node-init" | grep -q "POD_cilium"; do sleep 1; done
|
||||
else
|
||||
# COS-beta (with containerd). Some versions of COS have crictl in /home/kubernetes/bin.
|
||||
while PATH="${PATH}:/home/kubernetes/bin" crictl ps | grep -v "node-init" | grep -q "POD_cilium"; do sleep 1; done
|
||||
fi
|
||||
|
||||
if ip link show cilium_host; then
|
||||
echo "Deleting cilium_host interface..."
|
||||
ip link del cilium_host
|
||||
fi
|
||||
|
||||
{{- if not (eq .Values.nodeinit.bootstrapFile "") }}
|
||||
rm -f {{ .Values.nodeinit.bootstrapFile | quote }}
|
||||
{{- end }}
|
||||
|
||||
rm -f /tmp/node-init.cilium.io
|
||||
touch /tmp/node-deinit.cilium.io
|
||||
|
||||
{{- if .Values.nodeinit.reconfigureKubelet }}
|
||||
# Check if we're running on a GKE containerd flavor.
|
||||
GKE_KUBERNETES_BIN_DIR="/home/kubernetes/bin"
|
||||
if [[ -f "${GKE_KUBERNETES_BIN_DIR}/gke" ]] && command -v containerd &>/dev/null; then
|
||||
CONTAINERD_CONFIG="/etc/containerd/config.toml"
|
||||
echo "Reverting changes to the containerd configuration"
|
||||
sed -Ei "s/^\#(\s+conf_template)/\1/g" "${CONTAINERD_CONFIG}"
|
||||
echo "Removing the kubelet wrapper"
|
||||
[[ -f "${GKE_KUBERNETES_BIN_DIR}/the-kubelet" ]] && mv "${GKE_KUBERNETES_BIN_DIR}/the-kubelet" "${GKE_KUBERNETES_BIN_DIR}/kubelet"
|
||||
else
|
||||
echo "Changing kubelet configuration to --network-plugin=kubenet"
|
||||
sed -i "s:--network-plugin=cni\ --cni-bin-dir={{ .Values.cni.binPath }}:--network-plugin=kubenet:g" /etc/default/kubelet
|
||||
fi
|
||||
echo "Restarting the kubelet"
|
||||
systemctl restart kubelet
|
||||
{{- end }}
|
||||
|
||||
{{- if (and .Values.gke.enabled (or .Values.enableIPv4Masquerade .Values.gke.disableDefaultSnat))}}
|
||||
# If the IP-MASQ chain exists, add back default jump rule from the GKE instance configure script
|
||||
if iptables -w -t nat -L IP-MASQ > /dev/null; then
|
||||
iptables -w -t nat -A POSTROUTING -m comment --comment "ip-masq: ensure nat POSTROUTING directs all non-LOCAL destination traffic to our custom IP-MASQ chain" -m addrtype ! --dst-type LOCAL -j IP-MASQ
|
||||
fi
|
||||
{{- end }}
|
||||
|
||||
echo "Node de-initialization complete"
|
||||
168
cli/internal/helm/charts/cilium/files/nodeinit/startup.bash
Normal file
168
cli/internal/helm/charts/cilium/files/nodeinit/startup.bash
Normal file
@ -0,0 +1,168 @@
|
||||
#!/bin/bash
|
||||
|
||||
set -o errexit
|
||||
set -o pipefail
|
||||
set -o nounset
|
||||
|
||||
echo "Link information:"
|
||||
ip link
|
||||
|
||||
echo "Routing table:"
|
||||
ip route
|
||||
|
||||
echo "Addressing:"
|
||||
ip -4 a
|
||||
ip -6 a
|
||||
|
||||
{{- if .Values.nodeinit.removeCbrBridge }}
|
||||
if ip link show cbr0; then
|
||||
echo "Detected cbr0 bridge. Deleting interface..."
|
||||
ip link del cbr0
|
||||
fi
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.nodeinit.reconfigureKubelet }}
|
||||
# Check if we're running on a GKE containerd flavor as indicated by the presence
|
||||
# of the '--container-runtime-endpoint' flag in '/etc/default/kubelet'.
|
||||
GKE_KUBERNETES_BIN_DIR="/home/kubernetes/bin"
|
||||
KUBELET_DEFAULTS_FILE="/etc/default/kubelet"
|
||||
if [[ -f "${GKE_KUBERNETES_BIN_DIR}/gke" ]] && [[ $(grep -cF -- '--container-runtime-endpoint' "${KUBELET_DEFAULTS_FILE}") == "1" ]]; then
|
||||
echo "GKE *_containerd flavor detected..."
|
||||
|
||||
# (GKE *_containerd) Upon node restarts, GKE's containerd images seem to reset
|
||||
# the /etc directory and our changes to the kubelet and Cilium's CNI
|
||||
# configuration are removed. This leaves room for containerd and its CNI to
|
||||
# take over pods previously managed by Cilium, causing Cilium to lose
|
||||
# ownership over these pods. We rely on the empirical observation that
|
||||
# /home/kubernetes/bin/kubelet is not changed across node reboots, and replace
|
||||
# it with a wrapper script that performs some initialization steps when
|
||||
# required and then hands over control to the real kubelet.
|
||||
|
||||
# Only create the kubelet wrapper if we haven't previously done so.
|
||||
if [[ ! -f "${GKE_KUBERNETES_BIN_DIR}/the-kubelet" ]];
|
||||
then
|
||||
echo "Installing the kubelet wrapper..."
|
||||
|
||||
# Rename the real kubelet.
|
||||
mv "${GKE_KUBERNETES_BIN_DIR}/kubelet" "${GKE_KUBERNETES_BIN_DIR}/the-kubelet"
|
||||
|
||||
# Initialize the kubelet wrapper which lives in the place of the real kubelet.
|
||||
touch "${GKE_KUBERNETES_BIN_DIR}/kubelet"
|
||||
chmod a+x "${GKE_KUBERNETES_BIN_DIR}/kubelet"
|
||||
|
||||
# Populate the kubelet wrapper. It will perform the initialization steps we
|
||||
# need and then become the kubelet.
|
||||
cat <<'EOF' | tee "${GKE_KUBERNETES_BIN_DIR}/kubelet"
|
||||
#!/bin/bash
|
||||
|
||||
set -euo pipefail
|
||||
|
||||
CNI_CONF_DIR="/etc/cni/net.d"
|
||||
CONTAINERD_CONFIG="/etc/containerd/config.toml"
|
||||
|
||||
# Only stop and start containerd if the Cilium CNI configuration does not exist,
|
||||
# or if the 'conf_template' property is present in the containerd config file,
|
||||
# in order to avoid unnecessarily restarting containerd.
|
||||
if [[ -z "$(find "${CNI_CONF_DIR}" -type f -name '*cilium*')" || \
|
||||
"$(grep -cE '^\s+conf_template' "${CONTAINERD_CONFIG}")" != "0" ]];
|
||||
then
|
||||
# Stop containerd as it starts by creating a CNI configuration from a template
|
||||
# causing pods to start with IPs assigned by GKE's CNI.
|
||||
# 'disable --now' is used instead of stop as this script runs concurrently
|
||||
# with containerd on node startup, and hence containerd might not have been
|
||||
# started yet, in which case 'disable' prevents it from starting.
|
||||
echo "Disabling and stopping containerd"
|
||||
systemctl disable --now containerd
|
||||
|
||||
# Remove any pre-existing files in the CNI configuration directory. We skip
|
||||
# any possibly existing Cilium configuration file for the obvious reasons.
|
||||
echo "Removing undesired CNI configuration files"
|
||||
find "${CNI_CONF_DIR}" -type f -not -name '*cilium*' -exec rm {} \;
|
||||
|
||||
# As mentioned above, the containerd configuration needs a little tweak in
|
||||
# order not to create the default CNI configuration, so we update its config.
|
||||
echo "Fixing containerd configuration"
|
||||
sed -Ei 's/^(\s+conf_template)/\#\1/g' "${CONTAINERD_CONFIG}"
|
||||
|
||||
# Start containerd. It won't create it's CNI configuration file anymore.
|
||||
echo "Enabling and starting containerd"
|
||||
systemctl enable --now containerd
|
||||
fi
|
||||
|
||||
# Become the real kubelet, and pass it some additionally required flags (and
|
||||
# place these last so they have precedence).
|
||||
exec /home/kubernetes/bin/the-kubelet "${@}" --network-plugin=cni --cni-bin-dir={{ .Values.cni.binPath }}
|
||||
EOF
|
||||
else
|
||||
echo "Kubelet wrapper already exists, skipping..."
|
||||
fi
|
||||
else
|
||||
# (Generic) Alter the kubelet configuration to run in CNI mode
|
||||
echo "Changing kubelet configuration to --network-plugin=cni --cni-bin-dir={{ .Values.cni.binPath }}"
|
||||
mkdir -p {{ .Values.cni.binPath }}
|
||||
sed -i "s:--network-plugin=kubenet:--network-plugin=cni\ --cni-bin-dir={{ .Values.cni.binPath }}:g" "${KUBELET_DEFAULTS_FILE}"
|
||||
fi
|
||||
echo "Restarting the kubelet..."
|
||||
systemctl restart kubelet
|
||||
{{- end }}
|
||||
|
||||
{{- if (and .Values.gke.enabled (or .Values.enableIPv4Masquerade .Values.gke.disableDefaultSnat))}}
|
||||
# If Cilium is configured to manage masquerading of traffic leaving the node,
|
||||
# we need to disable the IP-MASQ chain because even if ip-masq-agent
|
||||
# is not installed, the node init script installs some default rules into
|
||||
# the IP-MASQ chain.
|
||||
# If we remove the jump to that ip-masq chain, then we ensure the ip masquerade
|
||||
# configuration is solely managed by Cilium.
|
||||
# Also, if Cilium is installed, it may be expected that it would be solely responsible
|
||||
# for the networking configuration on that node. So provide the same functionality
|
||||
# as the --disable-snat-flag for existing GKE clusters.
|
||||
iptables -w -t nat -D POSTROUTING -m comment --comment "ip-masq: ensure nat POSTROUTING directs all non-LOCAL destination traffic to our custom IP-MASQ chain" -m addrtype ! --dst-type LOCAL -j IP-MASQ || true
|
||||
{{- end }}
|
||||
|
||||
{{- if not (eq .Values.nodeinit.bootstrapFile "") }}
|
||||
mkdir -p {{ .Values.nodeinit.bootstrapFile | dir | quote }}
|
||||
date > {{ .Values.nodeinit.bootstrapFile | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.azure.enabled }}
|
||||
# AKS: If azure-vnet is installed on the node, and (still) configured in bridge mode,
|
||||
# configure it as 'transparent' to be consistent with Cilium's CNI chaining config.
|
||||
# If the azure-vnet CNI config is not removed, kubelet will execute CNI CHECK commands
|
||||
# against it every 5 seconds and write 'bridge' to its state file, causing inconsistent
|
||||
# behaviour when Pods are removed.
|
||||
if [ -f /etc/cni/net.d/10-azure.conflist ]; then
|
||||
echo "Ensuring azure-vnet is configured in 'transparent' mode..."
|
||||
sed -i 's/"mode":\s*"bridge"/"mode":"transparent"/g' /etc/cni/net.d/10-azure.conflist
|
||||
fi
|
||||
|
||||
# The azure0 interface being present means the node was booted with azure-vnet configured
|
||||
# in bridge mode. This means there might be ebtables rules and neight entries interfering
|
||||
# with pod connectivity if we deploy with Azure IPAM.
|
||||
if ip l show dev azure0 >/dev/null 2>&1; then
|
||||
|
||||
# In Azure IPAM mode, also remove the azure-vnet state file, otherwise ebtables rules get
|
||||
# restored by the azure-vnet CNI plugin on every CNI CHECK, which can cause connectivity
|
||||
# issues in Cilium-managed Pods. Since azure-vnet is no longer called on scheduling events,
|
||||
# this file can be removed.
|
||||
rm -f /var/run/azure-vnet.json
|
||||
|
||||
# This breaks connectivity for existing workload Pods when Cilium is scheduled, but we need
|
||||
# to flush these to prevent Cilium-managed Pod IPs conflicting with Pod IPs previously allocated
|
||||
# by azure-vnet. These ebtables DNAT rules contain fixed MACs that are no longer bound on the node,
|
||||
# causing packets for these Pods to be redirected back out to the gateway, where they are dropped.
|
||||
echo 'Flushing ebtables pre/postrouting rules in nat table.. (disconnecting non-Cilium Pods!)'
|
||||
ebtables -t nat -F PREROUTING || true
|
||||
ebtables -t nat -F POSTROUTING || true
|
||||
|
||||
# ip-masq-agent periodically injects PERM neigh entries towards the gateway
|
||||
# for all other k8s nodes in the cluster. These are safe to flush, as ARP can
|
||||
# resolve these nodes as usual. PERM entries will be automatically restored later.
|
||||
echo 'Deleting all permanent neighbour entries on azure0...'
|
||||
ip neigh show dev azure0 nud permanent | cut -d' ' -f1 | xargs -r -n1 ip neigh del dev azure0 to || true
|
||||
fi
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.nodeinit.revertReconfigureKubelet }}
|
||||
rm -f /tmp/node-deinit.cilium.io
|
||||
{{- end }}
|
||||
echo "Node initialization complete"
|
||||
22
cli/internal/helm/charts/cilium/templates/NOTES.txt
Normal file
22
cli/internal/helm/charts/cilium/templates/NOTES.txt
Normal file
@ -0,0 +1,22 @@
|
||||
{{- if (and (.Values.preflight.enabled) (not (.Values.agent)) (not (.Values.operator.enabled))) }}
|
||||
You have successfully ran the preflight check.
|
||||
Now make sure to check the number of READY pods is the same as the number of running cilium pods.
|
||||
Then make sure the cilium preflight deployment is also marked READY 1/1.
|
||||
If you have an issues please refer to the CNP Validation section in the upgrade guide.
|
||||
{{- else if (and (.Values.hubble.enabled) (.Values.hubble.relay.enabled)) }}
|
||||
{{- if (.Values.hubble.ui.enabled) }}
|
||||
You have successfully installed {{ title .Chart.Name }} with Hubble Relay and Hubble UI.
|
||||
{{- else }}
|
||||
You have successfully installed {{ title .Chart.Name }} with Hubble Relay.
|
||||
{{- end }}
|
||||
{{- else if .Values.hubble.enabled }}
|
||||
You have successfully installed {{ title .Chart.Name }} with Hubble.
|
||||
{{- else if (and (.Values.hubble.ui.enabled) (.Values.hubble.ui.standalone.enabled)) }}
|
||||
You have successfully installed {{ title .Chart.Name }} with standalone Hubble UI.
|
||||
{{- else }}
|
||||
You have successfully installed {{ title .Chart.Name }}.
|
||||
{{- end }}
|
||||
|
||||
Your release version is {{ .Chart.Version }}.
|
||||
|
||||
For any further help, visit https://docs.cilium.io/en/v{{ (semver .Chart.Version).Major }}.{{ (semver .Chart.Version).Minor }}/gettinghelp
|
||||
134
cli/internal/helm/charts/cilium/templates/_helpers.tpl
Normal file
134
cli/internal/helm/charts/cilium/templates/_helpers.tpl
Normal file
@ -0,0 +1,134 @@
|
||||
{{/*
|
||||
Create chart name and version as used by the chart label.
|
||||
*/}}
|
||||
{{- define "cilium.chart" -}}
|
||||
{{- printf "%s-%s" .Chart.Name .Chart.Version | replace "+" "_" | trunc 63 | trimSuffix "-" }}
|
||||
{{- end }}
|
||||
|
||||
{{/*
|
||||
Render full image name from given values, e.g:
|
||||
```
|
||||
image:
|
||||
repository: quay.io/cilium/cilium
|
||||
tag: v1.10.1
|
||||
useDigest: true
|
||||
digest: abcdefgh
|
||||
```
|
||||
then `include "cilium.image" .Values.image`
|
||||
will return `quay.io/cilium/cilium:v1.10.1@abcdefgh`
|
||||
*/}}
|
||||
{{- define "cilium.image" -}}
|
||||
{{- $digest := (.useDigest | default false) | ternary (printf "@%s" .digest) "" -}}
|
||||
{{- if .override -}}
|
||||
{{- printf "%s" .override -}}
|
||||
{{- else -}}
|
||||
{{- printf "%s:%s%s" .repository .tag $digest -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return user specify priorityClass or default criticalPriorityClass
|
||||
Usage:
|
||||
include "cilium.priorityClass" (list $ <priorityClass> <criticalPriorityClass>)
|
||||
where:
|
||||
* `priorityClass`: is user specify priorityClass e.g `.Values.operator.priorityClassName`
|
||||
* `criticalPriorityClass`: default criticalPriorityClass, e.g `"system-cluster-critical"`
|
||||
This value is used when `priorityClass` is `nil` and
|
||||
`.Values.enableCriticalPriorityClass=true` and kubernetes supported it.
|
||||
*/}}
|
||||
{{- define "cilium.priorityClass" -}}
|
||||
{{- $root := index . 0 -}}
|
||||
{{- $priorityClass := index . 1 -}}
|
||||
{{- $criticalPriorityClass := index . 2 -}}
|
||||
{{- if $priorityClass }}
|
||||
{{- $priorityClass }}
|
||||
{{- else if and $root.Values.enableCriticalPriorityClass $criticalPriorityClass -}}
|
||||
{{- if and (eq $root.Release.Namespace "kube-system") (semverCompare ">=1.10-0" $root.Capabilities.KubeVersion.Version) -}}
|
||||
{{- $criticalPriorityClass }}
|
||||
{{- else if semverCompare ">=1.17-0" $root.Capabilities.KubeVersion.Version -}}
|
||||
{{- $criticalPriorityClass }}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return the appropriate apiVersion for ingress.
|
||||
*/}}
|
||||
{{- define "ingress.apiVersion" -}}
|
||||
{{- if semverCompare ">=1.16-0, <1.19-0" .Capabilities.KubeVersion.Version -}}
|
||||
{{- print "networking.k8s.io/v1beta1" -}}
|
||||
{{- else if semverCompare "^1.19-0" .Capabilities.KubeVersion.Version -}}
|
||||
{{- print "networking.k8s.io/v1" -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return the appropriate backend for Hubble UI ingress.
|
||||
*/}}
|
||||
{{- define "ingress.paths" -}}
|
||||
{{ if semverCompare ">=1.4-0, <1.19-0" .Capabilities.KubeVersion.Version -}}
|
||||
backend:
|
||||
serviceName: hubble-ui
|
||||
servicePort: http
|
||||
{{- else if semverCompare "^1.19-0" .Capabilities.KubeVersion.Version -}}
|
||||
pathType: Prefix
|
||||
backend:
|
||||
service:
|
||||
name: hubble-ui
|
||||
port:
|
||||
name: http
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return the appropriate apiVersion for cronjob.
|
||||
*/}}
|
||||
{{- define "cronjob.apiVersion" -}}
|
||||
{{- if semverCompare ">=1.21-0" .Capabilities.KubeVersion.Version -}}
|
||||
{{- print "batch/v1" -}}
|
||||
{{- else -}}
|
||||
{{- print "batch/v1beta1" -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return the appropriate apiVersion for podDisruptionBudget.
|
||||
*/}}
|
||||
{{- define "podDisruptionBudget.apiVersion" -}}
|
||||
{{- if semverCompare ">=1.21-0" .Capabilities.KubeVersion.Version -}}
|
||||
{{- print "policy/v1" -}}
|
||||
{{- else -}}
|
||||
{{- print "policy/v1beta1" -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Generate TLS CA for Cilium
|
||||
Note: Always use this template as follows:
|
||||
{{- $_ := include "cilium.ca.setup" . -}}
|
||||
|
||||
The assignment to `$_` is required because we store the generated CI in a global `commonCA`
|
||||
and `commonCASecretName` variables.
|
||||
|
||||
*/}}
|
||||
{{- define "cilium.ca.setup" }}
|
||||
{{- if not .commonCA -}}
|
||||
{{- $ca := "" -}}
|
||||
{{- $secretName := "cilium-ca" -}}
|
||||
{{- $crt := .Values.tls.ca.cert -}}
|
||||
{{- $key := .Values.tls.ca.key -}}
|
||||
{{- if and $crt $key }}
|
||||
{{- $ca = buildCustomCert $crt $key -}}
|
||||
{{- else }}
|
||||
{{- with lookup "v1" "Secret" .Release.Namespace $secretName }}
|
||||
{{- $crt := index .data "ca.crt" }}
|
||||
{{- $key := index .data "ca.key" }}
|
||||
{{- $ca = buildCustomCert $crt $key -}}
|
||||
{{- else }}
|
||||
{{- $validity := ( .Values.tls.ca.certValidityDuration | int) -}}
|
||||
{{- $ca = genCA "Cilium CA" $validity -}}
|
||||
{{- end }}
|
||||
{{- end -}}
|
||||
{{- $_ := set (set . "commonCA" $ca) "commonCASecretName" $secretName -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
@ -0,0 +1,124 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) }}
|
||||
{{- /*
|
||||
Keep file in sync with cilium-preflight/clusterrole.yaml
|
||||
*/ -}}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRole
|
||||
metadata:
|
||||
name: cilium
|
||||
rules:
|
||||
- apiGroups:
|
||||
- networking.k8s.io
|
||||
resources:
|
||||
- networkpolicies
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- discovery.k8s.io
|
||||
resources:
|
||||
- endpointslices
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- namespaces
|
||||
- services
|
||||
- pods
|
||||
- endpoints
|
||||
- nodes
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
{{- if .Values.annotateK8sNode }}
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- nodes/status
|
||||
verbs:
|
||||
# To annotate the k8s node with Cilium's metadata
|
||||
- patch
|
||||
{{- end }}
|
||||
- apiGroups:
|
||||
- apiextensions.k8s.io
|
||||
resources:
