5.3 KiB
The meeting in Arago, Barcelona
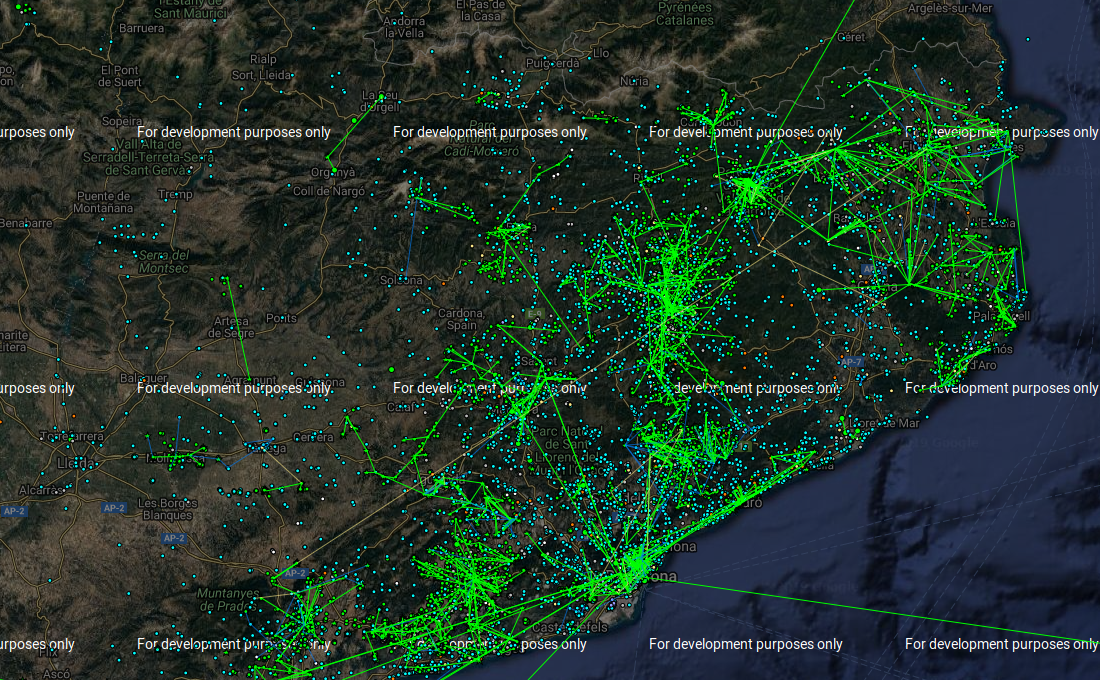
This is the network graph of guifi.net. A wireless routed layer three network. B.A.T.M.A.N. [1] routing protocol is active, but also OSPF [2] and BGP [3].
Like I've already said guifi is based upon Mikrotik. The stupid little purple bitch, a telecommunications entrepreneur in France, a daughter of military family in Italy, an hacker of systems and people in Spain and a terrorist in the world have used a public exploit to gain access in this free network. The problem is that this free network has got a BGP autonomous system number [4]. The primary exchange ASN is 49835 [5], the data center is the Catalunya neutral Internet exchange [6]. In the same IXP [7] there is others very important connections:
- Adamo [8] 35699 [9]
- ESPANIX [10]
- Andorra Telecom [11] 6752 [12]
- Claranet [13] 8426 [14]
- Cloudfare [15] 13335 [16]
- Google LLC [17] 15169 [18]
- Microsoft [19] 8075 [20]
- Orange Spain [21] 11902 [22]
- RedIRIS [23] 766 [24]
- RIPE NCC [25] 12654 [26]
- Hurricane Electric [27] 6939 [28]
- ISC [29] 1280 [30]
- T-Systems [31] 30892 [32]
- Telefonica de España [33] 3352 [34]
- VeriSign [35] 26415 [36]
In the Orange network but also probably in the Telefonica one hackers gain access to the LTE towers and the passive scanning system for brain waves. The ones that are stimulated by the satellite in 3GHz. Like we've seen.
All the customers premise equipments of Telefonica in FTTH mount the CPE Wan Management Protocol TR-069 [37] soap [38] based message system with the data center to them. And there is a public vulnerability [39], simple to use to exploit the client hardware. Movistar equipment got three VLANS 2 voice 3 iptv and 6 data. PPPoE daemon in the FTTH movistar network serve dynamic public ips over an virtual encapsulation with a maximum transfer unit of 1500 - 8 bytes with vlan tag number 2. CWMP daemon it's opened by default over that vlan and got an access list with default permissions on deny and accept only a range of public ip from the same provider. Those people with BGP Hijacking have hoped from AS
External links
- https://en.wikipedia.org/wiki/B.A.T.M.A.N.
- https://en.wikipedia.org/wiki/Open_Shortest_Path_First
- https://en.wikipedia.org/wiki/Border_Gateway_Protocol
- https://www.inetdaemon.com/tutorials/internet/ip/routing/bgp/autonomous_system_number.shtml
- https://www.peeringdb.com/asn/49835
- https://www.catnix.net/
- https://en.wikipedia.org/wiki/Internet_exchange_point
- http://www.adamo.es
- https://www.peeringdb.com/net/1989
- http://www.espanix.net
- https://www.andorratelecom.ad
- https://www.peeringdb.com/net/14854
- http://www.clara.net
- https://www.peeringdb.com/net/116
- https://www.cloudflare.com
- https://www.peeringdb.com/net/4224
- https://about.google/intl/en/
- https://www.peeringdb.com/net/433
- https://www.microsoft.com/nl-nl/
- https://www.peeringdb.com/net/694
- https://www.orange.es/
- https://www.peeringdb.com/net/11902
- http://www.rediris.es
- https://www.peeringdb.com/net/2813
- https://stat.ripe.net/widget/looking-glass
- https://www.peeringdb.com/net/621
- http://lg.he.net
- https://www.peeringdb.com/net/291
- https://www.isc.org
- https://www.peeringdb.com/net/1111
- https://www.t-systems.es
- https://www.peeringdb.com/net/10653
- www.telefonica.es
- https://www.peeringdb.com/net/12709
- http://www.verisign.com/rirs
- https://www.peeringdb.com/net/9897
- https://en.wikipedia.org/wiki/TR-069
- https://en.wikipedia.org/wiki/SOAP
- https://www.defcon.org/images/defcon-22/dc-22-presentations/Tal/DEFCON-22-Shahar-TaI-I-hunt-TR-069-admins-UPDATED.pdf