|
||||
- customresourcedefinitions
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
# This is used when validating policies in preflight. This will need to stay
|
||||
# until we figure out how to avoid "get" inside the preflight, and then
|
||||
# should be removed ideally.
|
||||
- get
|
||||
{{- if eq "k8s" .Values.tls.secretsBackend }}
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
verbs:
|
||||
- get
|
||||
{{- end }}
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumbgploadbalancerippools
|
||||
- ciliumbgppeeringpolicies
|
||||
- ciliumclusterwideenvoyconfigs
|
||||
- ciliumclusterwidenetworkpolicies
|
||||
- ciliumegressgatewaypolicies
|
||||
- ciliumegressnatpolicies
|
||||
- ciliumendpoints
|
||||
- ciliumendpointslices
|
||||
- ciliumenvoyconfigs
|
||||
- ciliumidentities
|
||||
- ciliumlocalredirectpolicies
|
||||
- ciliumnetworkpolicies
|
||||
- ciliumnodes
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumidentities
|
||||
- ciliumendpoints
|
||||
- ciliumnodes
|
||||
verbs:
|
||||
- create
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
# To synchronize garbage collection of such resources
|
||||
resources:
|
||||
- ciliumidentities
|
||||
verbs:
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumendpoints
|
||||
verbs:
|
||||
- delete
|
||||
- get
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnodes
|
||||
- ciliumnodes/status
|
||||
verbs:
|
||||
- get
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnetworkpolicies/status
|
||||
- ciliumclusterwidenetworkpolicies/status
|
||||
- ciliumendpoints/status
|
||||
- ciliumendpoints
|
||||
verbs:
|
||||
- patch
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) .Values.serviceAccounts.cilium.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRoleBinding
|
||||
metadata:
|
||||
name: cilium
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: ClusterRole
|
||||
name: cilium
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.cilium.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,844 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) }}
|
||||
|
||||
{{- /* Default values with backwards compatibility */ -}}
|
||||
{{- $defaultKeepDeprecatedProbes := true -}}
|
||||
|
||||
{{- /* Default values when 1.8 was initially deployed */ -}}
|
||||
{{- if semverCompare ">=1.8" (default "1.8" .Values.upgradeCompatibility) -}}
|
||||
{{- $defaultKeepDeprecatedProbes = false -}}
|
||||
{{- end -}}
|
||||
|
||||
{{- $kubeProxyReplacement := (coalesce .Values.kubeProxyReplacement "disabled") -}}
|
||||
|
||||
---
|
||||
apiVersion: apps/v1
|
||||
kind: DaemonSet
|
||||
metadata:
|
||||
name: cilium
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: cilium
|
||||
{{- if .Values.keepDeprecatedLabels }}
|
||||
kubernetes.io/cluster-service: "true"
|
||||
{{- if and .Values.gke.enabled (eq .Release.Namespace "kube-system" ) }}
|
||||
{{- fail "Invalid configuration: Installing Cilium on GKE with 'kubernetes.io/cluster-service' labels on 'kube-system' namespace causes Cilium DaemonSet to be removed by GKE. Either install Cilium on a different Namespace or install with '--set keepDeprecatedLabels=false'" }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: cilium
|
||||
{{- if .Values.keepDeprecatedLabels }}
|
||||
kubernetes.io/cluster-service: "true"
|
||||
{{- end }}
|
||||
{{- with .Values.updateStrategy }}
|
||||
updateStrategy:
|
||||
{{- toYaml . | trim | nindent 4 }}
|
||||
{{- end }}
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
{{- if and .Values.prometheus.enabled (not .Values.prometheus.serviceMonitor.enabled) }}
|
||||
prometheus.io/port: "{{ .Values.prometheus.port }}"
|
||||
prometheus.io/scrape: "true"
|
||||
{{- end }}
|
||||
{{- if .Values.rollOutCiliumPods }}
|
||||
# ensure pods roll when configmap updates
|
||||
cilium.io/cilium-configmap-checksum: {{ include (print $.Template.BasePath "/cilium-configmap.yaml") . | sha256sum | quote }}
|
||||
{{- end }}
|
||||
{{- if not .Values.securityContext.privileged }}
|
||||
# Set app AppArmor's profile to "unconfined". The value of this annotation
|
||||
# can be modified as long users know which profiles they have available
|
||||
# in AppArmor.
|
||||
container.apparmor.security.beta.kubernetes.io/cilium-agent: "unconfined"
|
||||
container.apparmor.security.beta.kubernetes.io/clean-cilium-state: "unconfined"
|
||||
container.apparmor.security.beta.kubernetes.io/mount-cgroup: "unconfined"
|
||||
container.apparmor.security.beta.kubernetes.io/apply-sysctl-overwrites: "unconfined"
|
||||
{{- end }}
|
||||
{{- with .Values.podAnnotations }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
k8s-app: cilium
|
||||
{{- if .Values.keepDeprecatedLabels }}
|
||||
kubernetes.io/cluster-service: "true"
|
||||
{{- end }}
|
||||
{{- with .Values.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
containers:
|
||||
- name: cilium-agent
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
{{- if .Values.sleepAfterInit }}
|
||||
command:
|
||||
- /bin/bash
|
||||
- -c
|
||||
- --
|
||||
args:
|
||||
- |
|
||||
while true; do
|
||||
sleep 30;
|
||||
done
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- "true"
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- "true"
|
||||
{{- else }}
|
||||
command:
|
||||
- cilium-agent
|
||||
args:
|
||||
- --config-dir=/tmp/cilium/config-map
|
||||
{{- with .Values.extraArgs }}
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if semverCompare ">=1.20-0" .Capabilities.KubeVersion.Version }}
|
||||
startupProbe:
|
||||
httpGet:
|
||||
host: {{ .Values.ipv4.enabled | ternary "127.0.0.1" "::1" | quote }}
|
||||
path: /healthz
|
||||
port: {{ .Values.healthPort }}
|
||||
scheme: HTTP
|
||||
httpHeaders:
|
||||
- name: "brief"
|
||||
value: "true"
|
||||
failureThreshold: {{ .Values.startupProbe.failureThreshold }}
|
||||
periodSeconds: {{ .Values.startupProbe.periodSeconds }}
|
||||
successThreshold: 1
|
||||
{{- end }}
|
||||
livenessProbe:
|
||||
{{- if or .Values.keepDeprecatedProbes $defaultKeepDeprecatedProbes }}
|
||||
exec:
|
||||
command:
|
||||
- cilium
|
||||
- status
|
||||
- --brief
|
||||
{{- else }}
|
||||
httpGet:
|
||||
host: {{ .Values.ipv4.enabled | ternary "127.0.0.1" "::1" | quote }}
|
||||
path: /healthz
|
||||
port: {{ .Values.healthPort }}
|
||||
scheme: HTTP
|
||||
httpHeaders:
|
||||
- name: "brief"
|
||||
value: "true"
|
||||
{{- end }}
|
||||
{{- if semverCompare "<1.20-0" .Capabilities.KubeVersion.Version }}
|
||||
# The initial delay for the liveness probe is intentionally large to
|
||||
# avoid an endless kill & restart cycle if in the event that the initial
|
||||
# bootstrapping takes longer than expected.
|
||||
# Starting from Kubernetes 1.20, we are using startupProbe instead
|
||||
# of this field.
|
||||
initialDelaySeconds: 120
|
||||
{{- end }}
|
||||
periodSeconds: {{ .Values.livenessProbe.periodSeconds }}
|
||||
successThreshold: 1
|
||||
failureThreshold: {{ .Values.livenessProbe.failureThreshold }}
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
{{- if or .Values.keepDeprecatedProbes $defaultKeepDeprecatedProbes }}
|
||||
exec:
|
||||
command:
|
||||
- cilium
|
||||
- status
|
||||
- --brief
|
||||
{{- else }}
|
||||
httpGet:
|
||||
host: {{ .Values.ipv4.enabled | ternary "127.0.0.1" "::1" | quote }}
|
||||
path: /healthz
|
||||
port: {{ .Values.healthPort }}
|
||||
scheme: HTTP
|
||||
httpHeaders:
|
||||
- name: "brief"
|
||||
value: "true"
|
||||
{{- end }}
|
||||
{{- if semverCompare "<1.20-0" .Capabilities.KubeVersion.Version }}
|
||||
initialDelaySeconds: 5
|
||||
{{- end }}
|
||||
periodSeconds: {{ .Values.readinessProbe.periodSeconds }}
|
||||
successThreshold: 1
|
||||
failureThreshold: {{ .Values.readinessProbe.failureThreshold }}
|
||||
timeoutSeconds: 5
|
||||
{{- end }}
|
||||
env:
|
||||
- name: K8S_NODE_NAME
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: spec.nodeName
|
||||
- name: CILIUM_K8S_NAMESPACE
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: metadata.namespace
|
||||
- name: CILIUM_CLUSTERMESH_CONFIG
|
||||
value: /var/lib/cilium/clustermesh/
|
||||
- name: CILIUM_CNI_CHAINING_MODE
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
name: cilium-config
|
||||
key: cni-chaining-mode
|
||||
optional: true
|
||||
- name: CILIUM_CUSTOM_CNI_CONF
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
name: cilium-config
|
||||
key: custom-cni-conf
|
||||
optional: true
|
||||
{{- if .Values.k8sServiceHost }}
|
||||
- name: KUBERNETES_SERVICE_HOST
|
||||
value: {{ .Values.k8sServiceHost | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.k8sServicePort }}
|
||||
- name: KUBERNETES_SERVICE_PORT
|
||||
value: {{ .Values.k8sServicePort | quote }}
|
||||
{{- end }}
|
||||
{{- with .Values.extraEnv }}
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.cni.install }}
|
||||
lifecycle:
|
||||
postStart:
|
||||
exec:
|
||||
command:
|
||||
- "/cni-install.sh"
|
||||
- "--enable-debug={{ .Values.debug.enabled }}"
|
||||
- "--cni-exclusive={{ .Values.cni.exclusive }}"
|
||||
- "--log-file={{ .Values.cni.logFile }}"
|
||||
preStop:
|
||||
exec:
|
||||
command:
|
||||
- /cni-uninstall.sh
|
||||
{{- end }}
|
||||
{{- with .Values.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
{{- if or .Values.prometheus.enabled .Values.hubble.metrics.enabled }}
|
||||
ports:
|
||||
{{- if .Values.hubble.peerService.enabled }}
|
||||
- name: peer-service
|
||||
containerPort: {{ .Values.hubble.peerService.targetPort }}
|
||||
hostPort: {{ .Values.hubble.peerService.targetPort }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
{{- if .Values.prometheus.enabled }}
|
||||
- name: prometheus
|
||||
containerPort: {{ .Values.prometheus.port }}
|
||||
hostPort: {{ .Values.prometheus.port }}
|
||||
protocol: TCP
|
||||
{{- if .Values.proxy.prometheus.enabled }}
|
||||
- name: envoy-metrics
|
||||
containerPort: {{ .Values.proxy.prometheus.port }}
|
||||
hostPort: {{ .Values.proxy.prometheus.port }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.hubble.metrics.enabled }}
|
||||
- name: hubble-metrics
|
||||
containerPort: {{ .Values.hubble.metrics.port }}
|
||||
hostPort: {{ .Values.hubble.metrics.port }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
securityContext:
|
||||
{{- if .Values.securityContext.privileged }}
|
||||
privileged: true
|
||||
{{- else }}
|
||||
seLinuxOptions:
|
||||
level: 's0'
|
||||
# Running with spc_t since we have removed the privileged mode.
|
||||
# Users can change it to a different type as long as they have the
|
||||
# type available on the system.
|
||||
type: 'spc_t'
|
||||
capabilities:
|
||||
add:
|
||||
# Use to set socket permission
|
||||
- CHOWN
|
||||
# Used to terminate envoy child process
|
||||
- KILL
|
||||
# Used since cilium modifies routing tables, etc...
|
||||
- NET_ADMIN
|
||||
# Used since cilium creates raw sockets, etc...
|
||||
- NET_RAW
|
||||
# Used since cilium monitor uses mmap
|
||||
- IPC_LOCK
|
||||
# Used in iptables. Consider removing once we are iptables-free
|
||||
- SYS_MODULE
|
||||
# We need it for now but might not need it for >= 5.11 specially
|
||||
# for the 'SYS_RESOURCE'.
|
||||
# In >= 5.8 there's already BPF and PERMON capabilities
|
||||
- SYS_ADMIN
|
||||
# Could be an alternative for the SYS_ADMIN for the RLIMIT_NPROC
|
||||
- SYS_RESOURCE
|
||||
# Both PERFMON and BPF requires kernel 5.8, container runtime
|
||||
# cri-o >= v1.22.0 or containerd >= v1.5.0.
|
||||
# If available, SYS_ADMIN can be removed.
|
||||
#- PERFMON
|
||||
#- BPF
|
||||
{{- with .Values.securityContext.extraCapabilities }}
|
||||
{{- toYaml . | nindent 14 }}
|
||||
{{- end }}
|
||||
drop:
|
||||
- ALL
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
{{- if not .Values.securityContext.privileged }}
|
||||
# Unprivileged containers need to mount /proc/sys/net from the host
|
||||
# to have write access
|
||||
- mountPath: /host/proc/sys/net
|
||||
name: host-proc-sys-net
|
||||
# Unprivileged containers need to mount /proc/sys/kernel from the host
|
||||
# to have write access
|
||||
- mountPath: /host/proc/sys/kernel
|
||||
name: host-proc-sys-kernel
|
||||
{{- end}}
|
||||
{{- /* CRI-O already mounts the BPF filesystem */ -}}
|
||||
{{- if not (eq .Values.containerRuntime.integration "crio") }}
|
||||
- name: bpf-maps
|
||||
mountPath: /sys/fs/bpf
|
||||
{{- if .Values.securityContext.privileged }}
|
||||
mountPropagation: Bidirectional
|
||||
{{- else }}
|
||||
# Unprivileged containers can't set mount propagation to bidirectional
|
||||
# in this case we will mount the bpf fs from an init container that
|
||||
# is privileged and set the mount propagation from host to container
|
||||
# in Cilium.
|
||||
mountPropagation: HostToContainer
|
||||
{{- end}}
|
||||
{{- end }}
|
||||
{{- if not (contains "/run/cilium/cgroupv2" .Values.cgroup.hostRoot) }}
|
||||
# Check for duplicate mounts before mounting
|
||||
- name: cilium-cgroup
|
||||
mountPath: {{ .Values.cgroup.hostRoot }}
|
||||
{{- end}}
|
||||
- name: cilium-run
|
||||
mountPath: /var/run/cilium
|
||||
- name: cni-path
|
||||
mountPath: /host/opt/cni/bin
|
||||
- name: etc-cni-netd
|
||||
mountPath: {{ .Values.cni.hostConfDirMountPath }}
|
||||
{{- if .Values.etcd.enabled }}
|
||||
- name: etcd-config-path
|
||||
mountPath: /var/lib/etcd-config
|
||||
readOnly: true
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
- name: etcd-secrets
|
||||
mountPath: /var/lib/etcd-secrets
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
- name: clustermesh-secrets
|
||||
mountPath: /var/lib/cilium/clustermesh
|
||||
readOnly: true
|
||||
- name: cilium-config-path
|
||||
mountPath: /tmp/cilium/config-map
|
||||
readOnly: true
|
||||
{{- if .Values.ipMasqAgent.enabled }}
|
||||
- name: ip-masq-agent
|
||||
mountPath: /etc/config
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- if .Values.cni.configMap }}
|
||||
- name: cni-configuration
|
||||
mountPath: {{ .Values.cni.confFileMountPath }}
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
# Needed to be able to load kernel modules
|
||||
- name: lib-modules
|
||||
mountPath: /lib/modules
|
||||
readOnly: true
|
||||
- name: xtables-lock
|
||||
mountPath: /run/xtables.lock
|
||||
{{- if and .Values.encryption.enabled (eq .Values.encryption.type "ipsec") }}
|
||||
- name: cilium-ipsec-secrets
|
||||
mountPath: {{ .Values.encryption.ipsec.mountPath | default .Values.encryption.mountPath }}
|
||||
{{- end }}
|
||||
{{- if .Values.kubeConfigPath }}
|
||||
- name: kube-config
|
||||
mountPath: {{ .Values.kubeConfigPath }}
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- if .Values.bgp.enabled }}
|
||||
- name: bgp-config-path
|
||||
mountPath: /var/lib/cilium/bgp
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- if and .Values.hubble.enabled .Values.hubble.tls.enabled (hasKey .Values.hubble "listenAddress") }}
|
||||
- name: hubble-tls
|
||||
mountPath: /var/lib/cilium/tls/hubble
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- range .Values.extraHostPathMounts }}
|
||||
- name: {{ .name }}
|
||||
mountPath: {{ .mountPath }}
|
||||
readOnly: {{ .readOnly }}
|
||||
{{- if .mountPropagation }}
|
||||
mountPropagation: {{ .mountPropagation }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- with .Values.extraVolumeMounts }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.monitor.enabled }}
|
||||
- name: cilium-monitor
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
command:
|
||||
- /bin/bash
|
||||
- -c
|
||||
- --
|
||||
args:
|
||||
- |-
|
||||
for i in {1..5}; do \
|
||||
[ -S /var/run/cilium/monitor1_2.sock ] && break || sleep 10;\
|
||||
done; \
|
||||
cilium monitor
|
||||
{{- range $type := .Values.monitor.eventTypes -}}
|
||||
{{ " " }}--type={{ $type }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: cilium-run
|
||||
mountPath: /var/run/cilium
|
||||
{{- with .Values.monitor.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
initContainers:
|
||||
{{- if .Values.cgroup.autoMount.enabled }}
|
||||
# Required to mount cgroup2 filesystem on the underlying Kubernetes node.
|
||||
# We use nsenter command with host's cgroup and mount namespaces enabled.
|
||||
- name: mount-cgroup
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
env:
|
||||
- name: CGROUP_ROOT
|
||||
value: {{ .Values.cgroup.hostRoot }}
|
||||
- name: BIN_PATH
|
||||
value: {{ .Values.cni.binPath }}
|
||||
command:
|
||||
- sh
|
||||
- -ec
|
||||
# The statically linked Go program binary is invoked to avoid any
|
||||
# dependency on utilities like sh and mount that can be missing on certain
|
||||
# distros installed on the underlying host. Copy the binary to the
|
||||
# same directory where we install cilium cni plugin so that exec permissions
|
||||
# are available.
|
||||
- |
|
||||
cp /usr/bin/cilium-mount /hostbin/cilium-mount;
|
||||
nsenter --cgroup=/hostproc/1/ns/cgroup --mount=/hostproc/1/ns/mnt "${BIN_PATH}/cilium-mount" $CGROUP_ROOT;
|
||||
rm /hostbin/cilium-mount
|
||||
volumeMounts:
|
||||
- name: hostproc
|
||||
mountPath: /hostproc
|
||||
- name: cni-path
|
||||
mountPath: /hostbin
|
||||
securityContext:
|
||||
{{- if .Values.securityContext.privileged }}
|
||||
privileged: true
|
||||
{{- else }}
|
||||
seLinuxOptions:
|
||||
level: 's0'
|
||||
# Running with spc_t since we have removed the privileged mode.
|
||||
# Users can change it to a different type as long as they have the
|
||||
# type available on the system.
|
||||
type: 'spc_t'
|
||||
capabilities:
|
||||
drop:
|
||||
- ALL
|
||||
add:
|
||||
# Only used for 'mount' cgroup
|
||||
- SYS_ADMIN
|
||||
# Used for nsenter
|
||||
- SYS_CHROOT
|
||||
- SYS_PTRACE
|
||||
{{- end}}
|
||||
{{- end }}
|
||||
- name: apply-sysctl-overwrites
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
env:
|
||||
- name: BIN_PATH
|
||||
value: {{ .Values.cni.binPath }}
|
||||
command:
|
||||
- sh
|
||||
- -ec
|
||||
# The statically linked Go program binary is invoked to avoid any
|
||||
# dependency on utilities like sh that can be missing on certain
|
||||
# distros installed on the underlying host. Copy the binary to the
|
||||
# same directory where we install cilium cni plugin so that exec permissions
|
||||
# are available.
|
||||
- |
|
||||
cp /usr/bin/cilium-sysctlfix /hostbin/cilium-sysctlfix;
|
||||
nsenter --mount=/hostproc/1/ns/mnt "${BIN_PATH}/cilium-sysctlfix";
|
||||
rm /hostbin/cilium-sysctlfix
|
||||
volumeMounts:
|
||||
- name: hostproc
|
||||
mountPath: /hostproc
|
||||
- name: cni-path
|
||||
mountPath: /hostbin
|
||||
securityContext:
|
||||
{{- if .Values.securityContext.privileged }}
|
||||
privileged: true
|
||||
{{- else }}
|
||||
seLinuxOptions:
|
||||
level: 's0'
|
||||
# Running with spc_t since we have removed the privileged mode.
|
||||
# Users can change it to a different type as long as they have the
|
||||
# type available on the system.
|
||||
type: 'spc_t'
|
||||
capabilities:
|
||||
drop:
|
||||
- ALL
|
||||
add:
|
||||
# Required in order to access host's /etc/sysctl.d dir
|
||||
- SYS_ADMIN
|
||||
# Used for nsenter
|
||||
- SYS_CHROOT
|
||||
- SYS_PTRACE
|
||||
{{- end}}
|
||||
{{- if not .Values.securityContext.privileged }}
|
||||
# Mount the bpf fs if it is not mounted. We will perform this task
|
||||
# from a privileged container because the mount propagation bidirectional
|
||||
# only works from privileged containers.
|
||||
- name: mount-bpf-fs
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
args:
|
||||
- 'mount | grep "/sys/fs/bpf type bpf" || mount -t bpf bpf /sys/fs/bpf'
|
||||
command:
|
||||
- /bin/bash
|
||||
- -c
|
||||
- --
|
||||
securityContext:
|
||||
privileged: true
|
||||
{{- /* CRI-O already mounts the BPF filesystem */ -}}
|
||||
{{- if not (eq .Values.containerRuntime.integration "crio") }}
|
||||
volumeMounts:
|
||||
- name: bpf-maps
|
||||
mountPath: /sys/fs/bpf
|
||||
mountPropagation: Bidirectional
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if and .Values.nodeinit.enabled .Values.nodeinit.bootstrapFile }}
|
||||
- name: wait-for-node-init
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
command:
|
||||
- sh
|
||||
- -c
|
||||
- |
|
||||
until test -s {{ (print "/tmp/cilium-bootstrap.d/" (.Values.nodeinit.bootstrapFile | base)) | quote }}; do
|
||||
echo "Waiting on node-init to run...";
|
||||
sleep 1;
|
||||
done
|
||||
volumeMounts:
|
||||
- name: cilium-bootstrap-file-dir
|
||||
mountPath: "/tmp/cilium-bootstrap.d"
|
||||
{{- end }}
|
||||
- name: clean-cilium-state
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
command:
|
||||
- /init-container.sh
|
||||
env:
|
||||
- name: CILIUM_ALL_STATE
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
name: cilium-config
|
||||
key: clean-cilium-state
|
||||
optional: true
|
||||
- name: CILIUM_BPF_STATE
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
name: cilium-config
|
||||
key: clean-cilium-bpf-state
|
||||
optional: true
|
||||
{{- if .Values.k8sServiceHost }}
|
||||
- name: KUBERNETES_SERVICE_HOST
|
||||
value: {{ .Values.k8sServiceHost | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.k8sServicePort }}
|
||||
- name: KUBERNETES_SERVICE_PORT
|
||||
value: {{ .Values.k8sServicePort | quote }}
|
||||
{{- end }}
|
||||
{{- with .Values.extraEnv }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
securityContext:
|
||||
{{- if .Values.securityContext.privileged }}
|
||||
privileged: true
|
||||
{{- else }}
|
||||
seLinuxOptions:
|
||||
level: 's0'
|
||||
# Running with spc_t since we have removed the privileged mode.
|
||||
# Users can change it to a different type as long as they have the
|
||||
# type available on the system.
|
||||
type: 'spc_t'
|
||||
capabilities:
|
||||
# Most of the capabilities here are the same ones used in the
|
||||
# cilium-agent's container because this container can be used to
|
||||
# uninstall all Cilium resources, and therefore it is likely that
|
||||
# will need the same capabilities.
|
||||
add:
|
||||
# Used since cilium modifies routing tables, etc...
|
||||
- NET_ADMIN
|
||||
# Used in iptables. Consider removing once we are iptables-free
|
||||
- SYS_MODULE
|
||||
# We need it for now but might not need it for >= 5.11 specially
|
||||
# for the 'SYS_RESOURCE'.
|
||||
# In >= 5.8 there's already BPF and PERMON capabilities
|
||||
- SYS_ADMIN
|
||||
# Could be an alternative for the SYS_ADMIN for the RLIMIT_NPROC
|
||||
- SYS_RESOURCE
|
||||
# Both PERFMON and BPF requires kernel 5.8, container runtime
|
||||
# cri-o >= v1.22.0 or containerd >= v1.5.0.
|
||||
# If available, SYS_ADMIN can be removed.
|
||||
#- PERFMON
|
||||
#- BPF
|
||||
drop:
|
||||
- ALL
|
||||
{{- end}}
|
||||
volumeMounts:
|
||||
{{- /* CRI-O already mounts the BPF filesystem */ -}}
|
||||
{{- if not (eq .Values.containerRuntime.integration "crio") }}
|
||||
- name: bpf-maps
|
||||
mountPath: /sys/fs/bpf
|
||||
{{- end }}
|
||||
# Required to mount cgroup filesystem from the host to cilium agent pod
|
||||
- name: cilium-cgroup
|
||||
mountPath: {{ .Values.cgroup.hostRoot }}
|
||||
mountPropagation: HostToContainer
|
||||
- name: cilium-run
|
||||
mountPath: /var/run/cilium
|
||||
{{- with .Values.nodeinit.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
{{- if and .Values.waitForKubeProxy (ne $kubeProxyReplacement "strict") }}
|
||||
- name: wait-for-kube-proxy
|
||||
image: {{ include "cilium.image" .Values.image | quote }}
|
||||
imagePullPolicy: {{ .Values.image.pullPolicy }}
|
||||
securityContext:
|
||||
privileged: true
|
||||
command:
|
||||
- bash
|
||||
- -c
|
||||
- |
|
||||
while true
|
||||
do
|
||||
if iptables-nft-save -t mangle | grep -E '^:(KUBE-IPTABLES-HINT|KUBE-PROXY-CANARY)'; then
|
||||
echo "Found KUBE-IPTABLES-HINT or KUBE-PROXY-CANARY iptables rule in 'iptables-nft-save -t mangle'"
|
||||
exit 0
|
||||
fi
|
||||
if ip6tables-nft-save -t mangle | grep -E '^:(KUBE-IPTABLES-HINT|KUBE-PROXY-CANARY)'; then
|
||||
echo "Found KUBE-IPTABLES-HINT or KUBE-PROXY-CANARY iptables rule in 'ip6tables-nft-save -t mangle'"
|
||||
exit 0
|
||||
fi
|
||||
if iptables-legacy-save | grep -E '^:KUBE-PROXY-CANARY'; then
|
||||
echo "Found KUBE-PROXY-CANARY iptables rule in 'iptables-legacy-save"
|
||||
exit 0
|
||||
fi
|
||||
if ip6tables-legacy-save | grep -E '^:KUBE-PROXY-CANARY'; then
|
||||
echo "KUBE-PROXY-CANARY iptables rule in 'ip6tables-legacy-save'"
|
||||
exit 0
|
||||
fi
|
||||
echo "Waiting for kube-proxy to create iptables rules...";
|
||||
sleep 1;
|
||||
done
|
||||
{{- end }} # wait-for-kube-proxy
|
||||
restartPolicy: Always
|
||||
priorityClassName: {{ include "cilium.priorityClass" (list $ .Values.priorityClassName "system-node-critical") }}
|
||||
serviceAccount: {{ .Values.serviceAccounts.cilium.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.cilium.name | quote }}
|
||||
terminationGracePeriodSeconds: {{ .Values.terminationGracePeriodSeconds }}
|
||||
hostNetwork: true
|
||||
{{- if and .Values.etcd.managed (not .Values.etcd.k8sService) }}
|
||||
# In managed etcd mode, Cilium must be able to resolve the DNS name of
|
||||
# the etcd service
|
||||
dnsPolicy: ClusterFirstWithHostNet
|
||||
{{- else if .Values.dnsPolicy }}
|
||||
dnsPolicy: {{ .Values.dnsPolicy }}
|
||||
{{- end }}
|
||||
{{- with .Values.affinity }}
|
||||
affinity:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if and .Values.clustermesh.useAPIServer .Values.clustermesh.config.enabled }}
|
||||
hostAliases:
|
||||
{{- range $cluster := .Values.clustermesh.config.clusters }}
|
||||
{{- range $ip := $cluster.ips }}
|
||||
- ip: {{ $ip }}
|
||||
hostnames: [ "{{ $cluster.name }}.{{ $.Values.clustermesh.config.domain }}" ]
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
volumes:
|
||||
# To keep state between restarts / upgrades
|
||||
- name: cilium-run
|
||||
hostPath:
|
||||
path: {{ .Values.daemon.runPath }}
|
||||
type: DirectoryOrCreate
|
||||
{{- /* CRI-O already mounts the BPF filesystem */ -}}
|
||||
{{- if not (eq .Values.containerRuntime.integration "crio") }}
|
||||
# To keep state between restarts / upgrades for bpf maps
|
||||
- name: bpf-maps
|
||||
hostPath:
|
||||
path: /sys/fs/bpf
|
||||
type: DirectoryOrCreate
|
||||
{{- end }}
|
||||
{{- if .Values.cgroup.autoMount.enabled }}
|
||||
# To mount cgroup2 filesystem on the host
|
||||
- name: hostproc
|
||||
hostPath:
|
||||
path: /proc
|
||||
type: Directory
|
||||
{{- end }}
|
||||
# To keep state between restarts / upgrades for cgroup2 filesystem
|
||||
- name: cilium-cgroup
|
||||
hostPath:
|
||||
path: {{ .Values.cgroup.hostRoot}}
|
||||
type: DirectoryOrCreate
|
||||
# To install cilium cni plugin in the host
|
||||
- name: cni-path
|
||||
hostPath:
|
||||
path: {{ .Values.cni.binPath }}
|
||||
type: DirectoryOrCreate
|
||||
# To install cilium cni configuration in the host
|
||||
- name: etc-cni-netd
|
||||
hostPath:
|
||||
path: {{ .Values.cni.confPath }}
|
||||
type: DirectoryOrCreate
|
||||
# To be able to load kernel modules
|
||||
- name: lib-modules
|
||||
hostPath:
|
||||
path: /lib/modules
|
||||
# To access iptables concurrently with other processes (e.g. kube-proxy)
|
||||
- name: xtables-lock
|
||||
hostPath:
|
||||
path: /run/xtables.lock
|
||||
type: FileOrCreate
|
||||
{{- if .Values.kubeConfigPath }}
|
||||
- name: kube-config
|
||||
hostPath:
|
||||
path: {{ .Values.kubeConfigPath }}
|
||||
type: FileOrCreate
|
||||
{{- end }}
|
||||
{{- if and .Values.nodeinit.enabled .Values.nodeinit.bootstrapFile }}
|
||||
- name: cilium-bootstrap-file-dir
|
||||
hostPath:
|
||||
path: {{ .Values.nodeinit.bootstrapFile | dir | quote }}
|
||||
type: DirectoryOrCreate
|
||||
{{- end }}
|
||||
{{- if .Values.etcd.enabled }}
|
||||
# To read the etcd config stored in config maps
|
||||
- name: etcd-config-path
|
||||
configMap:
|
||||
name: cilium-config
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
items:
|
||||
- key: etcd-config
|
||||
path: etcd.config
|
||||
# To read the k8s etcd secrets in case the user might want to use TLS
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
- name: etcd-secrets
|
||||
secret:
|
||||
secretName: cilium-etcd-secrets
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
optional: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
# To read the clustermesh configuration
|
||||
- name: clustermesh-secrets
|
||||
secret:
|
||||
secretName: cilium-clustermesh
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
optional: true
|
||||
# To read the configuration from the config map
|
||||
- name: cilium-config-path
|
||||
configMap:
|
||||
name: cilium-config
|
||||
{{- if and .Values.ipMasqAgent .Values.ipMasqAgent.enabled }}
|
||||
- name: ip-masq-agent
|
||||
configMap:
|
||||
name: ip-masq-agent
|
||||
optional: true
|
||||
items:
|
||||
- key: config
|
||||
path: ip-masq-agent
|
||||
{{- end }}
|
||||
{{- if and .Values.encryption.enabled (eq .Values.encryption.type "ipsec") }}
|
||||
- name: cilium-ipsec-secrets
|
||||
secret:
|
||||
secretName: {{ .Values.encryption.ipsec.secretName | default .Values.encryption.secretName }}
|
||||
{{- end }}
|
||||
{{- if .Values.cni.configMap }}
|
||||
- name: cni-configuration
|
||||
configMap:
|
||||
name: {{ .Values.cni.configMap }}
|
||||
{{- end }}
|
||||
{{- if .Values.bgp.enabled }}
|
||||
- name: bgp-config-path
|
||||
configMap:
|
||||
name: bgp-config
|
||||
{{- end }}
|
||||
{{- if not .Values.securityContext.privileged }}
|
||||
- name: host-proc-sys-net
|
||||
hostPath:
|
||||
path: /proc/sys/net
|
||||
type: Directory
|
||||
- name: host-proc-sys-kernel
|
||||
hostPath:
|
||||
path: /proc/sys/kernel
|
||||
type: Directory
|
||||
{{- end }}
|
||||
{{- if and .Values.hubble.enabled .Values.hubble.tls.enabled (hasKey .Values.hubble "listenAddress") }}
|
||||
- name: hubble-tls
|
||||
projected:
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
sources:
|
||||
- secret:
|
||||
name: hubble-server-certs
|
||||
optional: true
|
||||
items:
|
||||
- key: ca.crt
|
||||
path: client-ca.crt
|
||||
- key: tls.crt
|
||||
path: server.crt
|
||||
- key: tls.key
|
||||
path: server.key
|
||||
{{- end }}
|
||||
{{- range .Values.extraHostPathMounts }}
|
||||
- name: {{ .name }}
|
||||
hostPath:
|
||||
path: {{ .hostPath }}
|
||||
{{- if .hostPathType }}
|
||||
type: {{ .hostPathType }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- with .Values.extraVolumes }}
|
||||
{{- toYaml . | nindent 6 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,16 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) .Values.serviceAccounts.cilium.create .Values.ingressController.enabled .Values.ingressController.secretsNamespace.name }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: Role
|
||||
metadata:
|
||||
name: cilium-secrets
|
||||
namespace: {{ .Values.ingressController.secretsNamespace.name | quote }}
|
||||
rules:
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
{{- end }}
|
||||
@ -0,0 +1,15 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) .Values.serviceAccounts.cilium.create .Values.ingressController.enabled .Values.ingressController.secretsNamespace.name}}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: RoleBinding
|
||||
metadata:
|
||||
name: cilium-secrets
|
||||
namespace: {{ .Values.ingressController.secretsNamespace.name | quote }}
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: Role
|
||||
name: cilium-secrets
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.cilium.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,46 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) .Values.prometheus.enabled }}
|
||||
{{- if .Values.prometheus.serviceMonitor.enabled }}
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: cilium-agent
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: cilium
|
||||
spec:
|
||||
clusterIP: None
|
||||
type: ClusterIP
|
||||
selector:
|
||||
k8s-app: cilium
|
||||
ports:
|
||||
- name: metrics
|
||||
port: {{ .Values.prometheus.port }}
|
||||
protocol: TCP
|
||||
targetPort: prometheus
|
||||
- name: envoy-metrics
|
||||
port: {{ .Values.proxy.prometheus.port }}
|
||||
protocol: TCP
|
||||
targetPort: envoy-metrics
|
||||
{{- else if .Values.proxy.prometheus.enabled }}
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: cilium-agent
|
||||
namespace: {{ .Release.Namespace }}
|
||||
annotations:
|
||||
prometheus.io/scrape: "true"
|
||||
prometheus.io/port: {{ .Values.proxy.prometheus.port | quote }}
|
||||
labels:
|
||||
k8s-app: cilium
|
||||
spec:
|
||||
clusterIP: None
|
||||
type: ClusterIP
|
||||
selector:
|
||||
k8s-app: cilium
|
||||
ports:
|
||||
- name: envoy-metrics
|
||||
port: {{ .Values.proxy.prometheus.port }}
|
||||
protocol: TCP
|
||||
targetPort: envoy-metrics
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,11 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) .Values.serviceAccounts.cilium.create }}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ .Values.serviceAccounts.cilium.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- if .Values.serviceAccounts.cilium.annotations }}
|
||||
annotations:
|
||||
{{- toYaml .Values.serviceAccounts.cilium.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,30 @@
|
||||
{{- if and .Values.agent (not .Values.preflight.enabled) .Values.prometheus.enabled .Values.prometheus.serviceMonitor.enabled }}
|
||||
---
|
||||
apiVersion: monitoring.coreos.com/v1
|
||||
kind: ServiceMonitor
|
||||
metadata:
|
||||
name: cilium-agent
|
||||
namespace: {{ .Values.prometheus.serviceMonitor.namespace | default .Release.Namespace }}
|
||||
labels:
|
||||
{{- with .Values.prometheus.serviceMonitor.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
annotations:
|
||||
{{- with .Values.prometheus.serviceMonitor.annotations }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: cilium
|
||||
namespaceSelector:
|
||||
matchNames:
|
||||
- {{ .Release.Namespace }}
|
||||
endpoints:
|
||||
- port: metrics
|
||||
interval: 10s
|
||||
honorLabels: true
|
||||
path: /metrics
|
||||
targetLabels:
|
||||
- k8s-app
|
||||
{{- end }}
|
||||
@ -0,0 +1,17 @@
|
||||
{{- if or
|
||||
(and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "helm") (not .Values.clustermesh.apiserver.tls.ca.cert))
|
||||
(and (or .Values.agent .Values.hubble.relay.enabled .Values.hubble.ui.enabled) .Values.hubble.enabled .Values.hubble.tls.enabled .Values.hubble.tls.auto.enabled (eq .Values.hubble.tls.auto.method "helm") (not .Values.hubble.tls.ca.cert))
|
||||
(and .Values.tls.ca.key .Values.tls.ca.cert)
|
||||
-}}
|
||||
|
||||
{{- $_ := include "cilium.ca.setup" . -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: {{ .commonCASecretName }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
ca.crt: {{ .commonCA.Cert | b64enc }}
|
||||
ca.key: {{ .commonCA.Key | b64enc }}
|
||||
{{- end }}
|
||||
950
cli/internal/helm/charts/cilium/templates/cilium-configmap.yaml
Normal file
950
cli/internal/helm/charts/cilium/templates/cilium-configmap.yaml
Normal file
@ -0,0 +1,950 @@
|
||||
{{- if and (.Values.agent) (not .Values.preflight.enabled) }}
|
||||
{{- /* Default values with backwards compatibility */ -}}
|
||||
{{- $defaultEnableCnpStatusUpdates := "true" -}}
|
||||
{{- $defaultBpfMapDynamicSizeRatio := 0.0 -}}
|
||||
{{- $defaultBpfMasquerade := "false" -}}
|
||||
{{- $defaultBpfClockProbe := "false" -}}
|
||||
{{- $defaultBpfTProxy := "false" -}}
|
||||
{{- $defaultIPAM := "cluster-pool" -}}
|
||||
{{- $defaultOperatorApiServeAddr := "localhost:9234" -}}
|
||||
{{- $defaultBpfCtTcpMax := 524288 -}}
|
||||
{{- $defaultBpfCtAnyMax := 262144 -}}
|
||||
{{- $enableIdentityMark := "true" -}}
|
||||
{{- $fragmentTracking := "true" -}}
|
||||
{{- $crdWaitTimeout := "5m" -}}
|
||||
{{- $defaultKubeProxyReplacement := "disabled" -}}
|
||||
{{- $azureUsePrimaryAddress := "true" -}}
|
||||
|
||||
{{- /* Default values when 1.8 was initially deployed */ -}}
|
||||
{{- if semverCompare ">=1.8" (default "1.8" .Values.upgradeCompatibility) -}}
|
||||
{{- $defaultEnableCnpStatusUpdates = "false" -}}
|
||||
{{- $defaultBpfMapDynamicSizeRatio = 0.0025 -}}
|
||||
{{- $defaultBpfMasquerade = "true" -}}
|
||||
{{- $defaultBpfClockProbe = "true" -}}
|
||||
{{- $defaultIPAM = "cluster-pool" -}}
|
||||
{{- if .Values.ipv4.enabled }}
|
||||
{{- $defaultOperatorApiServeAddr = "127.0.0.1:9234" -}}
|
||||
{{- else -}}
|
||||
{{- $defaultOperatorApiServeAddr = "[::1]:9234" -}}
|
||||
{{- end }}
|
||||
{{- $defaultBpfCtTcpMax = 0 -}}
|
||||
{{- $defaultBpfCtAnyMax = 0 -}}
|
||||
{{- $defaultKubeProxyReplacement = "probe" -}}
|
||||
{{- end -}}
|
||||
|
||||
{{- /* Default values when 1.9 was initially deployed */ -}}
|
||||
{{- if semverCompare ">=1.9" (default "1.9" .Values.upgradeCompatibility) -}}
|
||||
{{- $defaultKubeProxyReplacement = "probe" -}}
|
||||
{{- end -}}
|
||||
|
||||
{{- /* Default values when 1.10 was initially deployed */ -}}
|
||||
{{- if semverCompare ">=1.10" (default "1.10" .Values.upgradeCompatibility) -}}
|
||||
{{- /* Needs to be explicitly disabled because it was enabled on all versions >=v1.8 above. */ -}}
|
||||
{{- $defaultBpfMasquerade = "false" -}}
|
||||
{{- end -}}
|
||||
|
||||
{{- /* Default values when 1.12 was initially deployed */ -}}
|
||||
{{- if semverCompare ">=1.12" (default "1.12" .Values.upgradeCompatibility) -}}
|
||||
{{- if .Values.azure.enabled }}
|
||||
{{- $azureUsePrimaryAddress = "false" -}}
|
||||
{{- end }}
|
||||
{{- end -}}
|
||||
|
||||
{{- $ipam := (coalesce .Values.ipam.mode $defaultIPAM) -}}
|
||||
{{- $bpfCtTcpMax := (coalesce .Values.bpf.ctTcpMax $defaultBpfCtTcpMax) -}}
|
||||
{{- $bpfCtAnyMax := (coalesce .Values.bpf.ctAnyMax $defaultBpfCtAnyMax) -}}
|
||||
{{- $kubeProxyReplacement := (coalesce .Values.kubeProxyReplacement $defaultKubeProxyReplacement) -}}
|
||||
{{- $azureUsePrimaryAddress = (coalesce .Values.azure.usePrimaryAddress $azureUsePrimaryAddress) -}}
|
||||
{{- $socketLB := (coalesce .Values.socketLB .Values.hostServices) -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: cilium-config
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
{{- if .Values.etcd.enabled }}
|
||||
# The kvstore configuration is used to enable use of a kvstore for state
|
||||
# storage. This can either be provided with an external kvstore or with the
|
||||
# help of cilium-etcd-operator which operates an etcd cluster automatically.
|
||||
kvstore: etcd
|
||||
{{- if .Values.etcd.k8sService }}
|
||||
kvstore-opt: '{"etcd.config": "/var/lib/etcd-config/etcd.config", "etcd.operator": "true"}'
|
||||
{{- else }}
|
||||
kvstore-opt: '{"etcd.config": "/var/lib/etcd-config/etcd.config"}'
|
||||
{{- end }}
|
||||
|
||||
# This etcd-config contains the etcd endpoints of your cluster. If you use
|
||||
# TLS please make sure you follow the tutorial in https://cilium.link/etcd-config
|
||||
etcd-config: |-
|
||||
---
|
||||
endpoints:
|
||||
{{- if .Values.etcd.managed }}
|
||||
- https://cilium-etcd-client.{{ .Release.Namespace }}.svc:2379
|
||||
{{- else }}
|
||||
{{- range .Values.etcd.endpoints }}
|
||||
- {{ . }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
trusted-ca-file: '/var/lib/etcd-secrets/etcd-client-ca.crt'
|
||||
key-file: '/var/lib/etcd-secrets/etcd-client.key'
|
||||
cert-file: '/var/lib/etcd-secrets/etcd-client.crt'
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "conntrackGCInterval" }}
|
||||
conntrack-gc-interval: {{ .Values.conntrackGCInterval | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "disableEnvoyVersionCheck" }}
|
||||
disable-envoy-version-check: {{ .Values.disableEnvoyVersionCheck | quote }}
|
||||
{{- end }}
|
||||
|
||||
# Identity allocation mode selects how identities are shared between cilium
|
||||
# nodes by setting how they are stored. The options are "crd" or "kvstore".
|
||||
# - "crd" stores identities in kubernetes as CRDs (custom resource definition).
|
||||
# These can be queried with:
|
||||
# kubectl get ciliumid
|
||||
# - "kvstore" stores identities in an etcd kvstore, that is
|
||||
# configured below. Cilium versions before 1.6 supported only the kvstore
|
||||
# backend. Upgrades from these older cilium versions should continue using
|
||||
# the kvstore by commenting out the identity-allocation-mode below, or
|
||||
# setting it to "kvstore".
|
||||
identity-allocation-mode: {{ .Values.identityAllocationMode }}
|
||||
{{- if hasKey .Values "identityHeartbeatTimeout" }}
|
||||
identity-heartbeat-timeout: "{{ .Values.identityHeartbeatTimeout }}"
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "identityGCInterval" }}
|
||||
identity-gc-interval: "{{ .Values.identityGCInterval }}"
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.operator "endpointGCInterval" }}
|
||||
cilium-endpoint-gc-interval: "{{ .Values.operator.endpointGCInterval }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.operator "nodeGCInterval" }}
|
||||
nodes-gc-interval: "{{ .Values.operator.nodeGCInterval | default "0s" }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "disableEndpointCRD" }}
|
||||
# Disable the usage of CiliumEndpoint CRD
|
||||
disable-endpoint-crd: "{{ .Values.disableEndpointCRD }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "identityChangeGracePeriod" }}
|
||||
# identity-change-grace-period is the grace period that needs to pass
|
||||
# before an endpoint that has changed its identity will start using
|
||||
# that new identity. During the grace period, the new identity has
|
||||
# already been allocated and other nodes in the cluster have a chance
|
||||
# to whitelist the new upcoming identity of the endpoint.
|
||||
identity-change-grace-period: {{ default "5s" .Values.identityChangeGracePeriod | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "labels" }}
|
||||
# To include or exclude matched resources from cilium identity evaluation
|
||||
labels: {{ .Values.labels | quote }}
|
||||
{{- end }}
|
||||
|
||||
# If you want to run cilium in debug mode change this value to true
|
||||
debug: {{ .Values.debug.enabled | quote }}
|
||||
|
||||
{{- if hasKey .Values.debug "verbose" }}
|
||||
debug-verbose: "{{ .Values.debug.verbose }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if ne (int .Values.healthPort) 9879 }}
|
||||
# Set the TCP port for the agent health status API. This is not the port used
|
||||
# for cilium-health.
|
||||
agent-health-port: "{{ .Values.healthPort }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "clusterHealthPort" }}
|
||||
# Set the TCP port for the agent health API. This port is used for cilium-health.
|
||||
cluster-health-port: "{{ .Values.clusterHealthPort }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "policyEnforcementMode" }}
|
||||
# The agent can be put into the following three policy enforcement modes
|
||||
# default, always and never.
|
||||
# https://docs.cilium.io/en/latest/policy/intro/#policy-enforcement-modes
|
||||
enable-policy: "{{ lower .Values.policyEnforcementMode }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.prometheus.enabled }}
|
||||
# If you want metrics enabled in all of your Cilium agents, set the port for
|
||||
# which the Cilium agents will have their metrics exposed.
|
||||
# This option deprecates the "prometheus-serve-addr" in the
|
||||
# "cilium-metrics-config" ConfigMap
|
||||
# NOTE that this will open the port on ALL nodes where Cilium pods are
|
||||
# scheduled.
|
||||
prometheus-serve-addr: ":{{ .Values.prometheus.port }}"
|
||||
# Port to expose Envoy metrics (e.g. "9964"). Envoy metrics listener will be disabled if this
|
||||
# field is not set.
|
||||
{{- if .Values.proxy.prometheus.enabled }}
|
||||
proxy-prometheus-port: "{{ .Values.proxy.prometheus.port }}"
|
||||
{{- end }}
|
||||
{{- if .Values.prometheus.metrics }}
|
||||
# Metrics that should be enabled or disabled from the default metric
|
||||
# list. (+metric_foo to enable metric_foo , -metric_bar to disable
|
||||
# metric_bar).
|
||||
metrics: {{- range .Values.prometheus.metrics }}
|
||||
{{ . }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.operator.prometheus.enabled }}
|
||||
# If you want metrics enabled in cilium-operator, set the port for
|
||||
# which the Cilium Operator will have their metrics exposed.
|
||||
# NOTE that this will open the port on the nodes where Cilium operator pod
|
||||
# is scheduled.
|
||||
operator-prometheus-serve-addr: ":{{ .Values.operator.prometheus.port }}"
|
||||
enable-metrics: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.operator.skipCRDCreation }}
|
||||
skip-crd-creation: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.ingressController.enabled }}
|
||||
enable-ingress-controller: "true"
|
||||
enable-envoy-config: "true"
|
||||
enforce-ingress-https: {{ .Values.ingressController.enforceHttps | quote }}
|
||||
enable-ingress-secrets-sync: {{ .Values.ingressController.secretsNamespace.sync | quote }}
|
||||
ingress-secrets-namespace: {{ .Values.ingressController.secretsNamespace.name | quote }}
|
||||
{{- end }}
|
||||
|
||||
# Enable IPv4 addressing. If enabled, all endpoints are allocated an IPv4
|
||||
# address.
|
||||
enable-ipv4: {{ .Values.ipv4.enabled | quote }}
|
||||
|
||||
# Enable IPv6 addressing. If enabled, all endpoints are allocated an IPv6
|
||||
# address.
|
||||
enable-ipv6: {{ .Values.ipv6.enabled | quote }}
|
||||
|
||||
{{- if .Values.cleanState }}
|
||||
# If a serious issue occurs during Cilium startup, this
|
||||
# invasive option may be set to true to remove all persistent
|
||||
# state. Endpoints will not be restored using knowledge from a
|
||||
# prior Cilium run, so they may receive new IP addresses upon
|
||||
# restart. This also triggers clean-cilium-bpf-state.
|
||||
clean-cilium-state: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.cleanBpfState }}
|
||||
# If you want to clean cilium BPF state, set this to true;
|
||||
# Removes all BPF maps from the filesystem. Upon restart,
|
||||
# endpoints are restored with the same IP addresses, however
|
||||
# any ongoing connections may be disrupted briefly.
|
||||
# Loadbalancing decisions will be reset, so any ongoing
|
||||
# connections via a service may be loadbalanced to a different
|
||||
# backend after restart.
|
||||
clean-cilium-bpf-state: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.cni "customConf" }}
|
||||
# Users who wish to specify their own custom CNI configuration file must set
|
||||
# custom-cni-conf to "true", otherwise Cilium may overwrite the configuration.
|
||||
custom-cni-conf: "{{ .Values.cni.customConf }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "bpfClockProbe" }}
|
||||
enable-bpf-clock-probe: {{ .Values.bpfClockProbe | quote }}
|
||||
{{- else if eq $defaultBpfClockProbe "true" }}
|
||||
enable-bpf-clock-probe: {{ $defaultBpfClockProbe | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.bpf "tproxy" }}
|
||||
enable-bpf-tproxy: {{ .Values.bpf.tproxy | quote }}
|
||||
{{- else if eq $defaultBpfTProxy "true" }}
|
||||
enable-bpf-tproxy: {{ $defaultBpfTProxy | quote }}
|
||||
{{- end }}
|
||||
# If you want cilium monitor to aggregate tracing for packets, set this level
|
||||
# to "low", "medium", or "maximum". The higher the level, the less packets
|
||||
# that will be seen in monitor output.
|
||||
monitor-aggregation: {{ .Values.bpf.monitorAggregation }}
|
||||
|
||||
# The monitor aggregation interval governs the typical time between monitor
|
||||
# notification events for each allowed connection.
|
||||
#
|
||||
# Only effective when monitor aggregation is set to "medium" or higher.
|
||||
monitor-aggregation-interval: {{ .Values.bpf.monitorInterval }}
|
||||
|
||||
# The monitor aggregation flags determine which TCP flags which, upon the
|
||||
# first observation, cause monitor notifications to be generated.
|
||||
#
|
||||
# Only effective when monitor aggregation is set to "medium" or higher.
|
||||
monitor-aggregation-flags: {{ .Values.bpf.monitorFlags }}
|
||||
|
||||
|
||||
|
||||
|
||||
{{- if hasKey .Values.bpf "mapDynamicSizeRatio" }}
|
||||
# Specifies the ratio (0.0-1.0) of total system memory to use for dynamic
|
||||
# sizing of the TCP CT, non-TCP CT, NAT and policy BPF maps.
|
||||
bpf-map-dynamic-size-ratio: {{ .Values.bpf.mapDynamicSizeRatio | quote }}
|
||||
{{- else if ne $defaultBpfMapDynamicSizeRatio 0.0 }}
|
||||
# Specifies the ratio (0.0-1.0) of total system memory to use for dynamic
|
||||
# sizing of the TCP CT, non-TCP CT, NAT and policy BPF maps.
|
||||
bpf-map-dynamic-size-ratio: {{ $defaultBpfMapDynamicSizeRatio | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.bpf "hostLegacyRouting" }}
|
||||
enable-host-legacy-routing: {{ .Values.bpf.hostLegacyRouting | quote }}
|
||||
{{- else if hasKey .Values.bpf "hostRouting" }}
|
||||
# DEPRECATED: this block should be removed in 1.13
|
||||
enable-host-legacy-routing: {{ .Values.bpf.hostRouting | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if or $bpfCtTcpMax $bpfCtAnyMax }}
|
||||
# bpf-ct-global-*-max specifies the maximum number of connections
|
||||
# supported across all endpoints, split by protocol: tcp or other. One pair
|
||||
# of maps uses these values for IPv4 connections, and another pair of maps
|
||||
# use these values for IPv6 connections.
|
||||
#
|
||||
# If these values are modified, then during the next Cilium startup the
|
||||
# tracking of ongoing connections may be disrupted. As a result, reply
|
||||
# packets may be dropped and the load-balancing decisions for established
|
||||
# connections may change.
|
||||
#
|
||||
# For users upgrading from Cilium 1.2 or earlier, to minimize disruption
|
||||
# during the upgrade process, set bpf-ct-global-tcp-max to 1000000.
|
||||
{{- if $bpfCtTcpMax }}
|
||||
bpf-ct-global-tcp-max: {{ $bpfCtTcpMax | quote }}
|
||||
{{- end }}
|
||||
{{- if $bpfCtAnyMax }}
|
||||
bpf-ct-global-any-max: {{ $bpfCtAnyMax | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.bpf "natMax" }}
|
||||
# bpf-nat-global-max specified the maximum number of entries in the
|
||||
# BPF NAT table.
|
||||
bpf-nat-global-max: "{{ .Values.bpf.natMax }}"
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.bpf "neighMax" }}
|
||||
# bpf-neigh-global-max specified the maximum number of entries in the
|
||||
# BPF neighbor table.
|
||||
bpf-neigh-global-max: "{{ .Values.bpf.neighMax }}"
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.bpf "policyMapMax" }}
|
||||
# bpf-policy-map-max specifies the maximum number of entries in endpoint
|
||||
# policy map (per endpoint)
|
||||
bpf-policy-map-max: "{{ .Values.bpf.policyMapMax }}"
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.bpf "lbMapMax" }}
|
||||
# bpf-lb-map-max specifies the maximum number of entries in bpf lb service,
|
||||
# backend and affinity maps.
|
||||
bpf-lb-map-max: "{{ .Values.bpf.lbMapMax }}"
|
||||
{{- end }}
|
||||
# bpf-lb-bypass-fib-lookup instructs Cilium to enable the FIB lookup bypass
|
||||
# optimization for nodeport reverse NAT handling.
|
||||
{{- if hasKey .Values.bpf "lbBypassFIBLookup" }}
|
||||
bpf-lb-bypass-fib-lookup: {{ .Values.bpf.lbBypassFIBLookup | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.bpf "lbExternalClusterIP" }}
|
||||
bpf-lb-external-clusterip: {{ .Values.bpf.lbExternalClusterIP | quote }}
|
||||
{{- end }}
|
||||
|
||||
# Pre-allocation of map entries allows per-packet latency to be reduced, at
|
||||
# the expense of up-front memory allocation for the entries in the maps. The
|
||||
# default value below will minimize memory usage in the default installation;
|
||||
# users who are sensitive to latency may consider setting this to "true".
|
||||
#
|
||||
# This option was introduced in Cilium 1.4. Cilium 1.3 and earlier ignore
|
||||
# this option and behave as though it is set to "true".
|
||||
#
|
||||
# If this value is modified, then during the next Cilium startup the restore
|
||||
# of existing endpoints and tracking of ongoing connections may be disrupted.
|
||||
# As a result, reply packets may be dropped and the load-balancing decisions
|
||||
# for established connections may change.
|
||||
#
|
||||
# If this option is set to "false" during an upgrade from 1.3 or earlier to
|
||||
# 1.4 or later, then it may cause one-time disruptions during the upgrade.
|
||||
preallocate-bpf-maps: "{{ .Values.bpf.preallocateMaps }}"
|
||||
|
||||
# Regular expression matching compatible Istio sidecar istio-proxy
|
||||
# container image names
|
||||
sidecar-istio-proxy-image: "{{ .Values.proxy.sidecarImageRegex }}"
|
||||
|
||||
# Name of the cluster. Only relevant when building a mesh of clusters.
|
||||
cluster-name: {{ .Values.cluster.name }}
|
||||
|
||||
{{- if hasKey .Values.cluster "id" }}
|
||||
# Unique ID of the cluster. Must be unique across all conneted clusters and
|
||||
# in the range of 1 and 255. Only relevant when building a mesh of clusters.
|
||||
cluster-id: "{{ .Values.cluster.id }}"
|
||||
{{- end }}
|
||||
|
||||
# Encapsulation mode for communication between nodes
|
||||
# Possible values:
|
||||
# - disabled
|
||||
# - vxlan (default)
|
||||
# - geneve
|
||||
{{- if .Values.gke.enabled }}
|
||||
tunnel: "disabled"
|
||||
enable-endpoint-routes: "true"
|
||||
enable-local-node-route: "false"
|
||||
{{- else if .Values.aksbyocni.enabled }}
|
||||
tunnel: "vxlan"
|
||||
{{- else }}
|
||||
tunnel: {{ .Values.tunnel | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "tunnelPort" }}
|
||||
tunnel-port: "{{ .Values.tunnelPort }}"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.eni.enabled }}
|
||||
enable-endpoint-routes: "true"
|
||||
auto-create-cilium-node-resource: "true"
|
||||
{{- if .Values.eni.updateEC2AdapterLimitViaAPI }}
|
||||
update-ec2-adapter-limit-via-api: "true"
|
||||
{{- end }}
|
||||
{{- if .Values.eni.awsReleaseExcessIPs }}
|
||||
aws-release-excess-ips: "true"
|
||||
{{- end }}
|
||||
{{- if .Values.eni.awsEnablePrefixDelegation }}
|
||||
aws-enable-prefix-delegation: "true"
|
||||
{{- end }}
|
||||
ec2-api-endpoint: {{ .Values.eni.ec2APIEndpoint | quote }}
|
||||
eni-tags: {{ .Values.eni.eniTags | toRawJson | quote }}
|
||||
subnet-ids-filter: {{ .Values.eni.subnetIDsFilter | quote }}
|
||||
subnet-tags-filter: {{ .Values.eni.subnetTagsFilter | quote }}
|
||||
instance-tags-filter: {{ .Values.eni.instanceTagsFilter | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.azure.enabled }}
|
||||
enable-endpoint-routes: "true"
|
||||
auto-create-cilium-node-resource: "true"
|
||||
enable-local-node-route: "false"
|
||||
{{- if .Values.azure.userAssignedIdentityID }}
|
||||
azure-user-assigned-identity-id: {{ .Values.azure.userAssignedIdentityID | quote }}
|
||||
{{- end }}
|
||||
azure-use-primary-address: {{ $azureUsePrimaryAddress | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.alibabacloud.enabled }}
|
||||
enable-endpoint-routes: "true"
|
||||
auto-create-cilium-node-resource: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "l7Proxy" }}
|
||||
# Enables L7 proxy for L7 policy enforcement and visibility
|
||||
enable-l7-proxy: {{ .Values.l7Proxy | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if ne .Values.cni.chainingMode "none" }}
|
||||
# Enable chaining with another CNI plugin
|
||||
#
|
||||
# Supported modes:
|
||||
# - none
|
||||
# - aws-cni
|
||||
# - flannel
|
||||
# - generic-veth
|
||||
# - portmap (Enables HostPort support for Cilium)
|
||||
cni-chaining-mode: {{ .Values.cni.chainingMode }}
|
||||
|
||||
{{- if hasKey .Values "enableIdentityMark" }}
|
||||
enable-identity-mark: {{ .Values.enableIdentityMark | quote }}
|
||||
{{- else if (ne $enableIdentityMark "true") }}
|
||||
enable-identity-mark: "false"
|
||||
{{- end }}
|
||||
{{- if ne .Values.cni.chainingMode "portmap" }}
|
||||
# Disable the PodCIDR route to the cilium_host interface as it is not
|
||||
# required. While chaining, it is the responsibility of the underlying plugin
|
||||
# to enable routing.
|
||||
enable-local-node-route: "false"
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
enable-ipv4-masquerade: {{ .Values.enableIPv4Masquerade | quote }}
|
||||
enable-ipv6-masquerade: {{ .Values.enableIPv6Masquerade | quote }}
|
||||
|
||||
{{- if hasKey .Values.bpf "masquerade" }}
|
||||
enable-bpf-masquerade: {{ .Values.bpf.masquerade | quote }}
|
||||
{{- else if eq $defaultBpfMasquerade "true" }}
|
||||
enable-bpf-masquerade: {{ $defaultBpfMasquerade | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "egressMasqueradeInterfaces" }}
|
||||
egress-masquerade-interfaces: {{ .Values.egressMasqueradeInterfaces }}
|
||||
{{- end }}
|
||||
{{- if and .Values.ipMasqAgent .Values.ipMasqAgent.enabled }}
|
||||
enable-ip-masq-agent: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.encryption.enabled }}
|
||||
{{- if eq .Values.encryption.type "ipsec" }}
|
||||
enable-ipsec: {{ .Values.encryption.enabled | quote }}
|
||||
|
||||
{{- if and .Values.encryption.ipsec.mountPath .Values.encryption.ipsec.keyFile }}
|
||||
ipsec-key-file: {{ .Values.encryption.ipsec.mountPath }}/{{ .Values.encryption.ipsec.keyFile }}
|
||||
{{- else }}
|
||||
ipsec-key-file: {{ .Values.encryption.mountPath }}/{{ .Values.encryption.keyFile }}
|
||||
{{- end }}
|
||||
{{- if .Values.encryption.ipsec.interface }}
|
||||
encrypt-interface: {{ .Values.encryption.ipsec.interface }}
|
||||
{{- else if .Values.encryption.interface }}
|
||||
encrypt-interface: {{ .Values.encryption.interface }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.encryption.nodeEncryption }}
|
||||
encrypt-node: {{ .Values.encryption.nodeEncryption | quote }}
|
||||
{{- end }}
|
||||
{{- else if eq .Values.encryption.type "wireguard" }}
|
||||
enable-wireguard: {{ .Values.encryption.enabled | quote }}
|
||||
{{- if .Values.encryption.wireguard.userspaceFallback }}
|
||||
enable-wireguard-userspace-fallback: {{ .Values.encryption.wireguard.userspaceFallback | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "datapathMode" }}
|
||||
{{- if eq .Values.datapathMode "ipvlan" }}
|
||||
datapath-mode: ipvlan
|
||||
ipvlan-master-device: {{ .Values.ipvlan.masterDevice }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.strictModeCIDR }}
|
||||
strict-mode-cidr: {{ .Values.strictModeCIDR | quote }}
|
||||
{{- end }}
|
||||
enable-xt-socket-fallback: {{ .Values.enableXTSocketFallback | quote }}
|
||||
install-iptables-rules: {{ .Values.installIptablesRules | quote }}
|
||||
{{- if or (.Values.azure.enabled) (.Values.eni.enabled) (.Values.gke.enabled) (ne .Values.cni.chainingMode "none") }}
|
||||
install-no-conntrack-iptables-rules: "false"
|
||||
{{- else }}
|
||||
install-no-conntrack-iptables-rules: {{ .Values.installNoConntrackIptablesRules | quote }}
|
||||
{{- end}}
|
||||
|
||||
{{- if hasKey .Values "iptablesRandomFully" }}
|
||||
iptables-random-fully: {{ .Values.iptablesRandomFully | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "iptablesLockTimeout" }}
|
||||
iptables-lock-timeout: {{ .Values.iptablesLockTimeout | quote }}
|
||||
{{- end }}
|
||||
|
||||
auto-direct-node-routes: {{ .Values.autoDirectNodeRoutes | quote }}
|
||||
|
||||
{{- if .Values.bandwidthManager }}
|
||||
{{- if typeIs "bool" .Values.bandwidthManager }}
|
||||
# DEPRECATED: this block should be removed in 1.13
|
||||
enable-bandwidth-manager: {{ .Values.bandwidthManager | quote }}
|
||||
{{- else }}
|
||||
{{- if .Values.bandwidthManager.enabled }}
|
||||
enable-bandwidth-manager: {{ .Values.bandwidthManager.enabled | quote }}
|
||||
enable-bbr: {{ .Values.bandwidthManager.bbr | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "localRedirectPolicy" }}
|
||||
enable-local-redirect-policy: {{ .Values.localRedirectPolicy | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "ipv4NativeRoutingCIDR" }}
|
||||
ipv4-native-routing-cidr: {{ .Values.ipv4NativeRoutingCIDR }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "ipv6NativeRoutingCIDR" }}
|
||||
ipv6-native-routing-cidr: {{ .Values.ipv6NativeRoutingCIDR }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "fragmentTracking" }}
|
||||
enable-ipv4-fragment-tracking: {{ .Values.fragmentTracking | quote }}
|
||||
{{- else if (ne $fragmentTracking "true") }}
|
||||
enable-ipv4-fragment-tracking: "false"
|
||||
{{- end }}
|
||||
|
||||
{{- if and .Values.hostFirewall .Values.hostFirewall.enabled }}
|
||||
enable-host-firewall: {{ .Values.hostFirewall.enabled | quote }}
|
||||
{{- end}}
|
||||
|
||||
{{- if hasKey .Values "devices" }}
|
||||
# List of devices used to attach bpf_host.o (implements BPF NodePort,
|
||||
# host-firewall and BPF masquerading)
|
||||
devices: {{ join " " .Values.devices | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.enableRuntimeDeviceDetection }}
|
||||
enable-runtime-device-detection: "true"
|
||||
{{- end }}
|
||||
|
||||
kube-proxy-replacement: {{ $kubeProxyReplacement | quote }}
|
||||
|
||||
{{- if ne $kubeProxyReplacement "disabled" }}
|
||||
kube-proxy-replacement-healthz-bind-address: {{ default "" .Values.kubeProxyReplacementHealthzBindAddr | quote}}
|
||||
{{- end }}
|
||||
|
||||
{{- if $socketLB }}
|
||||
{{- if hasKey $socketLB "enabled" }}
|
||||
bpf-lb-sock: {{ $socketLB.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey $socketLB "hostNamespaceOnly" }}
|
||||
bpf-lb-sock-hostns-only: {{ $socketLB.hostNamespaceOnly | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "hostServices" }}
|
||||
{{- if ne .Values.hostServices.protocols "tcp,udp" }}
|
||||
host-reachable-services-protos: {{ .Values.hostServices.protocols }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "hostPort" }}
|
||||
{{- if eq $kubeProxyReplacement "partial" }}
|
||||
enable-host-port: {{ .Values.hostPort.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "externalIPs" }}
|
||||
{{- if eq $kubeProxyReplacement "partial" }}
|
||||
enable-external-ips: {{ .Values.externalIPs.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "nodePort" }}
|
||||
{{- if eq $kubeProxyReplacement "partial" }}
|
||||
enable-node-port: {{ .Values.nodePort.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.nodePort "range" }}
|
||||
node-port-range: {{ .Values.nodePort.range | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.nodePort "directRoutingDevice" }}
|
||||
direct-routing-device: {{ .Values.nodePort.directRoutingDevice | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.nodePort "enableHealthCheck" }}
|
||||
enable-health-check-nodeport: {{ .Values.nodePort.enableHealthCheck | quote}}
|
||||
{{- end }}
|
||||
node-port-bind-protection: {{ .Values.nodePort.bindProtection | quote }}
|
||||
enable-auto-protect-node-port-range: {{ .Values.nodePort.autoProtectPortRange | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "loadBalancer" }}
|
||||
{{- if .Values.loadBalancer.standalone }}
|
||||
datapath-mode: lb-only
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.loadBalancer "mode" }}
|
||||
bpf-lb-mode: {{ .Values.loadBalancer.mode | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.loadBalancer "algorithm" }}
|
||||
bpf-lb-algorithm: {{ .Values.loadBalancer.algorithm | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.loadBalancer "acceleration" }}
|
||||
bpf-lb-acceleration: {{ .Values.loadBalancer.acceleration | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.loadBalancer "dsrDispatch" }}
|
||||
bpf-lb-dsr-dispatch: {{ .Values.loadBalancer.dsrDispatch | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.loadBalancer "serviceTopology" }}
|
||||
enable-service-topology: {{ .Values.loadBalancer.serviceTopology | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.maglev "tableSize" }}
|
||||
bpf-lb-maglev-table-size: {{ .Values.maglev.tableSize | quote}}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.maglev "hashSeed" }}
|
||||
bpf-lb-maglev-hash-seed: {{ .Values.maglev.hashSeed | quote}}
|
||||
{{- end }}
|
||||
{{- if .Values.sessionAffinity }}
|
||||
enable-session-affinity: {{ .Values.sessionAffinity | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.svcSourceRangeCheck }}
|
||||
enable-svc-source-range-check: {{ .Values.svcSourceRangeCheck | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "l2NeighDiscovery" }}
|
||||
{{- if hasKey .Values.l2NeighDiscovery "enabled" }}
|
||||
enable-l2-neigh-discovery: {{ .Values.l2NeighDiscovery.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.l2NeighDiscovery "refreshPeriod" }}
|
||||
arping-refresh-period: {{ .Values.l2NeighDiscovery.refreshPeriod | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if and .Values.pprof .Values.pprof.enabled }}
|
||||
pprof: {{ .Values.pprof.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.logSystemLoad }}
|
||||
log-system-load: {{ .Values.logSystemLoad | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.logOptions }}
|
||||
log-opt: {{ .Values.logOptions | toJson | quote }}
|
||||
{{- end }}
|
||||
{{- if and .Values.sockops .Values.sockops.enabled }}
|
||||
sockops-enable: {{ .Values.sockops.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.k8s "requireIPv4PodCIDR" }}
|
||||
k8s-require-ipv4-pod-cidr: {{ .Values.k8s.requireIPv4PodCIDR | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.k8s "requireIPv6PodCIDR" }}
|
||||
k8s-require-ipv6-pod-cidr: {{ .Values.k8s.requireIPv6PodCIDR | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.endpointStatus.enabled }}
|
||||
endpoint-status: {{ required "endpointStatus.status required: policy, health, controllers, logs and / or state. For 2 or more options use a comma: \"policy, health\"" .Values.endpointStatus.status | quote }}
|
||||
{{- end }}
|
||||
{{- if and .Values.endpointRoutes .Values.endpointRoutes.enabled }}
|
||||
enable-endpoint-routes: {{ .Values.endpointRoutes.enabled | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.cni.configMap }}
|
||||
read-cni-conf: {{ .Values.cni.confFileMountPath }}/{{ .Values.cni.configMapKey }}
|
||||
write-cni-conf-when-ready: {{ .Values.cni.hostConfDirMountPath }}/05-cilium.conflist
|
||||
{{- else if .Values.cni.readCniConf }}
|
||||
read-cni-conf: {{ .Values.cni.readCniConf }}
|
||||
{{- end }}
|
||||
{{- if .Values.kubeConfigPath }}
|
||||
k8s-kubeconfig-path: {{ .Values.kubeConfigPath | quote }}
|
||||
{{- end }}
|
||||
{{- if and ( .Values.endpointHealthChecking.enabled ) (or (eq .Values.cni.chainingMode "portmap") (eq .Values.cni.chainingMode "none")) }}
|
||||
enable-endpoint-health-checking: "true"
|
||||
{{- else}}
|
||||
# Disable health checking, when chaining mode is not set to portmap or none
|
||||
enable-endpoint-health-checking: "false"
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "healthChecking" }}
|
||||
enable-health-checking: {{ .Values.healthChecking | quote }}
|
||||
{{- end }}
|
||||
{{- if or .Values.wellKnownIdentities.enabled .Values.etcd.managed }}
|
||||
enable-well-known-identities: "true"
|
||||
{{- else }}
|
||||
enable-well-known-identities: "false"
|
||||
{{- end }}
|
||||
enable-remote-node-identity: {{ .Values.remoteNodeIdentity | quote }}
|
||||
|
||||
{{- if hasKey .Values "synchronizeK8sNodes" }}
|
||||
synchronize-k8s-nodes: {{ .Values.synchronizeK8sNodes | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "policyAuditMode" }}
|
||||
policy-audit-mode: {{ .Values.policyAuditMode | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if ne $defaultOperatorApiServeAddr "localhost:9234" }}
|
||||
operator-api-serve-addr: {{ $defaultOperatorApiServeAddr | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.hubble.enabled }}
|
||||
# Enable Hubble gRPC service.
|
||||
enable-hubble: {{ .Values.hubble.enabled | quote }}
|
||||
# UNIX domain socket for Hubble server to listen to.
|
||||
hubble-socket-path: {{ .Values.hubble.socketPath | quote }}
|
||||
{{- if hasKey .Values.hubble "eventQueueSize" }}
|
||||
# Buffer size of the channel for Hubble to receive monitor events. If this field is not set,
|
||||
# the buffer size is set to the default monitor queue size.
|
||||
hubble-event-queue-size: {{ .Values.hubble.eventQueueSize | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.hubble "flowBufferSize" }}
|
||||
# DEPRECATED: this block should be removed in 1.11
|
||||
hubble-flow-buffer-size: {{ .Values.hubble.flowBufferSize | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.hubble "eventBufferCapacity" }}
|
||||
# Capacity of the buffer to store recent events.
|
||||
hubble-event-buffer-capacity: {{ .Values.hubble.eventBufferCapacity | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.hubble.metrics.enabled }}
|
||||
# Address to expose Hubble metrics (e.g. ":7070"). Metrics server will be disabled if this
|
||||
# field is not set.
|
||||
hubble-metrics-server: ":{{ .Values.hubble.metrics.port }}"
|
||||
# A space separated list of metrics to enable. See [0] for available metrics.
|
||||
#
|
||||
# https://github.com/cilium/hubble/blob/master/Documentation/metrics.md
|
||||
hubble-metrics: {{- range .Values.hubble.metrics.enabled }}
|
||||
{{.}}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.hubble "listenAddress" }}
|
||||
# An additional address for Hubble server to listen to (e.g. ":4244").
|
||||
hubble-listen-address: {{ .Values.hubble.listenAddress | quote }}
|
||||
{{- if .Values.hubble.tls.enabled }}
|
||||
hubble-disable-tls: "false"
|
||||
hubble-tls-cert-file: /var/lib/cilium/tls/hubble/server.crt
|
||||
hubble-tls-key-file: /var/lib/cilium/tls/hubble/server.key
|
||||
hubble-tls-client-ca-files: /var/lib/cilium/tls/hubble/client-ca.crt
|
||||
{{- else }}
|
||||
hubble-disable-tls: "true"
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values "disableIptablesFeederRules" }}
|
||||
# A space separated list of iptables chains to disable when installing feeder rules.
|
||||
disable-iptables-feeder-rules: {{ .Values.disableIptablesFeederRules | join " " | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.aksbyocni.enabled }}
|
||||
ipam: "cluster-pool"
|
||||
{{- else }}
|
||||
ipam: {{ $ipam | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if or (eq $ipam "cluster-pool") (eq $ipam "cluster-pool-v2beta") }}
|
||||
{{- if .Values.ipv4.enabled }}
|
||||
{{- if .Values.ipam.operator.clusterPoolIPv4PodCIDRList }}
|
||||
cluster-pool-ipv4-cidr: {{ .Values.ipam.operator.clusterPoolIPv4PodCIDRList | join " " | quote }}
|
||||
{{- else }}
|
||||
cluster-pool-ipv4-cidr: {{ .Values.ipam.operator.clusterPoolIPv4PodCIDR | quote }}
|
||||
{{- end }}
|
||||
cluster-pool-ipv4-mask-size: {{ .Values.ipam.operator.clusterPoolIPv4MaskSize | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.ipv6.enabled }}
|
||||
{{- if .Values.ipam.operator.clusterPoolIPv6PodCIDRList }}
|
||||
cluster-pool-ipv6-cidr: {{ .Values.ipam.operator.clusterPoolIPv6PodCIDRList | join " " | quote }}
|
||||
{{- else }}
|
||||
cluster-pool-ipv6-cidr: {{ .Values.ipam.operator.clusterPoolIPv6PodCIDR | quote }}
|
||||
{{- end }}
|
||||
cluster-pool-ipv6-mask-size: {{ .Values.ipam.operator.clusterPoolIPv6MaskSize | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.enableCnpStatusUpdates }}
|
||||
disable-cnp-status-updates: {{ (not .Values.enableCnpStatusUpdates) | quote }}
|
||||
{{- else if (eq $defaultEnableCnpStatusUpdates "false") }}
|
||||
disable-cnp-status-updates: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.egressGateway.enabled }}
|
||||
enable-ipv4-egress-gateway: "true"
|
||||
{{- end }}
|
||||
{{- if .Values.egressGateway.installRoutes }}
|
||||
install-egress-gateway-routes: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "vtep" }}
|
||||
enable-vtep: {{ .Values.vtep.enabled | quote }}
|
||||
{{- if hasKey .Values.vtep "endpoint" }}
|
||||
vtep-endpoint: {{ .Values.vtep.endpoint | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.vtep "cidr" }}
|
||||
vtep-cidr: {{ .Values.vtep.cidr | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.vtep "mask" }}
|
||||
vtep-mask: {{ .Values.vtep.mask | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.vtep "mac" }}
|
||||
vtep-mac: {{ .Values.vtep.mac | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.enableK8sEventHandover }}
|
||||
enable-k8s-event-handover: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "crdWaitTimeout" }}
|
||||
crd-wait-timeout: {{ .Values.crdWaitTimeout | quote }}
|
||||
{{- else if ( ne $crdWaitTimeout "5m" ) }}
|
||||
crd-wait-timeout: {{ $crdWaitTimeout | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.enableK8sEndpointSlice }}
|
||||
enable-k8s-endpoint-slice: {{ .Values.enableK8sEndpointSlice | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.k8s "serviceProxyName" }}
|
||||
# Configure service proxy name for Cilium.
|
||||
k8s-service-proxy-name: {{ .Values.k8s.serviceProxyName | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if and .Values.customCalls .Values.customCalls.enabled }}
|
||||
# Enable tail call hooks for custom eBPF programs.
|
||||
enable-custom-calls: {{ .Values.customCalls.enabled | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if and .Values.bgp.enabled (and (not .Values.bgp.announce.loadbalancerIP) (not .Values.bgp.announce.podCIDR)) }}
|
||||
{{ fail "BGP was enabled, but no announcements were enabled. Please enable one or more announcements." }}
|
||||
{{- end }}
|
||||
|
||||
{{- if and .Values.bgp.enabled .Values.bgp.announce.loadbalancerIP }}
|
||||
bgp-announce-lb-ip: {{ .Values.bgp.announce.loadbalancerIP | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if and .Values.bgp.enabled .Values.bgp.announce.podCIDR }}
|
||||
bgp-announce-pod-cidr: {{ .Values.bgp.announce.podCIDR | quote }}
|
||||
{{- end}}
|
||||
|
||||
{{- if .Values.bgpControlPlane.enabled }}
|
||||
enable-bgp-control-plane: "true"
|
||||
{{- else }}
|
||||
enable-bgp-control-plane: "false"
|
||||
{{- end }}
|
||||
|
||||
{{- if not .Values.securityContext.privileged }}
|
||||
procfs: "/host/proc"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.bpf "root" }}
|
||||
bpf-root: {{ .Values.bpf.root | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.cgroup "hostRoot" }}
|
||||
cgroup-root: {{ .Values.cgroup.hostRoot | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values.bpf "vlanBypass" }}
|
||||
# A space separated list of explicitly allowed vlan id's
|
||||
vlan-bpf-bypass: {{ .Values.bpf.vlanBypass | join " " | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.enableCiliumEndpointSlice }}
|
||||
enable-cilium-endpoint-slice: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "enableK8sTerminatingEndpoint" }}
|
||||
enable-k8s-terminating-endpoint: {{ .Values.enableK8sTerminatingEndpoint | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "dnsPolicyUnloadOnShutdown" }}
|
||||
# Unload DNS policy rules on graceful shutdown
|
||||
dns-policy-unload-on-shutdown: {{.Values.dnsPolicyUnloadOnShutdown | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.annotateK8sNode }}
|
||||
annotate-k8s-node: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.operator.removeNodeTaints }}
|
||||
remove-cilium-node-taints: "true"
|
||||
{{- end }}
|
||||
{{- if .Values.operator.setNodeNetworkStatus }}
|
||||
set-cilium-is-up-condition: "true"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.operator.unmanagedPodWatcher.restart }}
|
||||
unmanaged-pod-watcher-interval: {{ .Values.operator.unmanagedPodWatcher.intervalSeconds | quote }}
|
||||
{{- else }}
|
||||
unmanaged-pod-watcher-interval: "0"
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.dnsProxy }}
|
||||
{{- if .Values.dnsProxy.dnsRejectResponseCode }}
|
||||
tofqdns-dns-reject-response-code: {{ .Values.dnsProxy.dnsRejectResponseCode | quote }}
|
||||
{{- end }}
|
||||
{{- if hasKey .Values.dnsProxy "enableDnsCompression" }}
|
||||
tofqdns-enable-dns-compression: {{ .Values.dnsProxy.enableDnsCompression | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.endpointMaxIpPerHostname }}
|
||||
tofqdns-endpoint-max-ip-per-hostname: {{ .Values.dnsProxy.endpointMaxIpPerHostname | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.idleConnectionGracePeriod }}
|
||||
tofqdns-idle-connection-grace-period: {{ .Values.dnsProxy.idleConnectionGracePeriod | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.maxDeferredConnectionDeletes }}
|
||||
tofqdns-max-deferred-connection-deletes: {{ .Values.dnsProxy.maxDeferredConnectionDeletes | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.minTtl }}
|
||||
tofqdns-min-ttl: {{ .Values.dnsProxy.minTtl | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.preCache }}
|
||||
tofqdns-pre-cache: {{ .Values.dnsProxy.preCache | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.proxyPort }}
|
||||
tofqdns-proxy-port: {{ .Values.dnsProxy.proxyPort | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.proxyResponseMaxDelay }}
|
||||
tofqdns-proxy-response-max-delay: {{ .Values.dnsProxy.proxyResponseMaxDelay | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.extraConfig }}
|
||||
{{ toYaml .Values.extraConfig | nindent 2 }}
|
||||
{{- end }}
|
||||
|
||||
{{- if hasKey .Values "agentNotReadyTaintKey" }}
|
||||
agent-not-ready-taint-key: {{ .Values.agentNotReadyTaintKey | quote }}
|
||||
{{- end }}
|
||||
|
||||
{{- end }}
|
||||
@ -0,0 +1,8 @@
|
||||
{{- if .Values.ingressController.enabled -}}
|
||||
apiVersion: networking.k8s.io/v1
|
||||
kind: IngressClass
|
||||
metadata:
|
||||
name: cilium
|
||||
spec:
|
||||
controller: cilium.io/ingress-controller
|
||||
{{- end}}
|
||||
@ -0,0 +1,111 @@
|
||||
{{- if .Values.nodeinit.enabled }}
|
||||
---
|
||||
kind: DaemonSet
|
||||
apiVersion: apps/v1
|
||||
metadata:
|
||||
name: cilium-node-init
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
app: cilium-node-init
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
app: cilium-node-init
|
||||
{{- with .Values.nodeinit.updateStrategy }}
|
||||
updateStrategy:
|
||||
{{- toYaml . | trim | nindent 4 }}
|
||||
{{- end }}
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
{{- with .Values.nodeinit.podAnnotations }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if not .Values.securityContext.privileged }}
|
||||
# Set app AppArmor's profile to "unconfined". The value of this annotation
|
||||
# can be modified as long users know which profiles they have available
|
||||
# in AppArmor.
|
||||
container.apparmor.security.beta.kubernetes.io/node-init: "unconfined"
|
||||
{{- end }}
|
||||
labels:
|
||||
app: cilium-node-init
|
||||
{{- with .Values.nodeinit.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
volumes:
|
||||
# To access iptables concurrently with other processes (e.g. kube-proxy)
|
||||
- hostPath:
|
||||
path: /run/xtables.lock
|
||||
type: FileOrCreate
|
||||
name: xtables-lock
|
||||
containers:
|
||||
- name: node-init
|
||||
image: {{ include "cilium.image" .Values.nodeinit.image | quote }}
|
||||
imagePullPolicy: {{ .Values.nodeinit.image.pullPolicy }}
|
||||
volumeMounts:
|
||||
# To access iptables concurrently with other processes (e.g. kube-proxy)
|
||||
- mountPath: /run/xtables.lock
|
||||
name: xtables-lock
|
||||
lifecycle:
|
||||
{{- if .Values.eni.enabled }}
|
||||
postStart:
|
||||
exec:
|
||||
command:
|
||||
- "/bin/sh"
|
||||
- "-c"
|
||||
- |
|
||||
{{- tpl (.Files.Get "files/nodeinit/poststart-eni.bash") . | nindent 20 }}
|
||||
{{- end }}
|
||||
{{- if .Values.nodeinit.revertReconfigureKubelet }}
|
||||
preStop:
|
||||
exec:
|
||||
command:
|
||||
- nsenter
|
||||
- --target=1
|
||||
- --mount
|
||||
- --
|
||||
- /bin/sh
|
||||
- -c
|
||||
- |
|
||||
{{- tpl (.Files.Get "files/nodeinit/prestop.bash") . | nindent 20 }}
|
||||
{{- end }}
|
||||
env:
|
||||
{{- with .Values.nodeinit.extraEnv }}
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
# STARTUP_SCRIPT is the script run on node bootstrap. Node
|
||||
# bootstrapping can be customized in this script. This script is invoked
|
||||
# using nsenter, so it runs in the host's network and mount namespace using
|
||||
# the host's userland tools!
|
||||
- name: STARTUP_SCRIPT
|
||||
value: |
|
||||
{{- tpl (.Files.Get "files/nodeinit/startup.bash") . | nindent 14 }}
|
||||
{{- with .Values.nodeinit.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- with .Values.nodeinit.securityContext }}
|
||||
securityContext:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- with .Values.nodeinit.affinity }}
|
||||
affinity:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.nodeinit.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.nodeinit.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
hostPID: true
|
||||
hostNetwork: true
|
||||
priorityClassName: {{ include "cilium.priorityClass" (list $ .Values.nodeinit.priorityClassName "system-node-critical") }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,36 @@
|
||||
{{- define "cilium.operator.cloud" -}}
|
||||
{{- $cloud := "generic" -}}
|
||||
{{- if .Values.eni.enabled -}}
|
||||
{{- $cloud = "aws" -}}
|
||||
{{- else if .Values.azure.enabled -}}
|
||||
{{- $cloud = "azure" -}}
|
||||
{{- else if .Values.alibabacloud.enabled -}}
|
||||
{{- $cloud = "alibabacloud" -}}
|
||||
{{- end -}}
|
||||
{{- $cloud -}}
|
||||
{{- end -}}
|
||||
|
||||
{{- define "cilium.operator.imageDigestName" -}}
|
||||
{{- $imageDigest := (.Values.operator.image.useDigest | default false) | ternary (printf "@%s" .Values.operator.image.genericDigest) "" -}}
|
||||
{{- if .Values.eni.enabled -}}
|
||||
{{- $imageDigest = (.Values.operator.image.useDigest | default false) | ternary (printf "@%s" .Values.operator.image.awsDigest) "" -}}
|
||||
{{- else if .Values.azure.enabled -}}
|
||||
{{- $imageDigest = (.Values.operator.image.useDigest | default false) | ternary (printf "@%s" .Values.operator.image.azureDigest) "" -}}
|
||||
{{- else if .Values.alibabacloud.enabled -}}
|
||||
{{- $imageDigest = (.Values.operator.image.useDigest | default false) | ternary (printf "@%s" .Values.operator.image.alibabacloudDigest) "" -}}
|
||||
{{- end -}}
|
||||
{{- $imageDigest -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return cilium operator image
|
||||
*/}}
|
||||
{{- define "cilium.operator.image" -}}
|
||||
{{- if .Values.operator.image.override -}}
|
||||
{{- printf "%s" .Values.operator.image.override -}}
|
||||
{{- else -}}
|
||||
{{- $cloud := include "cilium.operator.cloud" . }}
|
||||
{{- $imageDigest := include "cilium.operator.imageDigestName" . }}
|
||||
{{- printf "%s-%s%s:%s%s" .Values.operator.image.repository $cloud .Values.operator.image.suffix .Values.operator.image.tag $imageDigest -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
@ -0,0 +1,225 @@
|
||||
{{- if and .Values.operator.enabled .Values.serviceAccounts.operator.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRole
|
||||
metadata:
|
||||
name: cilium-operator
|
||||
rules:
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- pods
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
{{- if hasKey .Values "disableEndpointCRD" }}
|
||||
{{- if (eq (.Values.disableEndpointCRD | quote ) ( "false" | quote )) }}
|
||||
{{- if (and .Values.operator.unmanagedPodWatcher.restart (ne (.Values.operator.unmanagedPodWatcher.intervalSeconds | int64) 0 ) ) }}
|
||||
# to automatically delete [core|kube]dns pods so that are starting to being
|
||||
# managed by Cilium
|
||||
- delete
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if or .Values.operator.removeNodeTaints .Values.operator.setNodeNetworkStatus .Values.operator.endpointGCInterval }}
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- nodes
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
{{- end }}
|
||||
{{- if or .Values.operator.removeNodeTaints .Values.operator.setNodeNetworkStatus }}
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
{{- if .Values.operator.removeNodeTaints }}
|
||||
# To remove node taints
|
||||
- nodes
|
||||
{{- end }}
|
||||
{{- if .Values.operator.setNodeNetworkStatus }}
|
||||
# To set NetworkUnavailable false on startup
|
||||
- nodes/status
|
||||
{{- end }}
|
||||
verbs:
|
||||
- patch
|
||||
{{- end }}
|
||||
- apiGroups:
|
||||
- discovery.k8s.io
|
||||
resources:
|
||||
- endpointslices
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
# to perform LB IP allocation for BGP
|
||||
- services/status
|
||||
verbs:
|
||||
- update
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
# to check apiserver connectivity
|
||||
- namespaces
|
||||
{{- if .Values.ingressController.enabled }}
|
||||
- secrets
|
||||
{{- end }}
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
# to perform the translation of a CNP that contains `ToGroup` to its endpoints
|
||||
- services
|
||||
- endpoints
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
{{- if .Values.ingressController.enabled }}
|
||||
- create
|
||||
- update
|
||||
- delete
|
||||
{{- end }}
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnetworkpolicies
|
||||
- ciliumclusterwidenetworkpolicies
|
||||
verbs:
|
||||
# Create auto-generated CNPs and CCNPs from Policies that have 'toGroups'
|
||||
- create
|
||||
- update
|
||||
- deletecollection
|
||||
# To update the status of the CNPs and CCNPs
|
||||
- patch
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnetworkpolicies/status
|
||||
- ciliumclusterwidenetworkpolicies/status
|
||||
verbs:
|
||||
# Update the auto-generated CNPs and CCNPs status.
|
||||
- patch
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumendpoints
|
||||
- ciliumidentities
|
||||
verbs:
|
||||
# To perform garbage collection of such resources
|
||||
- delete
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumidentities
|
||||
verbs:
|
||||
# To synchronize garbage collection of such resources
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnodes
|
||||
verbs:
|
||||
- create
|
||||
- update
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
{{- if .Values.operator.nodeGCInterval }}
|
||||
{{- if ne .Values.operator.nodeGCInterval "0s" }}
|
||||
# To perform CiliumNode garbage collector
|
||||
- delete
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnodes/status
|
||||
verbs:
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumendpointslices
|
||||
- ciliumenvoyconfigs
|
||||
verbs:
|
||||
- create
|
||||
- update
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- delete
|
||||
- apiGroups:
|
||||
- apiextensions.k8s.io
|
||||
resources:
|
||||
- customresourcedefinitions
|
||||
verbs:
|
||||
- create
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- apiextensions.k8s.io
|
||||
resources:
|
||||
- customresourcedefinitions
|
||||
verbs:
|
||||
- update
|
||||
resourceNames:
|
||||
- ciliumbgploadbalancerippools.cilium.io
|
||||
- ciliumbgppeeringpolicies.cilium.io
|
||||
- ciliumclusterwideenvoyconfigs.cilium.io
|
||||
- ciliumclusterwidenetworkpolicies.cilium.io
|
||||
- ciliumegressgatewaypolicies.cilium.io
|
||||
- ciliumegressnatpolicies.cilium.io
|
||||
- ciliumendpoints.cilium.io
|
||||
- ciliumendpointslices.cilium.io
|
||||
- ciliumenvoyconfigs.cilium.io
|
||||
- ciliumexternalworkloads.cilium.io
|
||||
- ciliumidentities.cilium.io
|
||||
- ciliumlocalredirectpolicies.cilium.io
|
||||
- ciliumnetworkpolicies.cilium.io
|
||||
- ciliumnodes.cilium.io
|
||||
# For cilium-operator running in HA mode.
|
||||
#
|
||||
# Cilium operator running in HA mode requires the use of ResourceLock for Leader Election
|
||||
# between multiple running instances.
|
||||
# The preferred way of doing this is to use LeasesResourceLock as edits to Leases are less
|
||||
# common and fewer objects in the cluster watch "all Leases".
|
||||
- apiGroups:
|
||||
- coordination.k8s.io
|
||||
resources:
|
||||
- leases
|
||||
verbs:
|
||||
- create
|
||||
- get
|
||||
- update
|
||||
{{- if .Values.ingressController.enabled }}
|
||||
- apiGroups:
|
||||
- networking.k8s.io
|
||||
resources:
|
||||
- ingresses
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- networking.k8s.io
|
||||
resources:
|
||||
- ingresses/status # To update ingress status with load balancer IP.
|
||||
verbs:
|
||||
- update
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and .Values.operator.enabled .Values.serviceAccounts.operator.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRoleBinding
|
||||
metadata:
|
||||
name: cilium-operator
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: ClusterRole
|
||||
name: cilium-operator
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.operator.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,278 @@
|
||||
{{- if .Values.operator.enabled }}
|
||||
---
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: cilium-operator
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
spec:
|
||||
# See docs on ServerCapabilities.LeasesResourceLock in file pkg/k8s/version/version.go
|
||||
# for more details.
|
||||
replicas: {{ .Values.operator.replicas }}
|
||||
selector:
|
||||
matchLabels:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
{{- with .Values.operator.updateStrategy }}
|
||||
strategy:
|
||||
{{- toYaml . | trim | nindent 4 }}
|
||||
{{- end }}
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
{{- if .Values.operator.rollOutPods }}
|
||||
# ensure pods roll when configmap updates
|
||||
cilium.io/cilium-configmap-checksum: {{ include (print $.Template.BasePath "/cilium-configmap.yaml") . | sha256sum | quote }}
|
||||
{{- end }}
|
||||
{{- if and .Values.operator.prometheus.enabled (not .Values.operator.prometheus.serviceMonitor.enabled) }}
|
||||
prometheus.io/port: {{ .Values.operator.prometheus.port | quote }}
|
||||
prometheus.io/scrape: "true"
|
||||
{{- end }}
|
||||
{{- with .Values.operator.podAnnotations }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
{{- with .Values.operator.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
containers:
|
||||
- name: cilium-operator
|
||||
image: {{ include "cilium.operator.image" . }}
|
||||
imagePullPolicy: {{ .Values.operator.image.pullPolicy }}
|
||||
command:
|
||||
- cilium-operator-{{ include "cilium.operator.cloud" . }}
|
||||
args:
|
||||
- --config-dir=/tmp/cilium/config-map
|
||||
- --debug=$(CILIUM_DEBUG)
|
||||
{{- with .Values.operator.extraArgs }}
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
env:
|
||||
- name: K8S_NODE_NAME
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: spec.nodeName
|
||||
- name: CILIUM_K8S_NAMESPACE
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: metadata.namespace
|
||||
- name: CILIUM_DEBUG
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
key: debug
|
||||
name: cilium-config
|
||||
optional: true
|
||||
{{- if and .Values.eni.enabled (not .Values.eni.iamRole ) }}
|
||||
- name: AWS_ACCESS_KEY_ID
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: cilium-aws
|
||||
key: AWS_ACCESS_KEY_ID
|
||||
optional: true
|
||||
- name: AWS_SECRET_ACCESS_KEY
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: cilium-aws
|
||||
key: AWS_SECRET_ACCESS_KEY
|
||||
optional: true
|
||||
- name: AWS_DEFAULT_REGION
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: cilium-aws
|
||||
key: AWS_DEFAULT_REGION
|
||||
optional: true
|
||||
{{- end }}
|
||||
{{- if .Values.alibabacloud.enabled }}
|
||||
- name: ALIBABA_CLOUD_ACCESS_KEY_ID
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: cilium-alibabacloud
|
||||
key: ALIBABA_CLOUD_ACCESS_KEY_ID
|
||||
optional: true
|
||||
- name: ALIBABA_CLOUD_ACCESS_KEY_SECRET
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: cilium-alibabacloud
|
||||
key: ALIBABA_CLOUD_ACCESS_KEY_SECRET
|
||||
optional: true
|
||||
{{- end }}
|
||||
{{- if .Values.k8sServiceHost }}
|
||||
- name: KUBERNETES_SERVICE_HOST
|
||||
value: {{ .Values.k8sServiceHost | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.k8sServicePort }}
|
||||
- name: KUBERNETES_SERVICE_PORT
|
||||
value: {{ .Values.k8sServicePort | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.azure.enabled }}
|
||||
{{- if .Values.azure.subscriptionID }}
|
||||
- name: AZURE_SUBSCRIPTION_ID
|
||||
value: {{ .Values.azure.subscriptionID }}
|
||||
{{- end }}
|
||||
{{- if .Values.azure.tenantID }}
|
||||
- name: AZURE_TENANT_ID
|
||||
value: {{ .Values.azure.tenantID }}
|
||||
{{- end }}
|
||||
{{- if .Values.azure.resourceGroup }}
|
||||
- name: AZURE_RESOURCE_GROUP
|
||||
value: {{ .Values.azure.resourceGroup }}
|
||||
{{- end }}
|
||||
- name: AZURE_CLIENT_ID
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: cilium-azure
|
||||
key: AZURE_CLIENT_ID
|
||||
- name: AZURE_CLIENT_SECRET
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: cilium-azure
|
||||
key: AZURE_CLIENT_SECRET
|
||||
{{- end }}
|
||||
{{- with .Values.operator.extraEnv }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.operator.prometheus.enabled }}
|
||||
ports:
|
||||
- name: prometheus
|
||||
containerPort: {{ .Values.operator.prometheus.port }}
|
||||
hostPort: {{ .Values.operator.prometheus.port }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
livenessProbe:
|
||||
httpGet:
|
||||
host: {{ .Values.ipv4.enabled | ternary "127.0.0.1" "::1" | quote }}
|
||||
path: /healthz
|
||||
port: 9234
|
||||
scheme: HTTP
|
||||
initialDelaySeconds: 60
|
||||
periodSeconds: 10
|
||||
timeoutSeconds: 3
|
||||
volumeMounts:
|
||||
- name: cilium-config-path
|
||||
mountPath: /tmp/cilium/config-map
|
||||
readOnly: true
|
||||
{{- if .Values.etcd.enabled }}
|
||||
- name: etcd-config-path
|
||||
mountPath: /var/lib/etcd-config
|
||||
readOnly: true
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
- name: etcd-secrets
|
||||
mountPath: /var/lib/etcd-secrets
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.kubeConfigPath }}
|
||||
- name: kube-config
|
||||
mountPath: {{ .Values.kubeConfigPath }}
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- range .Values.operator.extraHostPathMounts }}
|
||||
- name: {{ .name }}
|
||||
mountPath: {{ .mountPath }}
|
||||
readOnly: {{ .readOnly }}
|
||||
{{- if .mountPropagation }}
|
||||
mountPropagation: {{ .mountPropagation }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.bgp.enabled }}
|
||||
- name: bgp-config-path
|
||||
mountPath: /var/lib/cilium/bgp
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- with .Values.operator.extraVolumeMounts }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.operator.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
{{- with .Values.operator.securityContext }}
|
||||
securityContext:
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
hostNetwork: true
|
||||
{{- if and .Values.etcd.managed (not .Values.etcd.k8sService) }}
|
||||
# In managed etcd mode, Cilium must be able to resolve the DNS name of
|
||||
# the etcd service
|
||||
dnsPolicy: ClusterFirstWithHostNet
|
||||
{{- else if .Values.dnsPolicy }}
|
||||
dnsPolicy: {{ .Values.operator.dnsPolicy }}
|
||||
{{- end }}
|
||||
restartPolicy: Always
|
||||
priorityClassName: {{ include "cilium.priorityClass" (list $ .Values.operator.priorityClassName "system-cluster-critical") }}
|
||||
serviceAccount: {{ .Values.serviceAccounts.operator.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.operator.name | quote }}
|
||||
{{- with .Values.operator.affinity }}
|
||||
# In HA mode, cilium-operator pods must not be scheduled on the same
|
||||
# node as they will clash with each other.
|
||||
affinity:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.operator.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.operator.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
volumes:
|
||||
# To read the configuration from the config map
|
||||
- name: cilium-config-path
|
||||
configMap:
|
||||
name: cilium-config
|
||||
{{- if .Values.etcd.enabled }}
|
||||
# To read the etcd config stored in config maps
|
||||
- name: etcd-config-path
|
||||
configMap:
|
||||
name: cilium-config
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
items:
|
||||
- key: etcd-config
|
||||
path: etcd.config
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
# To read the k8s etcd secrets in case the user might want to use TLS
|
||||
- name: etcd-secrets
|
||||
secret:
|
||||
secretName: cilium-etcd-secrets
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
optional: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.kubeConfigPath }}
|
||||
- name: kube-config
|
||||
hostPath:
|
||||
path: {{ .Values.kubeConfigPath }}
|
||||
type: FileOrCreate
|
||||
{{- end }}
|
||||
{{- range .Values.operator.extraHostPathMounts }}
|
||||
- name: {{ .name }}
|
||||
hostPath:
|
||||
path: {{ .hostPath }}
|
||||
{{- if .hostPathType }}
|
||||
type: {{ .hostPathType }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.bgp.enabled }}
|
||||
- name: bgp-config-path
|
||||
configMap:
|
||||
name: bgp-config
|
||||
{{- end }}
|
||||
{{- with .Values.operator.extraVolumes }}
|
||||
{{- toYaml . | nindent 6 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,22 @@
|
||||
{{- if and .Values.operator.enabled .Values.operator.podDisruptionBudget.enabled }}
|
||||
{{- $component := .Values.operator.podDisruptionBudget }}
|
||||
apiVersion: {{ include "podDisruptionBudget.apiVersion" . }}
|
||||
kind: PodDisruptionBudget
|
||||
metadata:
|
||||
name: cilium-operator
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
spec:
|
||||
{{- with $component.maxUnavailable }}
|
||||
maxUnavailable: {{ . }}
|
||||
{{- end }}
|
||||
{{- with $component.minAvailable }}
|
||||
minAvailable: {{ . }}
|
||||
{{- end }}
|
||||
selector:
|
||||
matchLabels:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
{{- end }}
|
||||
@ -0,0 +1,16 @@
|
||||
{{- if and .Values.operator.enabled .Values.serviceAccounts.operator.create .Values.ingressController.enabled .Values.ingressController.secretsNamespace.sync .Values.ingressController.secretsNamespace.name }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: Role
|
||||
metadata:
|
||||
name: cilium-operator-secrets
|
||||
namespace: {{ .Values.ingressController.secretsNamespace.name | quote }}
|
||||
rules:
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
verbs:
|
||||
- create
|
||||
- delete
|
||||
- update
|
||||
{{- end }}
|
||||
@ -0,0 +1,15 @@
|
||||
{{- if and .Values.operator.enabled .Values.serviceAccounts.operator.create .Values.ingressController.enabled .Values.ingressController.secretsNamespace.sync .Values.ingressController.secretsNamespace.name }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: RoleBinding
|
||||
metadata:
|
||||
name: cilium-operator-secrets
|
||||
namespace: {{ .Values.ingressController.secretsNamespace.name | quote }}
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: Role
|
||||
name: cilium-operator-secrets
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.operator.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,13 @@
|
||||
{{- if .Values.operator.enabled }}
|
||||
{{- if .Values.azure.enabled }}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: cilium-azure
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: Opaque
|
||||
data:
|
||||
AZURE_CLIENT_ID: {{ default "" .Values.azure.clientID | b64enc | quote }}
|
||||
AZURE_CLIENT_SECRET: {{ default "" .Values.azure.clientSecret | b64enc | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,21 @@
|
||||
{{- if and .Values.operator.enabled .Values.operator.prometheus.enabled .Values.operator.prometheus.serviceMonitor.enabled }}
|
||||
kind: Service
|
||||
apiVersion: v1
|
||||
metadata:
|
||||
name: cilium-operator
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
spec:
|
||||
clusterIP: None
|
||||
type: ClusterIP
|
||||
ports:
|
||||
- name: metrics
|
||||
port: 9963
|
||||
protocol: TCP
|
||||
targetPort: prometheus
|
||||
selector:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
{{- end }}
|
||||
@ -0,0 +1,15 @@
|
||||
{{- if and .Values.operator.enabled .Values.serviceAccounts.operator.create }}
|
||||
{{- if and .Values.eni.enabled .Values.eni.iamRole }}
|
||||
{{ $_ := set .Values.serviceAccounts.operator.annotations "eks.amazonaws.com/role-arn" .Values.eni.iamRole }}
|
||||
{{- end}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ .Values.serviceAccounts.operator.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- if .Values.serviceAccounts.operator.annotations }}
|
||||
annotations:
|
||||
{{- toYaml .Values.serviceAccounts.operator.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,30 @@
|
||||
{{- if and .Values.operator.enabled .Values.operator.prometheus.enabled .Values.operator.prometheus.serviceMonitor.enabled }}
|
||||
apiVersion: monitoring.coreos.com/v1
|
||||
kind: ServiceMonitor
|
||||
metadata:
|
||||
name: cilium-operator
|
||||
namespace: {{ .Values.operator.prometheus.serviceMonitor.namespace | default .Release.Namespace }}
|
||||
labels:
|
||||
{{- with .Values.operator.prometheus.serviceMonitor.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
annotations:
|
||||
{{- with .Values.operator.prometheus.serviceMonitor.annotations }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
io.cilium/app: operator
|
||||
name: cilium-operator
|
||||
namespaceSelector:
|
||||
matchNames:
|
||||
- {{ .Release.Namespace }}
|
||||
endpoints:
|
||||
- port: metrics
|
||||
interval: 10s
|
||||
honorLabels: true
|
||||
path: /metrics
|
||||
targetLabels:
|
||||
- io.cilium/app
|
||||
{{- end }}
|
||||
@ -0,0 +1,124 @@
|
||||
{{- if .Values.preflight.enabled }}
|
||||
{{- /*
|
||||
Keep file in sync with cilium-agent/clusterrole.yaml
|
||||
*/ -}}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRole
|
||||
metadata:
|
||||
name: cilium-pre-flight
|
||||
rules:
|
||||
- apiGroups:
|
||||
- networking.k8s.io
|
||||
resources:
|
||||
- networkpolicies
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- discovery.k8s.io
|
||||
resources:
|
||||
- endpointslices
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- namespaces
|
||||
- services
|
||||
- pods
|
||||
- endpoints
|
||||
- nodes
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
{{- if .Values.annotateK8sNode }}
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- nodes/status
|
||||
verbs:
|
||||
# To annotate the k8s node with Cilium's metadata
|
||||
- patch
|
||||
{{- end }}
|
||||
- apiGroups:
|
||||
- apiextensions.k8s.io
|
||||
resources:
|
||||
- customresourcedefinitions
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
# This is used when validating policies in preflight. This will need to stay
|
||||
# until we figure out how to avoid "get" inside the preflight, and then
|
||||
# should be removed ideally.
|
||||
- get
|
||||
{{- if eq "k8s" .Values.tls.secretsBackend }}
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
verbs:
|
||||
- get
|
||||
{{- end }}
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumbgploadbalancerippools
|
||||
- ciliumbgppeeringpolicies
|
||||
- ciliumclusterwideenvoyconfigs
|
||||
- ciliumclusterwidenetworkpolicies
|
||||
- ciliumegressgatewaypolicies
|
||||
- ciliumegressnatpolicies
|
||||
- ciliumendpoints
|
||||
- ciliumendpointslices
|
||||
- ciliumenvoyconfigs
|
||||
- ciliumidentities
|
||||
- ciliumlocalredirectpolicies
|
||||
- ciliumnetworkpolicies
|
||||
- ciliumnodes
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumidentities
|
||||
- ciliumendpoints
|
||||
- ciliumnodes
|
||||
verbs:
|
||||
- create
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
# To synchronize garbage collection of such resources
|
||||
resources:
|
||||
- ciliumidentities
|
||||
verbs:
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumendpoints
|
||||
verbs:
|
||||
- delete
|
||||
- get
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnodes
|
||||
- ciliumnodes/status
|
||||
verbs:
|
||||
- get
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnetworkpolicies/status
|
||||
- ciliumclusterwidenetworkpolicies/status
|
||||
- ciliumendpoints/status
|
||||
- ciliumendpoints
|
||||
verbs:
|
||||
- patch
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and .Values.preflight.enabled .Values.serviceAccounts.preflight.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRoleBinding
|
||||
metadata:
|
||||
name: cilium-pre-flight
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: ClusterRole
|
||||
name: cilium-pre-flight
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.preflight.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,188 @@
|
||||
{{- if .Values.preflight.enabled }}
|
||||
apiVersion: apps/v1
|
||||
kind: DaemonSet
|
||||
metadata:
|
||||
name: cilium-pre-flight-check
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: cilium-pre-flight-check
|
||||
kubernetes.io/cluster-service: "true"
|
||||
template:
|
||||
metadata:
|
||||
{{- with .Values.preflight.podAnnotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
k8s-app: cilium-pre-flight-check
|
||||
kubernetes.io/cluster-service: "true"
|
||||
{{- with .Values.preflight.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 6 }}
|
||||
{{- end }}
|
||||
initContainers:
|
||||
- name: clean-cilium-state
|
||||
image: {{ include "cilium.image" .Values.preflight.image | quote }}
|
||||
imagePullPolicy: {{ .Values.preflight.image.pullPolicy }}
|
||||
command: ["/bin/echo"]
|
||||
args:
|
||||
- "hello"
|
||||
containers:
|
||||
- name: cilium-pre-flight-check
|
||||
image: {{ include "cilium.image" .Values.preflight.image | quote }}
|
||||
imagePullPolicy: {{ .Values.preflight.image.pullPolicy }}
|
||||
command: ["/bin/sh"]
|
||||
args:
|
||||
- -c
|
||||
- "touch /tmp/ready; sleep 1h"
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- cat
|
||||
- /tmp/ready
|
||||
initialDelaySeconds: 5
|
||||
periodSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- cat
|
||||
- /tmp/ready
|
||||
initialDelaySeconds: 5
|
||||
periodSeconds: 5
|
||||
{{- with .Values.preflight.extraEnv }}
|
||||
env:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: cilium-run
|
||||
mountPath: /var/run/cilium
|
||||
{{- if .Values.etcd.enabled }}
|
||||
- name: etcd-config-path
|
||||
mountPath: /var/lib/etcd-config
|
||||
readOnly: true
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
- name: etcd-secrets
|
||||
mountPath: /var/lib/etcd-secrets
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.securityContext }}
|
||||
securityContext:
|
||||
{{- toYaml . | trim | nindent 14 }}
|
||||
{{- end }}
|
||||
{{- if ne .Values.preflight.tofqdnsPreCache "" }}
|
||||
- name: cilium-pre-flight-fqdn-precache
|
||||
image: {{ include "cilium.image" .Values.preflight.image | quote }}
|
||||
imagePullPolicy: {{ .Values.preflight.image.pullPolicy }}
|
||||
name: cilium-pre-flight-fqdn-precache
|
||||
command: ["/bin/sh"]
|
||||
args:
|
||||
- -ec
|
||||
- |
|
||||
cilium preflight fqdn-poller --tofqdns-pre-cache {{ .Values.preflight.tofqdnsPreCache }};
|
||||
touch /tmp/ready-tofqdns-precache;
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- cat
|
||||
- /tmp/read-tofqdns-precachey
|
||||
initialDelaySeconds: 5
|
||||
periodSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- cat
|
||||
- /tmp/read-tofqdns-precachey
|
||||
initialDelaySeconds: 5
|
||||
periodSeconds: 5
|
||||
env:
|
||||
{{- if .Values.k8sServiceHost }}
|
||||
- name: KUBERNETES_SERVICE_HOST
|
||||
value: {{ .Values.k8sServiceHost | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.k8sServicePort }}
|
||||
- name: KUBERNETES_SERVICE_PORT
|
||||
value: {{ .Values.k8sServicePort | quote }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: cilium-run
|
||||
mountPath: /var/run/cilium
|
||||
{{- if .Values.etcd.enabled }}
|
||||
- name: etcd-config-path
|
||||
mountPath: /var/lib/etcd-config
|
||||
readOnly: true
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
- name: etcd-secrets
|
||||
mountPath: /var/lib/etcd-secrets
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.extraEnv }}
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.securityContext }}
|
||||
securityContext:
|
||||
{{- toYaml . | trim | nindent 14 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
hostNetwork: true
|
||||
# This is here to seamlessly allow migrate-identity to work with
|
||||
# etcd-operator setups. The assumption is that other cases would also
|
||||
# work since the cluster DNS would forward the request on.
|
||||
# This differs from the cilium-agent daemonset, where this is only
|
||||
# enabled when etcd.managed=true
|
||||
dnsPolicy: ClusterFirstWithHostNet
|
||||
restartPolicy: Always
|
||||
priorityClassName: {{ include "cilium.priorityClass" (list $ .Values.preflight.priorityClassName "system-node-critical") }}
|
||||
serviceAccount: {{ .Values.serviceAccounts.preflight.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.preflight.name | quote }}
|
||||
terminationGracePeriodSeconds: {{ .Values.preflight.terminationGracePeriodSeconds }}
|
||||
{{- with .Values.preflight.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
volumes:
|
||||
# To keep state between restarts / upgrades
|
||||
- name: cilium-run
|
||||
hostPath:
|
||||
path: /var/run/cilium
|
||||
type: DirectoryOrCreate
|
||||
- name: bpf-maps
|
||||
hostPath:
|
||||
path: /sys/fs/bpf
|
||||
type: DirectoryOrCreate
|
||||
{{- if .Values.etcd.enabled }}
|
||||
# To read the etcd config stored in config maps
|
||||
- name: etcd-config-path
|
||||
configMap:
|
||||
name: cilium-config
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
items:
|
||||
- key: etcd-config
|
||||
path: etcd.config
|
||||
# To read the k8s etcd secrets in case the user might want to use TLS
|
||||
{{- if or .Values.etcd.ssl .Values.etcd.managed }}
|
||||
- name: etcd-secrets
|
||||
secret:
|
||||
secretName: cilium-etcd-secrets
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
optional: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,88 @@
|
||||
{{- if and .Values.preflight.enabled .Values.preflight.validateCNPs }}
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: cilium-pre-flight-check
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: cilium-pre-flight-check-deployment
|
||||
kubernetes.io/cluster-service: "true"
|
||||
template:
|
||||
metadata:
|
||||
{{- with .Values.preflight.podAnnotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
k8s-app: cilium-pre-flight-check-deployment
|
||||
kubernetes.io/cluster-service: "true"
|
||||
{{- with .Values.preflight.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
containers:
|
||||
- name: cnp-validator
|
||||
image: {{ include "cilium.image" .Values.preflight.image | quote }}
|
||||
imagePullPolicy: {{ .Values.preflight.image.pullPolicy }}
|
||||
command: ["/bin/sh"]
|
||||
args:
|
||||
- -ec
|
||||
- |
|
||||
cilium preflight validate-cnp;
|
||||
touch /tmp/ready-validate-cnp;
|
||||
sleep 1h;
|
||||
livenessProbe:
|
||||
exec:
|
||||
command:
|
||||
- cat
|
||||
- /tmp/ready-validate-cnp
|
||||
initialDelaySeconds: 5
|
||||
periodSeconds: 5
|
||||
readinessProbe:
|
||||
exec:
|
||||
command:
|
||||
- cat
|
||||
- /tmp/ready-validate-cnp
|
||||
initialDelaySeconds: 5
|
||||
periodSeconds: 5
|
||||
env:
|
||||
{{- if .Values.k8sServiceHost }}
|
||||
- name: KUBERNETES_SERVICE_HOST
|
||||
value: {{ .Values.k8sServiceHost | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.k8sServicePort }}
|
||||
- name: KUBERNETES_SERVICE_PORT
|
||||
value: {{ .Values.k8sServicePort | quote }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.extraEnv }}
|
||||
{{- toYaml . | trim | nindent 10 }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
hostNetwork: true
|
||||
restartPolicy: Always
|
||||
priorityClassName: {{ include "cilium.priorityClass" (list $ .Values.preflight.priorityClassName "system-cluster-critical") }}
|
||||
serviceAccount: {{ .Values.serviceAccounts.preflight.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.preflight.name | quote }}
|
||||
terminationGracePeriodSeconds: {{ .Values.preflight.terminationGracePeriodSeconds }}
|
||||
{{- with .Values.preflight.affinity }}
|
||||
affinity:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.preflight.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,22 @@
|
||||
{{- if and .Values.preflight.enabled .Values.preflight.validateCNPs .Values.preflight.podDisruptionBudget.enabled }}
|
||||
{{- $component := .Values.preflight.podDisruptionBudget }}
|
||||
apiVersion: {{ include "podDisruptionBudget.apiVersion" . }}
|
||||
kind: PodDisruptionBudget
|
||||
metadata:
|
||||
name: cilium-pre-flight-check
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: cilium-pre-flight-check-deployment
|
||||
kubernetes.io/cluster-service: "true"
|
||||
spec:
|
||||
{{- with $component.maxUnavailable }}
|
||||
maxUnavailable: {{ . }}
|
||||
{{- end }}
|
||||
{{- with $component.minAvailable }}
|
||||
minAvailable: {{ . }}
|
||||
{{- end }}
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: cilium-pre-flight-check-deployment
|
||||
kubernetes.io/cluster-service: "true"
|
||||
{{- end }}
|
||||
@ -0,0 +1,11 @@
|
||||
{{- if and .Values.preflight.enabled .Values.serviceAccounts.preflight.create }}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ .Values.serviceAccounts.preflight.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- if .Values.serviceAccounts.preflight.annotations }}
|
||||
annotations:
|
||||
{{ toYaml .Values.serviceAccounts.preflight.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,35 @@
|
||||
{{- if or .Values.resourceQuotas.enabled (and (ne .Release.Namespace "kube-system") .Values.gke.enabled) }}
|
||||
{{- if .Values.agent }}
|
||||
apiVersion: v1
|
||||
kind: ResourceQuota
|
||||
metadata:
|
||||
name: cilium-resource-quota
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
hard:
|
||||
pods: {{ .Values.resourceQuotas.cilium.hard.pods | quote }}
|
||||
scopeSelector:
|
||||
matchExpressions:
|
||||
- operator: In
|
||||
scopeName: PriorityClass
|
||||
values:
|
||||
- system-node-critical
|
||||
{{- end }}
|
||||
{{- if .Values.operator.enabled }}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: ResourceQuota
|
||||
metadata:
|
||||
name: cilium-operator-resource-quota
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
hard:
|
||||
pods: {{ .Values.resourceQuotas.operator.hard.pods | quote }}
|
||||
scopeSelector:
|
||||
matchExpressions:
|
||||
- operator: In
|
||||
scopeName: PriorityClass
|
||||
values:
|
||||
- system-cluster-critical
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,6 @@
|
||||
{{- if and .Values.ingressController.enabled .Values.ingressController.secretsNamespace.create .Values.ingressController.secretsNamespace.name }}
|
||||
apiVersion: v1
|
||||
kind: Namespace
|
||||
metadata:
|
||||
name: {{ .Values.ingressController.secretsNamespace.name | quote }}
|
||||
{{- end}}
|
||||
@ -0,0 +1,66 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.serviceAccounts.clustermeshApiserver.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRole
|
||||
metadata:
|
||||
name: clustermesh-apiserver
|
||||
rules:
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumnodes
|
||||
- ciliumendpoints
|
||||
- ciliumidentities
|
||||
verbs:
|
||||
- create
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumexternalworkloads/status
|
||||
- ciliumnodes
|
||||
- ciliumidentities
|
||||
verbs:
|
||||
- update
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumendpoints
|
||||
- ciliumendpoints/status
|
||||
verbs:
|
||||
- patch
|
||||
- apiGroups:
|
||||
- cilium.io
|
||||
resources:
|
||||
- ciliumidentities
|
||||
- ciliumexternalworkloads
|
||||
- ciliumendpoints
|
||||
- ciliumnodes
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- apiextensions.k8s.io
|
||||
resources:
|
||||
- customresourcedefinitions
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- endpoints
|
||||
- namespaces
|
||||
- services
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- discovery.k8s.io
|
||||
resources:
|
||||
- endpointslices
|
||||
verbs:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.serviceAccounts.clustermeshApiserver.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRoleBinding
|
||||
metadata:
|
||||
name: clustermesh-apiserver
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: ClusterRole
|
||||
name: clustermesh-apiserver
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.clustermeshApiserver.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,170 @@
|
||||
{{- if (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) }}
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: clustermesh-apiserver
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: clustermesh-apiserver
|
||||
spec:
|
||||
replicas: {{ .Values.clustermesh.apiserver.replicas }}
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: clustermesh-apiserver
|
||||
{{- with .Values.clustermesh.apiserver.updateStrategy }}
|
||||
strategy:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
{{- with .Values.clustermesh.apiserver.podAnnotations }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
k8s-app: clustermesh-apiserver
|
||||
{{- with .Values.clustermesh.apiserver.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
initContainers:
|
||||
- name: etcd-init
|
||||
image: {{ include "cilium.image" .Values.clustermesh.apiserver.etcd.image | quote }}
|
||||
imagePullPolicy: {{ .Values.clustermesh.apiserver.etcd.image.pullPolicy }}
|
||||
command: ["/bin/sh", "-c"]
|
||||
args:
|
||||
- |
|
||||
rm -rf /var/run/etcd/*;
|
||||
/usr/local/bin/etcd --data-dir=/var/run/etcd --name=clustermesh-apiserver --listen-client-urls=http://127.0.0.1:2379 --advertise-client-urls=http://127.0.0.1:2379 --initial-cluster-token=clustermesh-apiserver --initial-cluster-state=new --auto-compaction-retention=1 &
|
||||
export rootpw=`head /dev/urandom | tr -dc A-Za-z0-9 | head -c 16`;
|
||||
echo $rootpw | etcdctl --interactive=false user add root;
|
||||
etcdctl user grant-role root root;
|
||||
export vmpw=`head /dev/urandom | tr -dc A-Za-z0-9 | head -c 16`;
|
||||
echo $vmpw | etcdctl --interactive=false user add externalworkload;
|
||||
etcdctl role add externalworkload;
|
||||
etcdctl role grant-permission externalworkload --from-key read '';
|
||||
etcdctl role grant-permission externalworkload readwrite --prefix cilium/state/noderegister/v1/;
|
||||
etcdctl role grant-permission externalworkload readwrite --prefix cilium/.initlock/;
|
||||
etcdctl user grant-role externalworkload externalworkload;
|
||||
export remotepw=`head /dev/urandom | tr -dc A-Za-z0-9 | head -c 16`;
|
||||
echo $remotepw | etcdctl --interactive=false user add remote;
|
||||
etcdctl role add remote;
|
||||
etcdctl role grant-permission remote --from-key read '';
|
||||
etcdctl user grant-role remote remote;
|
||||
etcdctl auth enable;
|
||||
exit
|
||||
env:
|
||||
- name: ETCDCTL_API
|
||||
value: "3"
|
||||
- name: HOSTNAME_IP
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
fieldPath: status.podIP
|
||||
volumeMounts:
|
||||
- name: etcd-data-dir
|
||||
mountPath: /var/run/etcd
|
||||
containers:
|
||||
- name: etcd
|
||||
image: {{ include "cilium.image" .Values.clustermesh.apiserver.etcd.image | quote }}
|
||||
imagePullPolicy: {{ .Values.clustermesh.apiserver.etcd.image.pullPolicy }}
|
||||
command:
|
||||
- /usr/local/bin/etcd
|
||||
args:
|
||||
- --data-dir=/var/run/etcd
|
||||
- --name=clustermesh-apiserver
|
||||
- --client-cert-auth
|
||||
- --trusted-ca-file=/var/lib/etcd-secrets/ca.crt
|
||||
- --cert-file=/var/lib/etcd-secrets/tls.crt
|
||||
- --key-file=/var/lib/etcd-secrets/tls.key
|
||||
- --listen-client-urls=https://127.0.0.1:2379,https://$(HOSTNAME_IP):2379
|
||||
- --advertise-client-urls=https://$(HOSTNAME_IP):2379
|
||||
- --initial-cluster-token=clustermesh-apiserver
|
||||
- --auto-compaction-retention=1
|
||||
env:
|
||||
- name: ETCDCTL_API
|
||||
value: "3"
|
||||
- name: HOSTNAME_IP
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
fieldPath: status.podIP
|
||||
volumeMounts:
|
||||
- name: etcd-server-secrets
|
||||
mountPath: /var/lib/etcd-secrets
|
||||
readOnly: true
|
||||
- name: etcd-data-dir
|
||||
mountPath: /var/run/etcd
|
||||
- name: apiserver
|
||||
image: {{ include "cilium.image" .Values.clustermesh.apiserver.image | quote }}
|
||||
imagePullPolicy: {{ .Values.clustermesh.apiserver.image.pullPolicy }}
|
||||
command:
|
||||
- /usr/bin/clustermesh-apiserver
|
||||
args:
|
||||
{{- if .Values.debug.enabled }}
|
||||
- --debug
|
||||
{{- end }}
|
||||
- --cluster-name=$(CLUSTER_NAME)
|
||||
- --cluster-id=$(CLUSTER_ID)
|
||||
- --kvstore-opt
|
||||
- etcd.config=/var/lib/cilium/etcd-config.yaml
|
||||
env:
|
||||
- name: CLUSTER_NAME
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
name: cilium-config
|
||||
key: cluster-name
|
||||
- name: CLUSTER_ID
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
name: cilium-config
|
||||
key: cluster-id
|
||||
optional: true
|
||||
- name: IDENTITY_ALLOCATION_MODE
|
||||
valueFrom:
|
||||
configMapKeyRef:
|
||||
name: cilium-config
|
||||
key: identity-allocation-mode
|
||||
{{- with .Values.clustermesh.apiserver.extraEnv }}
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.clustermesh.apiserver.resources }}
|
||||
resources:
|
||||
{{- toYaml . | nindent 10 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: etcd-admin-client
|
||||
mountPath: /var/lib/cilium/etcd-secrets
|
||||
readOnly: true
|
||||
volumes:
|
||||
- name: etcd-server-secrets
|
||||
secret:
|
||||
secretName: clustermesh-apiserver-server-cert
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
- name: etcd-admin-client
|
||||
secret:
|
||||
secretName: clustermesh-apiserver-admin-cert
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
- name: etcd-data-dir
|
||||
emptyDir: {}
|
||||
restartPolicy: Always
|
||||
priorityClassName: {{ include "cilium.priorityClass" (list $ .Values.clustermesh.apiserver.priorityClassName "system-cluster-critical") }}
|
||||
serviceAccount: {{ .Values.serviceAccounts.clustermeshApiserver.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.clustermeshApiserver.name | quote }}
|
||||
{{- with .Values.clustermesh.apiserver.affinity }}
|
||||
affinity:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.clustermesh.apiserver.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.clustermesh.apiserver.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,20 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.podDisruptionBudget.enabled }}
|
||||
{{- $component := .Values.clustermesh.apiserver.podDisruptionBudget }}
|
||||
apiVersion: {{ include "podDisruptionBudget.apiVersion" . }}
|
||||
kind: PodDisruptionBudget
|
||||
metadata:
|
||||
name: clustermesh-apiserver
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: clustermesh-apiserver
|
||||
spec:
|
||||
{{- with $component.maxUnavailable }}
|
||||
maxUnavailable: {{ . }}
|
||||
{{- end }}
|
||||
{{- with $component.minAvailable }}
|
||||
minAvailable: {{ . }}
|
||||
{{- end }}
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: clustermesh-apiserver
|
||||
{{- end }}
|
||||
@ -0,0 +1,25 @@
|
||||
{{- if (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) }}
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: clustermesh-apiserver
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: clustermesh-apiserver
|
||||
{{- with .Values.clustermesh.apiserver.service.annotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
type: {{ .Values.clustermesh.apiserver.service.type }}
|
||||
selector:
|
||||
k8s-app: clustermesh-apiserver
|
||||
ports:
|
||||
- port: 2379
|
||||
{{- if and (eq "NodePort" .Values.clustermesh.apiserver.service.type) .Values.clustermesh.apiserver.service.nodePort }}
|
||||
nodePort: {{ .Values.clustermesh.apiserver.service.nodePort }}
|
||||
{{- end }}
|
||||
{{- if and (eq "LoadBalancer" .Values.clustermesh.apiserver.service.type) .Values.clustermesh.apiserver.service.loadBalancerIP }}
|
||||
loadBalancerIP: {{ .Values.clustermesh.apiserver.service.loadBalancerIP }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,11 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.serviceAccounts.clustermeshApiserver.create -}}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ .Values.serviceAccounts.clustermeshApiserver.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- with .Values.serviceAccounts.clustermeshApiserver.annotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,9 @@
|
||||
{{- define "clustermesh-apiserver-generate-certs.certmanager.issuer" }}
|
||||
{{- if .Values.clustermesh.apiserver.tls.auto.certManagerIssuerRef }}
|
||||
{{- toYaml .Values.clustermesh.apiserver.tls.auto.certManagerIssuerRef }}
|
||||
{{- else }}
|
||||
group: cert-manager.io
|
||||
kind: Issuer
|
||||
name: clustermesh-apiserver-issuer
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,16 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "certmanager") }}
|
||||
---
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: clustermesh-apiserver-admin-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
issuerRef:
|
||||
{{- include "clustermesh-apiserver-generate-certs.certmanager.issuer" . | nindent 4 }}
|
||||
secretName: clustermesh-apiserver-admin-cert
|
||||
commonName: root
|
||||
dnsNames:
|
||||
- localhost
|
||||
duration: {{ printf "%dh" (mul .Values.clustermesh.apiserver.tls.auto.certValidityDuration 24) }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and .Values.externalWorkloads.enabled .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "certmanager") }}
|
||||
---
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: clustermesh-apiserver-client-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
issuerRef:
|
||||
{{- include "clustermesh-apiserver-generate-certs.certmanager.issuer" . | nindent 4 }}
|
||||
secretName: clustermesh-apiserver-client-cert
|
||||
commonName: externalworkload
|
||||
duration: {{ printf "%dh" (mul .Values.clustermesh.apiserver.tls.auto.certValidityDuration 24) }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,21 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "certmanager") (not .Values.clustermesh.apiserver.tls.auto.certManagerIssuerRef) }}
|
||||
{{- $_ := include "clustermesh-apiserver-generate-certs.helm.setup-ca" . -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-ca-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
ca.crt: {{ .cmca.Cert | b64enc }}
|
||||
ca.key: {{ .cmca.Key | b64enc }}
|
||||
---
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Issuer
|
||||
metadata:
|
||||
name: clustermesh-apiserver-issuer
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
ca:
|
||||
secretName: clustermesh-apiserver-ca-cert
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and .Values.clustermesh.useAPIServer .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "certmanager") }}
|
||||
---
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: clustermesh-apiserver-remote-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
issuerRef:
|
||||
{{- include "clustermesh-apiserver-generate-certs.certmanager.issuer" . | nindent 4 }}
|
||||
secretName: clustermesh-apiserver-remote-cert
|
||||
commonName: remote
|
||||
duration: {{ printf "%dh" (mul .Values.clustermesh.apiserver.tls.auto.certValidityDuration 24) }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,26 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "certmanager") }}
|
||||
---
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: clustermesh-apiserver-server-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
issuerRef:
|
||||
{{- include "clustermesh-apiserver-generate-certs.certmanager.issuer" . | nindent 4 }}
|
||||
secretName: clustermesh-apiserver-server-cert
|
||||
commonName: clustermesh-apiserver.cilium.io
|
||||
dnsNames:
|
||||
- clustermesh-apiserver.cilium.io
|
||||
- "*.mesh.cilium.io"
|
||||
{{- range $dns := .Values.clustermesh.apiserver.tls.server.extraDnsNames }}
|
||||
- {{ $dns | quote }}
|
||||
{{- end }}
|
||||
ipAddresses:
|
||||
- "127.0.0.1"
|
||||
- "::1"
|
||||
{{- range $ip := .Values.clustermesh.apiserver.tls.server.extraIpAddresses }}
|
||||
- {{ $ip | quote }}
|
||||
{{- end }}
|
||||
duration: {{ printf "%dh" (mul .Values.clustermesh.apiserver.tls.auto.certValidityDuration 24) }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,53 @@
|
||||
{{- define "clustermesh-apiserver-generate-certs.job.spec" }}
|
||||
{{- $certValiditySecondsStr := printf "%ds" (mul .Values.clustermesh.apiserver.tls.auto.certValidityDuration 24 60 60) -}}
|
||||
spec:
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
k8s-app: clustermesh-apiserver-generate-certs
|
||||
{{- with .Values.clustermesh.apiserver.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
containers:
|
||||
- name: certgen
|
||||
image: {{ include "cilium.image" .Values.certgen.image | quote }}
|
||||
imagePullPolicy: {{ .Values.certgen.image.pullPolicy }}
|
||||
command:
|
||||
- "/usr/bin/cilium-certgen"
|
||||
args:
|
||||
- "--cilium-namespace={{ .Release.Namespace }}"
|
||||
{{- if .Values.debug.enabled }}
|
||||
- "--debug"
|
||||
{{- end }}
|
||||
- "--ca-generate"
|
||||
- "--ca-reuse-secret"
|
||||
{{- if .Values.clustermesh.apiserver.tls.ca.cert }}
|
||||
- "--ca-secret-name=clustermesh-apiserver-ca-cert"
|
||||
{{- else -}}
|
||||
{{- if and .Values.tls.ca.cert .Values.tls.ca.key }}
|
||||
- "--ca-secret-name=cilium-ca"
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
- "--clustermesh-apiserver-server-cert-generate"
|
||||
- "--clustermesh-apiserver-server-cert-validity-duration={{ $certValiditySecondsStr }}"
|
||||
- "--clustermesh-apiserver-admin-cert-generate"
|
||||
- "--clustermesh-apiserver-admin-cert-validity-duration={{ $certValiditySecondsStr }}"
|
||||
{{- if .Values.externalWorkloads.enabled }}
|
||||
- "--clustermesh-apiserver-client-cert-generate"
|
||||
- "--clustermesh-apiserver-client-cert-validity-duration={{ $certValiditySecondsStr }}"
|
||||
{{- end }}
|
||||
{{- if .Values.clustermesh.useAPIServer }}
|
||||
- "--clustermesh-apiserver-remote-cert-generate"
|
||||
- "--clustermesh-apiserver-remote-cert-validity-duration={{ $certValiditySecondsStr }}"
|
||||
{{- end }}
|
||||
hostNetwork: true
|
||||
serviceAccount: {{ .Values.serviceAccounts.clustermeshcertgen.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.clustermeshcertgen.name | quote }}
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
restartPolicy: OnFailure
|
||||
ttlSecondsAfterFinished: {{ .Values.certgen.ttlSecondsAfterFinished }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,15 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "cronJob") }}
|
||||
{{- $crt := .Values.clustermesh.apiserver.tls.ca.cert | default .Values.tls.ca.cert -}}
|
||||
{{- $key := .Values.clustermesh.apiserver.tls.ca.key | default .Values.tls.ca.key -}}
|
||||
{{- if and $crt $key }}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-ca-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
ca.crt: {{ $crt }}
|
||||
ca.key: {{ $key }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "cronJob") .Values.clustermesh.apiserver.tls.auto.schedule }}
|
||||
apiVersion: {{ include "cronjob.apiVersion" . }}
|
||||
kind: CronJob
|
||||
metadata:
|
||||
name: clustermesh-apiserver-generate-certs
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: clustermesh-apiserver-generate-certs
|
||||
spec:
|
||||
schedule: {{ .Values.clustermesh.apiserver.tls.auto.schedule | quote }}
|
||||
concurrencyPolicy: Forbid
|
||||
jobTemplate:
|
||||
{{- include "clustermesh-apiserver-generate-certs.job.spec" . | nindent 4 }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,20 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "cronJob") }}
|
||||
{{/*
|
||||
Because Kubernetes job specs are immutable, Helm will fail patch this job if
|
||||
the spec changes between releases. To avoid breaking the upgrade path, we
|
||||
generate a name for the job here which is based on the checksum of the spec.
|
||||
This will cause the name of the job to change if its content changes,
|
||||
and in turn cause Helm to do delete the old job and replace it with a new one.
|
||||
*/}}
|
||||
{{- $jobSpec := include "clustermesh-apiserver-generate-certs.job.spec" . -}}
|
||||
{{- $checkSum := $jobSpec | sha256sum | trunc 10 -}}
|
||||
---
|
||||
apiVersion: batch/v1
|
||||
kind: Job
|
||||
metadata:
|
||||
name: clustermesh-apiserver-generate-certs-{{$checkSum}}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: clustermesh-apiserver-generate-certs
|
||||
{{ $jobSpec }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,35 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "cronJob") .Values.serviceAccounts.clustermeshcertgen.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: Role
|
||||
metadata:
|
||||
name: clustermesh-apiserver-generate-certs
|
||||
namespace: {{ .Release.Namespace }}
|
||||
rules:
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
verbs:
|
||||
- create
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
resourceNames:
|
||||
- cilium-ca
|
||||
- clustermesh-apiserver-ca-cert
|
||||
verbs:
|
||||
- get
|
||||
- update
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
resourceNames:
|
||||
- clustermesh-apiserver-server-cert
|
||||
- clustermesh-apiserver-admin-cert
|
||||
- clustermesh-apiserver-remote-cert
|
||||
- clustermesh-apiserver-client-cert
|
||||
verbs:
|
||||
- update
|
||||
{{- end }}
|
||||
@ -0,0 +1,15 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "cronJob") .Values.serviceAccounts.clustermeshcertgen.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: RoleBinding
|
||||
metadata:
|
||||
name: clustermesh-apiserver-generate-certs
|
||||
namespace: {{ .Release.Namespace }}
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: Role
|
||||
name: clustermesh-apiserver-generate-certs
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.clustermeshcertgen.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,11 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "cronJob") .Values.serviceAccounts.clustermeshcertgen.create }}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ .Values.serviceAccounts.clustermeshcertgen.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- with .Values.serviceAccounts.clustermeshcertgen.annotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,37 @@
|
||||
{{/*
|
||||
Generate TLS certificates for ClusterMesh.
|
||||
|
||||
Note: Always use this template as follows:
|
||||
|
||||
{{- $_ := include "clustermesh-apiserver-generate-certs.helm.setup-ca" . -}}
|
||||
|
||||
The assignment to `$_` is required because we store the generated CI in a global `cmca` variable.
|
||||
Please, don't try to "simplify" this, as without this trick, every generated
|
||||
certificate would be signed by a different CA.
|
||||
*/}}
|
||||
{{- define "clustermesh-apiserver-generate-certs.helm.setup-ca" }}
|
||||
{{- if not .cmca }}
|
||||
{{- $ca := "" -}}
|
||||
{{- $crt := .Values.clustermesh.apiserver.tls.ca.cert | default .Values.tls.ca.cert -}}
|
||||
{{- $key := .Values.clustermesh.apiserver.tls.ca.key | default .Values.tls.ca.key -}}
|
||||
{{- if and $crt $key }}
|
||||
{{- $ca = buildCustomCert $crt $key -}}
|
||||
{{- else }}
|
||||
{{- with lookup "v1" "Secret" .Release.Namespace "clustermesh-apiserver-ca-cert" }}
|
||||
{{- $crt := index .data "ca.crt" }}
|
||||
{{- $key := index .data "ca.key" }}
|
||||
{{- $ca = buildCustomCert $crt $key -}}
|
||||
{{- else }}
|
||||
{{- $_ := include "cilium.ca.setup" . -}}
|
||||
{{- with lookup "v1" "Secret" .Release.Namespace .commonCASecretName }}
|
||||
{{- $crt := index .data "ca.crt" }}
|
||||
{{- $key := index .data "ca.key" }}
|
||||
{{- $ca = buildCustomCert $crt $key -}}
|
||||
{{- else }}
|
||||
{{- $ca = .commonCA -}}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- $_ := set . "cmca" $ca -}}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,17 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "helm") }}
|
||||
{{- $_ := include "clustermesh-apiserver-generate-certs.helm.setup-ca" . -}}
|
||||
{{- $cn := "root" }}
|
||||
{{- $dns := list "localhost" }}
|
||||
{{- $cert := genSignedCert $cn nil $dns (.Values.clustermesh.apiserver.tls.auto.certValidityDuration | int) .cmca -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-admin-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .cmca.Cert | b64enc }}
|
||||
tls.crt: {{ $cert.Cert | b64enc }}
|
||||
tls.key: {{ $cert.Key | b64enc }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,12 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "helm") }}
|
||||
{{- $_ := include "clustermesh-apiserver-generate-certs.helm.setup-ca" . -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-ca-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
ca.crt: {{ .cmca.Cert | b64enc }}
|
||||
ca.key: {{ .cmca.Key | b64enc }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,16 @@
|
||||
{{- if and .Values.externalWorkloads.enabled .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "helm") }}
|
||||
{{- $_ := include "clustermesh-apiserver-generate-certs.helm.setup-ca" . -}}
|
||||
{{- $cn := "externalworkload" }}
|
||||
{{- $cert := genSignedCert $cn nil nil (.Values.clustermesh.apiserver.tls.auto.certValidityDuration | int) .cmca -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-client-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .cmca.Cert | b64enc }}
|
||||
tls.crt: {{ $cert.Cert | b64enc }}
|
||||
tls.key: {{ $cert.Key | b64enc }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,16 @@
|
||||
{{- if and .Values.clustermesh.useAPIServer .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "helm") }}
|
||||
{{- $_ := include "clustermesh-apiserver-generate-certs.helm.setup-ca" . -}}
|
||||
{{- $cn := "remote" }}
|
||||
{{- $cert := genSignedCert $cn nil nil (.Values.clustermesh.apiserver.tls.auto.certValidityDuration | int) .cmca -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-remote-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .cmca.Cert | b64enc }}
|
||||
tls.crt: {{ $cert.Cert | b64enc }}
|
||||
tls.key: {{ $cert.Key | b64enc }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,18 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) .Values.clustermesh.apiserver.tls.auto.enabled (eq .Values.clustermesh.apiserver.tls.auto.method "helm") }}
|
||||
{{- $_ := include "clustermesh-apiserver-generate-certs.helm.setup-ca" . -}}
|
||||
{{- $cn := "clustermesh-apiserver.cilium.io" }}
|
||||
{{- $ip := concat (list "127.0.0.1" "::1") .Values.clustermesh.apiserver.tls.server.extraIpAddresses }}
|
||||
{{- $dns := concat (list $cn "*.mesh.cilium.io") .Values.clustermesh.apiserver.tls.server.extraDnsNames }}
|
||||
{{- $cert := genSignedCert $cn $ip $dns (.Values.clustermesh.apiserver.tls.auto.certValidityDuration | int) .cmca -}}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-server-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .cmca.Cert | b64enc }}
|
||||
tls.crt: {{ $cert.Cert | b64enc }}
|
||||
tls.key: {{ $cert.Key | b64enc }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,12 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) (not .Values.clustermesh.apiserver.tls.auto.enabled) }}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-admin-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .Values.clustermesh.apiserver.tls.ca.cert }}
|
||||
tls.crt: {{ .Values.clustermesh.apiserver.tls.admin.cert | required "missing clustermesh.apiserver.tls.admin.cert" }}
|
||||
tls.key: {{ .Values.clustermesh.apiserver.tls.admin.key | required "missing clustermesh.apiserver.tls.admin.key" }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,12 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) (not .Values.clustermesh.apiserver.tls.auto.enabled) }}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-ca-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
ca.crt: {{ .Values.clustermesh.apiserver.tls.ca.cert }}
|
||||
{{- if .Values.clustermesh.apiserver.tls.ca.key }}
|
||||
ca.key: {{ .Values.clustermesh.apiserver.tls.ca.key }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,12 @@
|
||||
{{- if and .Values.externalWorkloads.enabled (not .Values.clustermesh.apiserver.tls.auto.enabled) }}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-client-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .Values.clustermesh.apiserver.tls.ca.cert }}
|
||||
tls.crt: {{ .Values.clustermesh.apiserver.tls.client.cert | required "missing clustermesh.apiserver.tls.client.cert" }}
|
||||
tls.key: {{ .Values.clustermesh.apiserver.tls.client.key | required "missing clustermesh.apiserver.tls.client.key" }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,12 @@
|
||||
{{- if and .Values.clustermesh.useAPIServer (not .Values.clustermesh.apiserver.tls.auto.enabled) }}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-remote-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .Values.clustermesh.apiserver.tls.ca.cert }}
|
||||
tls.crt: {{ .Values.clustermesh.apiserver.tls.remote.cert | required "missing clustermesh.apiserver.tls.remote.cert" }}
|
||||
tls.key: {{ .Values.clustermesh.apiserver.tls.remote.key | required "missing clustermesh.apiserver.tls.remote.key" }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,12 @@
|
||||
{{- if and (or .Values.externalWorkloads.enabled .Values.clustermesh.useAPIServer) (not .Values.clustermesh.apiserver.tls.auto.enabled) }}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: clustermesh-apiserver-server-cert
|
||||
namespace: {{ .Release.Namespace }}
|
||||
type: kubernetes.io/tls
|
||||
data:
|
||||
ca.crt: {{ .Values.clustermesh.apiserver.tls.ca.cert }}
|
||||
tls.crt: {{ .Values.clustermesh.apiserver.tls.server.cert | required "missing clustermesh.apiserver.tls.server.cert" }}
|
||||
tls.key: {{ .Values.clustermesh.apiserver.tls.server.key | required "missing clustermesh.apiserver.tls.server.key" }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- define "clustermesh-config-generate-etcd-cfg" }}
|
||||
{{- $cluster := index . 0 -}}
|
||||
{{- $domain := index . 1 -}}
|
||||
|
||||
endpoints:
|
||||
{{- if $cluster.ips }}
|
||||
- https://{{ $cluster.name }}.{{ $domain }}:{{ $cluster.port }}
|
||||
{{ else }}
|
||||
- https://{{ $cluster.address | required "missing clustermesh.apiserver.config.clusters.address" }}:{{ $cluster.port }}
|
||||
{{- end }}
|
||||
trusted-ca-file: /var/lib/cilium/clustermesh/{{ $cluster.name }}.etcd-client-ca.crt
|
||||
key-file: /var/lib/cilium/clustermesh/{{ $cluster.name }}.etcd-client.key
|
||||
cert-file: /var/lib/cilium/clustermesh/{{ $cluster.name }}.etcd-client.crt
|
||||
{{- end }}
|
||||
@ -0,0 +1,15 @@
|
||||
{{- if and .Values.clustermesh.useAPIServer .Values.clustermesh.config.enabled }}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: cilium-clustermesh
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
{{- range .Values.clustermesh.config.clusters }}
|
||||
{{ .name }}: {{ include "clustermesh-config-generate-etcd-cfg" (list . $.Values.clustermesh.config.domain) | b64enc }}
|
||||
{{ .name }}.etcd-client-ca.crt: {{ $.Values.clustermesh.apiserver.tls.ca.cert }}
|
||||
{{ .name }}.etcd-client.key: {{ .tls.key }}
|
||||
{{ .name }}.etcd-client.crt: {{ .tls.cert }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,73 @@
|
||||
{{- if .Values.etcd.managed }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRole
|
||||
metadata:
|
||||
name: cilium-etcd-operator
|
||||
rules:
|
||||
- apiGroups:
|
||||
- etcd.database.coreos.com
|
||||
resources:
|
||||
- etcdclusters
|
||||
verbs:
|
||||
- get
|
||||
- delete
|
||||
- create
|
||||
- update
|
||||
- apiGroups:
|
||||
- apiextensions.k8s.io
|
||||
resources:
|
||||
- customresourcedefinitions
|
||||
verbs:
|
||||
- delete
|
||||
- get
|
||||
- create
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- deployments
|
||||
verbs:
|
||||
- delete
|
||||
- create
|
||||
- get
|
||||
- update
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- pods
|
||||
verbs:
|
||||
- list
|
||||
- get
|
||||
- delete
|
||||
- apiGroups:
|
||||
- apps
|
||||
resources:
|
||||
- deployments
|
||||
verbs:
|
||||
- delete
|
||||
- create
|
||||
- get
|
||||
- update
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- componentstatuses
|
||||
verbs:
|
||||
- get
|
||||
- apiGroups:
|
||||
- extensions
|
||||
resources:
|
||||
- deployments
|
||||
verbs:
|
||||
- delete
|
||||
- create
|
||||
- get
|
||||
- update
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
verbs:
|
||||
- get
|
||||
- create
|
||||
- delete
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if and .Values.etcd.managed .Values.serviceAccounts.etcd.create }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRoleBinding
|
||||
metadata:
|
||||
name: cilium-etcd-operator
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: ClusterRole
|
||||
name: cilium-etcd-operator
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ .Values.serviceAccounts.etcd.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,90 @@
|
||||
{{- if .Values.etcd.managed }}
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
labels:
|
||||
io.cilium/app: etcd-operator
|
||||
name: cilium-etcd-operator
|
||||
name: cilium-etcd-operator
|
||||
namespace: {{ .Release.Namespace }}
|
||||
spec:
|
||||
replicas: 1
|
||||
selector:
|
||||
matchLabels:
|
||||
io.cilium/app: etcd-operator
|
||||
name: cilium-etcd-operator
|
||||
{{- with .Values.etcd.updateStrategy }}
|
||||
strategy:
|
||||
{{- toYaml . | trim | nindent 4 }}
|
||||
{{- end }}
|
||||
template:
|
||||
metadata:
|
||||
{{- with .Values.etcd.podAnnotations }}
|
||||
annotations:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
io.cilium/app: etcd-operator
|
||||
name: cilium-etcd-operator
|
||||
{{- with .Values.etcd.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- if .Values.etcd.affinity }}
|
||||
affinity:
|
||||
{{ toYaml .Values.etcd.affinity | indent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{ toYaml .Values.imagePullSecrets | indent 8 }}
|
||||
{{- end }}
|
||||
containers:
|
||||
- args:
|
||||
{{- with .Values.etcd.extraArgs }}
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
#- --etcd-node-selector=disktype=ssd,cputype=high
|
||||
command:
|
||||
- /usr/bin/cilium-etcd-operator
|
||||
env:
|
||||
- name: CILIUM_ETCD_OPERATOR_CLUSTER_DOMAIN
|
||||
value: "{{ .Values.etcd.clusterDomain }}"
|
||||
- name: CILIUM_ETCD_OPERATOR_ETCD_CLUSTER_SIZE
|
||||
value: "{{ .Values.etcd.clusterSize }}"
|
||||
- name: CILIUM_ETCD_OPERATOR_NAMESPACE
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: metadata.namespace
|
||||
- name: CILIUM_ETCD_OPERATOR_POD_NAME
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: metadata.name
|
||||
- name: CILIUM_ETCD_OPERATOR_POD_UID
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: metadata.uid
|
||||
- name: CILIUM_ETCD_META_ETCD_AUTO_COMPACTION_MODE
|
||||
value: "revision"
|
||||
- name: CILIUM_ETCD_META_ETCD_AUTO_COMPACTION_RETENTION
|
||||
value: "25000"
|
||||
image: {{ .Values.etcd.image.repository }}:{{ .Values.etcd.image.tag }}
|
||||
imagePullPolicy: {{ .Values.etcd.image.pullPolicy }}
|
||||
name: cilium-etcd-operator
|
||||
dnsPolicy: ClusterFirst
|
||||
hostNetwork: true
|
||||
priorityClassName: {{ include "cilium.priorityClass" (list $ .Values.clustermesh.apiserver.priorityClassName "system-cluster-critical") }}
|
||||
restartPolicy: Always
|
||||
serviceAccount: {{ .Values.serviceAccounts.etcd.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.etcd.name | quote }}
|
||||
{{- with .Values.etcd.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.etcd.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | trim | nindent 6 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,11 @@
|
||||
{{- if and .Values.etcd.managed .Values.serviceAccounts.etcd.create }}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ .Values.serviceAccounts.etcd.name | quote }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- if .Values.serviceAccounts.etcd.annotations }}
|
||||
annotations:
|
||||
{{ toYaml .Values.serviceAccounts.etcd.annotations | indent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,54 @@
|
||||
{{- if .Values.etcd.managed }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRole
|
||||
metadata:
|
||||
name: etcd-operator
|
||||
rules:
|
||||
- apiGroups:
|
||||
- etcd.database.coreos.com
|
||||
resources:
|
||||
- etcdclusters
|
||||
- etcdbackups
|
||||
- etcdrestores
|
||||
verbs:
|
||||
- '*'
|
||||
- apiGroups:
|
||||
- apiextensions.k8s.io
|
||||
resources:
|
||||
- customresourcedefinitions
|
||||
verbs:
|
||||
- '*'
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- pods
|
||||
- services
|
||||
- endpoints
|
||||
- persistentvolumeclaims
|
||||
- events
|
||||
- deployments
|
||||
verbs:
|
||||
- '*'
|
||||
- apiGroups:
|
||||
- apps
|
||||
resources:
|
||||
- deployments
|
||||
verbs:
|
||||
- '*'
|
||||
- apiGroups:
|
||||
- extensions
|
||||
resources:
|
||||
- deployments
|
||||
verbs:
|
||||
- create
|
||||
- get
|
||||
- list
|
||||
- patch
|
||||
- update
|
||||
- apiGroups:
|
||||
- ""
|
||||
resources:
|
||||
- secrets
|
||||
verbs:
|
||||
- get
|
||||
{{- end }}
|
||||
@ -0,0 +1,14 @@
|
||||
{{- if .Values.etcd.managed }}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRoleBinding
|
||||
metadata:
|
||||
name: etcd-operator
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: ClusterRole
|
||||
name: etcd-operator
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: cilium-etcd-sa
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,11 @@
|
||||
{{- if .Values.etcd.managed }}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: cilium-etcd-sa
|
||||
namespace: {{ .Release.Namespace }}
|
||||
{{- if .Values.serviceAccounts.etcd.annotations }}
|
||||
annotations:
|
||||
{{ toYaml .Values.serviceAccounts.etcd.annotations | indent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,22 @@
|
||||
{{- if and .Values.etcd.managed .Values.etcd.podDisruptionBudget.enabled }}
|
||||
{{- $component := .Values.etcd.podDisruptionBudget }}
|
||||
apiVersion: {{ include "podDisruptionBudget.apiVersion" . }}
|
||||
kind: PodDisruptionBudget
|
||||
metadata:
|
||||
name: cilium-etcd-operator
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
io.cilium/app: etcd-operator
|
||||
name: cilium-etcd-operator
|
||||
spec:
|
||||
{{- with $component.maxUnavailable }}
|
||||
maxUnavailable: {{ . }}
|
||||
{{- end }}
|
||||
{{- with $component.minAvailable }}
|
||||
minAvailable: {{ . }}
|
||||
{{- end }}
|
||||
selector:
|
||||
matchLabels:
|
||||
io.cilium/app: etcd-operator
|
||||
name: cilium-etcd-operator
|
||||
{{- end }}
|
||||
@ -0,0 +1,41 @@
|
||||
{{- if and .Values.hubble.enabled .Values.hubble.relay.enabled }}
|
||||
{{- $peerSvcPort := .Values.hubble.peerService.servicePort -}}
|
||||
{{- if not .Values.hubble.peerService.servicePort }}
|
||||
{{- $peerSvcPort = (.Values.hubble.tls.enabled | ternary 443 80) -}}
|
||||
{{- end }}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: hubble-relay-config
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
config.yaml: |
|
||||
cluster-name: {{ .Values.cluster.name }}
|
||||
{{- if and .Values.hubble.enabled .Values.hubble.peerService.enabled }}
|
||||
peer-service: "hubble-peer.{{ .Release.Namespace }}.svc.{{ .Values.hubble.peerService.clusterDomain }}:{{ $peerSvcPort }}"
|
||||
{{- else }}
|
||||
peer-service: unix://{{ .Values.hubble.socketPath }}
|
||||
{{- end }}
|
||||
listen-address: {{ .Values.hubble.relay.listenHost }}:{{ .Values.hubble.relay.listenPort }}
|
||||
{{- if .Values.hubble.relay.prometheus.enabled }}
|
||||
metrics-listen-address: ":{{ .Values.hubble.relay.prometheus.port }}"
|
||||
{{- end }}
|
||||
dial-timeout: {{ .Values.hubble.relay.dialTimeout }}
|
||||
retry-timeout: {{ .Values.hubble.relay.retryTimeout }}
|
||||
sort-buffer-len-max: {{ .Values.hubble.relay.sortBufferLenMax }}
|
||||
sort-buffer-drain-timeout: {{ .Values.hubble.relay.sortBufferDrainTimeout }}
|
||||
{{- if .Values.hubble.tls.enabled }}
|
||||
tls-client-cert-file: /var/lib/hubble-relay/tls/client.crt
|
||||
tls-client-key-file: /var/lib/hubble-relay/tls/client.key
|
||||
tls-hubble-server-ca-files: /var/lib/hubble-relay/tls/hubble-server-ca.crt
|
||||
{{- else }}
|
||||
disable-client-tls: true
|
||||
{{- end }}
|
||||
{{- if and .Values.hubble.tls.enabled .Values.hubble.relay.tls.server.enabled }}
|
||||
tls-server-cert-file: /var/lib/hubble-relay/tls/server.crt
|
||||
tls-server-key-file: /var/lib/hubble-relay/tls/server.key
|
||||
{{- else }}
|
||||
disable-server-tls: true
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,146 @@
|
||||
{{- if and .Values.hubble.enabled .Values.hubble.relay.enabled }}
|
||||
{{- $mountSocket := not .Values.hubble.peerService.enabled -}}
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
name: hubble-relay
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: hubble-relay
|
||||
spec:
|
||||
replicas: {{ .Values.hubble.relay.replicas }}
|
||||
selector:
|
||||
matchLabels:
|
||||
k8s-app: hubble-relay
|
||||
{{- with .Values.hubble.relay.updateStrategy }}
|
||||
strategy:
|
||||
{{- toYaml . | trim | nindent 4 }}
|
||||
{{- end }}
|
||||
template:
|
||||
metadata:
|
||||
annotations:
|
||||
{{- if .Values.hubble.relay.rollOutPods }}
|
||||
# ensure pods roll when configmap updates
|
||||
cilium.io/hubble-relay-configmap-checksum: {{ include (print $.Template.BasePath "/hubble-relay/configmap.yaml") . | sha256sum | quote }}
|
||||
{{- end }}
|
||||
{{- with .Values.hubble.relay.podAnnotations }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
k8s-app: hubble-relay
|
||||
{{- with .Values.hubble.relay.podLabels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
{{- with .Values.hubble.relay.securityContext }}
|
||||
securityContext:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.imagePullSecrets }}
|
||||
imagePullSecrets:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
containers:
|
||||
- name: hubble-relay
|
||||
image: {{ include "cilium.image" .Values.hubble.relay.image | quote }}
|
||||
imagePullPolicy: {{ .Values.hubble.relay.image.pullPolicy }}
|
||||
command:
|
||||
- hubble-relay
|
||||
args:
|
||||
- serve
|
||||
{{- if .Values.debug.enabled }}
|
||||
- --debug
|
||||
{{- end }}
|
||||
ports:
|
||||
- name: grpc
|
||||
containerPort: {{ .Values.hubble.relay.listenPort }}
|
||||
{{- if .Values.hubble.relay.prometheus.enabled }}
|
||||
- name: prometheus
|
||||
containerPort: {{ .Values.hubble.relay.prometheus.port }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
readinessProbe:
|
||||
tcpSocket:
|
||||
port: grpc
|
||||
livenessProbe:
|
||||
tcpSocket:
|
||||
port: grpc
|
||||
{{- with .Values.hubble.relay.extraEnv }}
|
||||
env:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- with .Values.hubble.relay.resources }}
|
||||
resources:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
{{- if $mountSocket }}
|
||||
- name: hubble-sock-dir
|
||||
mountPath: {{ dir .Values.hubble.socketPath }}
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
- name: config
|
||||
mountPath: /etc/hubble-relay
|
||||
readOnly: true
|
||||
{{- if .Values.hubble.tls.enabled }}
|
||||
- name: tls
|
||||
mountPath: /var/lib/hubble-relay/tls
|
||||
readOnly: true
|
||||
{{- end }}
|
||||
restartPolicy: Always
|
||||
priorityClassName: {{ .Values.hubble.relay.priorityClassName }}
|
||||
serviceAccount: {{ .Values.serviceAccounts.relay.name | quote }}
|
||||
serviceAccountName: {{ .Values.serviceAccounts.relay.name | quote }}
|
||||
automountServiceAccountToken: false
|
||||
terminationGracePeriodSeconds: {{ .Values.hubble.relay.terminationGracePeriodSeconds }}
|
||||
{{- with .Values.hubble.relay.affinity }}
|
||||
affinity:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.hubble.relay.nodeSelector }}
|
||||
nodeSelector:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.hubble.relay.tolerations }}
|
||||
tolerations:
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
volumes:
|
||||
- name: config
|
||||
configMap:
|
||||
name: hubble-relay-config
|
||||
items:
|
||||
- key: config.yaml
|
||||
path: config.yaml
|
||||
{{- if $mountSocket }}
|
||||
- name: hubble-sock-dir
|
||||
hostPath:
|
||||
path: {{ dir .Values.hubble.socketPath }}
|
||||
type: Directory
|
||||
{{- end }}
|
||||
{{- if .Values.hubble.tls.enabled }}
|
||||
- name: tls
|
||||
projected:
|
||||
# note: the leading zero means this number is in octal representation: do not remove it
|
||||
defaultMode: 0400
|
||||
sources:
|
||||
- secret:
|
||||
name: hubble-relay-client-certs
|
||||
items:
|
||||
- key: ca.crt
|
||||
path: hubble-server-ca.crt
|
||||
- key: tls.crt
|
||||
path: client.crt
|
||||
- key: tls.key
|
||||
path: client.key
|
||||
{{- if .Values.hubble.relay.tls.server.enabled }}
|
||||
- secret:
|
||||
name: hubble-relay-server-certs
|
||||
items:
|
||||
- key: tls.crt
|
||||
path: server.crt
|
||||
- key: tls.key
|
||||
path: server.key
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@ -0,0 +1,20 @@
|
||||
{{- if and .Values.hubble.enabled .Values.hubble.relay.enabled .Values.hubble.relay.prometheus.enabled }}
|
||||
# We use a separate service from hubble-relay which can be exposed externally
|
||||
kind: Service
|
||||
apiVersion: v1
|
||||
metadata:
|
||||
name: hubble-relay-metrics
|
||||
namespace: {{ .Release.Namespace }}
|
||||
labels:
|
||||
k8s-app: hubble-relay
|
||||
spec:
|
||||
clusterIP: None
|
||||
type: ClusterIP
|
||||
selector:
|
||||
k8s-app: hubble-relay
|
||||
ports:
|
||||
- name: metrics
|
||||
port: {{ .Values.hubble.relay.prometheus.port }}
|
||||
protocol: TCP
|
||||
targetPort: prometheus
|
||||
{{- end }}
|
||||
Some files were not shown because too many files have changed in this diff Show More
Loading…
x
Reference in New Issue
Block a user